Vulnerabilities > CVE-2017-14849 - Path Traversal vulnerability in Nodejs Node.Js 8.5.0
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
NONE Availability impact
NONE Summary
Node.js 8.5.0 before 8.6.0 allows remote attackers to access unintended files, because a change to ".." handling was incompatible with the pathname validation used by unspecified community modules.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Relative Path Traversal An attacker exploits a weakness in input validation on the target by supplying a specially constructed path utilizing dot and slash characters for the purpose of obtaining access to arbitrary files or resources. An attacker modifies a known path on the target in order to reach material that is not available through intended channels. These attacks normally involve adding additional path separators (/ or \) and/or dots (.), or encodings thereof, in various combinations in order to reach parent directories or entirely separate trees of the target's directory structure.
- Directory Traversal An attacker with access to file system resources, either directly or via application logic, will use various file path specification or navigation mechanisms such as ".." in path strings and absolute paths to extend their range of access to inappropriate areas of the file system. The attacker attempts to either explore the file system for recon purposes or access directories and files that are intended to be restricted from their access. Exploring the file system can be achieved through constructing paths presented to directory listing programs, such as "ls" and 'dir', or through specially crafted programs that attempt to explore the file system. The attacker engaging in this type of activity is searching for information that can be used later in a more exploitive attack. Access to restricted directories or files can be achieved through modification of path references utilized by system applications.
- File System Function Injection, Content Based An attack of this type exploits the host's trust in executing remote content including binary files. The files are poisoned with a malicious payload (targeting the file systems accessible by the target software) by the attacker and may be passed through standard channels such as via email, and standard web content like PDF and multimedia files. The attacker exploits known vulnerabilities or handling routines in the target processes. Vulnerabilities of this type have been found in a wide variety of commercial applications from Microsoft Office to Adobe Acrobat and Apple Safari web browser. When the attacker knows the standard handling routines and can identify vulnerabilities and entry points they can be exploited by otherwise seemingly normal content. Once the attack is executed, the attackers' program can access relative directories such as C:\Program Files or other standard system directories to launch further attacks. In a worst case scenario, these programs are combined with other propagation logic and work as a virus.
