Vulnerabilities > CVE-2017-8422 - Authentication Bypass by Spoofing vulnerability in KDE Kauth
Attack vector
LOCAL Attack complexity
LOW Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
KDE kdelibs before 4.14.32 and KAuth before 5.34 allow local users to gain root privileges by spoofing a callerID and leveraging a privileged helper app.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Exploitation of Session Variables, Resource IDs and other Trusted Credentials Attacks on session IDs and resource IDs take advantage of the fact that some software accepts user input without verifying its authenticity. For example, a message queuing system that allows service requesters to post messages to its queue through an open channel (such as anonymous FTP), authorization is done through checking group or role membership contained in the posted message. However, there is no proof that the message itself, the information in the message (such group or role membership), or indeed the process that wrote the message to the queue are authentic and authorized to do so. Many server side processes are vulnerable to these attacks because the server to server communications have not been analyzed from a security perspective or the processes "trust" other systems because they are behind a firewall. In a similar way servers that use easy to guess or spoofable schemes for representing digital identity can also be vulnerable. Such systems frequently use schemes without cryptography and digital signatures (or with broken cryptography). Session IDs may be guessed due to insufficient randomness, poor protection (passed in the clear), lack of integrity (unsigned), or improperly correlation with access control policy enforcement points. Exposed configuration and properties files that contain system passwords, database connection strings, and such may also give an attacker an edge to identify these identifiers. The net result is that spoofing and impersonation is possible leading to an attacker's ability to break authentication, authorization, and audit controls on the system.
- Exploiting Trust in Client (aka Make the Client Invisible) An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Creating a Rogue Certificate Authority Certificate An attacker exploits a weakness in the MD5 hash algorithm (weak collision resistance) to generate a certificate signing request (CSR) that contains collision blocks in the "to be signed" part. The attacker specially crafts two different, but valid X.509 certificates that when hashed with the MD5 algorithm would yield the same value. The attacker then sends the CSR for one of the certificates to the Certification Authority which uses the MD5 hashing algorithm. That request is completely valid and the Certificate Authority issues an X.509 certificate to the attacker which is signed with its private key. An attacker then takes that signed blob and inserts it into another X.509 certificate that the attacker generated. Due to the MD5 collision, both certificates, though different, hash to the same value and so the signed blob works just as well in the second certificate. The net effect is that the attackers' second X.509 certificate, which the Certification Authority has never seen, is now signed and validated by that Certification Authority. To make the attack more interesting, the second certificate could be not just a regular certificate, but rather itself a signing certificate. Thus the attacker is able to start their own Certification Authority that is anchored in its root of trust in the legitimate Certification Authority that has signed the attackers' first X.509 certificate. If the original Certificate Authority was accepted by default by browsers, so will now the Certificate Authority set up by the attacker and of course any certificates that it signs. So the attacker is now able to generate any SSL certificates to impersonate any web server, and the user's browser will not issue any warning to the victim. This can be used to compromise HTTPS communications and other types of systems where PKI and X.509 certificates may be used (e.g., VPN, IPSec) .
- Web Services API Signature Forgery Leveraging Hash Function Extension Weakness When web services require callees to authenticate, they sometimes issue a token / secret to the caller that the caller is to use to sign their web service calls. In one such scheme the caller when constructing a request would concatenate all of the parameters passed to the web service with the provided authentication token and then generate a hash of the concatenated string (e.g., MD5, SHA1, etc.). That hash then forms the signature that is passed to the web service which is used on the server side to verify the origin authenticity and integrity of the message. There is a practical attack against an authentication scheme of this nature that makes use of the hash function extension / padding weakness. Leveraging this weakness, an attacker, who does not know the secret token, is able to modify the parameters passed to the web service by generating their own call and still generate a legitimate signature hash. For instance, consider the message to be passed to the web service is M (this message includes the parameters passed to the web service concatenated with the secret token / key bytes). The message M is hashed and that hash is passed to the web service and is used for authentication. The attacker does not know M, but can see Hash (M) and Length (M). The attacker can then compute Hash (M || Padding (M) II M') for any M'. The attacker does not know the entire message M, specifically the attacker does not know the secret bytes, but that does not matter. The attacker is still able to sign their own message M' and make the called web service verify the integrity of the message without an error. Because of the iterative design of the hash function, it is possible, from only the hash of a message and its length, to compute the hash of longer messages that start with the initial message and include the padding required for the initial message to reach a multiple of 512 bits. It is important to note that the attack not limited to MD5 and will work just as well with another hash function like SHA1.
