Vulnerabilities > CVE-2016-1631 - Permissions, Privileges, and Access Controls vulnerability in Google Chrome
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
The PPB_Flash_MessageLoop_Impl::InternalRun function in content/renderer/pepper/ppb_flash_message_loop_impl.cc in the Pepper plugin in Google Chrome before 49.0.2623.75 mishandles nested message loops, which allows remote attackers to bypass the Same Origin Policy via a crafted web site.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Accessing, Modifying or Executing Executable Files An attack of this type exploits a system's configuration that allows an attacker to either directly access an executable file, for example through shell access; or in a possible worst case allows an attacker to upload a file and then execute it. Web servers, ftp servers, and message oriented middleware systems which have many integration points are particularly vulnerable, because both the programmers and the administrators must be in synch regarding the interfaces and the correct privileges for each interface.
- Leverage Executable Code in Non-Executable Files An attack of this type exploits a system's trust in configuration and resource files, when the executable loads the resource (such as an image file or configuration file) the attacker has modified the file to either execute malicious code directly or manipulate the target process (e.g. application server) to execute based on the malicious configuration parameters. Since systems are increasingly interrelated mashing up resources from local and remote sources the possibility of this attack occurring is high. The attack can be directed at a client system, such as causing buffer overrun through loading seemingly benign image files, as in Microsoft Security Bulletin MS04-028 where specially crafted JPEG files could cause a buffer overrun once loaded into the browser. Another example targets clients reading pdf files. In this case the attacker simply appends javascript to the end of a legitimate url for a pdf (http://www.gnucitizen.org/blog/danger-danger-danger/) http://path/to/pdf/file.pdf#whatever_name_you_want=javascript:your_code_here The client assumes that they are reading a pdf, but the attacker has modified the resource and loaded executable javascript into the client's browser process. The attack can also target server processes. The attacker edits the resource or configuration file, for example a web.xml file used to configure security permissions for a J2EE app server, adding role name "public" grants all users with the public role the ability to use the administration functionality. The server trusts its configuration file to be correct, but when they are manipulated, the attacker gains full control.
- Blue Boxing This type of attack against older telephone switches and trunks has been around for decades. A tone is sent by an adversary to impersonate a supervisor signal which has the effect of rerouting or usurping command of the line. While the US infrastructure proper may not contain widespread vulnerabilities to this type of attack, many companies are connected globally through call centers and business process outsourcing. These international systems may be operated in countries which have not upgraded Telco infrastructure and so are vulnerable to Blue boxing. Blue boxing is a result of failure on the part of the system to enforce strong authorization for administrative functions. While the infrastructure is different than standard current applications like web applications, there are historical lessons to be learned to upgrade the access control for administrative functions.
- Restful Privilege Elevation Rest uses standard HTTP (Get, Put, Delete) style permissions methods, but these are not necessarily correlated generally with back end programs. Strict interpretation of HTTP get methods means that these HTTP Get services should not be used to delete information on the server, but there is no access control mechanism to back up this logic. This means that unless the services are properly ACL'd and the application's service implementation are following these guidelines then an HTTP request can easily execute a delete or update on the server side. The attacker identifies a HTTP Get URL such as http://victimsite/updateOrder, which calls out to a program to update orders on a database or other resource. The URL is not idempotent so the request can be submitted multiple times by the attacker, additionally, the attacker may be able to exploit the URL published as a Get method that actually performs updates (instead of merely retrieving data). This may result in malicious or inadvertent altering of data on the server.
- Target Programs with Elevated Privileges This attack targets programs running with elevated privileges. The attacker would try to leverage a bug in the running program and get arbitrary code to execute with elevated privileges. For instance an attacker would look for programs that write to the system directories or registry keys (such as HKLM, which stores a number of critical Windows environment variables). These programs are typically running with elevated privileges and have usually not been designed with security in mind. Such programs are excellent exploit targets because they yield lots of power when they break. The malicious user try to execute its code at the same level as a privileged system call.
