Vulnerabilities > CVE-2016-9838 - Improper Access Control vulnerability in Joomla Joomla!
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
NONE Integrity impact
HIGH Availability impact
NONE Summary
An issue was discovered in components/com_users/models/registration.php in Joomla! before 3.6.5. Incorrect filtering of registration form data stored to the session on a validation error enables a user to gain access to a registered user's account and reset the user's group mappings, username, and password, as demonstrated by submitting a form that targets the `registration.register` task.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Signature Spoofing by Key Theft An attacker obtains an authoritative or reputable signer's private signature key by theft and then uses this key to forge signatures from the original signer to mislead a victim into performing actions that benefit the attacker.
Exploit-Db
| description | Joomla! < 3.6.4 - Admin TakeOver. CVE-2016-9838. Webapps exploit for PHP platform |
| file | exploits/php/webapps/41157.py |
| id | EDB-ID:41157 |
| last seen | 2017-01-26 |
| modified | 2017-01-20 |
| platform | php |
| port | |
| published | 2017-01-20 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/41157/ |
| title | Joomla! < 3.6.4 - Admin TakeOver |
| type | webapps |
Nessus
NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_624B45C0C7F311E6AE1B002590263BF5.NASL description The JSST and the Joomla! Security Center report : [20161201] - Core - Elevated Privileges Incorrect use of unfiltered data stored to the session on a form validation failure allows for existing user accounts to be modified; to include resetting their username, password, and user group assignments. [20161202] - Core - Shell Upload Inadequate filesystem checks allowed files with alternative PHP file extensions to be uploaded. [20161203] - Core - Information Disclosure Inadequate ACL checks in the Beez3 com_content article layout override enables a user to view restricted content. last seen 2020-06-01 modified 2020-06-02 plugin id 96059 published 2016-12-22 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96059 title FreeBSD : Joomla! -- multiple vulnerabilities (624b45c0-c7f3-11e6-ae1b-002590263bf5) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from the FreeBSD VuXML database : # # Copyright 2003-2018 Jacques Vidrine and contributors # # Redistribution and use in source (VuXML) and 'compiled' forms (SGML, # HTML, PDF, PostScript, RTF and so forth) with or without modification, # are permitted provided that the following conditions are met: # 1. Redistributions of source code (VuXML) must retain the above # copyright notice, this list of conditions and the following # disclaimer as the first lines of this file unmodified. # 2. Redistributions in compiled form (transformed to other DTDs, # published online in any format, converted to PDF, PostScript, # RTF and other formats) must reproduce the above copyright # notice, this list of conditions and the following disclaimer # in the documentation and/or other materials provided with the # distribution. # # THIS DOCUMENTATION IS PROVIDED BY THE AUTHOR AND CONTRIBUTORS "AS IS" # AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, # THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR # PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS # BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, # OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT # OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR # BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, # WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE # OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS DOCUMENTATION, # EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. # include("compat.inc"); if (description) { script_id(96059); script_version("3.5"); script_cvs_date("Date: 2019/04/11 17:23:06"); script_cve_id("CVE-2016-9836", "CVE-2016-9837", "CVE-2016-9838"); script_name(english:"FreeBSD : Joomla! -- multiple vulnerabilities (624b45c0-c7f3-11e6-ae1b-002590263bf5)"); script_summary(english:"Checks for updated package in pkg_info output"); script_set_attribute( attribute:"synopsis", value:"The remote FreeBSD host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "The JSST and the Joomla! Security Center report : [20161201] - Core - Elevated Privileges Incorrect use of unfiltered data stored to the session on a form validation failure allows for existing user accounts to be modified; to include resetting their username, password, and user group assignments. [20161202] - Core - Shell Upload Inadequate filesystem checks allowed files with alternative PHP file extensions to be uploaded. [20161203] - Core - Information Disclosure Inadequate ACL checks in the Beez3 com_content article layout override enables a user to view restricted content." ); # https://developer.joomla.org/security-centre/664-20161201-core-elevated-privileges.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?7934a324" ); # https://developer.joomla.org/security-centre/665-20161202-core-shell-upload.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?6c4c5a5e" ); # https://developer.joomla.org/security-centre/666-20161203-core-information-disclosure.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?a397aea4" ); # https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?3ca7356f" ); # https://vuxml.freebsd.org/freebsd/624b45c0-c7f3-11e6-ae1b-002590263bf5.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?4b66e4e1" ); script_set_attribute(attribute:"solution", value:"Update the affected package."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:freebsd:freebsd:joomla3"); script_set_attribute(attribute:"cpe", value:"cpe:/o:freebsd:freebsd"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/12/06"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/22"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/22"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"FreeBSD Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/FreeBSD/release", "Host/FreeBSD/pkg_info"); exit(0); } include("audit.inc"); include("freebsd_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/FreeBSD/release")) audit(AUDIT_OS_NOT, "FreeBSD"); if (!get_kb_item("Host/FreeBSD/pkg_info")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (pkg_test(save_report:TRUE, pkg:"joomla3>=1.6.0<3.6.5")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:pkg_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family CGI abuses NASL id JOOMLA_365.NASL description According to its self-reported version number, the Joomla! installation running on the remote web server is prior to 3.6.5. It is, therefore, affected by multiple vulnerabilities : - A flaw exists in the JFilterInput::isFileSafe() function due to improper validation of file types and extensions of uploaded files before placing