Vulnerabilities > CVE-2016-5195 - Race Condition vulnerability in multiple products
Attack vector
LOCAL Attack complexity
HIGH Privileges required
LOW Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH local
high complexity
canonical
linux
redhat
debian
fedoraproject
paloaltonetworks
netapp
CWE-362
nessus
exploit available
Summary
Race condition in mm/gup.c in the Linux kernel 2.x through 4.x before 4.8.3 allows local users to gain privileges by leveraging incorrect handling of a copy-on-write (COW) feature to write to a read-only memory mapping, as exploited in the wild in October 2016, aka "Dirty COW."
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Leveraging Race Conditions This attack targets a race condition occurring when multiple processes access and manipulate the same resource concurrently and the outcome of the execution depends on the particular order in which the access takes place. The attacker can leverage a race condition by "running the race", modifying the resource and modifying the normal execution flow. For instance a race condition can occur while accessing a file, the attacker can trick the system by replacing the original file with his version and cause the system to read the malicious file.
- Leveraging Time-of-Check and Time-of-Use (TOCTOU) Race Conditions This attack targets a race condition occurring between the time of check (state) for a resource and the time of use of a resource. The typical example is the file access. The attacker can leverage a file access race condition by "running the race", meaning that he would modify the resource between the first time the target program accesses the file and the time the target program uses the file. During that period of time, the attacker could do something such as replace the file and cause an escalation of privilege.
Exploit-Db
description Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Escalation. CVE-2016-5195. Local exploit for Linux platform file exploits/linux/local/40839.c id EDB-ID:40839 last seen 2016-11-28 modified 2016-11-28 platform linux port published 2016-11-28 reporter Exploit-DB source https://www.exploit-db.com/download/40839/ title Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Escalation type local description Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Escalation (Write Access). CVE-2016-5195. Local exploit for Linux platform id EDB-ID:40838 last seen 2016-11-28 modified 2016-10-26 published 2016-10-26 reporter Exploit-DB source https://www.exploit-db.com/download/40838/ title Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Escalation (Write Access) description Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' /proc/self/mem Race Condition Privilege Escalation (/etc/passwd). CVE-2016-5195. Local exploit for Linux platform file exploits/linux/local/40847.cpp id EDB-ID:40847 last seen 2016-11-29 modified 2016-11-27 platform linux port published 2016-11-27 reporter Exploit-DB source https://www.exploit-db.com/download/40847/ title Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' /proc/self/mem Race Condition Privilege Escalation (/etc/passwd) type local description Linux Kernel 2.6.22 < 3.9 (x86/x64) - 'Dirty COW' Race Condition Privilege Escalation (SUID). CVE-2016-5195. Local exploit for Linux platform file exploits/linux/local/40616.c id EDB-ID:40616 last seen 2016-10-21 modified 2016-10-21 platform linux port published 2016-10-21 reporter Robin Verton source https://www.exploit-db.com/download/40616/ title Linux Kernel 2.6.22 < 3.9 (x86/x64) - 'Dirty COW' Race Condition Privilege Escalation (SUID) type local description Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' Race Condition Privilege Escalation (Write Access). CVE-2016-5195. Local exploit for Linux platform file exploits/linux/local/40611.c id EDB-ID:40611 last seen 2016-10-21 modified 2016-10-19 platform linux port published 2016-10-19 reporter Phil Oester source https://www.exploit-db.com/download/40611/ title Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' Race Condition Privilege Escalation (Write Access) type local
Nessus
NASL family Slackware Local Security Checks NASL id SLACKWARE_SSA_2016-305-01.NASL description New kernel packages are available for Slackware 14.0, 14.1, 14.2, and -current to fix a security issue. last seen 2020-06-01 modified 2020-06-02 plugin id 94438 published 2016-11-01 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94438 title Slackware 14.0 / 14.1 / 14.2 / current : kernel (SSA:2016-305-01) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2120.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6.5 Advanced Update Support and Red Hat Enterprise Linux 6.5 Telco Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94348 published 2016-10-28 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94348 title RHEL 6 : kernel (RHSA-2016:2120) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2118.NASL description An update for kernel is now available for Red Hat Enterprise Linux 7.1 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94317 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94317 title RHEL 7 : kernel (RHSA-2016:2118) (Dirty COW) NASL family Debian Local Security Checks NASL id DEBIAN_DLA-670.NASL description Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks. CVE-2015-8956 It was discovered that missing input sanitising in RFCOMM Bluetooth socket handling may result in denial of service or information leak. CVE-2016-5195 It was discovered that a race condition in the memory management code can be used for local privilege escalation. This does not affect kernels built with PREEMPT_RT enabled. CVE-2016-7042 Ondrej Kozina discovered that incorrect buffer allocation in the proc_keys_show() function may result in local denial of service. CVE-2016-7425 Marco Grassi discovered a buffer overflow in the arcmsr SCSI driver which may result in local denial of service, or potentially, arbitrary code execution. For Debian 7 last seen 2020-03-17 modified 2016-10-20 plugin id 94144 published 2016-10-20 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94144 title Debian DLA-670-1 : linux security update (Dirty COW) NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3696.NASL description Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks. - CVE-2015-8956 It was discovered that missing input sanitising in RFCOMM Bluetooth socket handling may result in denial of service or information leak. - CVE-2016-5195 It was discovered that a race condition in the memory management code can be used for local privilege escalation. - CVE-2016-7042 Ondrej Kozina discovered that incorrect buffer allocation in the proc_keys_show() function may result in local denial of service. - CVE-2016-7425 Marco Grassi discovered a buffer overflow in the arcmsr SCSI driver which may result in local denial of service, or potentially, arbitrary code execution. Additionally this update fixes a regression introduced in DSA-3616-1 causing iptables performance issues (cf. Debian Bug #831014). last seen 2020-06-01 modified 2020-06-02 plugin id 94146 published 2016-10-20 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94146 title Debian DSA-3696-1 : linux - security update (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2107.NASL description An update for kernel-rt is now available for Red Hat Enterprise MRG 2.5. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel-rt packages provide the Real Time Linux Kernel, which enables fine-tuning for systems with extremely high determinism requirements. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94315 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94315 title RHEL 6 : MRG (RHSA-2016:2107) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2659-1.NASL description This update for the Linux Kernel 3.12.55-52_45 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986377). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94326 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94326 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2659-1) (Dirty COW) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-3634.NASL description Description of changes: [2.6.39-400.286.3.el6uek] - mm, gup: close FOLL MAP_PRIVATE race (Linus Torvalds) [Orabug: 24928646] {CVE-2016-5195} last seen 2020-06-01 modified 2020-06-02 plugin id 94225 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94225 title Oracle Linux 5 / 6 : Unbreakable Enterprise kernel (ELSA-2016-3634) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2133.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6.4 Advanced Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94463 published 2016-11-02 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94463 title RHEL 6 : kernel (RHSA-2016:2133) (Dirty COW) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-3633.NASL description Description of changes: kernel-uek [3.8.13-118.13.3.el7uek] - mm, gup: close FOLL MAP_PRIVATE race (Linus Torvalds) [Orabug: 24928591] {CVE-2016-5195} last seen 2020-06-01 modified 2020-06-02 plugin id 94224 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94224 title Oracle Linux 6 / 7 : Unbreakable Enterprise kernel (ELSA-2016-3633) (Dirty COW) NASL family Huawei Local Security Checks NASL id EULEROS_SA-2019-1505.NASL description According to the versions of the kernel packages installed, the EulerOS Virtualization for ARM 64 installation on the remote host is affected by the following vulnerabilities : - The kernel package contains the Linux kernel (vmlinuz), the core of any Linux operating system. The kernel handles the basic functions of the operating system: memory allocation, process allocation, device input and output, etc.Security Fix(es):A flaw named FragmentSmack was found in the way the Linux kernel handled reassembly of fragmented IPv4 and IPv6 packets. A remote attacker could use this flaw to trigger time and calculation expensive fragment reassembly algorithm by sending specially crafted packets which could lead to a CPU saturation and hence a denial of service on the system.(CVE-2018-5391)Multiple out-of-bounds write flaws were found in the way the Cherry Cymotion keyboard driver, KYE/Genius device drivers, Logitech device drivers, Monterey Genius KB29E keyboard driver, Petalynx Maxter remote control driver, and Sunplus wireless desktop driver handled HID reports with an invalid report descriptor size. An attacker with physical access to the system could use either of these flaws to write data past an allocated memory buffer.(CVE-2014-3184)The __get_data_block function in fs/f2fs/data.c in the Linux kernel before 4.11 allows local users to cause a denial of service (integer overflow and loop) via crafted use of the open and fallocate system calls with an FS_IOC_FIEMAP ioctl.(CVE-2017-18257)netetfilter/xt_osf.c in the Linux kernel through 4.14.4 does not require the CAP_NET_ADMIN capability for add_callback and remove_callback operations. This allows local users to bypass intended access restrictions because the xt_osf_fingers data structure is shared across all network namespaces.(CVE-2017-17450)A denial of service flaw was discovered in the Linux kernel, where a race condition caused a NULL pointer dereference in the RDS socket-creation code. A local attacker could use this flaw to create a situation in which a NULL pointer crashed the kernel.(CVE-2015-7990)An issue was discovered in the Linux kernel before 4.19.9. The USB subsystem mishandles size checks during the reading of an extra descriptor, related to __usb_get_extra_descriptor in drivers/usb/core/usb.c.