- Signature Spoof An attacker generates a message or datablock that causes the recipient to believe that the message or datablock was generated and cryptographically signed by an authoritative or reputable source, misleading a victim or victim operating system into performing malicious actions.
Exploit-Db
| description | KDE 4/5 - 'KAuth' Privilege Escalation. CVE-2017-8422,CVE-2017-8849. Local exploit for Linux platform |
| file | exploits/linux/local/42053.c |
| id | EDB-ID:42053 |
| last seen | 2017-05-25 |
| modified | 2017-05-18 |
| platform | linux |
| port | |
| published | 2017-05-18 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/42053/ |
| title | KDE 4/5 - 'KAuth' Privilege Escalation |
| type | local |
Nessus
NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZLSA-2017-1264.NASL description An update for kdelibs is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The K Desktop Environment (KDE) is a graphical desktop environment for the X Window System. The kdelibs packages include core libraries for the K Desktop Environment. Security Fix(es) : * A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) Red Hat would like to thank Sebastian Krahmer (SUSE) for reporting this issue. Note that Tenable Network Security has attempted to extract the preceding description block directly from the corresponding Red Hat security advisory. Virtuozzo provides no description for VZLSA advisories. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 101468 published 2017-07-13 reporter This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101468 title Virtuozzo 7 : kdelibs / kdelibs-apidocs / kdelibs-common / etc (VZLSA-2017-1264) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(101468); script_version("1.9"); script_cvs_date("Date: 2018/11/20 11:04:17"); script_cve_id( "CVE-2017-8422" ); script_name(english:"Virtuozzo 7 : kdelibs / kdelibs-apidocs / kdelibs-common / etc (VZLSA-2017-1264)"); script_summary(english:"Checks the rpm output for the updated package."); script_set_attribute(attribute:"synopsis", value: "The remote Virtuozzo host is missing a security update."); script_set_attribute(attribute:"description", value: "An update for kdelibs is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The K Desktop Environment (KDE) is a graphical desktop environment for the X Window System. The kdelibs packages include core libraries for the K Desktop Environment. Security Fix(es) : * A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) Red Hat would like to thank Sebastian Krahmer (SUSE) for reporting this issue. Note that Tenable Network Security has attempted to extract the preceding description block directly from the corresponding Red Hat security advisory. Virtuozzo provides no description for VZLSA advisories. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues."); # http://repo.virtuozzo.com/vzlinux/announcements/json/VZLSA-2017-1264.json script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?c60a4e2e"); script_set_attribute(attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2017-1264"); script_set_attribute(attribute:"solution", value: "Update the affected kdelibs / kdelibs-apidocs / kdelibs-common / etc package."); script_set_cvss_base_vector("CVSS2#AV:L/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/22"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:virtuozzo:virtuozzo:kdelibs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:virtuozzo:virtuozzo:kdelibs-apidocs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:virtuozzo:virtuozzo:kdelibs-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:virtuozzo:virtuozzo:kdelibs-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:virtuozzo:virtuozzo:kdelibs-ktexteditor"); script_set_attribute(attribute:"cpe", value:"cpe:/o:virtuozzo:virtuozzo:7"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/07/13"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Virtuozzo Local Security Checks"); script_copyright(english:"This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Virtuozzo/release", "Host/Virtuozzo/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/Virtuozzo/release"); if (isnull(release) || "Virtuozzo" >!< release) audit(AUDIT_OS_NOT, "Virtuozzo"); os_ver = pregmatch(pattern: "Virtuozzo Linux release ([0-9]+\.