them in a user-accessible path. An unauthenticated, remote attacker can exploit this issue, by uploading a specially crafted file using an alternative PHP extension and then requesting it, to execute arbitrary code with the privileges of the web service. Note that this issue affects versions 3.0.0 to 3.6.4. (CVE-2016-9836) - An information disclosure vulnerability exists in the Beez3 com_content article layout override due to inadequate access control list (ACL) checks. An authenticated, remote attacker can exploit this to disclose restricted content. Note that this issue affects versions 3.0.0 to 3.6.4. (CVE-2016-9837) - A privilege escalation vulnerability exists due to improper validation of form data before storing it in the session. An authenticated, remote attacker can exploit this, via a specially crafted request, to modify existing user accounts, such as resetting credentials or group assignments. (CVE-2016-9838) Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 95916 published 2016-12-16 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95916 title Joomla! < 3.6.5 Multiple Vulnerabilities code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(95916); script_version("1.8"); script_cvs_date("Date: 2019/11/13"); script_cve_id("CVE-2016-9836", "CVE-2016-9837", "CVE-2016-9838"); script_bugtraq_id(94663, 94892, 94893); script_name(english:"Joomla! < 3.6.5 Multiple Vulnerabilities"); script_summary(english:"Checks the version of Joomla!."); script_set_attribute(attribute:"synopsis", value: "The remote web server contains a PHP application that is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "According to its self-reported version number, the Joomla! installation running on the remote web server is prior to 3.6.5. It is, therefore, affected by multiple vulnerabilities : - A flaw exists in the JFilterInput::isFileSafe() function due to improper validation of file types and extensions of uploaded files before placing them in a user-accessible path. An unauthenticated, remote attacker can exploit this issue, by uploading a specially crafted file using an alternative PHP extension and then requesting it, to execute arbitrary code with the privileges of the web service. Note that this issue affects versions 3.0.0 to 3.6.4. (CVE-2016-9836) - An information disclosure vulnerability exists in the Beez3 com_content article layout override due to inadequate access control list (ACL) checks. An authenticated, remote attacker can exploit this to disclose restricted content. Note that this issue affects versions 3.0.0 to 3.6.4. (CVE-2016-9837) - A privilege escalation vulnerability exists due to improper validation of form data before storing it in the session. An authenticated, remote attacker can exploit this, via a specially crafted request, to modify existing user accounts, such as resetting credentials or group assignments. (CVE-2016-9838) Note that Nessus has not tested for these issues but has instead relied only on the application's self-reported version number."); # https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?3ca7356f"); # https://developer.joomla.org/security-centre/664-20161201-core-elevated-privileges.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?7934a324"); # https://developer.joomla.org/security-centre/665-20161202-core-shell-upload.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?6c4c5a5e"); # https://developer.joomla.org/security-centre/666-20161203-core-information-disclosure.