(CVE-2018-20169)mm/memory.c in the Linux kernel before 4.1.4 mishandles anonymous pages, which allows local users to gain privileges or cause a denial of service (page tainting) via a crafted application that triggers writing to page zero.(CVE-2015-3288)The ovl_setattr function in fs/overlayfs/inode.c in the Linux kernel through 4.3.3 attempts to merge distinct setattr operations, which allows local users to bypass intended access restrictions and modify the attributes of arbitrary overlay files via a crafted application.(CVE-2015-8660)A flaw was found in the Linux kernel where a local user with a shell account can abuse the userfaultfd syscall when using hugetlbfs. A missing size check in hugetlb_mcopy_atomic_pte could create an invalid inode variable, leading to a kernel panic.(CVE-2017-15128)An integer overflow flaw was found in the way the lzo1x_decompress_safe() function of the Linux kernel last seen 2020-04-16 modified 2019-05-13 plugin id 124828 published 2019-05-13 reporter This script is Copyright (C) 2019-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/124828 title EulerOS Virtualization for ARM 64 3.0.1.0 : kernel (EulerOS-SA-2019-1505) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2657-1.NASL description This update for the Linux Kernel 3.12.60-52_54 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94324 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94324 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2657-1) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2596-1.NASL description The SUSE Linux Enterprise 11 SP2 LTSS kernel was updated to fix one security issue. This security bug was fixed : - CVE-2016-5195: Local privilege escalation using MAP_PRIVATE. It is reportedly exploited in the wild (bsc#1004418). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94280 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94280 title SUSE SLES11 Security Update : kernel (SUSE-SU-2016:2596-1) (Dirty COW) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2016-757.NASL description A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94182 published 2016-10-21 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94182 title Amazon Linux AMI : kernel (ALAS-2016-757) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2632-1.NASL description This update for the Linux Kernel 3.12.51-52_34 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004418). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986362). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94284 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94284 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2632-1) (Dirty COW) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2018-956.NASL description Kernel address information leak in drivers/acpi/sbshc.c:acpi_smbus_hc_add() function potentially allowing KASLR bypass The acpi_smbus_hc_add function in drivers/acpi/sbshc.c in the Linux kernel, through 4.14.15, allows local users to obtain sensitive address information by reading dmesg data from an SBS HC printk call.(CVE-2018-5750) Improper sorting of GIDs in nfsd can lead to incorrect permissions being applied Linux kernel contains a Incorrect Access Control vulnerability in NFS server (nfsd) that can result in remote users reading or writing files they should not be able to via NFS. This attack appear to be exploitable via NFS server must export a filesystem with the last seen 2020-06-01 modified 2020-06-02 plugin id 106933 published 2018-02-22 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106933 title Amazon Linux AMI : kernel (ALAS-2018-956) (Dirty COW) (Spectre) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3106-1.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94155 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94155 title Ubuntu 16.04 LTS : linux vulnerability (USN-3106-1) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3106-2.NASL description USN-3106-1 fixed vulnerabilities in the Linux kernel for Ubuntu 16.04 LTS. This update provides the corresponding updates for the Linux Hardware Enablement (HWE) kernel from Ubuntu 16.04 LTS for Ubuntu 14.04 LTS. It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94156 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94156 title Ubuntu 14.04 LTS : linux-lts-xenial vulnerability (USN-3106-2) (Dirty COW) NASL family Fedora Local Security Checks NASL id FEDORA_2016-C3558808CD.NASL description The 4.7.9 stable update contains a number of important fixes across the tree. In particular, it includes a fix for CVE-2016-5195. Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-10-24 plugin id 94212 published 2016-10-24 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94212 title Fedora 23 : kernel (2016-c3558808cd) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2132.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6.2 Advanced Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94462 published 2016-11-02 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94462 title RHEL 6 : kernel (RHSA-2016:2132) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2128.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6.6 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A flaw was found in the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94454 published 2016-11-01 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94454 title RHEL 6 : kernel (RHSA-2016:2128) (Dirty COW) NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-1212.NASL description The openSUSE Leap 42.1 kernel was updated to 4.1.34, fixing bugs and security issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004418). - CVE-2016-8658: Stack-based buffer overflow in the brcmf_cfg80211_start_ap function in drivers/net/wireless/broadcom/brcm80211/brcmfmac/cfg8021 1.c in the Linux kernel allowed local users to cause a denial of service (system crash) or possibly have unspecified other impact via a long SSID Information Element in a command to a Netlink socket (bnc#1004462). - CVE-2016-7039: The IP stack in the Linux kernel allowed remote attackers to cause a denial of service (stack consumption and panic) or possibly have unspecified other impact by triggering use of the GRO path for large crafted packets, as demonstrated by packets that contain only VLAN headers, a related issue to CVE-2016-8666 (bnc#1001486). - CVE-2016-7425: The arcmsr_iop_message_xfer function in drivers/scsi/arcmsr/arcmsr_hba.c in the Linux kernel did not restrict a certain length field, which allowed local users to gain privileges or cause a denial of service (heap-based buffer overflow) via an ARCMSR_MESSAGE_WRITE_WQBUFFER control code (bnc#999932). The following non-security bugs were fixed : - 9p: use file_dentry() (bsc#1005101). - af_unix: Do not set err in unix_stream_read_generic unless there was an error (bsc#1005101). - alsa: hda - Fix superfluous HDMI jack repoll (bsc#1005101). - alsa: hda - Turn off loopback mixing as default (bsc#1001462). - apparmor: add missing id bounds check on dfa verification (bsc#1000304). - apparmor: check that xindex is in trans_table bounds (bsc#1000304). - apparmor: do not check for vmalloc_addr if kvzalloc() failed (bsc#1000304). - apparmor: do not expose kernel stack (bsc#1000304). - apparmor: ensure the target profile name is always audited (bsc#1000304). - apparmor: exec should not be returning ENOENT when it denies (bsc#1000304). - apparmor: fix audit full profile hname on successful load (bsc#1000304). - apparmor: fix change_hat not finding hat after policy replacement (bsc#1000287). - apparmor: fix disconnected bind mnts reconnection (bsc#1000304). - apparmor: fix log failures for all profiles in a set (bsc#1000304). - apparmor: fix module parameters can be changed after policy is locked (bsc#1000304). - apparmor: fix oops in profile_unpack() when policy_db is not present (bsc#1000304). - apparmor: fix put() parent ref after updating the active ref (bsc#1000304). - apparmor: fix refcount bug in profile replacement (bsc#1000304). - apparmor: fix refcount race when finding a child profile (bsc#1000304). - apparmor: fix replacement bug that adds new child to old parent (bsc#1000304). - apparmor: fix uninitialized lsm_audit member (bsc#1000304). - apparmor: fix update the mtime of the profile file on replacement (bsc#1000304). - apparmor: internal paths should be treated as disconnected (bsc#1000304). - apparmor: use list_next_entry instead of list_entry_next (bsc#1000304). - arm: orion5x: Fix legacy get_irqnr_and_base (bsc#1005101). - batman-adv: Fix memory leak on tt add with invalid vlan (bsc#1005101). - batman-adv: replace WARN with rate limited output on non-existing VLAN (bsc#1005101). - blacklist.conf: add some commits (bsc#1005101) - blacklist.conf: add unaplicable IB/uverbs commit (bsc#1005101) - blacklist.conf: Blacklist unsupported architectures - blkfront: fix an error path memory leak (luckily none so far). - blktap2: eliminate deadlock potential from shutdown path (bsc#909994). - blktap2: eliminate race from deferred work queue handling (bsc#911687). - btrfs: ensure that file descriptor used with subvol ioctls is a dir (bsc#999600). - cdc-acm: added sanity checking for probe() (bsc#993891). - cgroup: add seq_file forward declaration for struct cftype (bsc#1005101). - do last seen 2020-06-05 modified 2016-10-24 plugin id 94219 published 2016-10-24 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94219 title openSUSE Security Update : the Linux Kernel (openSUSE-2016-1212) (Dirty COW) NASL family Huawei Local Security Checks NASL id EULEROS_SA-2016-1051.NASL description According to the versions of the kernel packages installed, the EulerOS installation on the remote host is affected by the following vulnerabilities : - A race condition was found in the way the Linux kernel last seen 2020-05-06 modified 2017-05-01 plugin id 99814 published 2017-05-01 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/99814 title EulerOS 2.0 SP1 : kernel (EulerOS-SA-2016-1051) NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2016-2105.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94292 published 2016-10-27 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94292 title CentOS 6 : kernel (CESA-2016:2105) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2655-1.NASL description This update for the Linux Kernel 3.12.55-52_42 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986377). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94323 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94323 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2655-1) (Dirty COW) NASL family Scientific Linux Local Security Checks NASL id SL_20161025_IMPORTANT__KERNEL_ON_SL6_X.NASL description The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : - A race condition was found in the way the Linux kernel last seen 2020-03-18 modified 2016-10-26 plugin id 94266 published 2016-10-26 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94266 title Scientific Linux Security Update : Important: kernel on SL6.x i386/x86_64 (20161025) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2106.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6.7 Extended Update Support. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94314 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94314 title RHEL 6 : kernel (RHSA-2016:2106) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2614-1.NASL description The SUSE Linux Enterprise 11 SP3 LTSS kernel was updated to fix one security issue. This security bug was fixed : - CVE-2016-5195: Local privilege escalation using MAP_PRIVATE. It is reportedly exploited in the wild (bsc#1004418). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94281 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94281 title SUSE SLES11 Security Update : kernel (SUSE-SU-2016:2614-1) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3106-4.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94158 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94158 title Ubuntu 16.04 LTS : linux-snapdragon vulnerability (USN-3106-4) (Dirty COW) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZA-2017-110.NASL description According to the version of the vzkernel package and the readykernel-patch installed, the Virtuozzo installation on the remote host is affected by the following vulnerabilities : - dccp_disconnect() set the socket state to DCCP_CLOSED but did not properly free some of the resources associated with that socket. This could result in a use-after-free and could potentially allow an attacker to escalate their privileges. - The Linux kernel is vulnerable to a use-after-free issue. It could occur while closing a xfrm netlink socket, in xfrm_dump_policy_done. A user/process could use this flaw to potentially escalate their privileges on a system. - A flaw was found in the patches used to fix the last seen 2020-06-01 modified 2020-06-02 plugin id 105166 published 2017-12-12 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/105166 title Virtuozzo 7 : readykernel-patch (VZA-2017-110) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2592-1.NASL description The SUSE Linux Enterprise 12 SP1 kernel was updated to fix two issues. This security bug was fixed : - CVE-2016-5195: Local privilege escalation using MAP_PRIVATE. It is reportedly exploited in the wild (bsc#1004418). The update package also includes non-security fixes. See advisory for details. Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94278 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94278 title SUSE SLED12 / SLES12 Security Update : kernel (SUSE-SU-2016:2592-1) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2124.NASL description An update for kernel is now available for Red Hat Enterprise Linux 5. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94431 published 2016-10-31 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94431 title RHEL 5 : kernel (RHSA-2016:2124) (Dirty COW) NASL family SuSE Local Security Checks NASL id OPENSUSE-2020-554.NASL description This update introduces kubernetes version 1.14.1 and cri-o 1.17.1 to Leap 15.1. last seen 2020-04-30 modified 2020-04-27 plugin id 136011 published 2020-04-27 reporter This script is Copyright (C) 2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/136011 title openSUSE Security Update : kubernetes (openSUSE-2020-554) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2633-1.NASL description This update for the Linux Kernel 3.12.51-52_39 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986377). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94285 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94285 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2633-1) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2098.NASL description An update for kernel is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94230 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94230 title RHEL 7 : kernel (RHSA-2016:2098) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2585-1.NASL description The SUSE Linux Enterprise 11 SP4 kernel was updated to fix one security issue. This security bug was fixed : - CVE-2016-5195: Local privilege escalation using MAP_PRIVATE. It is reportedly exploited in the wild (bsc#1004418). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94276 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94276 title SUSE SLES11 Security Update : kernel (SUSE-SU-2016:2585-1) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2105.NASL description An update for kernel is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94313 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94313 title RHEL 6 : kernel (RHSA-2016:2105) (Dirty COW) NASL family OracleVM Local Security Checks NASL id ORACLEVM_OVMSA-2016-0149.NASL description The remote OracleVM system is missing necessary patches to address critical security updates : - mm: remove gup_flags FOLL_WRITE games from __get_user_pages (Linus Torvalds) [Orabug: 24927306] (CVE-2016-5195) - drivers/nvme: provide a module parameter for setting number of I/O queues (Shan Hai) [Orabug: 24914956] - blk-mq: improve warning for running a queue on the wrong CPU (Jens Axboe) [Orabug: 24914956] - blk-mq: fix freeze queue race (Shan Hai) [Orabug: 24914956] last seen 2020-06-01 modified 2020-06-02 plugin id 94228 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94228 title OracleVM 3.4 : Unbreakable / etc (OVMSA-2016-0149) (Dirty COW) NASL family Scientific Linux Local Security Checks NASL id SL_20161024_KERNEL_ON_SL7_X.NASL description Security Fix(es) : - A race condition was found in the way the Linux kernel last seen 2020-03-18 modified 2016-10-25 plugin id 94248 published 2016-10-25 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94248 title Scientific Linux Security Update : kernel on SL7.x x86_64 (20161024) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3105-1.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94153 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94153 title Ubuntu 14.04 LTS : linux vulnerability (USN-3105-1) (Dirty COW) NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-1227.NASL description The openSUSE 13.2 kernel was updated to receive various security and bugfixes. The following security bugs were fixed : - CVE-2015-8956: The rfcomm_sock_bind function in net/bluetooth/rfcomm/sock.c in the Linux kernel allowed local users to obtain sensitive information or cause a denial of service (NULL pointer dereference) via vectors involving a bind system call on a Bluetooth RFCOMM socket (bnc#1003925). - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004418). - CVE-2016-8658: Stack-based buffer overflow in the brcmf_cfg80211_start_ap function in drivers/net/wireless/broadcom/brcm80211/brcmfmac/cfg8021 1.c in the Linux kernel allowed local users to cause a denial of service (system crash) or possibly have unspecified other impact via a long SSID Information Element in a command to a Netlink socket (bnc#1004462). - CVE-2016-7117: Use-after-free vulnerability in the __sys_recvmmsg function in net/socket.c in the Linux kernel allowed remote attackers to execute arbitrary code via vectors involving a recvmmsg system call that is mishandled during error processing (bnc#1003077). - CVE-2016-0823: The pagemap_open function in fs/proc/task_mmu.c in the Linux kernel before 3.19.3, as used in Android 6.0.1 before 2016-03-01, allowed local users to obtain sensitive physical-address information by reading a pagemap file, aka Android internal bug 25739721 (bnc#994759). - CVE-2016-7425: The arcmsr_iop_message_xfer function in drivers/scsi/arcmsr/arcmsr_hba.c in the Linux kernel did not restrict a certain length field, which allowed local users to gain privileges or cause a denial of service (heap-based buffer overflow) via an ARCMSR_MESSAGE_WRITE_WQBUFFER control code (bnc#999932). - CVE-2016-6327: drivers/infiniband/ulp/srpt/ib_srpt.c in the Linux kernel allowed local users to cause a denial of service (NULL pointer dereference and system crash) by using an ABORT_TASK command to abort a device write operation (bnc#994748). - CVE-2016-6828: The tcp_check_send_head function in include/net/tcp.h in the Linux kernel did not properly maintain certain SACK state after a failed data copy, which allowed local users to cause a denial of service (tcp_xmit_retransmit_queue use-after-free and system crash) via a crafted SACK option (bnc#994296). - CVE-2016-5696: net/ipv4/tcp_input.c in the Linux kernel did not properly determine the rate of challenge ACK segments, which made it easier for man-in-the-middle attackers to hijack TCP sessions via a blind in-window attack (bnc#989152) - CVE-2016-6480: Race condition in the ioctl_send_fib function in drivers/scsi/aacraid/commctrl.c in the Linux kernel allowed local users to cause a denial of service (out-of-bounds access or system crash) by changing a certain size value, aka a last seen 2020-06-05 modified 2016-10-27 plugin id 94303 published 2016-10-27 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94303 title openSUSE Security Update : the Linux Kernel (openSUSE-2016-1227) (Dirty COW) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZA-2017-109.NASL description According to the version of the vzkernel package and the readykernel-patch installed, the Virtuozzo installation on the remote host is affected by the following vulnerabilities : - dccp_disconnect() set the socket state to DCCP_CLOSED but did not properly free some of the resources associated with that socket. This could result in a use-after-free and could potentially allow an attacker to escalate their privileges. - The Linux kernel is vulnerable to a use-after-free issue. It could occur while closing a xfrm netlink socket, in xfrm_dump_policy_done. A user/process could use this flaw to potentially escalate their privileges on a system. - A flaw was found in the patches used to fix the last seen 2020-06-01 modified 2020-06-02 plugin id 105165 published 2017-12-12 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/105165 title Virtuozzo 7 : readykernel-patch (VZA-2017-109) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3107-1.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94159 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94159 title Ubuntu 16.10 : linux vulnerability (USN-3107-1) (Dirty COW) NASL family OracleVM Local Security Checks NASL id ORACLEVM_OVMSA-2017-0057.NASL description The remote OracleVM system is missing necessary patches to address critical security updates : please see Oracle VM Security Advisory OVMSA-2017-0057 for details. last seen 2020-06-01 modified 2020-06-02 plugin id 99163 published 2017-04-03 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/99163 title OracleVM 3.3 : Unbreakable / etc (OVMSA-2017-0057) (Dirty COW) NASL family Amazon Linux Local Security Checks NASL id ALA_ALAS-2017-937.NASL description A flaw was found in the patches used to fix the last seen 2020-06-01 modified 2020-06-02 plugin id 105422 published 2017-12-26 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/105422 title Amazon Linux AMI : kernel (ALAS-2017-937) (Dirty COW) NASL family OracleVM Local Security Checks NASL id ORACLEVM_OVMSA-2016-0158.NASL description The remote OracleVM system is missing necessary patches to address critical security updates : - mm, gup: close FOLL MAP_PRIVATE race (Linus Torvalds) [Orabug: 24928646] (CVE-2016-5195) - HID: hiddev: validate num_values for HIDIOCGUSAGES, HIDIOCSUSAGES commands (Scott Bauer) [Orabug: 24798694] (CVE-2016-5829) - Revert last seen 2020-06-01 modified 2020-06-02 plugin id 94929 published 2016-11-17 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94929 title OracleVM 3.2 : Unbreakable / etc (OVMSA-2016-0158) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2127.NASL description An update for kernel is now available for Red Hat Enterprise Linux 5.6 Long Life. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94453 published 2016-11-01 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94453 title RHEL 5 : kernel (RHSA-2016:2127) (Dirty COW) NASL family Scientific Linux Local Security Checks NASL id SL_20161028_KERNEL_ON_SL5_X.NASL description Security Fix(es) : - A race condition was found in the way the Linux kernel last seen 2020-03-18 modified 2016-10-31 plugin id 94432 published 2016-10-31 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94432 title Scientific Linux Security Update : kernel on SL5.x i386/x86_64 (20161028) (Dirty COW) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-2124.NASL description From Red Hat Security Advisory 2016:2124 : An update for kernel is now available for Red Hat Enterprise Linux 5. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94429 published 2016-10-31 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94429 title Oracle Linux 5 : kernel (ELSA-2016-2124) (Dirty COW) NASL family F5 Networks Local Security Checks NASL id F5_BIGIP_SOL10558632.NASL description Race condition in mm/gup.c in the Linux kernel 2.x through 4.x before 4.8.3 allows local users to gain privileges by leveraging incorrect handling of a copy-on-write (COW) feature to write to a read-only memory mapping, as exploited in the wild in October 2016, aka last seen 2020-03-17 modified 2017-02-22 plugin id 97306 published 2017-02-22 reporter This script is Copyright (C) 2017-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/97306 title F5 Networks BIG-IP : Linux privilege-escalation vulnerability (K10558632) (Dirty COW) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-2098.NASL description From Red Hat Security Advisory 2016:2098 : An update for kernel is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94247 published 2016-10-25 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94247 title Oracle Linux 7 : kernel (ELSA-2016-2098) (Dirty COW) NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2016-2098.NASL description An update for kernel is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94254 published 2016-10-26 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94254 title CentOS 7 : kernel (CESA-2016:2098) (Dirty COW) NASL family Fedora Local Security Checks NASL id FEDORA_2016-DB4B75B352.NASL description The 4.7.9 stable update contains a number of important fixes across the tree. In particular, it includes a fix for CVE-2016-5195. ---- The 4.7.8 update contains a number of important fixes across the tree. Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-10-24 plugin id 94213 published 2016-10-24 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94213 title Fedora 24 : kernel (2016-db4b75b352) (Dirty COW) NASL family Huawei Local Security Checks NASL id EULEROS_SA-2019-1494.NASL description According to the versions of the kernel packages installed, the EulerOS Virtualization installation on the remote host is affected by the following vulnerabilities : - A vulnerability was found in Linux kernel. There is an information leak in file last seen 2020-03-19 modified 2019-05-15 plugin id 125100 published 2019-05-15 reporter This script is Copyright (C) 2019-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/125100 title EulerOS Virtualization 3.0.1.0 : kernel (EulerOS-SA-2019-1494) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2658-1.NASL description This update for the Linux Kernel 3.12.60-52_49 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986377). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94325 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94325 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2658-1) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3104-1.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94152 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94152 title Ubuntu 12.04 LTS : linux vulnerability (USN-3104-1) (Dirty COW) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZA-2017-111.NASL description According to the version of the vzkernel package and the readykernel-patch installed, the Virtuozzo installation on the remote host is affected by the following vulnerabilities : - dccp_disconnect() set the socket state to DCCP_CLOSED but did not properly free some of the resources associated with that socket. This could result in a use-after-free and could potentially allow an attacker to escalate their privileges. - The Linux kernel is vulnerable to a use-after-free issue. It could occur while closing a xfrm netlink socket, in xfrm_dump_policy_done. A user/process could use this flaw to potentially escalate their privileges on a system. - A flaw was found in the patches used to fix the last seen 2020-06-01 modified 2020-06-02 plugin id 105167 published 2017-12-12 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/105167 title Virtuozzo 7 : readykernel-patch (VZA-2017-111) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3107-2.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94249 published 2016-10-25 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94249 title Ubuntu 16.10 : linux-raspi2 vulnerability (USN-3107-2) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3105-2.NASL description USN-3105-1 fixed vulnerabilities in the Linux kernel for Ubuntu 14.04 LTS. This update provides the corresponding updates for the Linux Hardware Enablement (HWE) kernel from Ubuntu 14.04 LTS for Ubuntu 12.04 LTS. It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94154 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94154 title Ubuntu 12.04 LTS : linux-lts-trusty vulnerability (USN-3105-2) (Dirty COW) NASL family CentOS Local Security Checks NASL id CENTOS_RHSA-2016-2124.NASL description An update for kernel is now available for Red Hat Enterprise Linux 5. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94409 published 2016-10-31 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94409 title CentOS 5 : kernel (CESA-2016:2124) (Dirty COW) NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-1211.NASL description The openSUSE 13.1 kernel was updated to fix bugs and security issues. The following security bugs were fixed : - CVE-2016-8666: The IP stack in the Linux kernel allowed remote attackers to cause a denial of service (stack consumption and panic) or possibly have unspecified other impact by triggering use of the GRO path for packets with tunnel stacking, as demonstrated by interleaved IPv4 headers and GRE headers, a related issue to CVE-2016-7039 (bnc#1001486). - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004418). The following non-security bugs were fixed : - sched/core: Fix a race between try_to_wake_up() and a woken up task (bsc#1002165, bsc#1001419). - sched/core: Fix an SMP ordering race in try_to_wake_up() vs. schedule() (bnc#1001419). - tunnels: Do not apply GRO to multiple layers of encapsulation (bsc#1001486). last seen 2020-06-05 modified 2016-10-25 plugin id 94239 published 2016-10-25 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94239 title openSUSE Security Update : the Linux Kernel (openSUSE-2016-1211) (Dirty COW) NASL family Amazon Linux Local Security Checks NASL id AL2_ALAS-2018-956.NASL description Stack-based out-of-bounds read via vmcall instruction Linux kernel compiled with the KVM virtualization (CONFIG_KVM) support is vulnerable to an out-of-bounds read access issue. It could occur when emulating vmcall instructions invoked by a guest. A guest user/process could use this flaw to disclose kernel memory bytes.(CVE-2017-17741) drivers/block/loop.c mishandles lo_release serialization allowing denial-of-service A flaw was found in the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 109127 published 2018-04-18 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/109127 title Amazon Linux 2 : kernel (ALAS-2018-956) (Dirty COW) (Spectre) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2110.NASL description An update for kernel-rt is now available for Red Hat Enterprise Linux 7. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel-rt packages provide the Real Time Linux Kernel, which enables fine-tuning for systems with extremely high determinism requirements. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94316 published 2016-10-27 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94316 title RHEL 7 : kernel-rt (RHSA-2016:2110) (Dirty COW) NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-3106-3.NASL description It was discovered that a race condition existed in the memory manager of the Linux kernel when handling copy-on-write breakage of private read-only memory mappings. A local attacker could use this to gain administrative privileges. Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94157 published 2016-10-20 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94157 title Ubuntu 16.04 LTS : linux-raspi2 vulnerability (USN-3106-3) (Dirty COW) NASL family Virtuozzo Local Security Checks NASL id VIRTUOZZO_VZA-2018-004.NASL description According to the version of the vzkernel package and the readykernel-patch installed, the Virtuozzo installation on the remote host is affected by the following vulnerabilities : - A vulnerability was found in DCCP socket handling code. dccp_disconnect() set the socket state to DCCP_CLOSED but did not properly free some of the resources associated with that socket. This could result in a use-after-free and could potentially allow an attacker to escalate their privileges. - The Linux kernel is vulnerable to a use-after-free issue. It could occur while closing a xfrm netlink socket, in xfrm_dump_policy_done. A user/process could use this flaw to potentially escalate their privileges on a system. - The function get_net_ns_by_id() does not check the net.count value when processing a peer network, which could lead to double free and memory corruption. An unprivileged local user could use this vulnerability to crash the system. - If the system uses iptables and there are iptables rules with TCPMSS action there, a remote attacker could cause a denial of service (use-after-free in tcpmss_mangle_packet function leading to memory corruption) or possibly have unspecified other impact by sending specially crafted network packets. - A flaw was found in the patches used to fix the last seen 2020-06-01 modified 2020-06-02 plugin id 106052 published 2018-01-16 reporter This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/106052 title Virtuozzo 7 : readykernel-patch (VZA-2018-004) NASL family Huawei Local Security Checks NASL id EULEROS_SA-2019-1529.NASL description According to the versions of the kernel packages installed, the EulerOS Virtualization for ARM 64 installation on the remote host is affected by the following vulnerabilities : - The ipx_recvmsg function in net/ipx/af_ipx.c in the Linux kernel before 3.12.4 updates a certain length value without ensuring that an associated data structure has been initialized, which allows local users to obtain sensitive information from kernel memory via a (1) recvfrom, (2) recvmmsg, or (3) recvmsg system call.(CVE-2013-7268i1/4%0 - The move_pages system call in mm/migrate.c in the Linux kernel doesn last seen 2020-03-19 modified 2019-05-14 plugin id 124982 published 2019-05-14 reporter This script is Copyright (C) 2019-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/124982 title EulerOS Virtualization for ARM 64 3.0.1.0 : kernel (EulerOS-SA-2019-1529) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-2105.NASL description From Red Hat Security Advisory 2016:2105 : An update for kernel is now available for Red Hat Enterprise Linux 6. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94264 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94264 title Oracle Linux 6 : kernel (ELSA-2016-2105) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2593-1.NASL description The SUSE Linux Enterprise 12 GA LTSS kernel was updated to fix two issues. This security bug was fixed : - CVE-2016-5195: Local privilege escalation using MAP_PRIVATE. It is reportedly exploited in the wild (bsc#1004418). The update package also includes non-security fixes. See advisory for details. Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94279 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94279 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2593-1) (Dirty COW) NASL family Oracle Linux Local Security Checks NASL id ORACLELINUX_ELSA-2016-3632.NASL description Description of changes: kernel-uek [4.1.12-61.1.16.el7uek] - mm: remove gup_flags FOLL_WRITE games from __get_user_pages() (Linus Torvalds) [Orabug: 24927306] {CVE-2016-5195} [4.1.12-61.1.15.el7uek] - drivers/nvme: provide a module parameter for setting number of I/O queues (Shan Hai) [Orabug: 24914956] - blk-mq: improve warning for running a queue on the wrong CPU (Jens Axboe) [Orabug: 24914956] - blk-mq: fix freeze queue race (Shan Hai) [Orabug: 24914956] last seen 2020-06-01 modified 2020-06-02 plugin id 94223 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94223 title Oracle Linux 6 / 7 : Unbreakable Enterprise kernel (ELSA-2016-3632) (Dirty COW) NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-2126.NASL description An update for kernel is now available for Red Hat Enterprise Linux 5.9 Long Life. Red Hat Product Security has rated this update as having a security impact of Important. A Common Vulnerability Scoring System (CVSS) base score, which gives a detailed severity rating, is available for each vulnerability from the CVE link(s) in the References section. The kernel packages contain the Linux kernel, the core of any Linux operating system. Security Fix(es) : * A race condition was found in the way the Linux kernel last seen 2020-06-01 modified 2020-06-02 plugin id 94452 published 2016-11-01 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94452 title RHEL 5 : kernel (RHSA-2016:2126) (Dirty COW) NASL family Fedora Local Security Checks NASL id FEDORA_2016-C8A0C7EECE.NASL description The 4.8.3 stable update contains a number of important fixes across the tree. In particular, it includes a fix for CVE-2016-5195. Note that Tenable Network Security has extracted the preceding description block directly from the Fedora update system website. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-11-15 plugin id 94861 published 2016-11-15 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94861 title Fedora 25 : kernel (2016-c8a0c7eece) (Dirty COW) NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-2636-1.NASL description This update for the Linux Kernel 3.12.51-52_31 fixes several issues. The following security bugs were fixed : - CVE-2016-5195: A local privilege escalation using MAP_PRIVATE was fixed, which is reportedly exploited in the wild (bsc#1004419). - CVE-2016-4997: The compat IPT_SO_SET_REPLACE and IP6T_SO_SET_REPLACE setsockopt implementations in the netfilter subsystem in the Linux kernel allowed local users to gain privileges or cause a denial of service (memory corruption) by leveraging in-container root access to provide a crafted offset value that triggers an unintended decrement (bsc#986377). Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-01 modified 2020-06-02 plugin id 94286 published 2016-10-26 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94286 title SUSE SLES12 Security Update : kernel (SUSE-SU-2016:2636-1) (Dirty COW) NASL family OracleVM Local Security Checks NASL id ORACLEVM_OVMSA-2016-0150.NASL description The remote OracleVM system is missing necessary patches to address critical security updates : - mm, gup: close FOLL MAP_PRIVATE race (Linus Torvalds) [Orabug: 24928591] (CVE-2016-5195) last seen 2020-06-01 modified 2020-06-02 plugin id 94229 published 2016-10-24 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94229 title OracleVM 3.3 : Unbreakable / etc (OVMSA-2016-0150) (Dirty COW)
Packetstorm
data source https://packetstormsecurity.com/files/download/139923/dirtydirtycow-escalate.txt id PACKETSTORM:139923 last seen 2016-12-05 published 2016-11-28 reporter FireFart source https://packetstormsecurity.com/files/139923/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html title Linux Kernel Dirty COW PTRACE_POKEDATA Privilege Escalation data source https://packetstormsecurity.com/files/download/139922/dirtycowptrace-escalate.txt id PACKETSTORM:139922 last seen 2016-12-05 published 2016-11-25 reporter Phil Oester source https://packetstormsecurity.com/files/139922/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html title Linux Kernel Dirty COW PTRACE_POKEDATA Privilege Escalation
Redhat
| advisories |
| ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| rpms |
|
Saint
| bid | 93793 |
| description | Linux Dirty COW Local File Overwrite |
| id | misc_linuxkernel |
| title | linux_dirty_cow_local_file_overwrite |
| type | tool |
Seebug
bulletinFamily exploit description The “Dirty COW” vulnerability ([CVE-2016–5195](https://medium.com/r/?url=https%3A%2F%2Fcve.mitre.org%2Fcgi-bin%2Fcvename.cgi%3Fname%3DCVE-2016-5195)) is one of the most hyped and branded vulnerabilities published. Every Linux version from the last decade, including Android, desktops and servers was vulnerable. The impact was vast — millions of users could be compromised easily and reliably, bypassing common exploit defenses. Plenty of information was published about the vulnerability, but its patch was not analyzed in detail. We at Bindecy were interested to study the patch and all of its implications. Surprisingly, despite the enormous publicity the bug had received, we discovered that the patch was incomplete. ### "Dirty COW" recap First, we need a full understanding of the original Dirty COW exploit. We’ll assume basic understanding of the Linux memory manager. We won’t recover the original gory details, as talented people have [already done](https://medium.com/r/?url=https%3A%2F%2Fchao-tic.github.io%2Fblog%2F2017%2F05%2F24%2Fdirty-cow) so. The original vulnerability was in the `get_user_pages` function. This function is used to get the physical pages behind virtual addresses in user processes. The caller has to specify what kind of actions he intends to perform on these pages (touch, write, lock, etc…), so the memory manager could prepare the pages accordingly. Specifically, when planning to perform a write action on a page inside a private mapping, the page may need to go through a COW (Copy-On-Write) cycle — the original, “read-only” page is copied to a new page which is writable. The original page could be “privileged” — it could be mapped in other processes as well, and might even be written back to the disk after it’s modified. Let’s now take a look at the relevant code in `__get_user_pages`: ``` static long __get_user_pages(struct task_struct *tsk, struct mm_struct *mm, unsigned long start, unsigned long nr_pages, unsigned int gup_flags, struct page **pages, struct vm_area_struct **vmas, int *nonblocking) { // ... do { struct page *page; unsigned int foll_flags = gup_flags; // ... vma = find_extend_vma(mm, start); // ... retry: // ... cond_resched(); page = follow_page_mask(vma, start, foll_flags, &page_mask); if (!page) { int ret; ret = faultin_page(tsk, vma, start, &foll_flags, nonblocking); switch (ret) { case 0: goto retry; case -EFAULT: case -ENOMEM: case -EHWPOISON: return i ? i : ret; case -EBUSY: return i; case -ENOENT: goto next_page; } BUG(); } // ... next_page: // ... nr_pages -= page_increm; } while (nr_pages); return i; } ``` The `while` loop’s goal is to fetch each page in the requested page range. Each page has to be faulted in until our requirements are satisfied — that’s what the `retry` label is used for. `follow_page_mask`’s role is to scan the page tables to get the physical page for the given address (while taking into account the PTE permissions), or fail in case the request can’t be satisfied. During `follow_page_mask`’s operation the PTE’s spinlock is acquired— this guarantees the physical page won’t be released before we grab a reference. `faultin_page` requests the memory manager to handle the fault in the given address with the specified permissions (also under the PTE’s spinlock). Note that after a successful call to `faultin_page` the lock is released — it’s not guaranteed that `follow_page_mask` will succeed in the next retry; another piece of code might have messed with our page. The original vulnerable code resided at the end of faultin_page: ``` if ((ret & VM_FAULT_WRITE) && !(vma->vm_flags & VM_WRITE)) *flags &= ~FOLL_WRITE; ``` The reason for removing the `FOLL_WRITE` flag is to take into account the case the `FOLL_FORCE` flag is applied on a read-only VMA (when the `VM_MAYWRITE` flag is set in the VMA). In that case, the `pte_maybe_mkwrite` function won’t set the write bit, however the faulted-in page is indeed ready for writing. If the page went through a COW cycle (marked by the `VM_FAULT_WRITE` flag) while performing faultin_page and the VMA is not writable, the `FOLL_WRITE flag` is removed from the next attempt to access the page — only read permissions will be requested. If the first `follow_page_mask` fails because the page was read-only or not present, we’ll try to fault it in. Now let’s imagine that during that time, until the next attempt to get the page, we’ll get rid of the COW version (e.g. by using `madvise(MADV_DONTNEED)`). The next call to `faultin_page` will be made without the `FOLL_WRITE` flag, so we’ll get the read-only version of the page from the page cache. Now, the next call to `follow_page_mask` will also happen without the `FOLL_WRITE` flag, so it will return the privileged read-only page — as opposed to the caller’s original request for a writable version of the page. Basically, the aforementioned flow is the Dirty COW vulnerability — it allows us to write to the read-only privileged version of a page. The following fix was introduced in `faultin_page`: ``` if ((ret & VM_FAULT_WRITE) && !(vma->vm_flags & VM_WRITE)) *flags |= FOLL_COW; // Instead of *flags &= ~FOLL_WRITE; ``` And a new function, which is called by `follow_page_mask`, was added: ``` /* * FOLL_FORCE can write to even unwritable pte's, but only * after we've gone through a COW cycle and they are dirty. */ static inline bool can_follow_write_pte(pte_t pte, unsigned int flags) { return pte_write(pte) || ((flags & FOLL_FORCE) && (flags & FOLL_COW) && pte_dirty(pte)); } ``` Instead of reducing the requested permissions, `get_user_pages` now remembers the fact the we went through a COW cycle. On the next iteration, we would be able to get a read-only page for a write operation only if the `FOLL_FORCE` and `FOLL_COW` flags are specified, and that the PTE is marked as dirty. This patch assumes that the read-only privileged copy of a page will never have a PTE pointing to it with the dirty bit on — a reasonable assumption… or is it? ### Transparent Huge Pages (THP) Normally, Linux usually uses a 4096-bytes long pages. In order to enable the system to manage large amounts of memory, we can either increase the number of page table entries, or use larger pages. We focus on the second method, which is implemented in Linux by using [huge pages](https://medium.com/r/?url=https%3A%2F%2Fgithub.com%2Florenzo-stoakes%2Flinux-vm-notes%2Fblob%2Fmaster%2Fsections%2Ftrans-huge-pages.md). A huge page is a 2MB long page. One of the ways to utilize this feature is through the Transparent Huge Pages mechanism. While there are other ways to get huge pages, they are outside of our scope. The kernel will attempt to satisfy relevant memory allocations using huge pages. THP are swappable and “breakable” (i.e. can be split into normal 4096-bytes pages), and can be used in anonymous, shmem and tmpfs mappings (the latter two are true only in newer kernel versions). Usually (depending on the