Vulnerabilities > CVE-2016-4758 - Information Exposure vulnerability in Apple Safari
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
NONE Availability impact
NONE Summary
WebKit in Apple iOS before 10, iTunes before 12.5.1 on Windows, and Safari before 10 does not properly restrict access to the location variable, which allows remote attackers to obtain sensitive information via a crafted web site.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Subverting Environment Variable Values The attacker directly or indirectly modifies environment variables used by or controlling the target software. The attacker's goal is to cause the target software to deviate from its expected operation in a manner that benefits the attacker.
- Footprinting An attacker engages in probing and exploration activity to identify constituents and properties of the target. Footprinting is a general term to describe a variety of information gathering techniques, often used by attackers in preparation for some attack. It consists of using tools to learn as much as possible about the composition, configuration, and security mechanisms of the targeted application, system or network. Information that might be collected during a footprinting effort could include open ports, applications and their versions, network topology, and similar information. While footprinting is not intended to be damaging (although certain activities, such as network scans, can sometimes cause disruptions to vulnerable applications inadvertently) it may often pave the way for more damaging attacks.
- Exploiting Trust in Client (aka Make the Client Invisible) An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Browser Fingerprinting An attacker carefully crafts small snippets of Java Script to efficiently detect the type of browser the potential victim is using. Many web-based attacks need prior knowledge of the web browser including the version of browser to ensure successful exploitation of a vulnerability. Having this knowledge allows an attacker to target the victim with attacks that specifically exploit known or zero day weaknesses in the type and version of the browser used by the victim. Automating this process via Java Script as a part of the same delivery system used to exploit the browser is considered more efficient as the attacker can supply a browser fingerprinting method and integrate it with exploit code, all contained in Java Script and in response to the same web page request by the browser.
- Session Credential Falsification through Prediction This attack targets predictable session ID in order to gain privileges. The attacker can predict the session ID used during a transaction to perform spoofing and session hijacking.
Nessus
NASL family Peer-To-Peer File Sharing NASL id ITUNES_12_5_1_BANNER.NASL description The version of Apple iTunes running on the remote Windows host is prior to 12.5.1. It is, therefore, affected by multiple vulnerabilities : - A remote code execution vulnerability exists due to improper handling of error prototypes. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to execute arbitrary code. (CVE-2016-4728) - An information disclosure vulnerability exists in WebKit due to a permission issue caused by improper handling of the location variable. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to disclose sensitive information. (CVE-2016-4758) - Multiple memory corruption errors exist in WebKit due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit these issues, by convincing a user to visit a maliciously crafted website, to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-4759, CVE-2016-4762, CVE-2016-4764, CVE-2016-4765, CVE-2016-4766, CVE-2016-4767, CVE-2016-4768, CVE-2016-4769) - A rebinding flaw exists in WebKit due to a failure to restrict HTTP/0.9 responses to default ports and cancel resource loads if a document is loaded with a different HTTP protocol version. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to access non-HTTP services. (CVE-2016-4760) - A security bypass vulnerability exists in WebKit in the WKWebView component due to a failure to properly verify X.509 certificates from HTTPS servers. A man-in-the-middle attacker can exploit this, via a specially crafted certificate, to spoof servers and disclose or manipulate network traffic. (CVE-2016-4763) Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 94971 published 2016-11-18 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94971 title Apple iTunes < 12.5.1 Multiple Vulnerabilities (uncredentialed Check) NASL family Windows NASL id ITUNES_12_5_1.NASL description The version of Apple iTunes installed on the remote Windows host is prior to 12.5.1. It is, therefore, affected by multiple vulnerabilities : - A remote code execution vulnerability exists due to improper handling of error prototypes. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to execute arbitrary code. (CVE-2016-4728) - An information disclosure vulnerability exists in WebKit due to a permission issue caused by improper handling of the location variable. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to disclose sensitive information. (CVE-2016-4758) - Multiple memory corruption errors exist in WebKit due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit these issues, by convincing a user to visit a maliciously crafted website, to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-4759, CVE-2016-4762, CVE-2016-4764, CVE-2016-4765, CVE-2016-4766, CVE-2016-4767, CVE-2016-4768, CVE-2016-4769) - A rebinding flaw exists in WebKit due to a failure to restrict HTTP/0.9 responses to default ports and cancel resource loads if a document is loaded with a different HTTP protocol version. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a maliciously crafted website, to access non-HTTP services. (CVE-2016-4760) - A security bypass vulnerability exists in WebKit in the WKWebView component due to a failure to properly verify X.509 certificates from HTTPS servers. A man-in-the-middle attacker can exploit this, via a specially crafted certificate, to spoof servers and disclose or manipulate network traffic. (CVE-2016-4763) Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 94914 published 2016-11-16 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/94914 title Apple iTunes < 12.5.1 Multiple Vulnerabilities (credentialed check) NASL family MacOS X Local Security Checks NASL id MACOSX_SAFARI10_0.NASL description The version of Apple Safari installed on the remote Mac OS X or macOS host is prior to 10.0. It is, therefore, affected by multiple vulnerabilities : - Multiple memory corruption issues exist in WebKit that allow an unauthenticated, remote attacker to cause a denial of service condition or execute arbitrary code via specially a crafted website. (CVE-2016-4611, CVE-2016-4729, CVE-2016-4730, CVE-2016-4731, CVE-2016-4734, CVE-2016-4735, CVE-2016-4737, CVE-2016-4759, CVE-2016-4762, CVE-2016-4766, CVE-2016-4767, CVE-2016-4768, CVE-2016-4769) - A cross-site scripting (XSS) vulnerability exists in the Reader feature due to improper validation of user-supplied input before returning it to users. An unauthenticated, remote attacker can exploit this, by convincing a user to follow a specially crafted link, to execute arbitrary script code in a user last seen 2020-06-01 modified 2020-06-02 plugin id 93721 published 2016-09-26 reporter This script is Copyright (C) 2016-2018 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/93721 title Mac OS X : Apple Safari < 10.0 Multiple Vulnerabilities
Seebug
| bulletinFamily | exploit |
| description | This article translated from: * http://mksben.l0.cm/2016/09/safari-uxss-showModalDialog.html (English version) * http://masatokinugawa.l0.cm/2016/09/safari-uxss-showModalDialog.html (Japanese version) Author:**Masato Kinugawa** Translator: **Holic (know Chong Yu 404 security lab)** Translator's note: as the translation date, the Japanese version and updated some content, this article is based on the English version of the original translation, part of the increase in the content of the turn from the Japanese original Edition. The present article share the Safari UXSS Vulnerability, CVE-2016-4758 about the details of the vulnerability in Safari 10 to be repaired. Official link: https://support.apple.com/en-us/HT207157 > WebKit Available for: OS X Yosemite v10. 10. 5, OS X Yosemite v10. 11. 