[0-9])(\D|$)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Virtuozzo"); os_ver = os_ver[1]; if (! preg(pattern:"^7([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Virtuozzo 7.x", "Virtuozzo " + os_ver); if (!get_kb_item("Host/Virtuozzo/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Virtuozzo", cpu); flag = 0; pkgs = ["kdelibs-4.14.8-6.vl7", "kdelibs-apidocs-4.14.8-6.vl7", "kdelibs-common-4.14.8-6.vl7", "kdelibs-devel-4.14.8-6.vl7", "kdelibs-ktexteditor-4.14.8-6.vl7"]; foreach (pkg in pkgs) if (rpm_check(release:"Virtuozzo-7", reference:pkg)) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "kdelibs / kdelibs-apidocs / kdelibs-common / etc"); }NASL family Debian Local Security Checks NASL id DEBIAN_DLA-952.NASL description Several vulnerabilities were discovered in kde4libs, the core libraries for all KDE 4 applications. The Common Vulnerabilities and Exposures project identifies the following problems : CVE-2017-6410 Itzik Kotler, Yonatan Fridburg and Amit Klein of Safebreach Labs reported that URLs are not sanitized before passing them to FindProxyForURL, potentially allowing a remote attacker to obtain sensitive information via a crafted PAC file. CVE-2017-8422 Sebastian Krahmer from SUSE discovered that the KAuth framework contains a logic flaw in which the service invoking dbus is not properly checked. This flaw allows spoofing the identity of the caller and gaining root privileges from an unprivileged account. CVE-2013-2074 It was discovered that KIO would show web authentication credentials in some error cases. For Debian 7 last seen 2020-03-17 modified 2017-05-26 plugin id 100431 published 2017-05-26 reporter This script is Copyright (C) 2017-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/100431 title Debian DLA-952-1 : kde4libs security update code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DLA-952-1. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(100431); script_version("3.7"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/03/12"); script_cve_id("CVE-2013-2074", "CVE-2017-6410", "CVE-2017-8422"); script_bugtraq_id(59808); script_name(english:"Debian DLA-952-1 : kde4libs security update"); script_summary(english:"Checks dpkg output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security update." ); script_set_attribute( attribute:"description", value: "Several vulnerabilities were discovered in kde4libs, the core libraries for all KDE 4 applications. The Common Vulnerabilities and Exposures project identifies the following problems : CVE-2017-6410 Itzik Kotler, Yonatan Fridburg and Amit Klein of Safebreach Labs reported that URLs are not sanitized before passing them to FindProxyForURL, potentially allowing a remote attacker to obtain sensitive information via a crafted PAC file. CVE-2017-8422 Sebastian Krahmer from SUSE discovered that the KAuth framework contains a logic flaw in which the service invoking dbus is not properly checked. This flaw allows spoofing the identity of the caller and gaining root privileges from an unprivileged account. CVE-2013-2074 It was discovered that KIO would show web authentication credentials in some error cases. For Debian 7 'Wheezy', these problems have been fixed in version 4:4.8.4-4+deb7u3. We recommend that you upgrade your kde4libs packages. NOTE: Tenable Network Security has extracted the preceding description block directly from the DLA security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://lists.debian.org/debian-lts-announce/2017/05/msg00023.html" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/wheezy/kde4libs" ); script_set_attribute(attribute:"solution", value:"Upgrade the affected packages."); script_set_cvss_base_vector("CVSS2#AV:L/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdelibs-bin"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdelibs5-data"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdelibs5-dbg"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdelibs5-dev"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdelibs5-plugins"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:kdoctools"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkcmutils4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkde3support4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdeclarative5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdecore5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdesu5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdeui5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdewebkit5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkdnssd4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkemoticons4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkfile4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkhtml5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkidletime4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkimproxy4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkio5"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkjsapi4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkjsembed4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkmediaplayer4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libknewstuff2-4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libknewstuff3-4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libknotifyconfig4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkntlm4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkparts4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkprintutils4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkpty4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkrosscore4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkrossui4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libktexteditor4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkunitconversion4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libkutils4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libnepomuk4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libnepomukquery4a"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libnepomukutils4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libplasma3"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libsolid4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libthreadweaver4"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:7.0"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/25"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/26"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 Tenable Network Security, Inc."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"7.0", prefix:"kdelibs-bin", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"kdelibs5-data", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"kdelibs5-dbg", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"kdelibs5-dev", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"kdelibs5-plugins", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"kdoctools", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkcmutils4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkde3support4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdeclarative5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdecore5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdesu5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdeui5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdewebkit5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkdnssd4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkemoticons4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkfile4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkhtml5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkidletime4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkimproxy4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkio5", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkjsapi4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkjsembed4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkmediaplayer4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libknewstuff2-4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libknewstuff3-4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libknotifyconfig4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkntlm4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkparts4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkprintutils4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkpty4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkrosscore4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkrossui4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libktexteditor4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkunitconversion4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libkutils4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libnepomuk4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libnepomukquery4a", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libnepomukutils4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libplasma3", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libsolid4", reference:"4:4.8.4-4+deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libthreadweaver4", reference:"4:4.8.4-4+deb7u3")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Fedora Local Security Checks NASL id FEDORA_2017-DD51077C87.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-07-17 plugin id 101735 published 2017-07-17 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101735 title Fedora 26 : 6:kdelibs (2017-dd51077c87) NASL family Fedora Local Security Checks NASL id FEDORA_2017-8B4898CE81.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-17 plugin id 100229 published 2017-05-17 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100229 title Fedora 24 : 6:kdelibs (2017-8b4898ce81) NASL family SuSE Local Security Checks NASL id SUSE_SU-2017-1335-1.NASL description This update for kdelibs4 fixes the following issues : - CVE-2017-8422: This update fixes problem in the DBUS authentication of the kauth framework that could be used to escalate privileges depending on bugs or misimplemented dbus services. (boo#1036244) Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 100290 published 2017-05-19 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100290 title SUSE SLED12 / SLES12 Security Update : kdelibs4 (SUSE-SU-2017:1335-1) NASL family Fedora Local Security Checks NASL id FEDORA_2017-0898C704A1.