Vulnerabilities > CVE-2016-8591 - Permissions, Privileges, and Access Controls vulnerability in Trendmicro Threat Discovery Appliance 2.6.1062
Attack vector
NETWORK Attack complexity
LOW Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
log_query.cgi in Trend Micro Threat Discovery Appliance 2.6.1062r1 and earlier allows remote authenticated users to execute arbitrary code as the root user via shell metacharacters in the cache_id parameter.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Accessing, Modifying or Executing Executable Files An attack of this type exploits a system's configuration that allows an attacker to either directly access an executable file, for example through shell access; or in a possible worst case allows an attacker to upload a file and then execute it. Web servers, ftp servers, and message oriented middleware systems which have many integration points are particularly vulnerable, because both the programmers and the administrators must be in synch regarding the interfaces and the correct privileges for each interface.
- Leverage Executable Code in Non-Executable Files An attack of this type exploits a system's trust in configuration and resource files, when the executable loads the resource (such as an image file or configuration file) the attacker has modified the file to either execute malicious code directly or manipulate the target process (e.g. application server) to execute based on the malicious configuration parameters. Since systems are increasingly interrelated mashing up resources from local and remote sources the possibility of this attack occurring is high. The attack can be directed at a client system, such as causing buffer overrun through loading seemingly benign image files, as in Microsoft Security Bulletin MS04-028 where specially crafted JPEG files could cause a buffer overrun once loaded into the browser. Another example targets clients reading pdf files. In this case the attacker simply appends javascript to the end of a legitimate url for a pdf (http://www.gnucitizen.org/blog/danger-danger-danger/) http://path/to/pdf/file.pdf#whatever_name_you_want=javascript:your_code_here The client assumes that they are reading a pdf, but the attacker has modified the resource and loaded executable javascript into the client's browser process. The attack can also target server processes. The attacker edits the resource or configuration file, for example a web.xml file used to configure security permissions for a J2EE app server, adding role name "public" grants all users with the public role the ability to use the administration functionality. The server trusts its configuration file to be correct, but when they are manipulated, the attacker gains full control.
- Blue Boxing This type of attack against older telephone switches and trunks has been around for decades. A tone is sent by an adversary to impersonate a supervisor signal which has the effect of rerouting or usurping command of the line. While the US infrastructure proper may not contain widespread vulnerabilities to this type of attack, many companies are connected globally through call centers and business process outsourcing. These international systems may be operated in countries which have not upgraded Telco infrastructure and so are vulnerable to Blue boxing. Blue boxing is a result of failure on the part of the system to enforce strong authorization for administrative functions. While the infrastructure is different than standard current applications like web applications, there are historical lessons to be learned to upgrade the access control for administrative functions.
- Restful Privilege Elevation Rest uses standard HTTP (Get, Put, Delete) style permissions methods, but these are not necessarily correlated generally with back end programs. Strict interpretation of HTTP get methods means that these HTTP Get services should not be used to delete information on the server, but there is no access control mechanism to back up this logic. This means that unless the services are properly ACL'd and the application's service implementation are following these guidelines then an HTTP request can easily execute a delete or update on the server side. The attacker identifies a HTTP Get URL such as http://victimsite/updateOrder, which calls out to a program to update orders on a database or other resource. The URL is not idempotent so the request can be submitted multiple times by the attacker, additionally, the attacker may be able to exploit the URL published as a Get method that actually performs updates (instead of merely retrieving data). This may result in malicious or inadvertent altering of data on the server.
- Target Programs with Elevated Privileges This attack targets programs running with elevated privileges. The attacker would try to leverage a bug in the running program and get arbitrary code to execute with elevated privileges. For instance an attacker would look for programs that write to the system directories or registry keys (such as HKLM, which stores a number of critical Windows environment variables). These programs are typically running with elevated privileges and have usually not been designed with security in mind. Such programs are excellent exploit targets because they yield lots of power when they break. The malicious user try to execute its code at the same level as a privileged system call.