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?a397aea4"); script_set_attribute(attribute:"solution", value: "Upgrade to Joomla! version 3.6.5 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:U/RC:ND"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:U/RC:X"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2016-9836"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/10/27"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/13"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/16"); script_set_attribute(attribute:"potential_vulnerability", value:"true"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/a:joomla:joomla\!"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"CGI abuses"); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("joomla_detect.nasl"); script_require_keys("installed_sw/Joomla!", "www/PHP", "Settings/ParanoidReport"); script_require_ports("Services/www", 80); exit(0); } include("audit.inc"); include("global_settings.inc"); include("http.inc"); include("install_func.inc"); include("misc_func.inc"); app = "Joomla!"; get_install_count(app_name:app, exit_if_zero:TRUE); port = get_http_port(default:80, php:TRUE); install = get_single_install( app_name : app, port : port, exit_if_unknown_ver : TRUE ); #if (report_paranoia < 2) audit(AUDIT_PARANOID); dir = install["path"]; install_loc = build_url(port:port, qs:dir); version = install['version']; fix = "3.6.5"; # Pull out the purely numeric version numeric = eregmatch(string:version, pattern:"^([0-9\.]+)($|[^0-9])"); if (empty_or_null(numeric)) audit(AUDIT_UNKNOWN_WEB_APP_VER, app, install_loc); numeric = numeric[1]; parts = split(numeric, sep:".", keep:FALSE); if (len(parts) < 3) audit(AUDIT_VER_NOT_GRANULAR, app, version); # Version 1.6.0 - 3.6.4 vulnerable to privilege escalation # https://developer.joomla.org/security-centre/664-20161201-core-elevated-privileges.html if (ver_compare(ver:numeric, minver:"1.6.0", fix:fix, strict:FALSE) < 0) { report = '\n URL : ' +install_loc+ '\n Installed version : ' +version+ '\n Fixed version : ' +fix+ '\n'; security_report_v4( port:port, extra:report, severity:SECURITY_HOLE); } else audit(AUDIT_WEB_APP_NOT_AFFECTED, app, install_loc, version);
Seebug
| bulletinFamily | exploit |
| description | **Author: p0wd3r (know Chong Yu 404 security lab)** **Date: 2016-12-21** ## 0x00 vulnerability overview ### 1\. Vulnerability description [Joomla ](<https://www.joomla.org/>) to 12, on 13, released 3. 6. 5 of the [upgrade announcement](<https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html>), the upgrade fixes three security vulnerabilities, wherein the [CVE-2016-9838 ](<https://developer.joomla.org/security-centre/664-20161201-core-elevated-privileges.html>) been officially designated as high risk. According to the official Description, This is a privilege elevation vulnerability, exploit the vulnerability an attacker can change the existing user's user information, including user name, password, email and permissions group. After analysis and testing, the successful achievement of a level of user rights breakthrough, but did not achieve the vertical elevation of privileges for the administrator. ### 2\. Vulnerability Trigger the vulnerability prerequisites: 1. Website open registration function 2. The attacker knows you want to attack the user's **id ** instead of user name A successful attack after the attacker can change