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-07-17 plugin id 101567 published 2017-07-17 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101567 title Fedora 26 : kf5-kauth (2017-0898c704a1) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1264.NASL description An update for kdelibs is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The K Desktop Environment (KDE) is a graphical desktop environment for the X Window System. The kdelibs packages include core libraries for the K Desktop Environment. Security Fix(es) : * A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) Red Hat would like to thank Sebastian Krahmer (SUSE) for reporting this issue. last seen 2020-06-01 modified 2020-06-02 plugin id 100345 published 2017-05-23 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100345 title RHEL 7 : kdelibs (RHSA-2017:1264) NASL family Fedora Local Security Checks NASL id FEDORA_2017-6BDBF57F29.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-16 plugin id 100191 published 2017-05-16 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100191 title Fedora 24 : kf5-kauth (2017-6bdbf57f29) NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2017-1264.NASL description An update for kdelibs is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The K Desktop Environment (KDE) is a graphical desktop environment for the X Window System. The kdelibs packages include core libraries for the K Desktop Environment. Security Fix(es) : * A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) Red Hat would like to thank Sebastian Krahmer (SUSE) for reporting this issue. last seen 2020-06-01 modified 2020-06-02 plugin id 100328 published 2017-05-23 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100328 title CentOS 7 : kdelibs (CESA-2017:1264) NASL family Gentoo Local Security Checks NASL id GENTOO_GLSA-201706-29.NASL description The remote host is affected by the vulnerability described in GLSA-201706-29 (KAuth and KDELibs: Privilege escalation) KAuth and KDELibs contains a logic flaw in which the service invoking D-Bus is not properly checked. This allows spoofing the identity of the caller and with some carefully crafted calls can lead to gaining root from an unprivileged account. Impact : A local attacker could spoof the identity of the caller invoking D-Bus, possibly resulting in gaining privileges. Workaround : There is no known workaround at this time. last seen 2020-06-01 modified 2020-06-02 plugin id 101075 published 2017-06-28 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101075 title GLSA-201706-29 : KAuth and KDELibs: Privilege escalation NASL family Scientific Linux Local Security Checks NASL id SL_20170522_KDELIBS_ON_SL7_X.NASL description Security Fix(es) : - A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) last seen 2020-03-18 modified 2017-05-23 plugin id 100349 published 2017-05-23 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100349 title Scientific Linux Security Update : kdelibs on SL7.x x86_64 (20170522) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2017-1264.NASL description From Red Hat Security Advisory 2017:1264 : An update for kdelibs is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The K Desktop Environment (KDE) is a graphical desktop environment for the X Window System. The kdelibs packages include core libraries for the K Desktop Environment. Security Fix(es) : * A privilege escalation flaw was found in the way kdelibs handled D-Bus messages. A local user could potentially use this flaw to gain root privileges by spoofing a callerID and leveraging a privileged helper application. (CVE-2017-8422) Red Hat would like to thank Sebastian Krahmer (SUSE) for reporting this issue. last seen 2020-06-01 modified 2020-06-02 plugin id 100343 published 2017-05-23 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100343 title Oracle Linux 7 : kdelibs (ELSA-2017-1264) NASL family Fedora Local Security Checks NASL id FEDORA_2017-7E3437B905.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-16 plugin id 100193 published 2017-05-16 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100193 title Fedora 25 : kf5-kauth (2017-7e3437b905) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3286-1.NASL description Sebastian Krahmer discovered that the KDE-Libs Kauth component incorrectly checked services invoking D-Bus. A local attacker could use this issue to gain root privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 100217 published 2017-05-16 reporter Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100217 title Ubuntu 14.04 LTS : kde4libs vulnerability (USN-3286-1) NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3849.NASL description Several vulnerabilities were discovered in kde4libs, the core libraries for all KDE 4 applications. The Common Vulnerabilities and Exposures project identifies the following problems : - CVE-2017-6410 Itzik Kotler, Yonatan Fridburg and Amit Klein of Safebreach Labs reported that URLs are not sanitized before passing them to FindProxyForURL, potentially allowing a remote attacker to obtain sensitive information via a crafted PAC