Packetstorm
| data source | https://packetstormsecurity.com/files/download/142217/tmtda261062rllq-exec.txt |
| id | PACKETSTORM:142217 |
| last seen | 2017-04-20 |
| published | 2017-04-20 |
| reporter | Roberto Suggi Liverani |
| source | https://packetstormsecurity.com/files/142217/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-log_query.cgi-Remote-Code-Execution.html |
| title | Trend Micro Threat Discovery Appliance 2.6.1062r1 log_query.cgi Remote Code Execution |
Seebug
bulletinFamily exploit description Summary: There exists a post authenticated command injection vulnerability that can be used to execute arbitrary code as root. Notes: - Since this is a busybox, getting a connectback seemed hard. So, for this particular PoC, all I did was exec a bind shell using netcat. - Auth is VERY weak, no privilege seperation, no username required, no password policy, no protection from bruteforce attempts... Example: ``` saturn:trend_micro_threat_discovery_log_query_rce mr_me$ ./poc.py (+) usage: ./poc.py <target> <pass> (+) eg: ./poc.py 172.16.175.123 admin123 saturn:trend_micro_threat_discovery_log_query_rce mr_me$ ./poc.py 172.16.175.123 admin123 (+) logged in... (+) starting backdoor, this will take a few secs... (+) calling backdoor! id uid=0(root) gid=0(root) uname -a Linux localhosta 2.6.24.4 #1 SMP Wed Oct 13 14:38:44 CST 2010 i686 unknown pwd /opt/TrendMicro/MinorityReport/www/cgi-bin exit ``` id SSV:92987 last seen 2017-11-19 modified 2017-04-21 published 2017-04-21 reporter Root source https://www.seebug.org/vuldb/ssvid-92987 title Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query.cgi Command Injection Remote Code Execution Vulnerability (CVE-2016-8591) bulletinFamily exploit description In the last few months, I have been testing several Trend Micro products with Steven Seeley ([@steventseeley](https://twitter.com/steventseeley)). Together, we have found more than 200+ RCE (Remote Code Execution) vulnerabilities and for the first time we presented the outcome of our research at [Hack In The Box 2017 Amsterdam](https://conference.hitb.org/hitbsecconf2017ams/sessions/trending-a-micro-line-how-we-found-over-100-rce-vulnerabilities-in-trend-micro-software/) in April. The presentation is available as a [PDF](http://conference.hitb.org/hitbsecconf2017ams/materials/D1T1%20-%20Steven%20Seeley%20and%20Roberto%20Suggi%20Liverani%20-%20I%20Got%2099%20Trends%20and%20a%20%23%20Is%20All%20Of%20Them.pdf) or as a [Slideshare](https://www.slideshare.net/robertosl81/i-got-99-trends-and-a-is-all-of-them). <iframe allowfullscreen="" frameborder="0" height="470px" marginheight="0" marginwidth="0" mozallowfullscreen="" scrolling="no" src="https://www.slideshare.net/robertosl81/slideshelf" style="border: none;" webkitallowfullscreen="" width="615px"></iframe> Since it was not possible to cover all discovered vulnerabilities with a single presentation, this blog post will cover and analyze a further vulnerability that did not make it to the slides, and which affects the Trend Micro Threat Discovery Appliance (TDA) product. **CVE-2016-8584 - TDA Session Generation Authentication Bypass** This was an interesting vulnerability, discovered after observing that two consecutive login attempts against the web interface returned the same session_id token. Following this observation, our inference was that time factor played a role. After further analysis and reversing of the TDA libraries, the session management was found to be defined in the following library: /opt/TrendMicro/MinorityReport/lib/mini_httpd/utils.so Within this library, the create_session() function is of particular interest, as shown below. 