- Using Slashes and URL Encoding Combined to Bypass Validation Logic This attack targets the encoding of the URL combined with the encoding of the slash characters. An attacker can take advantage of the multiple way of encoding an URL and abuse the interpretation of the URL. An URL may contain special character that need special syntax handling in order to be interpreted. Special characters are represented using a percentage character followed by two digits representing the octet code of the original character (%HEX-CODE). For instance US-ASCII space character would be represented with %20. This is often referred as escaped ending or percent-encoding. Since the server decodes the URL from the requests, it may restrict the access to some URL paths by validating and filtering out the URL requests it received. An attacker will try to craft an URL with a sequence of special characters which once interpreted by the server will be equivalent to a forbidden URL. It can be difficult to protect against this attack since the URL can contain other format of encoding such as UTF-8 encoding, Unicode-encoding, etc.
- Manipulating Input to File System Calls An attacker manipulates inputs to the target software which the target software passes to file system calls in the OS. The goal is to gain access to, and perhaps modify, areas of the file system that the target software did not intend to be accessible.
D2sec
| name | Node.js 8.5.0 Path Traversal File Disclosure |
| url | http://www.d2sec.com/exploits/node.js_8.5.0_path_traversal_file_disclosure.html |
Nessus
| NASL family | FreeBSD Local Security Checks |
| NASL id | FREEBSD_PKG_1257718EBE97458A9744D938B592DB42.NASL |
| description | node developers report : Node.js 8.5.0 before 8.6.0 allows remote attackers to access unintended files, because a change to |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 103759 |
| published | 2017-10-11 |
| reporter | This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/103759 |
| title | FreeBSD : node -- access to unintended files (1257718e-be97-458a-9744-d938b592db42) |
| code | |
Seebug
| bulletinFamily | exploit |
| description | Author: [niubl@TSRC](<https://security.tencent.com/index.php/blog/msg/121?from=timeline&isappinstalled=0> "niubl@TSRC" ) #### 1\. Vulnerability description 2017 9 November 28, the company scanner found a business there is an example of the arbitrary file read vulnerability, the team follow-up analysis found that this is the Node. js and Express the common result of a Common Vulnerability. As we prepare to inform the official, The found Node. js official website to 9 on 29, shows the vulnerability announcement, and the corresponding CVE number for CVE-2017-14849。 ###### 1.1 关于Node.js Node. js is a Javascript Runtime Environment(runtime), released in 2009 for 5 months, by Ryan Dahl developed, in essence, is the Chrome V8 engine package. Node. js for some of the special cases for optimization, to provide an alternative API, such that a V8 in a non-browser environment run better. ###### 1.2 about Express Express is a concise and flexible node.js Web application framework, providing a range of powerful features to help you create a variety of Web applications. Express does not node.js the existing characteristics of the secondary abstraction, we are just on the top of it extended the Web application the desired functionality. Rich the HTTP tool from the Connect framework middleware with the take with the use, create a robust, friendly API is quick and easy. ###### 1.3 vulnerability Node.js 8.5.0 + Express 3.19.0-3.21.2 Node.js 8.5.0 + Express 4.11.0-4.15.5 #### 2\. Vulnerability demo 1. 安装Node.js 8.5.0 2. 下载并解压express-4.15.5.zip 3. expresss-4.15.5 directory execute npm install 4. expresss-4.15.5/examples/static-files directory in the implementation of nodejs index.js 5. The use of POC tests, web listening to the 5678 port, default 3000 the following figure 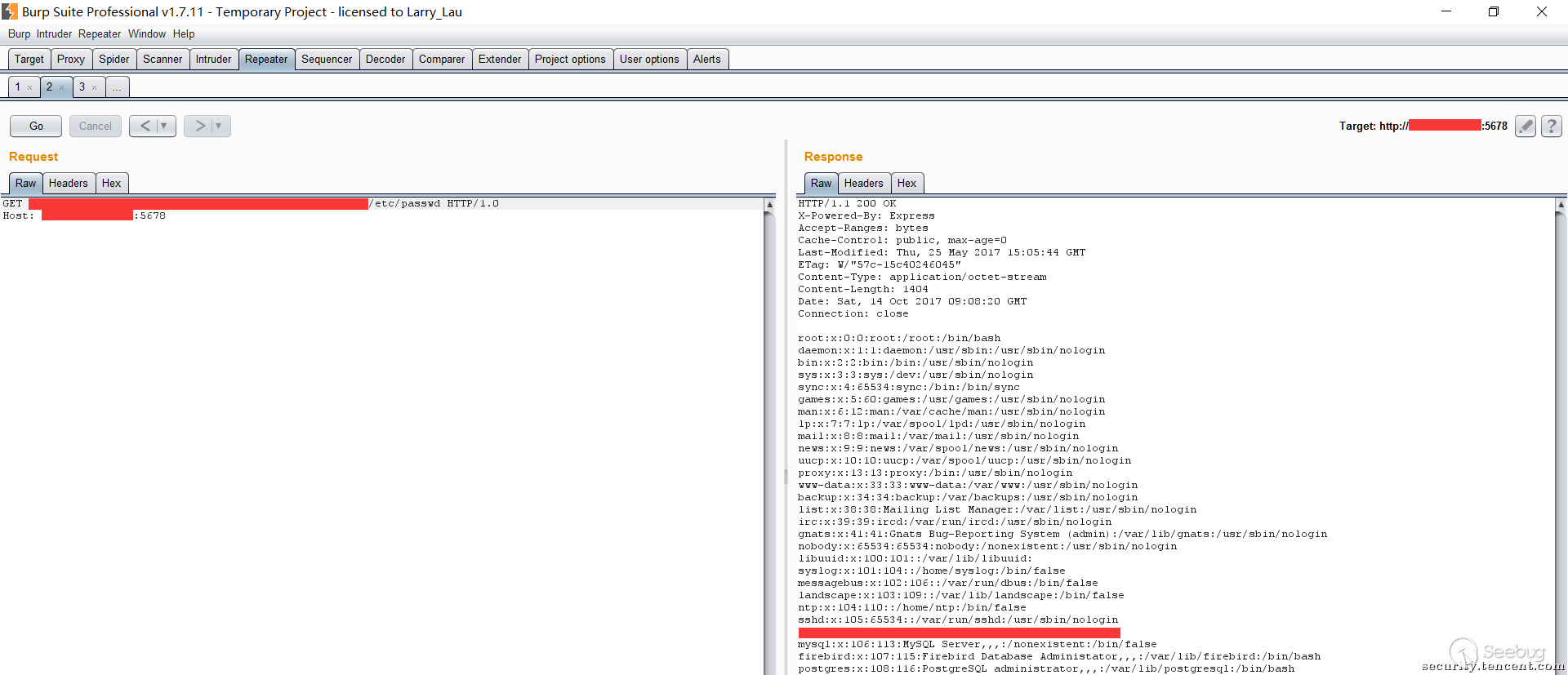 #### 3\. Vulnerability analysis Express reliance on the Send component, Send component 0. 11. 0-0. 15. 6 version of the pipe()function, as shown: 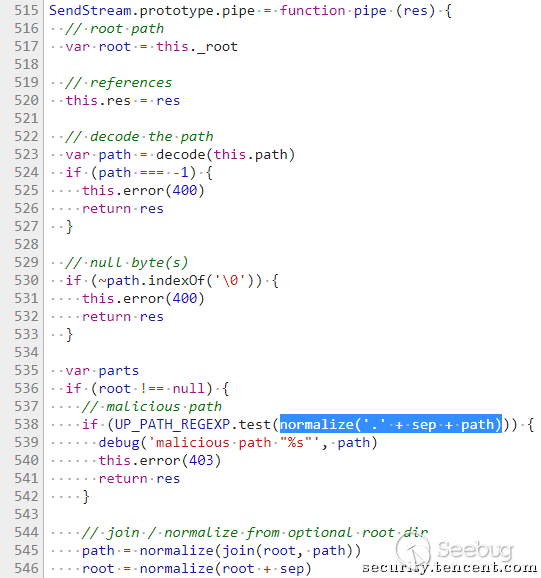 The Send module by `normalize('.' + sep + path) `standardized path path, and not assigned to a path, but merely determine the whether there is a directory jump characters. If we can bypass the directory jump character of the judgment, you can put the directory jump character into 545 the rows of the `join(root, path) `function, jump to we want to jump to the directory, this is the Send module of a bug has now been fixed. 再来看Node.js that Node.js 8.5.0 the path. js file in the `normalizeStringPosix `function has been modified, so that it can be the path to do the following standardization: `assert. strictEqual(path. posix. normalize('bar/foo../..'), 'bar');` New modifications brought to the problem, by stepping through we found that, by `foo../../`and directory jump characters together is injected into the path, `foo../../`you can put variables `isAboveRoot `set to `false `code 161 rows, and in the code 135 line put your own delete; variable `isAboveRoot `for the `false `case, can be in the `foo../../`both sides set the same number of jump characters, make them the same in code 135 line to remove yourself, so that you can construct a A with a jump character, but by `normalizeStringPosix `function after normalization will all automatically remove the payload, the payload with the above-mentioned Send module bug will be able to successfully return the one we want the physical path, and finally in the Send module reads and returns the file.`normalizeStringPosix `function as shown below: 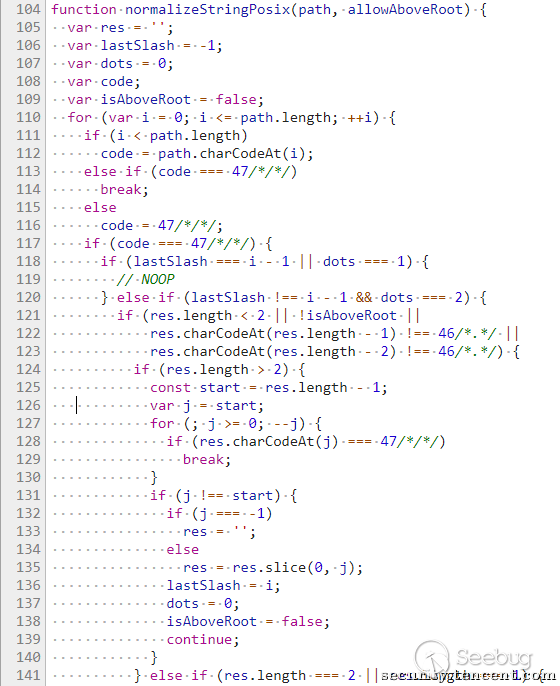 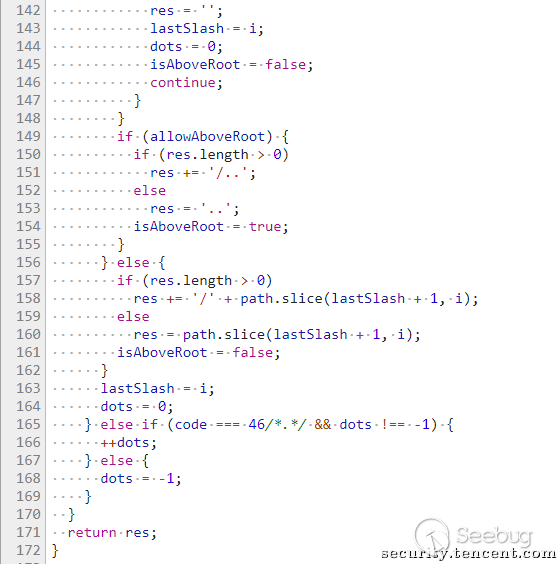 |
| id | SSV:96804 |
| last seen | 2017-11-19 |
| modified | 2017-11-07 |
| published | 2017-11-07 |
| reporter | Root |
| title | Node.js arbitrary file read Vulnerability(CVE-2017-14849) |
References
- http://www.securityfocus.com/bid/101056
- http://www.securityfocus.com/bid/101056
- https://nodejs.org/en/blog/vulnerability/september-2017-path-validation/
- https://nodejs.org/en/blog/vulnerability/september-2017-path-validation/
- https://twitter.com/nodejs/status/913131152868876288
- https://twitter.com/nodejs/status/913131152868876288