file. - CVE-2017-8422 Sebastian Krahmer from SUSE discovered that the KAuth framework contains a logic flaw in which the service invoking dbus is not properly checked. This flaw allows spoofing the identity of the caller and gaining root privileges from an unprivileged account. last seen 2020-06-01 modified 2020-06-02 plugin id 100163 published 2017-05-15 reporter This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100163 title Debian DSA-3849-1 : kde4libs - security update NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_0BAEE383356C11E7B9A950E549EBAB6C.NASL description Albert Astals Cid reports : KAuth contains a logic flaw in which the service invoking dbus is not properly checked. This allows spoofing the identity of the caller and with some carefully crafted calls can lead to gaining root from an unprivileged account. last seen 2020-06-01 modified 2020-06-02 plugin id 100113 published 2017-05-11 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100113 title FreeBSD : kauth: Local privilege escalation (0baee383-356c-11e7-b9a9-50e549ebab6c) NASL family SuSE Local Security Checks NASL id OPENSUSE-2017-575.NASL description This update for kauth and kdelibs4 fixes the following issues : - CVE-2017-8422: logic flaw in the KAuth framework allowed privilege escalation (boo#1036244). last seen 2020-06-05 modified 2017-05-16 plugin id 100202 published 2017-05-16 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100202 title openSUSE Security Update : kauth / kdelibs4 (openSUSE-2017-575) NASL family Slackware Local Security Checks NASL id SLACKWARE_SSA_2017-136-02.NASL description New kdelibs packages are available for Slackware 13.37, 14.0, 14.1, 14.2, and -current to fix a security issue. last seen 2020-06-01 modified 2020-06-02 plugin id 100224 published 2017-05-17 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100224 title Slackware 13.37 / 14.0 / 14.1 / 14.2 / current : kdelibs (SSA:2017-136-02) NASL family Fedora Local Security Checks NASL id FEDORA_2017-AFF6F6BD9D.NASL description security fix for CVE-2017-8422. https://www.kde.org/info/security/advisory-20170510-1.txt Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-16 plugin id 100197 published 2017-05-16 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100197 title Fedora 25 : 6:kdelibs (2017-aff6f6bd9d)
Packetstorm
| data source | https://packetstormsecurity.com/files/download/142638/kde45-escalate.txt |
| id | PACKETSTORM:142638 |
| last seen | 2017-05-25 |
| published | 2017-05-23 |
| reporter | stealth |
| source | https://packetstormsecurity.com/files/142638/KDE-4-5-KAuth-Privilege-Escalation.html |
| title | KDE 4/5 KAuth Privilege Escalation |
Redhat
| advisories |
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| rpms |
|
Seebug
| bulletinFamily | exploit |
| description | This document describes a generic root exploit against kde. The exploit is achieved by abusing a logic flaw within the KAuth framework which is present in kde4 (org.kde.auth) and kde5 (org.kde.kf5auth). It is possible to spoof what KAuth calls callerID's which are indeed D-Bus unique names of the sender of a D-Bus message. Exploitation requires a helper which is doing some privileged work as root. Kde ships quite some of them, but for this writeup I chose the smb4k helper because it contains another vulnerability that makes exploitation a lot easier; but in general any KAuth privileged helper code can be triggered by users with arbitrary arguments which leads to LPE on default kde installations. I will describe the overall problem by walking through the smb4k code and explain which D-Bus functions are called and how a particular smb4k bug maps into the bigger picture of the KAuth flaw. Theres a problem with smb4k using the KAuth framework and trusting all the arguments passed to the helper: ``` ActionReply Smb4KMountHelper::mount(const QVariantMap &args) { ... command << args["mh_command"].toString(); command << args["mh_unc"].toString(); command << args["mh_mountpoint"].toString(); command << args["mh_options"].toStringList(); ... proc.setProgram(command); // Run the mount process. proc.start(); ... } ``` This code is running as root, triggered via D-Bus activation by smb4k GUI code running as user, and the args supplied by the user, via: ``` void Smb4KMountJob::slotStartMount() { ... Action::executeActions(actions, NULL, "net.sourceforge.smb4k.mounthelper"); ... } ``` after filling actions (theres only one) with the proper Name net.sourceforge.smb4k.mounthelper.mount and HelperID net.sourceforge.smb4k.mounthelper in order to trigger D-Bus activation as well as the argument dictionary which contains the mh_command etc. key/value pairs. Its calling the list-version of Action::executeAction() [note the trailing 's'] with a one-element list, but that doesn't matter. The important thing here is that the arguments are created by code running as user - potentially containing evil input - and are evaluated by the helper program