the existing user's user information, including user name, password, email and permissions group. ### 3\. Impact version 1.6.0 - 3.6.4 ## 0x01 vulnerability reproduction ### 1\. Environment to build docker-compose. yml: `` version: '2' services: db: image: mysql environment: \- MYSQL_ROOT_PASSWORD=hellojm \- MYSQL_DATABASE=jm app: image: joomla:3.6.3 depends_on: \- db links: \- db ports: \- "127.0.0.1:8080:80" `` Then in the docker-compose. yml the directory where the executing `docker-compose up`, access to the backstage open the registry and then configure the SMTP. ### 2\. Vulnerability analysis The official did not give a specific analysis, only to give a description: 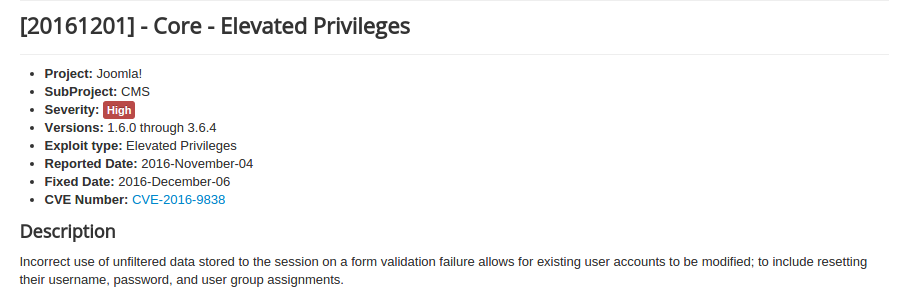 The translation here is: Table single validation failure is stored to the session of the unfiltered data not used correctly can lead to an existing user account to modify, including to reset their user name, password, and user group assignment. Because there is no specific details, so we start from a patch start, wherein the file change caught my attention: <https://github.com/joomla/joomla-cms/commit/435a2226118a4e83ecaf33431ec05f39c640c744> 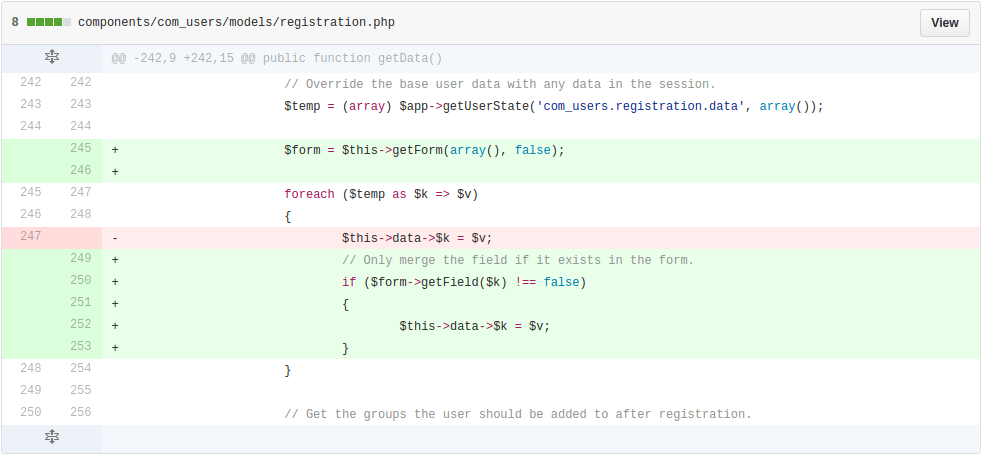 You can see where`$temp `is session data, the file and associated with the user, so it is likely that the vulnerability point. We the following through this two step analysis: 1. Looking for input points 2. Carding processing logic **1\. Looking for input points** We look for this session came from: 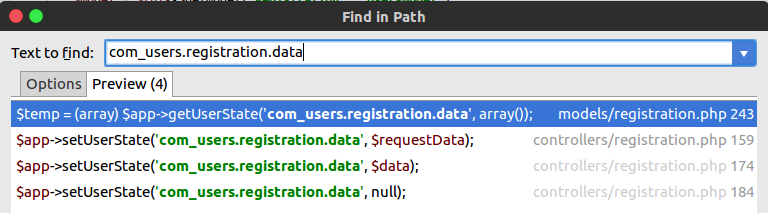 In `components/com_users/controllers/registration.php `set in `components/com_users/models/registration.php`. We see `components/com_users/controllers/registration.php `in the 108-204 line of the `register `function: ``php public function register() { ... $data = $model->validate($form, $requestData); // Check for validation errors. if ($data === false) { ... // Save the data in the session. $app->setUserState('com_users. registration. data', $requestData); ... } // Attempt to save the data. $return = $model->register($data); // Check for errors. if ($return === false) { // Save the data in the session. $app->setUserState('com_users. registration. data', $data); ... } ... } `` This two set at the session are generated in the error after the line, and the vulnerability DESCRIPTION is consistent, and`$requestData `is our original request data, and is not filtered, so the basic can be put here as our input points. We verify, first just register an user, and then re-register the same user and open the dynamic debug: 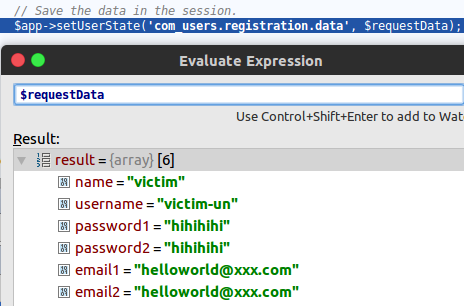 Since this user registered before, so the validation error, so the request is to write data into the session. Take the session somewhere in `components/com_users/models/registration.php `the `getData `function, the function in access the registration page will be called once we are in then you can see the session value: 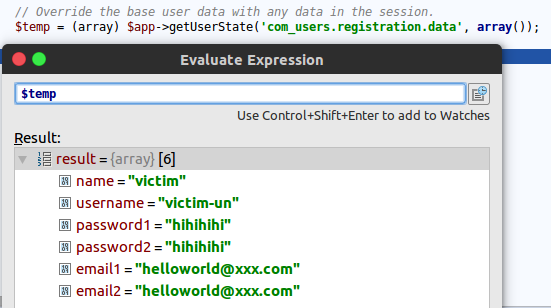 Since the stored request data, so we can also construct the request to the session to write some **additional **variables. **2\. Carding processing logic** The input point is found, let's look at our input data where to be used. We see `components/com_users/models/registration.php `the `register `function: ``php public function register($temp) { $params = JComponentHelper::getParams('com_users'); // Initialise the table with JUser. $user = new JUser; $data = (array) $this->getData(); // Merge in the registration data. foreach ($temp as $k => $v) { $data[$k] = $v; } // Prepare the data for the user object. $data['email'] = JStringPunycode::emailToPunycode($data['email1']); $data['password'] = $data['password1']; $useractivation = $params->get('useractivation'); $sendpassword = $params->get('sendpassword', 1); ... // Bind the data. if (!