Vulnerabilities > CVE-2016-8593 - Path Traversal vulnerability in Trendmicro Threat Discovery Appliance 2.6.1062
Attack vector
NETWORK Attack complexity
LOW Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Directory traversal vulnerability in upload.cgi in Trend Micro Threat Discovery Appliance 2.6.1062r1 and earlier allows remote authenticated users to execute arbitrary code via a .. (dot dot) in the dID parameter.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Relative Path Traversal An attacker exploits a weakness in input validation on the target by supplying a specially constructed path utilizing dot and slash characters for the purpose of obtaining access to arbitrary files or resources. An attacker modifies a known path on the target in order to reach material that is not available through intended channels. These attacks normally involve adding additional path separators (/ or \) and/or dots (.), or encodings thereof, in various combinations in order to reach parent directories or entirely separate trees of the target's directory structure.
- Directory Traversal An attacker with access to file system resources, either directly or via application logic, will use various file path specification or navigation mechanisms such as ".." in path strings and absolute paths to extend their range of access to inappropriate areas of the file system. The attacker attempts to either explore the file system for recon purposes or access directories and files that are intended to be restricted from their access. Exploring the file system can be achieved through constructing paths presented to directory listing programs, such as "ls" and 'dir', or through specially crafted programs that attempt to explore the file system. The attacker engaging in this type of activity is searching for information that can be used later in a more exploitive attack. Access to restricted directories or files can be achieved through modification of path references utilized by system applications.
- File System Function Injection, Content Based An attack of this type exploits the host's trust in executing remote content including binary files. The files are poisoned with a malicious payload (targeting the file systems accessible by the target software) by the attacker and may be passed through standard channels such as via email, and standard web content like PDF and multimedia files. The attacker exploits known vulnerabilities or handling routines in the target processes. Vulnerabilities of this type have been found in a wide variety of commercial applications from Microsoft Office to Adobe Acrobat and Apple Safari web browser. When the attacker knows the standard handling routines and can identify vulnerabilities and entry points they can be exploited by otherwise seemingly normal content. Once the attack is executed, the attackers' program can access relative directories such as C:\Program Files or other standard system directories to launch further attacks. In a worst case scenario, these programs are combined with other propagation logic and work as a virus.
- Using Slashes and URL Encoding Combined to Bypass Validation Logic This attack targets the encoding of the URL combined with the encoding of the slash characters. An attacker can take advantage of the multiple way of encoding an URL and abuse the interpretation of the URL. An URL may contain special character that need special syntax handling in order to be interpreted. Special characters are represented using a percentage character followed by two digits representing the octet code of the original character (%HEX-CODE). For instance US-ASCII space character would be represented with %20. This is often referred as escaped ending or percent-encoding. Since the server decodes the URL from the requests, it may restrict the access to some URL paths by validating and filtering out the URL requests it received. An attacker will try to craft an URL with a sequence of special characters which once interpreted by the server will be equivalent to a forbidden URL. It can be difficult to protect against this attack since the URL can contain other format of encoding such as UTF-8 encoding, Unicode-encoding, etc.
- Manipulating Input to File System Calls An attacker manipulates inputs to the target software which the target software passes to file system calls in the OS. The goal is to gain access to, and perhaps modify, areas of the file system that the target software did not intend to be accessible.
Packetstorm
| data source | https://packetstormsecurity.com/files/download/142215/tmtda261062rl-exec.txt |
| id | PACKETSTORM:142215 |
| last seen | 2017-04-20 |
| published | 2017-04-19 |
| reporter | Roberto Suggi Liverani |
| source | https://packetstormsecurity.com/files/142215/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-upload.cgi-Remote-Code-Execution.html |
| title | Trend Micro Threat Discovery Appliance 2.6.1062r1 upload.cgi Remote Code Execution |
Seebug
bulletinFamily exploit description In the last few months, I have been testing several Trend Micro products with Steven Seeley ([@steventseeley](https://twitter.com/steventseeley)). Together, we have found more than 200+ RCE (Remote Code Execution) vulnerabilities and for the first time we presented the outcome of our research at [Hack In The Box 2017 Amsterdam](https://conference.hitb.org/hitbsecconf2017ams/sessions/trending-a-micro-line-how-we-found-over-100-rce-vulnerabilities-in-trend-micro-software/) in April. The presentation is available as a [PDF](http://conference.hitb.org/hitbsecconf2017ams/materials/D1T1%20-%20Steven%20Seeley%20and%20Roberto%20Suggi%20Liverani%20-%20I%20Got%2099%20Trends%20and%20a%20%23%20Is%20All%20Of%20Them.pdf) or as a [Slideshare](https://www.slideshare.net/robertosl81/i-got-99-trends-and-a-is-all-of-them). <iframe allowfullscreen="" frameborder="0" height="470px" marginheight="0" marginwidth="0" mozallowfullscreen="" scrolling="no" src="https://www.slideshare.net/robertosl81/slideshelf" style="border: none;" webkitallowfullscreen="" width="615px"></iframe> Since it was not possible to cover all discovered vulnerabilities with a single presentation, this blog post will cover and analyze a further vulnerability that did not make it to the slides, and which affects the Trend Micro Threat Discovery Appliance (TDA) product. **CVE-2016-8584 - TDA Session Generation Authentication Bypass** This was an interesting vulnerability, discovered after observing that two consecutive login attempts against the web interface returned the same session_id token. Following this observation, our inference was that time factor played a role. After further analysis and reversing of the TDA libraries, the session management was found to be defined in the following library: /opt/TrendMicro/MinorityReport/lib/mini_httpd/utils.so Within this library, the create_session() function is of particular interest, as shown below. 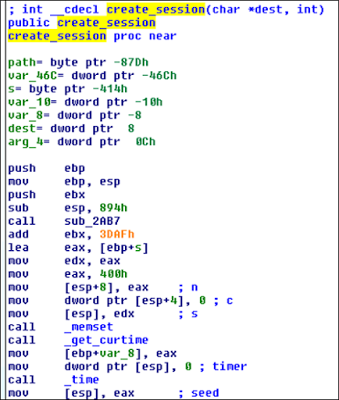 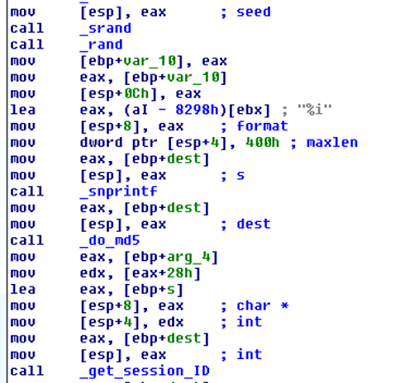 This function performs the following actions: - Gets current time - Use time as “seed” - Use srand() with above seed - MD5 hash the rest All these functions can be shortened as the following: _session_id = md5(srand(get_curtime()))_ The vulnerability is that the seed is predictable, and therefore an attacker can generate session IDs issued in the past. However, there are two conditions which affect exploitation of this vulnerability: 1) A legitimate user has to be authenticated - a session token is associated with an IP address when a user logs in 2) Attacker needs to perform the attack with the same IP address of legitimate user The second condition is not an issue in a NATed environment but in a different environment it's definitely the most significant constraint. A further conclusion is that although the attacker is able to technically predict "future" session_id tokens, there is no point in doing that, since condition (1) has to be to met first and an association between an IP address and session_id has to exist in the database. The exploit Proof-of-Concept (poc) has been published [here](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) and below a video showing the attack in action: https://www.youtube.com/embed/rwmfbvvGHDw The exploits for all the other TDA vulnerabilities that were discovered as part of this research can be found below: [CVE-2016-8584 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) Session Generation Authentication Bypass Vulnerability](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) [CVE-2016-7547 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure Vulnerability](https://gist.github.com/malerisch/b8764501d299f2ec9eb145258d404e5f) [CVE-2016-7552 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 logoff.cgi Directory Traversal Authentication Bypass Vulnerability](https://gist.github.com/malerisch/5de8b408443ee9253b3954a62a8d97b4) [CVE-2016-8585 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 admin_sys_time.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/91239147d4fceffa63006974889ef1af) [CVE-2016-8586 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 detected_potential_files.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/97c160aa4e8219c7c9ad25107444a280) [CVE-2016-8587 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/aac1ad3e6f3bfd70b35ba6538ecbff23) [CVE-2016-8588 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 hotfix_upload.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/93be2141dfc5709159468762937f2853) [CVE-2016-8589 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dae.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/3bbb6d0b235fa5af2ba6f05826fe3846) [CVE-2016-8590 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dlp.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/7b84a4bd6eee0a3a591677f421653a2e) [CVE-2016-8591 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/5dd838a723b342bb04121f29a8333e00) [CVE-2016-8592 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query_system.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/0c78e49124561524fd59d6635007eefd) [CVE-2016-8593 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/c59ab650c8e226ef22cdfbfeeee6d4ec) A Metasploit module has been developed and added to the master branch: [https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb](https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb) id SSV:92978 last seen 2017-11-19 modified 2017-04-20 published 2017-04-20 reporter Root source https://www.seebug.org/vuldb/ssvid-92978 title Trend Micro Threat Discovery Appliance - Session Generation Authentication Bypass (CVE-2016-8584) bulletinFamily exploit description Summary: There exists a post authenticated upload vulnerability that can be used to execute arbitrary code. Notes: - Since this is a busybox, getting a connectback seemed hard. So, for this particular PoC, all I did was take command, upload bd, exec, read, rinse, repeat. - You maybe can get a binded netcat using '`nc -e /bin/sh -lp 1337`' but this at times broke the cgi and the rest of the log_query_system.cgi was unstable. - Auth is VERY weak, no privilege seperation, no username required, no password policy, no protection from bruteforce attempts... Example: ``` saturn:trend_micro_threat_discovery_upload_rce mr_me$ ./poc.py (+) usage: ./poc.py <target> <pass> (+) eg: ./poc.py 172.16.175.123 admin123 saturn:trend_micro_threat_discovery_upload_rce mr_me$ ./poc.py 172.16.175.123 admin123 (+) logged in... (+) popping shell, type 'exit' to exit. $ id uid=0(root) gid=0(root) $ uname -a Linux localhost 2.6.24.4 #1 SMP Wed Oct 13 14:38:44 CST 2010 i686 unknown $ pwd /opt/TrendMicro/MinorityReport/www/cgi-bin $ exit ``` id SSV:92990 last seen 2017-11-19 modified 2017-04-21 published 2017-04-21 reporter Root source https://www.seebug.org/vuldb/ssvid-92990 title Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) upload.cgi Remote Code Execution Vulnerability Raw (CVE-2016-8593)