running as root. The above call ends at DBusHelperProxy::executeAction(), still at callers side. This function translates it into a D-Bus method call which is finally running privileged and has the following interface: ``` <interface name="org.kde.kf5auth"> ... <method name="performAction" > <arg name="action" type="s" direction="in" /> <arg name="callerID" type="ay" direction="in" /> <arg name="arguments" type="ay" direction="in" /> <arg name="r" type="ay" direction="out" /> </method> ... </interface> ``` Unlike the root helpers D-Bus interfaces itself, which are not accessible as user, the KAuth D-Bus interface org.kde.kf5auth is: ``` <busconfig> <policy context="default"> <allow send_interface="org.kde.kf5auth"/> <allow receive_sender="org.kde.kf5auth"/> <allow receive_interface="org.kde.kf5auth"/> </policy> </busconfig> ``` The code for actually doing the call from user to root is this: ``` void DBusHelperProxy::executeAction(const QString &action, const QString &helperID, const QVariantMap &arguments) { ... QDBusMessage::createMethodCall(helperID, QLatin1String("/"), QLatin1String("org.kde.kf5auth"), QLatin1String("performAction")); QList<QVariant> args; args << action << BackendsManager::authBackend()->callerID() << blob; message.setArguments(args); m_actionsInProgress.push_back(action); QDBusPendingCall pendingCall = m_busConnection.asyncCall(message); ... } ``` This code is invoking the performAction() D-Bus method, passing along the user supplied arguments dictionary, in our smb4k case containing the handcrafted evil mh_command key, amongst others key/value pairs. There are two problems: The KAuth frameworks performAction() method is passed the callerID by the user and the method is invokable by the user. This allows to mask as any caller, bypassing any polkit checks that may happen later in the KAuth polkit backend via calls into ``` PolicyKitBackend::isCallerAuthorized(const QString &action, QByteArray callerID) ``` The second problem is smb4k trusting the arguments that are passed from the user and which are forwarded by the KAuth D-Bus service running as root to the mount helper D-Bus service which is also running as root but not allowed to be contacted by users. Thats a logical flaw. It was probably not intented that users invoke performAction() themself, using it as a proxy into D-Bus services and faking caller IDs en-passant. The callerID usually looks like :1.123 and is a D-Bus unique name that maps to the sender of the message. You can think of it like the source address of an IP packet. This ID should be obtained via a D-Bus function while the message is arriving, so it can actually be trusted and used as a subject for polkit authorizations when using systembus-name subjects. Allowing callers to arbitrarily choosing values for this ID is taking down the whole idea of authentication and authorization. I made an exploit for smb4k that works on openSUSE Leap 42.2 thats using the org.kde.auth interface (rather than org.kde.kf5auth) but both interfaces share the same problems. The exploit also works on the latest Fedora26 Alpha kde spin with SELinux in enforcing mode. In order to test the callerID spoofing, I "protected" the smb4k helper code via auth_admin polkit settings and tried mounting SMB shares via smb4k GUI. This asked for the root password, as its expected. The exploit however still works, as its spoofing the callerID to be D-Bus itself and the request is taken as legit, requiring no root password. 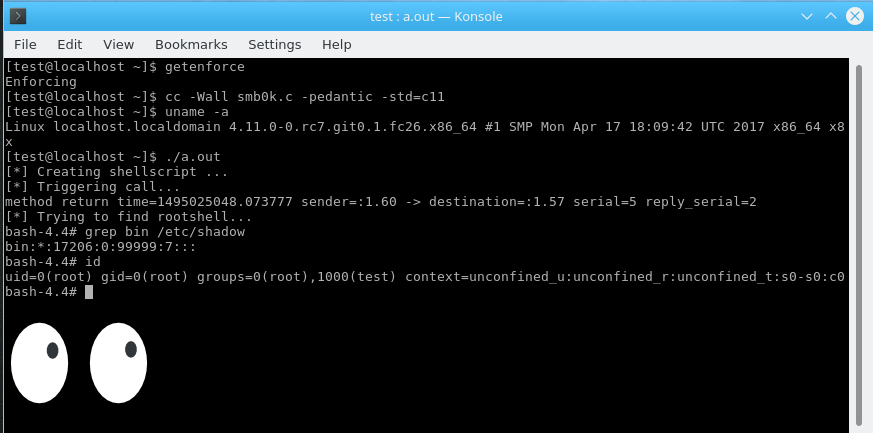 |
| id | SSV:93115 |
| last seen | 2017-11-19 |
| modified | 2017-05-19 |
| published | 2017-05-19 |
| reporter | Root |
| title | KDE kauth and kdelibs Logic Flaw Lets Local Users Obtain Root Privileges(CVE-2017-8422) |
References
- http://www.debian.org/security/2017/dsa-3849
- http://www.debian.org/security/2017/dsa-3849
- http://www.openwall.com/lists/oss-security/2017/05/10/3
- http://www.openwall.com/lists/oss-security/2017/05/10/3
- http://www.securityfocus.com/bid/98412
- http://www.securityfocus.com/bid/98412
- http://www.securitytracker.com/id/1038480
- http://www.securitytracker.com/id/1038480
- https://access.redhat.com/errata/RHSA-2017:1264
- https://access.redhat.com/errata/RHSA-2017:1264
- https://bugzilla.redhat.com/show_bug.cgi?id=1449647
- https://bugzilla.redhat.com/show_bug.cgi?id=1449647
- https://cgit.kde.org/kauth.git/commit/?id=df875f725293af53399f5146362eb158b4f9216a
- https://cgit.kde.org/kauth.git/commit/?id=df875f725293af53399f5146362eb158b4f9216a
- https://cgit.kde.org/kdelibs.git/commit/?id=264e97625abe2e0334f97de17f6ffb52582888ab
- https://cgit.kde.org/kdelibs.git/commit/?id=264e97625abe2e0334f97de17f6ffb52582888ab
- https://security.gentoo.org/glsa/201706-29
- https://security.gentoo.org/glsa/201706-29
- https://www.exploit-db.com/exploits/42053/
- https://www.exploit-db.com/exploits/42053/
- https://www.kde.org/info/security/advisory-20170510-1.txt
- https://www.kde.org/info/security/advisory-20170510-1.txt