$ user->bind($data)) { $this->setError(JText::sprintf('COM_USERS_REGISTRATION_BIND_FAILED', $user->getError())); return false; } // Load the users plugin group. JPluginHelper::importPlugin('user'); // Store the data. if (!$ user->save()) { $this->setError(JText::sprintf('COM_USERS_REGISTRATION_SAVE_FAILED', $user->getError())); return false; } ... } `` Here call the `getData `function, and then use the request data to the`$data `assignment, and then use`$data `to the user data changes. The first follow-up`$user->bind($data)`, in `libraries/joomla/user/user.php `in No. 595-693 lines: ``php public function bind(&$array) { ... // Bind the array if (!$ this->setProperties($array)) { $this->setError(JText::_('JLIB_USER_ERROR_BIND_ARRAY')); return false; } // Make sure its an integer $this->id = (int) $this->id; return true; } `` Here according to our incoming data to the object attribute assignment, `setProperties `and no assignment restrictions. Next we look at`$user->save($data)`, in `libraries/joomla/user/user.php `in the first 706-818 line: ``php public function save($updateOnly = false) { // Create the user table object $table = $this->getTable(); $this->params = (string) $this->_params; $table->bind($this->getProperties()); ... if (!$ table->check()) { $this->setError($table->getError()); return false; } ... // Store the user data in the database $result = $table->store(); ... } `` The specific content is the`$user `attribute is bound to the`$table `and`$table `is checked, there is only filtering special symbols and a repeated username and email, if the check is passed, the data stored in the database, the stored data function in the `libraries/joomla/table/user.php `in: `php /** * Method to store a row in the database from the JTable instance properties. * * If a primary key value is set the row with that primary key value will be updated with the instance property values. * If no primary key value is set a new row will be inserted into the database with the properties from the JTable instance. * * @param boolean $updateNulls True to update fields even if they are null. * * @return boolean True on success. * * @since 11.1 */ public function store($updateNulls = false)` If the primary key exists then update, the primary key does not exist it is inserted. The whole process looked down, I found a problem: **If`$data `has `id `this attribute and its value is an existing user id, since in `the bind `and `save `and not for the attribute filter, then the final saved data will with id the primary key, which becomes the update operation, that is, by our request of data to update an existing user.