compilation flags and the machine configuration) the default THP support is for anonymous mapping only. Shmem and tmpfs support can be turned on manually, and in general THP support can be turned on and off while the system is running by writing to some kernel’s special files. An important optimization opportunity is to coalesce normal pages into huge pages. A special daemon called khugepaged scans constantly for possible candidate pages that could be merged into huge pages. Obviously, to be a candidate, a VMA must cover a whole, aligned 2MB memory range. THP is implemented by turning on the `_PAGE_PSE` bit of the PMD (Page Medium Directory, one level above the PTE level). The PMD thus points to a 2MB physical page, instead of a directory of PTEs. Each time the page tables are scanned, the PMDs must be checked with the `pmd_trans_huge` function, so we can decide whether the PMD points to a pfn or a directory of PTEs. On some architectures, huge PUDs (Page Upper Directory) exist as well, resulting in 1GB pages. THP is supported since kernel 2.6.38. On most Android devices the THP subsystem is not enabled. ### The bug Delving into the Dirty COW patch code that deals with THP, we can see that the same logic of `can_follow_write_pte` was applied to huge PMDs. A matching function called `can_follow_write_pm`d was added: ``` static inline bool can_follow_write_pmd(pmd_t pmd, unsigned int flags) { return pmd_write(pmd) || ((flags & FOLL_FORCE) && (flags & FOLL_COW) && pmd_dirty(pmd)); } ``` However, in the huge PMD case, a page can be marked dirty without going through a COW cycle, using the `touch_pmd` function: ``` static void touch_pmd(struct vm_area_struct *vma, unsigned long addr, pmd_t *pmd) { pmd_t _pmd; /* * We should set the dirty bit only for FOLL_WRITE but for now * the dirty bit in the pmd is meaningless. And if the dirty * bit will become meaningful and we'll only set it with * FOLL_WRITE, an atomic set_bit will be required on the pmd to * set the young bit, instead of the current set_pmd_at. */ _pmd = pmd_mkyoung(pmd_mkdirty(*pmd)); if (pmdp_set_access_flags(vma, addr & HPAGE_PMD_MASK, pmd, _pmd, 1)) update_mmu_cache_pmd(vma, addr, pmd); } ``` This function is reached by `follow_page_mask`, which will be called each time `get_user_pages` tries to get a huge page. Obviously, the comment is incorrect and nowadays the dirty bit is NOT meaningless. In particular — when using `get_user_pages` to read a huge page, that page will be marked dirty without going through a COW cycle, and `can_follow_write_pmd`’s logic is now broken. At this point, exploiting the bug is straightforward — we can use a similar pattern of the original Dirty COW race. This time, after we get rid of the copied version of the page, we have to fault the original page twice — first to make it present, and then to turn on the dirty bit. Now comes the inevitable question — how bad is this? ### Bug implications In order to exploit the bug, we have to choose an interesting read-only huge page as a target for the writing. The only constraint is that we need to be able to fetch it after it’s discarded with `madvise(MADV_DONTNEED)`. Anonymous huge pages that were inherited from a parent process after a `fork` are a valuable target, however once they are discarded they are lost for good — we can’t fetch them again. We found two interesting targets that should not be written into: * The huge zero page * Sealed (read-only) huge pages ### The zero page When issuing a read fault on an anonymous mapping before it was ever written, we get a special physical page called the zero page. This optimization prevents the system from having to allocate multiple zeroed out pages in the system, which might never be written to. Thus, the exact same zero page is mapped in many different processes, which have different security levels. The same principle applies to huge pages as well — there’s no need to create another huge page if no write fault has occurred yet — a special page called the huge zero page will be mapped, instead. Note that this feature can be turned off as well. ### THP, shmem and sealed files shmem and [tmpfs](https://medium.com/r/?url=https%3A%2F%2Fwww.kernel.org%2Fdoc%2FDocumentation%2Ffilesystems%2Ftmpfs.txt) files can be mapped using THP as well. shmem files can be created using the [memfd_create](https://medium.com/r/?url=http%3A%2F%2Fman7.org%2Flinux%2Fman-pages%2Fman2%2Fmemfd_create.2.html) syscall, or by mmaping anonymous shared mappings. tmpfs files can be created using the mount point of the tmpfs (usually `/dev/shm`). Both can be mapped with huge pages, depending on the system configuration. shmem files can be sealed — sealing a file restricts the set of operations allowed on the file in question. This mechanism allows processes that don’t trust each other to communicate via shared memory without having to take extra measures to deal with unexpected manipulations of the shared memory region (see `man memfd_create()` for more info). Three types of seals exist - * `F_SEAL_SHRINK`: file size cannot be reduced * `F_SEAL_GROW`: file size cannot be increased * `F_SEAL_WRITE`: file content cannot be modified These seals can be added to the shmem file using the `fcntl` syscall. ### POC Our POC demonstrates overwriting the huge zero page. Overwriting shmem should be equally possible and would lead to an alternative exploit path. Note that after the first write page-fault to the zero page, it will be replaced with a new fresh (and zeroed) THP. Using this primitive, we successfully crash several processes. A likely consequence of overwriting the huge zero page is having improper initial values inside large BSS sections. A common vulnerable pattern would be using the zero value as an indicator that a global variable hasn’t been initialized yet. The following crash example demonstrates that pattern. In this example, the JS Helper thread of Firefox makes a `NULL`-deref, probably because the boolean pointed by `%rdx` erroneously says the object was initialized: ``` Thread 10 "JS Helper" received signal SIGSEGV, Segmentation fault. [Switching to Thread 0x7fffe2aee700 (LWP 14775)] 0x00007ffff13233d3 in ?? () from /opt/firefox/libxul.so (gdb) i r rax 0x7fffba7ef080 140736322269312 rbx 0x0 0 rcx 0x22 34 rdx 0x7fffba7ef080 140736322269312 rsi 0x400000000 17179869184 rdi 0x7fffe2aede10 140736996498960 rbp 0x0 0x0 rsp 0x7fffe2aede10 0x7fffe2aede10 r8 0x20000 131072 r9 0x7fffba900000 140736323387392 r10 0x7fffba700000 140736321290240 r11 0x7fffe2aede50 140736996499024 r12 0x1 1 r13 0x7fffba7ef090 140736322269328 r14 0x2 2 r15 0x7fffe2aee700 140736996501248 rip 0x7ffff13233d3 0x7ffff13233d3 eflags 0x10246 [ PF ZF IF RF ] cs 0x33 51 ss 0x2b 43 ds 0x0 0 es 0x0 0 fs 0x0 0 gs 0x0 0 (gdb) x/10i $pc-0x10 0x7ffff13233c3: mov %rax,0x10(%rsp) 0x7ffff13233c8: mov 0x8(%rdx),%rbx 0x7ffff13233cc: mov %rbx,%rbp 0x7ffff13233cf: and $0xfffffffffffffffe,%rbp => 0x7ffff13233d3: mov 0x0(%rbp),%eax 0x7ffff13233d6: and $0x28,%eax 0x7ffff13233d9: cmp $0x28,%eax 0x7ffff13233dc: je 0x7ffff1323440 0x7ffff13233de: mov %rbx,%r13 0x7ffff13233e1: and $0xfffffffffff00000,%r13 (gdb) x/10w $rdx 0x7fffba7ef080: 0x41414141 0x00000000 0x00000000 0x00000000 0x7fffba7ef090: 0xeef93bba 0x00000000 0xda95dd80 0x00007fff 0x7fffba7ef0a0: 0x778513f1 0x00000000 ``` This is another crash example — gdb crashes while loading the symbols for a Firefox debugging session: ``` (gdb) r Starting program: /opt/firefox/firefox [Thread debugging using libthread_db enabled] Using host libthread_db library "/lib/x86_64-linux-gnu/libthread_db.so.1". Program received signal SIGSEGV, Segmentation fault. 0x0000555555825487 in eq_demangled_name_entry (a=0x4141414141414141, b=<optimized out>) at symtab.c:697 697 return strcmp (da->mangled, db->mangled) == 0; (gdb) i s #0 0x0000555555825487 in eq_demangled_name_entry (a=0x4141414141414141, b=<optimized out>) at symtab.c:697 #1 0x0000555555955203 in htab_find_slot_with_hash (htab=0x555557008e60, element=element@entry=0x7fffffffdb00, hash=4181413748, insert=insert@entry=INSERT) at ./hashtab.c:659 #2 0x0000555555955386 in htab_find_slot (htab=<optimized out>, element=element@entry=0x7fffffffdb00, insert=insert@entry=INSERT) at ./hashtab.c:703 #3 0x00005555558273e5 in symbol_set_names (gsymbol=gsymbol@entry=0x5555595b3778, linkage_name=linkage_name@entry=0x7ffff2ac5254 "_ZN7mozilla3dom16HTMLTableElement11CreateTHeadEv", len=len@entry=48, copy_name=copy_name@entry=0, objfile=<optimized out>) at symtab.c:818 #4 0x00005555557d186f in minimal_symbol_reader::record_full (this=0x7fffffffdce0, this@entry=0x1768bd6, name=<optimized out>, name@entry=0x7ffff2ac5254 "_ZN7mozilla3dom16HTMLTableElement11CreateTHeadEv", name_len=<optimized out>, copy_name=copy_name@entry=48, address=24546262, ms_type=ms_type@entry=mst_file_text, section=13) at minsyms.c:1010 #5 0x00005555556959ec in record_minimal_symbol (reader=..., name=name@entry=0x7ffff2ac5254 "_ZN7mozilla3dom16HTMLTableElement11CreateTHeadEv", name_len=<optimized out>, copy_name=copy_name@entry=false, address=<optimized out>, address@entry=24546262, ms_type=ms_type@entry=mst_file_text, bfd_section=<optimized out>, objfile=0x555557077860) at elfread.c:209 #6 0x0000555555696ac6 in elf_symtab_read (reader=..., objfile=objfile@entry=0x555557077860, type=type@entry=0, number_of_symbols=number_of_symbols@entry=365691, symbol_table=symbol_table@entry=0x7ffff6a6d020, copy_names=copy_names@entry=false) at elfread.c:462 #7 0x00005555556970c4 in elf_read_minimal_symbols (symfile_flags=<optimized out>, ei=0x7fffffffdcd0, objfile=0x555557077860) at elfread.c:1084 #8 elf_symfile_read (objfile=0x555557077860, symfile_flags=...) at elfread.c:1194 #9 0x000055555581f559 in read_symbols (objfile=objfile@entry=0x555557077860, add_flags=...) at symfile.c:861 #10 0x000055555581f00b in syms_from_objfile_1 (add_flags=..., addrs=0x555557101b00, objfile=0x555557077860) at symfile.c:1062 #11 syms_from_objfile (add_flags=..., addrs=0x555557101b00, objfile=0x555557077860) at symfile.c:1078 #12 symbol_file_add_with_addrs (abfd=<optimized out>, name=name@entry=0x55555738c1d0 "/opt/firefox/libxul.so", add_flags=..., addrs=addrs@entry=0x555557101b00, flags=..., parent=parent@entry=0x0) at symfile.c:1177 #13 0x000055555581f63d in symbol_file_add_from_bfd (abfd=<optimized out>, name=name@entry=0x55555738c1d0 "/opt/firefox/libxul.so", add_flags=..., addrs=addrs@entry=0x555557101b00, flags=..., parent=parent@entry=0x0) at symfile.c:1268 #14 0x000055555580b256 in solib_read_symbols (so=so@entry=0x55555738bfc0, flags=...) at solib.c:712 #15 0x000055555580be9b in solib_add (pattern=pattern@entry=0x0, from_tty=from_tty@entry=0, readsyms=1) at solib.c:1016 #16 0x000055555580c678 in handle_solib_event () at solib.c:1301 #17 0x00005555556f9db4 in bpstat_stop_status (aspace=0x555555ff5670, bp_addr=bp_addr@entry=140737351961185, ptid=..., ws=ws@entry=0x7fffffffe1d0) at breakpoint.c:5712 #18 0x00005555557ad1ef in handle_signal_stop (ecs=0x7fffffffe1b0) at infrun.c:5963 #19 0x00005555557aec8a in handle_inferior_event_1 (ecs=0x7fffffffe1b0) at infrun.c:5392 #20 handle_inferior_event (ecs=ecs@entry=0x7fffffffe1b0) at infrun.c:5427 #21 0x00005555557afd57 in fetch_inferior_event (client_data=<optimized out>) at infrun.c:3932 #22 0x000055555576ade5 in gdb_wait_for_event (block=block@entry=0) at event-loop.c:859 #23 0x000055555576aef7 in gdb_do_one_event () at event-loop.c:322 #24 0x000055555576b095 in gdb_do_one_event () at ./common/common-exceptions.h:221 #25 start_event_loop () at event-loop.c:371 #26 0x00005555557c3938 in captured_command_loop (data=data@entry=0x0) at main.c:325 #27 0x000055555576d243 in catch_errors (func=func@entry=0x5555557c3910 <captured_command_loop(void*)>, func_args=func_args@entry=0x0, errstring=errstring@entry=0x555555a035da "", mask=mask@entry=RETURN_MASK_ALL) at exceptions.c:236 #28 0x00005555557c49ae in captured_main (data=<optimized out>) at main.c:1150 #29 gdb_main (args=<optimized out>) at main.c:1160 #30 0x00005555555ed628 in main (argc=<optimized out>, argv=<optimized out>) at gdb.c:32 (gdb) list 692 const struct demangled_name_entry *da 693 = (const struct demangled_name_entry *) a; 694 const struct demangled_name_entry *db 695 = (const struct demangled_name_entry *) b; 696 697 return strcmp (da->mangled, db->mangled) == 0; 698 } 699 700 /* Create the hash table used for demangled names. Each hash entry is 701 a pair of strings; one for the mangled name and one for the demangled (gdb) ``` Link to our [POC](https://medium.com/r/?url=https%3A%2F%2Fgithub.com%2Fbindecy%2FHugeDirtyCowPOC) ### Summary This bug demonstrates the importance of patch auditing in the security development life-cycle. As the Dirty COW case and other [past cases](https://medium.com/r/?url=https%3A%2F%2Fsektioneins.de%2Fblog%2F16-09-05-pegasus-ios-kernel-vulnerability-explained-part-2.html) show, even hyped vulnerabilities may get incomplete patches. The situation is not reserved for closed source software only; open source software suffers just as much. Feel free to comment with any question or idea about the issue ### Disclosure timeline The initial report was on the 22.11.17 to the kernel and distros mailing lists. The response was immediate and professional with a [patch](https://medium.com/r/?url=https%3A%2F%2Fgithub.com%2Ftorvalds%2Flinux%2Fcommit%2Fa8f97366452ed491d13cf1e44241bc0b5740b1f0) ready in a few days. The patch fixes the touch_pmd function to set the dirty bit of the PMD entry only when the caller asks for write access. Thanks to the Security team and the distros for their time and effort of maintaining a high standard of security. * 22.11.17 — Initial report to [email protected] and [email protected] * 22.11.17 — CVE-2017–1000405 was assigned * 27.11.17 — Patch was committed to mainline kernel * 29.11.17 — Public announcement id SSV:96908 last seen 2017-12-25 modified 2017-11-30 published 2017-11-30 reporter Root source https://www.seebug.org/vuldb/ssvid-96908 title "Huge Dirty COW" (CVE-2017–1000405) bulletinFamily exploit description ### Summary A race condition was found in the way the Linux kernel's memory subsystem handled the copy-on-write (COW) breakage of private read-only memory mappings. All the information we have so far is included in this page. The bug has existed since around 2.6.22 (released in 2007) and was fixed on Oct 18, 2016. There are proof of concept available [here](https://github.com/dirtycow/dirtycow.github.io/wiki/PoCs). ### Video Explanation 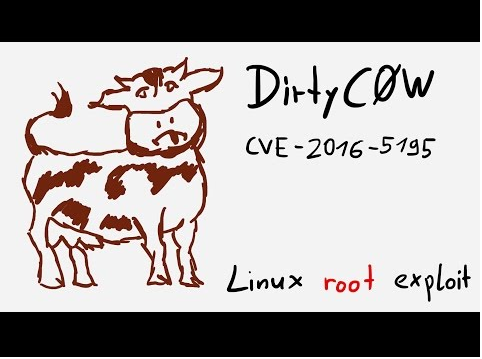 [link](https://www.youtube.com/watch?v=kEsshExn7aE) ### Impact * An unprivileged local user could use this flaw to gain write access to otherwise read-only memory mappings and thus increase their privileges on the system. * This flaw allows an attacker with a local system account to modify on-disk binaries, bypassing the standard permission mechanisms that would prevent modification without an appropriate permission set. ### Analysis ``` faultin_page handle_mm_fault __handle_mm_fault handle_pte_fault do_fault <- pte is not present do_cow_fault <- FAULT_FLAG_WRITE alloc_set_pte maybe_mkwrite(pte_mkdirty(entry), vma) <- mark the page dirty but keep it RO # Returns with 0 and retry follow_page_mask follow_page_pte (flags & FOLL_WRITE) && !pte_write(pte) <- retry fault faultin_page handle_mm_fault __handle_mm_fault handle_pte_fault FAULT_FLAG_WRITE && !pte_write do_wp_page PageAnon() <- this is CoWed page already reuse_swap_page <- page is exclusively ours wp_page_reuse maybe_mkwrite <- dirty but RO again ret = VM_FAULT_WRITE ((ret & VM_FAULT_WRITE) && !(vma->vm_flags & VM_WRITE)) <- we drop FOLL_WRITE #Returns with 0 and retry as a read fault cond_resched -> different thread will now unmap via madvise follow_page_mask !pte_present && pte_none faultin_page handle_mm_fault __handle_mm_fault handle_pte_fault do_fault <- pte is not present do_read_fault <- this is a read fault and we will get pagecache page! ``` ### How * The In The Wild exploit relied on writing to /proc/self/mem on one side of the race. * ptrace(PTRACE_POKEDATA) can write to readonly mappings. * The attack relies on racing the madvise(MADV_DONTNEED) system call while having the page of the executable mmapped in memory. ### Commit messages commit 4ceb5db9757aaeadcf8fbbf97d76bd42aa4df0d6 Author: Linus Torvalds <[email protected]> Date: Mon Aug 1 11:14:49 2005 -0700 Fix get_user_pages() race for write access There's no real guarantee that handle_mm_fault() will always be able to break a COW situation - if an update from another thread ends up modifying the page table some way, handle_mm_fault() may end up requiring us to re-try the operation. That's normally fine, but get_user_pages() ended up re-trying it as a read, and thus a write access could in theory end up losing the dirty bit or be done on a page that had not been properly COW'ed. This makes get_user_pages() always retry write accesses as write accesses by making "follow_page()" require that a writable follow has the dirty bit set. That simplifies the code and solves the race: if the COW break fails for some reason, we'll just loop around and try again. commit 19be0eaffa3ac7d8eb6784ad9bdbc7d67ed8e619 Author: Linus Torvalds <[email protected]> Date: Thu Oct 13 20:07:36 2016 GMT This is an ancient bug that was actually attempted to be fixed once (badly) by me eleven years ago in commit 4ceb5db9757a ("Fix get_user_pages() race for write access") but that was then undone due to problems on s390 by commit f33ea7f404e5 ("fix get_user_pages bug"). In the meantime, the s390 situation has long been fixed, and we can now fix it by checking the pte_dirty() bit properly (and do it better). The s390 dirty bit was implemented in abf09bed3cce ("s390/mm: implement software dirty bits") which made it into v3.9. Earlier kernels will have to look at the page state itself. Also, the VM has become more scalable, and what used a purely theoretical race back then has become easier to trigger. To fix it, we introduce a new internal FOLL_COW flag to mark the "yes, we already did a COW" rather than play racy games with FOLL_WRITE that is very fundamental, and then use the pte dirty flag to validate that the FOLL_COW flag is still valid. ### References https://dirtycow.ninja https://github.com/dirtycow/dirtycow.github.io/wiki/PoCs https://bugzilla.redhat.com/show_bug.cgi?id=1384344 https://access.redhat.com/security/vulnerabilities/2706661 https://plus.google.com/+KeesCook/posts/UUaXm3PcQ4n https://twitter.com/nelhage/status/789196293629370368 https://bugzilla.suse.com/show_bug.cgi?id=1004418#c14 id SSV:92488 last seen 2017-11-19 modified 2016-10-22 published 2016-10-22 reporter Root source https://www.seebug.org/vuldb/ssvid-92488 title Linux kernel 2.6.22 < 3.9 elevation of privilege vulnerability (Dirty COW)
The Hacker News
id THN:B571C1AAA8CDDC10150ABA0BF22B19E6 last seen 2018-01-27 modified 2016-10-25 published 2016-10-20 reporter Swati Khandelwal source https://thehackernews.com/2016/10/linux-kernel-exploit.html title Dirty COW — Critical Linux Kernel Flaw Being Exploited in the Wild id THN:6681D64EFC53E13356AF1184CE1D6024 last seen 2019-04-09 modified 2019-04-09 published 2019-04-09 reporter The Hacker News source https://thehackernews.com/2019/04/exodus-ios-malware.html title 'Exodus' Surveillance Malware Found Targeting Apple iOS Users id THN:1F1264BE105BBA74057A5E702B33D71F last seen 2018-01-27 modified 2017-09-26 published 2017-09-26 reporter Swati Khandelwal source https://thehackernews.com/2017/09/dirty-cow-android-malware.html title First Android Malware Found Exploiting Dirty COW Linux Flaw to Gain Root Privileges
Related news
References
- http://www.openwall.com/lists/oss-security/2022/08/08/7
- http://www.openwall.com/lists/oss-security/2022/08/08/8
- http://www.openwall.com/lists/oss-security/2022/08/08/8
- http://www.openwall.com/lists/oss-security/2022/08/09/4
- http://www.openwall.com/lists/oss-security/2022/08/09/4
- http://www.openwall.com/lists/oss-security/2022/08/15/1
- http://www.openwall.com/lists/oss-security/2022/08/15/1
- http://www.oracle.com/technetwork/security-advisory/cpujul2018-4258247.html
- http://www.oracle.com/technetwork/security-advisory/cpujul2018-4258247.html
- http://www.securityfocus.com/archive/1/539611/100/0/threaded
- http://www.securityfocus.com/archive/1/539611/100/0/threaded
- http://www.securityfocus.com/archive/1/540252/100/0/threaded
- http://www.securityfocus.com/archive/1/540252/100/0/threaded
- http://www.securityfocus.com/archive/1/540344/100/0/threaded
- http://www.securityfocus.com/archive/1/540344/100/0/threaded
- http://www.securityfocus.com/archive/1/540736/100/0/threaded
- http://www.securityfocus.com/archive/1/540736/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/539611/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/539611/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540252/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540252/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540344/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540344/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540736/100/0/threaded
- http://www.securityfocus.com/archive/1/archive/1/540736/100/0/threaded
- http://www.securityfocus.com/bid/93793
- http://www.securityfocus.com/bid/93793
- http://www.securitytracker.com/id/1037078
- http://www.securitytracker.com/id/1037078
- http://www.ubuntu.com/usn/USN-3104-1
- http://www.ubuntu.com/usn/USN-3104-1
- http://www.ubuntu.com/usn/USN-3104-2
- http://www.ubuntu.com/usn/USN-3104-2
- http://www.ubuntu.com/usn/USN-3105-1
- http://www.ubuntu.com/usn/USN-3105-1
- http://www.ubuntu.com/usn/USN-3105-2
- http://www.ubuntu.com/usn/USN-3105-2
- http://www.ubuntu.com/usn/USN-3106-1
- http://www.ubuntu.com/usn/USN-3106-1
- http://www.ubuntu.com/usn/USN-3106-2
- http://www.ubuntu.com/usn/USN-3106-2
- http://www.ubuntu.com/usn/USN-3106-3
- http://www.ubuntu.com/usn/USN-3106-3
- http://www.ubuntu.com/usn/USN-3106-4
- http://www.ubuntu.com/usn/USN-3106-4
- http://www.ubuntu.com/usn/USN-3107-1
- http://www.ubuntu.com/usn/USN-3107-1
- http://www.ubuntu.com/usn/USN-3107-2
- http://www.ubuntu.com/usn/USN-3107-2
- https://access.redhat.com/errata/RHSA-2017:0372
- https://access.redhat.com/errata/RHSA-2017:0372
- https://access.redhat.com/security/cve/cve-2016-5195
- https://access.redhat.com/security/cve/cve-2016-5195
- https://access.redhat.com/security/vulnerabilities/2706661
- https://access.redhat.com/security/vulnerabilities/2706661
- https://bto.bluecoat.com/security-advisory/sa134
- https://bto.bluecoat.com/security-advisory/sa134
- https://bugzilla.redhat.com/show_bug.cgi?id=1384344
- https://bugzilla.redhat.com/show_bug.cgi?id=1384344
- https://bugzilla.suse.com/show_bug.cgi?id=1004418
- https://bugzilla.suse.com/show_bug.cgi?id=1004418
- https://dirtycow.ninja
- https://dirtycow.ninja
- https://github.com/dirtycow/dirtycow.github.io/wiki/PoCs
- https://github.com/dirtycow/dirtycow.github.io/wiki/PoCs
- https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetails
- https://github.com/dirtycow/dirtycow.github.io/wiki/VulnerabilityDetails
- https://github.com/torvalds/linux/commit/19be0eaffa3ac7d8eb6784ad9bdbc7d67ed8e619
- https://github.com/torvalds/linux/commit/19be0eaffa3ac7d8eb6784ad9bdbc7d67ed8e619
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-c05352241