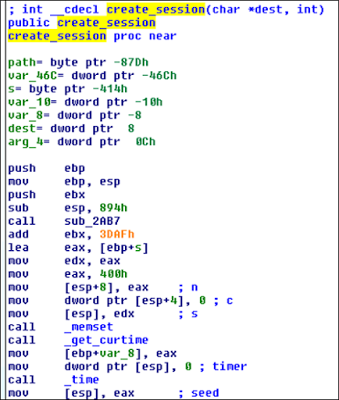 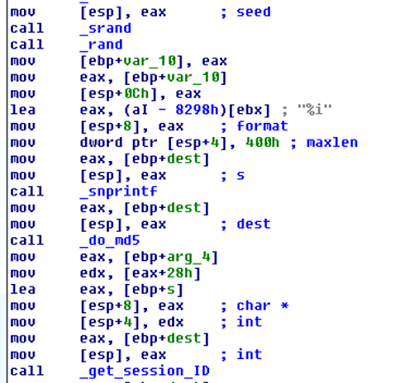 This function performs the following actions: - Gets current time - Use time as “seed” - Use srand() with above seed - MD5 hash the rest All these functions can be shortened as the following: _session_id = md5(srand(get_curtime()))_ The vulnerability is that the seed is predictable, and therefore an attacker can generate session IDs issued in the past. However, there are two conditions which affect exploitation of this vulnerability: 1) A legitimate user has to be authenticated - a session token is associated with an IP address when a user logs in 2) Attacker needs to perform the attack with the same IP address of legitimate user The second condition is not an issue in a NATed environment but in a different environment it's definitely the most significant constraint. A further conclusion is that although the attacker is able to technically predict "future" session_id tokens, there is no point in doing that, since condition (1) has to be to met first and an association between an IP address and session_id has to exist in the database. The exploit Proof-of-Concept (poc) has been published [here](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) and below a video showing the attack in action: https://www.youtube.com/embed/rwmfbvvGHDw The exploits for all the other TDA vulnerabilities that were discovered as part of this research can be found below: [CVE-2016-8584 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) Session Generation Authentication Bypass Vulnerability](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) [CVE-2016-7547 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure Vulnerability](https://gist.github.com/malerisch/b8764501d299f2ec9eb145258d404e5f) [CVE-2016-7552 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 logoff.cgi Directory Traversal Authentication Bypass Vulnerability](https://gist.github.com/malerisch/5de8b408443ee9253b3954a62a8d97b4) [CVE-2016-8585 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 admin_sys_time.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/91239147d4fceffa63006974889ef1af) [CVE-2016-8586 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 detected_potential_files.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/97c160aa4e8219c7c9ad25107444a280) [CVE-2016-8587 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/aac1ad3e6f3bfd70b35ba6538ecbff23) [CVE-2016-8588 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 hotfix_upload.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/93be2141dfc5709159468762937f2853) [CVE-2016-8589 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dae.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/3bbb6d0b235fa5af2ba6f05826fe3846) [CVE-2016-8590 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dlp.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/7b84a4bd6eee0a3a591677f421653a2e) [CVE-2016-8591 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/5dd838a723b342bb04121f29a8333e00) [CVE-2016-8592 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query_system.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/0c78e49124561524fd59d6635007eefd) [CVE-2016-8593 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/c59ab650c8e226ef22cdfbfeeee6d4ec) A Metasploit module has been developed and added to the master branch: [https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb](https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb) id SSV:92978 last seen 2017-11-19 modified 2017-04-20 published 2017-04-20 reporter Root source https://www.seebug.org/vuldb/ssvid-92978 title Trend Micro Threat Discovery Appliance - Session Generation Authentication Bypass (CVE-2016-8584)
References
- http://packetstormsecurity.com/files/142217/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-log_query.cgi-Remote-Code-Execution.html
- http://packetstormsecurity.com/files/142217/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-log_query.cgi-Remote-Code-Execution.html
- http://www.securityfocus.com/bid/98343
- http://www.securityfocus.com/bid/98343