** The actual operation of what we previously registered a name for the victim user, the database id is 57: the 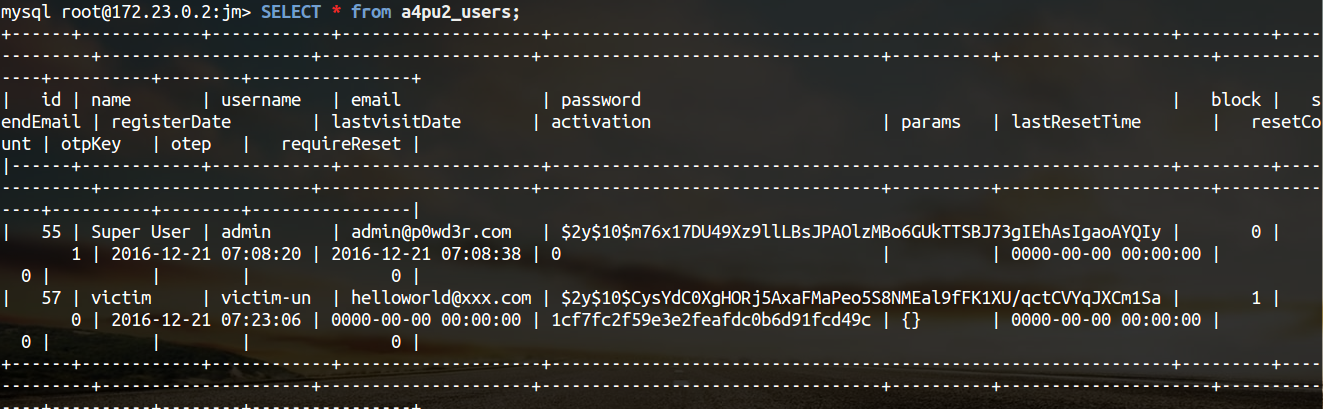 And then we with the same username then initiate a request, then intercept the package, add a value of 57 named `jform[id] `attribute: 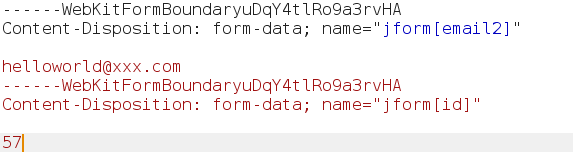 After the release due to duplicate registry which the error occurred, the program would then request data recorded to the session: 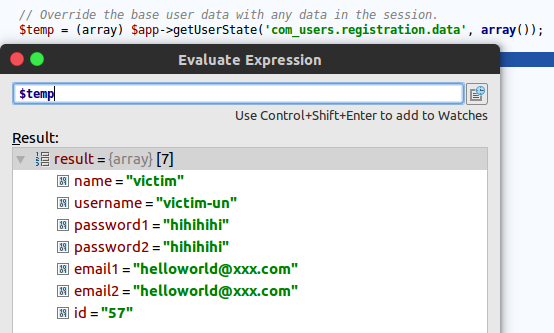 Next we send a new registration request, the user name of the mailbox are not previously registered, in the `save `function at the following breakpoints: 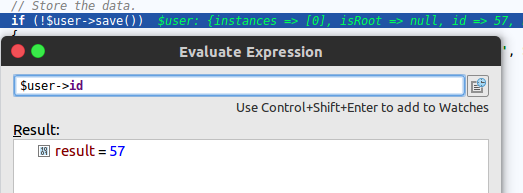 id is written into the`$user`. Then release the request to the database to see the results: 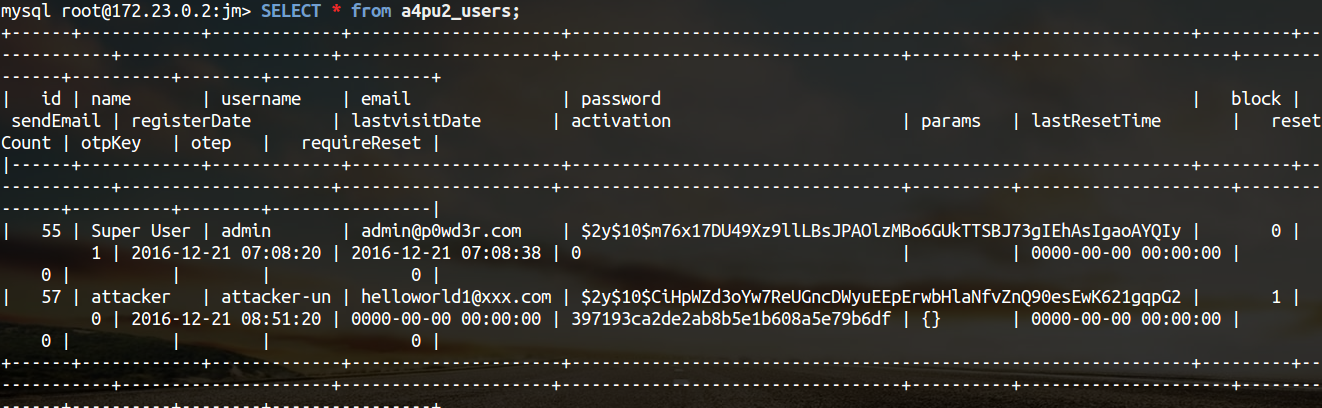 Before the victim has to be a new user attacker replaced. The entire attack process is summarized as follows: 1. Registered user A 2. Repeated registration of the user A, The request packet Plus The want to attack the user C's id 3. Registered User B 4. User B replaces the user C Above the the demo A and C are the same user Note that we can not directly send an id request to update the user, such request will be in `the validate `function is filtered out, in `components/com_users/controllers/registration.php `the `register `function: ``php public function register() { ... $data = $model->validate($form, $requestData); // Check for validation errors. if ($data === false) { ... // Save the data in the session. $app->setUserState('com_users. registration. data', $requestData); ... } // Attempt to save the data. $return = $model->register($data); ... } `` So we use the first through the `validate `trigger error to the id is written to session, and then send a normal request, in the `register `in the reading session to introduce the id, so that you can bypass `the validate`. Another point, the implementation of the attack after the attack the user's permissions will be changed to the new registered user's permission generally is Registered, and the permissions currently we cannot change, because in the `getData `function in the `groups `to do the mandatory assignment: ``php $temp = (array) $app->getUserState('com_users. registration. data', array()); ... // Get the groups the user should be added to after registration. $this->data->groups = array(); // Get the default new user group, Registered if not specified. $system = $params->get('new_usertype', 2); $this->data->groups[] = $system; `` So now just to achieve a level of elevation of Privilege, as to whether can be vertically elevated as well as how to upgrade to official instructions or is everyone's analysis. Since no technical details, everything is according to their own estimation, as there is an error, also hope to correct me :) ### 3\. Patch analysis 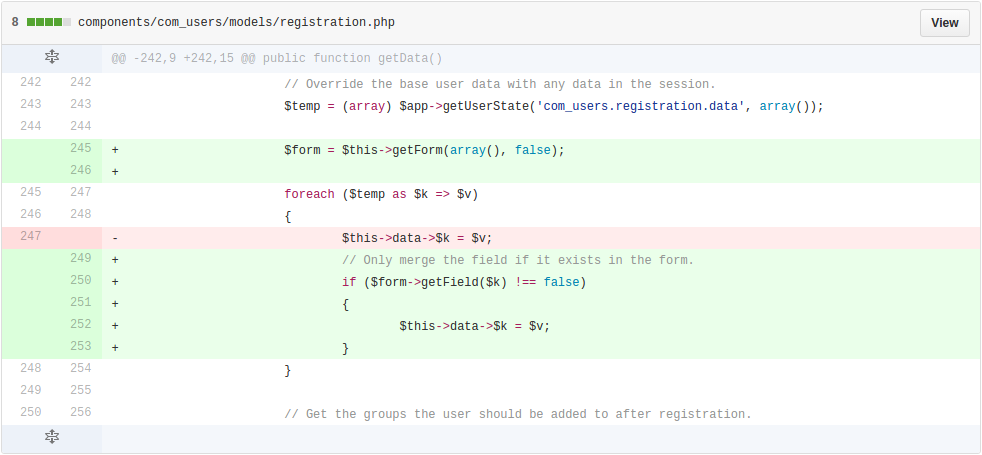 Use the session only allows the use of the specified attribute. ## 0x02 repair program Upgrade to 3. 6. 5 <https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html> ## 0x03 reference * <https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html> * <https://developer.joomla.org/security-centre/664-20161201-core-elevated-privileges.html> * <https://github.com/joomla/joomla-cms/commit/435a2226118a4e83ecaf33431ec05f39c640c744> |
| id | SSV:92574 |
| last seen | 2017-11-19 |
| modified | 2016-12-15 |
| published | 2016-12-15 |
| reporter | Root |
| title | Joomla! Core Remote Privilege Escalation Vulnerability (CVE-2016-9838) |
Related news
References
- http://www.securityfocus.com/bid/94893
- http://www.securityfocus.com/bid/94893
- https://www.exploit-db.com/exploits/41157/
- https://www.exploit-db.com/exploits/41157/
- https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html
- https://www.joomla.org/announcements/release-news/5693-joomla-3-6-5-released.html