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-c05352241
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03707en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03707en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03722en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03722en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03742en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03742en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03761en_us
- https://h20566.www2.hpe.com/hpsc/doc/public/display?docLocale=en_US&docId=emr_na-hpesbgn03761en_us
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05341463
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05341463
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05347541
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05347541
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05352241
- https://h20566.www2.hpe.com/portal/site/hpsc/public/kb/docDisplay?docId=emr_na-c05352241
- https://help.ecostruxureit.com/display/public/UADCO8x/StruxureWare+Data+Center+Operation+Software+Vulnerability+Fixes
- https://help.ecostruxureit.com/display/public/UADCO8x/StruxureWare+Data+Center+Operation+Software+Vulnerability+Fixes
- https://kc.mcafee.com/corporate/index?page=content&id=SB10176
- https://kc.mcafee.com/corporate/index?page=content&id=SB10176
- https://kc.mcafee.com/corporate/index?page=content&id=SB10177
- https://kc.mcafee.com/corporate/index?page=content&id=SB10177
- https://kc.mcafee.com/corporate/index?page=content&id=SB10222
- https://kc.mcafee.com/corporate/index?page=content&id=SB10222
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/E7M62SRP6CZLJ4ZXCRZKV4WPLQBSR7DT/
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/E7M62SRP6CZLJ4ZXCRZKV4WPLQBSR7DT/
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/NWMDLBWMGZKFHMRJ7QUQVCERP5QHDB6W/
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/NWMDLBWMGZKFHMRJ7QUQVCERP5QHDB6W/
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/W3APRVDVPDBXLH4DC5UKZVCR742MJIM3/
- https://lists.fedoraproject.org/archives/list/package-announce%40lists.fedoraproject.org/message/W3APRVDVPDBXLH4DC5UKZVCR742MJIM3/
- https://people.canonical.com/~ubuntu-security/cve/2016/CVE-2016-5195.html
- https://people.canonical.com/~ubuntu-security/cve/2016/CVE-2016-5195.html
- https://security.netapp.com/advisory/ntap-20161025-0001/
- https://security.netapp.com/advisory/ntap-20161025-0001/
- https://security.paloaltonetworks.com/CVE-2016-5195
- https://security.paloaltonetworks.com/CVE-2016-5195
- https://security-tracker.debian.org/tracker/CVE-2016-5195
- https://security-tracker.debian.org/tracker/CVE-2016-5195
- https://source.android.com/security/bulletin/2016-11-01.html
- https://source.android.com/security/bulletin/2016-11-01.html
- https://source.android.com/security/bulletin/2016-12-01.html
- https://source.android.com/security/bulletin/2016-12-01.html
- https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20181107-vcsd
- https://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20181107-vcsd
- https://www.arista.com/en/support/advisories-notices/security-advisories/1753-security-advisory-0026
- https://www.arista.com/en/support/advisories-notices/security-advisories/1753-security-advisory-0026
- https://www.exploit-db.com/exploits/40611/
- https://www.exploit-db.com/exploits/40611/
- https://www.exploit-db.com/exploits/40616/
- https://www.exploit-db.com/exploits/40616/
- https://www.exploit-db.com/exploits/40839/
- https://www.exploit-db.com/exploits/40839/
- https://www.exploit-db.com/exploits/40847/
- https://www.exploit-db.com/exploits/40847/
- https://www.kb.cert.org/vuls/id/243144
- https://www.kb.cert.org/vuls/id/243144
- http://fortiguard.com/advisory/FG-IR-16-063
- http://fortiguard.com/advisory/FG-IR-16-063
- http://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=19be0eaffa3ac7d8eb6784ad9bdbc7d67ed8e619
- http://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=19be0eaffa3ac7d8eb6784ad9bdbc7d67ed8e619
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10770
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10770
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10774
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10774
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10807
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10807
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00034.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00034.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00035.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00035.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00036.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00036.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00038.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00038.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00039.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00039.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00040.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00040.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00045.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00045.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00048.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00048.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00049.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00049.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00050.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00050.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00051.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00051.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00052.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00052.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00053.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00053.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00054.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00054.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00055.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00055.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00056.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00056.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00057.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00057.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00058.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00058.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00063.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00063.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00064.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00064.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00065.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00065.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00066.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00066.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00067.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00067.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00072.html
- http://lists.opensuse.org/opensuse-security-announce/2016-10/msg00072.html
- http://lists.opensuse.org/opensuse-security-announce/2016-12/msg00033.html
- http://lists.opensuse.org/opensuse-security-announce/2016-12/msg00033.html
- http://lists.opensuse.org/opensuse-security-announce/2016-12/msg00100.html
- http://lists.opensuse.org/opensuse-security-announce/2016-12/msg00100.html
- http://lists.opensuse.org/opensuse-security-announce/2020-04/msg00041.html
- http://lists.opensuse.org/opensuse-security-announce/2020-04/msg00041.html
- http://packetstormsecurity.com/files/139277/Kernel-Live-Patch-Security-Notice-LSN-0012-1.html
- http://packetstormsecurity.com/files/139277/Kernel-Live-Patch-Security-Notice-LSN-0012-1.html
- http://packetstormsecurity.com/files/139286/DirtyCow-Linux-Kernel-Race-Condition.html
- http://packetstormsecurity.com/files/139286/DirtyCow-Linux-Kernel-Race-Condition.html
- http://packetstormsecurity.com/files/139287/DirtyCow-Local-Root-Proof-Of-Concept.html
- http://packetstormsecurity.com/files/139287/DirtyCow-Local-Root-Proof-Of-Concept.html
- http://packetstormsecurity.com/files/139922/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html
- http://packetstormsecurity.com/files/139922/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html
- http://packetstormsecurity.com/files/139923/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html
- http://packetstormsecurity.com/files/139923/Linux-Kernel-Dirty-COW-PTRACE_POKEDATA-Privilege-Escalation.html
- http://packetstormsecurity.com/files/142151/Kernel-Live-Patch-Security-Notice-LSN-0021-1.html
- http://packetstormsecurity.com/files/142151/Kernel-Live-Patch-Security-Notice-LSN-0021-1.html
- http://rhn.redhat.com/errata/RHSA-2016-2098.html
- http://rhn.redhat.com/errata/RHSA-2016-2098.html
- http://rhn.redhat.com/errata/RHSA-2016-2105.html
- http://rhn.redhat.com/errata/RHSA-2016-2105.html
- http://rhn.redhat.com/errata/RHSA-2016-2106.html
- http://rhn.redhat.com/errata/RHSA-2016-2106.html
- http://rhn.redhat.com/errata/RHSA-2016-2107.html
- http://rhn.redhat.com/errata/RHSA-2016-2107.html
- http://rhn.redhat.com/errata/RHSA-2016-2110.html
- http://rhn.redhat.com/errata/RHSA-2016-2110.html
- http://rhn.redhat.com/errata/RHSA-2016-2118.html
- http://rhn.redhat.com/errata/RHSA-2016-2118.html
- http://rhn.redhat.com/errata/RHSA-2016-2120.html
- http://rhn.redhat.com/errata/RHSA-2016-2120.html
- http://rhn.redhat.com/errata/RHSA-2016-2124.html
- http://rhn.redhat.com/errata/RHSA-2016-2124.html
- http://rhn.redhat.com/errata/RHSA-2016-2126.html
- http://rhn.redhat.com/errata/RHSA-2016-2126.html
- http://rhn.redhat.com/errata/RHSA-2016-2127.html
- http://rhn.redhat.com/errata/RHSA-2016-2127.html
- http://rhn.redhat.com/errata/RHSA-2016-2128.html
- http://rhn.redhat.com/errata/RHSA-2016-2128.html
- http://rhn.redhat.com/errata/RHSA-2016-2132.html
- http://rhn.redhat.com/errata/RHSA-2016-2132.html
- http://rhn.redhat.com/errata/RHSA-2016-2133.html
- http://rhn.redhat.com/errata/RHSA-2016-2133.html
- http://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20161026-linux
- http://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20161026-linux
- http://www.debian.org/security/2016/dsa-3696
- http://www.debian.org/security/2016/dsa-3696
- http://www.huawei.com/en/psirt/security-advisories/huawei-sa-20161207-01-dirtycow-en
- http://www.huawei.com/en/psirt/security-advisories/huawei-sa-20161207-01-dirtycow-en
- http://www.kernel.org/pub/linux/kernel/v4.x/ChangeLog-4.8.3
- http://www.kernel.org/pub/linux/kernel/v4.x/ChangeLog-4.8.3
- http://www.openwall.com/lists/oss-security/2016/10/21/1
- http://www.openwall.com/lists/oss-security/2016/10/21/1
- http://www.openwall.com/lists/oss-security/2016/10/26/7
- http://www.openwall.com/lists/oss-security/2016/10/26/7
- http://www.openwall.com/lists/oss-security/2016/10/27/13
- http://www.openwall.com/lists/oss-security/2016/10/27/13
- http://www.openwall.com/lists/oss-security/2016/10/30/1
- http://www.openwall.com/lists/oss-security/2016/10/30/1
- http://www.openwall.com/lists/oss-security/2016/11/03/7
- http://www.openwall.com/lists/oss-security/2016/11/03/7
- http://www.openwall.com/lists/oss-security/2022/03/07/1
- http://www.openwall.com/lists/oss-security/2022/03/07/1
- http://www.openwall.com/lists/oss-security/2022/08/08/1
- http://www.openwall.com/lists/oss-security/2022/08/08/1
- http://www.openwall.com/lists/oss-security/2022/08/08/2
- http://www.openwall.com/lists/oss-security/2022/08/08/2
- http://www.openwall.com/lists/oss-security/2022/08/08/7