6, and macOS Sierra 10.12 Impact: Visiting a maliciously crafted website may leak sensitive data Description: A permissions issue existed in the handling of the location variable. This was addressed though the additional ownership checks. CVE-2016-4758: Masato Kinugawa of Cure53 Vulnerability conditions for reference, the mobile version of Safari is not affected by the vulnerabilities, because there is no `showModalDialog `method. IE showModalDialog possible to use the XSS protection mechanism, related to the content you can refer to the following link: http://masatokinugawa.l0.cm/2015/06/xss6.html Original author's note: > By the way,on finishing a blog surrounding the behavior, noticed a more serious problem, the following started to write is this”serious problem“ ### The exploit conditions In exploit this vulnerability prior to attack, there are two prerequisites: 1\. The target page using the JavaScript Guide to the relative URL. Such as `location="/"`, `window. open("/","_blank", a`) 2\. Jump on page load after The original author set up a test page: https://vulnerabledoma.in/safari_uxss_showModalDialog/target.html `javascript the <script> function go_top(){ location="/index.html"; } </script> <button onclick=go_top()>Top Page</button>` This page is for the user to click on"Top Page"of the time jump to https://vulnerabledoma.in/index.html the. I think pages like this are everywhere, and in this case we can use this BUG to expand the XSS attack. ### Vulnerability details Now use `the showModalDialog `method. The following page in the modal dialog(mode window opens. https://l0.cm/safari_uxss_showModalDialog/example.html `javascript the <script> function go(){ showModalDialog("https://vulnerabledoma.in/safari_uxss_showModalDialog/target.html"); } </script> <button onclick=go()>go</button>` Click on the”Top Page“button after the modal dialog what happens? Needless to say, will visit https://vulnerabledoma.in/index.html the. However in Safari but not the same. Safari unexpectedly jump to the https://l0.cm/index.html page to go to. Obviously Safari to be confused with the parent window and the modal window base address. In this case, the relative URL contains the private information case, you can use independent pages to obtain private information. `javascript the <script> function navigation(){ location="/test? token=abb29ad9adda09";//get the private information } </script> <button onclick=navigation()>Click</button>` This is very dangerous behavior, there may also be further carried out XSS attacks. (Side note: this behavior only exists in the JavaScript navigation API, such as`<a>`tag and `xhr. open("GET",[URL]) ` use the correct URL.) ### Extended XSS attacks According to [html5sec. org#42](<https://html5sec.org/#42>), Safari allows `javascript: ` URL set to the base tag. Therefore, if the `javascript `tag is set to the parent page's base tag, it will lead to XSS vulnerabilities. My conjecture was confirmed. The following is the final PoC of: https://l0.cm/safari_uxss_showModalDialog/ `javascript <! DOCTYPE html> the <html> the <head> <base href="javascript://%0Aalert%28document. domain%29%2F/"> </head> the <body> the <script> function go(){ showModalDialog("http://vulnerabledoma.in/safari_uxss_showModalDialog/target.html"); } </script> <button onclick=go()>go</button> </body> </html>` The normal case, click"Top Page"button, you will see the alert session window as follows: 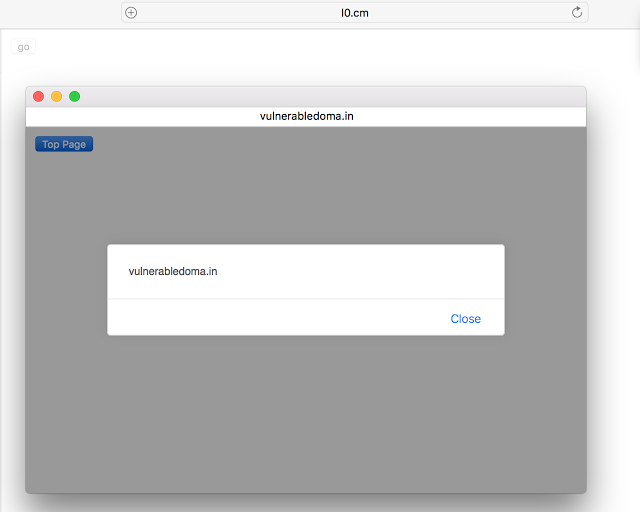 Yay! ### Summary The original authors 2015 June 15 report of this vulnerability, before this bug has been in WebKit in there for over a year. |
| id | SSV:92439 |
| last seen | 2017-11-19 |
| modified | 2016-09-27 |
| published | 2016-09-27 |
| reporter | Root |
| title | Safari the showModalDialog method UXSS vulnerability |
References
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00007.html
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00007.html
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00008.html
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00008.html
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00012.html
- http://lists.apple.com/archives/security-announce/2016/Sep/msg00012.html
- http://mksben.l0.cm/2016/09/safari-uxss-showModalDialog.html
- http://mksben.l0.cm/2016/09/safari-uxss-showModalDialog.html
- http://www.securityfocus.com/bid/93066
- http://www.securityfocus.com/bid/93066
- http://www.securitytracker.com/id/1036854
- http://www.securitytracker.com/id/1036854
- https://support.apple.com/HT207143
- https://support.apple.com/HT207143
- https://support.apple.com/HT207157
- https://support.apple.com/HT207157
- https://support.apple.com/HT207158
- https://support.apple.com/HT207158