Nessus
NASL family Gentoo Local Security Checks NASL id GENTOO_GLSA-201603-09.NASL description The remote host is affected by the vulnerability described in GLSA-201603-09 (Chromium: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in the Chromium web browser. Please review the CVE identifiers referenced below for details. Impact : A remote attacker could possibly execute arbitrary code with the privileges of the process, cause a Denial of Service condition, obtain sensitive information, or bypass security restrictions. Workaround : There is no known workaround at this time. last seen 2020-06-01 modified 2020-06-02 plugin id 89902 published 2016-03-14 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89902 title GLSA-201603-09 : Chromium: Multiple vulnerabilities code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Gentoo Linux Security Advisory GLSA 201603-09. # # The advisory text is Copyright (C) 2001-2016 Gentoo Foundation, Inc. # and licensed under the Creative Commons - Attribution / Share Alike # license. See http://creativecommons.org/licenses/by-sa/3.0/ # include("compat.inc"); if (description) { script_id(89902); script_version("2.5"); script_cvs_date("Date: 2019/04/11 17:23:06"); script_cve_id("CVE-2015-1270", "CVE-2015-1271", "CVE-2015-1272", "CVE-2015-1273", "CVE-2015-1274", "CVE-2015-1275", "CVE-2015-1276", "CVE-2015-1277", "CVE-2015-1278", "CVE-2015-1279", "CVE-2015-1280", "CVE-2015-1281", "CVE-2015-1282", "CVE-2015-1283", "CVE-2015-1284", "CVE-2015-1285", "CVE-2015-1286", "CVE-2015-1287", "CVE-2015-1288", "CVE-2015-1289", "CVE-2015-1291", "CVE-2015-1292", "CVE-2015-1293", "CVE-2015-1294", "CVE-2015-1295", "CVE-2015-1296", "CVE-2015-1297", "CVE-2015-1298", "CVE-2015-1299", "CVE-2015-1300", "CVE-2015-1302", "CVE-2015-1303", "CVE-2015-1304", "CVE-2015-6755", "CVE-2015-6756", "CVE-2015-6757", "CVE-2015-6758", "CVE-2015-6759", "CVE-2015-6760", "CVE-2015-6761", "CVE-2015-6762", "CVE-2015-6763", "CVE-2015-6764", "CVE-2015-6765", "CVE-2015-6766", "CVE-2015-6767", "CVE-2015-6768", "CVE-2015-6769", "CVE-2015-6770", "CVE-2015-6771", "CVE-2015-6772", "CVE-2015-6773", "CVE-2015-6774", "CVE-2015-6775", "CVE-2015-6776", "CVE-2015-6777", "CVE-2015-6778", "CVE-2015-6779", "CVE-2015-6780", "CVE-2015-6781", "CVE-2015-6782", "CVE-2015-6783", "CVE-2015-6784", "CVE-2015-6785", "CVE-2015-6786", "CVE-2015-6787", "CVE-2015-6788", "CVE-2015-6789", "CVE-2015-6790", "CVE-2015-6791", "CVE-2015-6792", "CVE-2015-8126", "CVE-2016-1612", "CVE-2016-1613", "CVE-2016-1614", "CVE-2016-1615", "CVE-2016-1616", "CVE-2016-1617", "CVE-2016-1618", "CVE-2016-1619", "CVE-2016-1620", "CVE-2016-1621", "CVE-2016-1622", "CVE-2016-1623", "CVE-2016-1624", "CVE-2016-1625", "CVE-2016-1626", "CVE-2016-1627", "CVE-2016-1628", "CVE-2016-1629", "CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1632", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1635", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1638", "CVE-2016-1639", "CVE-2016-1640", "CVE-2016-1641"); script_xref(name:"GLSA", value:"201603-09"); script_name(english:"GLSA-201603-09 : Chromium: Multiple vulnerabilities"); script_summary(english:"Checks for updated package(s) in /var/db/pkg"); script_set_attribute( attribute:"synopsis", value: "The remote Gentoo host is missing one or more security-related patches." ); script_set_attribute( attribute:"description", value: "The remote host is affected by the vulnerability described in GLSA-201603-09 (Chromium: Multiple vulnerabilities) Multiple vulnerabilities have been discovered in the Chromium web browser. Please review the CVE identifiers referenced below for details. Impact : A remote attacker could possibly execute arbitrary code with the privileges of the process, cause a Denial of Service condition, obtain sensitive information, or bypass security restrictions. Workaround : There is no known workaround at this time." ); script_set_attribute( attribute:"see_also", value:"https://security.gentoo.org/glsa/201603-09" ); script_set_attribute( attribute:"solution", value: "All Chromium users should upgrade to the latest version: # emerge --sync # emerge --ask --oneshot --verbose '>=www-client/chromium-49.0.2623.87'" ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:POC/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:P/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:gentoo:linux:chromium"); script_set_attribute(attribute:"cpe", value:"cpe:/o:gentoo:linux"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/12"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/14"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Gentoo Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/Gentoo/release", "Host/Gentoo/qpkg-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("qpkg.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); if (!get_kb_item("Host/Gentoo/release")) audit(AUDIT_OS_NOT, "Gentoo"); if (!get_kb_item("Host/Gentoo/qpkg-list")) audit(AUDIT_PACKAGE_LIST_MISSING); flag = 0; if (qpkg_check(package:"www-client/chromium", unaffected:make_list("ge 49.0.2623.87"), vulnerable:make_list("lt 49.0.2623.87"))) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:qpkg_report_get()); else security_hole(0); exit(0); } else { tested = qpkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "Chromium"); }NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-316.NASL description Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) last seen 2020-06-05 modified 2016-03-10 plugin id 89813 published 2016-03-10 reporter This script is Copyright (C) 2016-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/89813 title openSUSE Security Update : Chromium (openSUSE-2016-316) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2016-316. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(89813); script_version("2.5"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2015-8126", "CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1632", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1635", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1638", "CVE-2016-1639", "CVE-2016-1640", "CVE-2016-1641", "CVE-2016-1642"); script_name(english:"openSUSE Security Update : Chromium (openSUSE-2016-316)"); script_summary(english:"Check for the openSUSE-2016-316 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26)" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=969333" ); script_set_attribute( attribute:"solution", value:"Update the affected Chromium packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromedriver"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromedriver-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-debugsource"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-desktop-gnome"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-desktop-kde"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-ffmpegsumo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-ffmpegsumo-debuginfo"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:13.1"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/08"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/10"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 Tenable Network Security, Inc."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE13\.1)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "13.1", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); ourarch = get_kb_item("Host/cpu"); if (!ourarch) audit(AUDIT_UNKNOWN_ARCH); if (ourarch !~ "^(i586|i686|x86_64)$") audit(AUDIT_ARCH_NOT, "i586 / i686 / x86_64", ourarch); flag = 0; if ( rpm_check(release:"SUSE13.1", reference:"chromedriver-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromedriver-debuginfo-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-debuginfo-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-debugsource-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-desktop-gnome-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-desktop-kde-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-ffmpegsumo-49.0.2623.75-135.1") ) flag++; if ( rpm_check(release:"SUSE13.1", reference:"chromium-ffmpegsumo-debuginfo-49.0.2623.75-135.1") ) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "chromedriver / chromedriver-debuginfo / chromium / etc"); }NASL family Red Hat Local Security Checks NASL id REDHAT-RHSA-2016-0359.NASL description Updated chromium-browser packages that fix multiple security issues are now available for Red Hat Enterprise Linux 6 Supplementary. Red Hat Product Security has rated this update as having Important security impact. Common Vulnerability Scoring System (CVSS) base scores, which give detailed severity ratings, are available for each vulnerability from the CVE links in the References section. Chromium is an open source web browser, powered by WebKit (Blink). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Chromium to crash, execute arbitrary code, or disclose sensitive information when visited by the victim. (CVE-2016-1630, CVE-2016-1631, CVE-2016-1632, CVE-2016-1633, CVE-2016-1634, CVE-2016-1635, CVE-2016-1636, CVE-2016-1637, CVE-2016-1638, CVE-2016-1639, CVE-2016-1640, CVE-2016-1641, CVE-2016-1642) All Chromium users should upgrade to these updated packages, which contain Chromium version 49.0.2623.75, which corrects these issues. After installing the update, Chromium must be restarted for the changes to take effect. last seen 2020-05-31 modified 2016-03-07 plugin id 89720 published 2016-03-07 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89720 title RHEL 6 : chromium-browser (RHSA-2016:0359) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Red Hat Security Advisory RHSA-2016:0359. The text # itself is copyright (C) Red Hat, Inc. # include("compat.inc"); if (description) { script_id(89720); script_version("2.17"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/05/29"); script_cve_id("CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1632", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1635", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1638", "CVE-2016-1639", "CVE-2016-1640", "CVE-2016-1641", "CVE-2016-1642"); script_xref(name:"RHSA", value:"2016:0359"); script_name(english:"RHEL 6 : chromium-browser (RHSA-2016:0359)"); script_summary(english:"Checks the rpm output for the updated packages"); script_set_attribute( attribute:"synopsis", value:"The remote Red Hat host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "Updated chromium-browser packages that fix multiple security issues are now available for Red Hat Enterprise Linux 6 Supplementary. Red Hat Product Security has rated this update as having Important security impact. Common Vulnerability Scoring System (CVSS) base scores, which give detailed severity ratings, are available for each vulnerability from the CVE links in the References section. Chromium is an open source web browser, powered by WebKit (Blink). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Chromium to crash, execute arbitrary code, or disclose sensitive information when visited by the victim. (CVE-2016-1630, CVE-2016-1631, CVE-2016-1632, CVE-2016-1633, CVE-2016-1634, CVE-2016-1635, CVE-2016-1636, CVE-2016-1637, CVE-2016-1638, CVE-2016-1639, CVE-2016-1640, CVE-2016-1641, CVE-2016-1642) All Chromium users should upgrade to these updated packages, which contain Chromium version 49.0.2623.75, which corrects these issues. After installing the update, Chromium must be restarted for the changes to take effect." ); # http://googlechromereleases.blogspot.com/2016/03/stable-channel-update.html script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?c095da5b" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/errata/RHSA-2016:0359" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1636" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1637" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1634" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1635" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1632" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1633" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1630" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1631" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1638" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1639" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1642" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1641" ); script_set_attribute( attribute:"see_also", value:"https://access.redhat.com/security/cve/cve-2016-1640" ); script_set_attribute( attribute:"solution", value: "Update the affected chromium-browser and / or chromium-browser-debuginfo packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:U/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:U/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"No known exploits are available"); script_set_attribute(attribute:"exploit_available", value:"false"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:chromium-browser"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:redhat:enterprise_linux:chromium-browser-debuginfo"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6"); script_set_attribute(attribute:"cpe", value:"cpe:/o:redhat:enterprise_linux:6.7"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/03/06"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/07"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/07"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Red Hat Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/RedHat/release", "Host/RedHat/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/RedHat/release"); if (isnull(release) || "Red Hat" >!< release) audit(AUDIT_OS_NOT, "Red Hat"); os_ver = pregmatch(pattern: "Red Hat Enterprise Linux.*release ([0-9]+(\.[0-9]+)?)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "Red Hat"); os_ver = os_ver[1]; if (! preg(pattern:"^6([^0-9]|$)", string:os_ver)) audit(AUDIT_OS_NOT, "Red Hat 6.x", "Red Hat " + os_ver); if (!get_kb_item("Host/RedHat/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$" && "s390" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Red Hat", cpu); yum_updateinfo = get_kb_item("Host/RedHat/yum-updateinfo"); if (!empty_or_null(yum_updateinfo)) { rhsa = "RHSA-2016:0359"; yum_report = redhat_generate_yum_updateinfo_report(rhsa:rhsa); if (!empty_or_null(yum_report)) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : yum_report ); exit(0); } else { audit_message = "affected by Red Hat security advisory " + rhsa; audit(AUDIT_OS_NOT, audit_message); } } else { flag = 0; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"chromium-browser-49.0.2623.75-1.el6", allowmaj:TRUE)) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"chromium-browser-49.0.2623.75-1.el6", allowmaj:TRUE)) flag++; if (rpm_check(release:"RHEL6", cpu:"i686", reference:"chromium-browser-debuginfo-49.0.2623.75-1.el6", allowmaj:TRUE)) flag++; if (rpm_check(release:"RHEL6", cpu:"x86_64", reference:"chromium-browser-debuginfo-49.0.2623.75-1.el6", allowmaj:TRUE)) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : rpm_report_get() + redhat_report_package_caveat() ); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "chromium-browser / chromium-browser-debuginfo"); } }NASL family SuSE Local Security Checks NASL id SUSE_SU-2016-0665-1.NASL description Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-05-31 modified 2016-03-09 plugin id 89775 published 2016-03-09 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89775 title SUSE SLES12 Security Update : Chromium (SUSE-SU-2016:0665-1) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from SUSE update advisory SUSE-SU-2016:0665-1. # The text itself is copyright (C) SUSE. # include("compat.inc"); if (description) { script_id(89775); script_version("2.15"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/05/29"); script_cve_id("CVE-2015-8126", "CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1632", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1635", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1638", "CVE-2016-1639", "CVE-2016-1640", "CVE-2016-1641", "CVE-2016-1642"); script_name(english:"SUSE SLES12 Security Update : Chromium (SUSE-SU-2016:0665-1)"); script_summary(english:"Checks rpm output for the updated packages."); script_set_attribute( attribute:"synopsis", value:"The remote SUSE host is missing one or more security updates." ); script_set_attribute( attribute:"description", value: "Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) Note that Tenable Network Security has extracted the preceding description block directly from the SUSE security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.suse.com/show_bug.cgi?id=969333" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2015-8126/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1630/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1631/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1632/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1633/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1634/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1635/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1636/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1637/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1638/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1639/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1640/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1641/" ); script_set_attribute( attribute:"see_also", value:"https://www.suse.com/security/cve/CVE-2016-1642/" ); # https://www.suse.com/support/update/announcement/2016/suse-su-20160665-1/ script_set_attribute( attribute:"see_also", value:"http://www.nessus.org/u?ff6e57cc" ); script_set_attribute( attribute:"solution", value: "To install this SUSE Security Update use YaST online_update. Alternatively you can run the command listed for your product : SUSE Package Hub for SUSE Linux Enterprise 12 : zypper in -t patch 4789=1 To bring your system up-to-date, use 'zypper patch'." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:U/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:U/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"No known exploits are available"); script_set_attribute(attribute:"exploit_available", value:"false"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromedriver"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromedriver-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-debugsource"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-desktop-gnome"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-desktop-kde"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-ffmpegsumo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:suse_linux:chromium-ffmpegsumo-debuginfo"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:suse_linux:12"); script_set_attribute(attribute:"vuln_publication_date", value:"2015/11/13"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/05"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/09"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/cpu", "Host/SuSE/release", "Host/SuSE/rpm-list"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release !~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "SUSE"); os_ver = pregmatch(pattern: "^(SLE(S|D)\d+)", string:release); if (isnull(os_ver)) audit(AUDIT_UNKNOWN_APP_VER, "SUSE"); os_ver = os_ver[1]; if (! preg(pattern:"^(SLES12)$", string:os_ver)) audit(AUDIT_OS_NOT, "SUSE SLES12", "SUSE " + os_ver); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if (cpu !~ "^i[3-6]86$" && "x86_64" >!< cpu && "s390x" >!< cpu) audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "SUSE " + os_ver, cpu); if (cpu >!< "x86_64") audit(AUDIT_ARCH_NOT, "x86_64", cpu); sp = get_kb_item("Host/SuSE/patchlevel"); if (isnull(sp)) sp = "0"; if (os_ver == "SLES12" && (! preg(pattern:"^(0)$", string:sp))) audit(AUDIT_OS_NOT, "SLES12 SP0", os_ver + " SP" + sp); flag = 0; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromedriver-49.0.2623.75-55.1")) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromedriver-debuginfo-49.0.2623.75-55.1")) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-debuginfo-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-debugsource-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-desktop-gnome-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-desktop-kde-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-ffmpegsumo-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (rpm_check(release:"SLES12", sp:"0", cpu:"x86_64", reference:"chromium-ffmpegsumo-debuginfo-49.0.2623.75-55.1", allowmaj:TRUE)) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "Chromium"); }NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-330.NASL description Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) last seen 2020-06-05 modified 2016-03-14 plugin id 89912 published 2016-03-14 reporter This script is Copyright (C) 2016-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/89912 title openSUSE Security Update : Chromium (openSUSE-2016-330) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2016-330. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(89912); script_version("2.5"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2015-8126", "CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1632", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1635", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1638", "CVE-2016-1639", "CVE-2016-1640", "CVE-2016-1641", "CVE-2016-1642"); script_name(english:"openSUSE Security Update : Chromium (openSUSE-2016-330)"); script_summary(english:"Check for the openSUSE-2016-330 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26)" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=969333" ); script_set_attribute( attribute:"solution", value:"Update the affected Chromium packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromedriver"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromedriver-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-debuginfo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-debugsource"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-desktop-gnome"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-desktop-kde"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-ffmpegsumo"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:chromium-ffmpegsumo-debuginfo"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:13.2"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/11"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/14"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 Tenable Network Security, Inc."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE13\.2)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "13.2", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); ourarch = get_kb_item("Host/cpu"); if (!ourarch) audit(AUDIT_UNKNOWN_ARCH); if (ourarch !~ "^(i586|i686|x86_64)$") audit(AUDIT_ARCH_NOT, "i586 / i686 / x86_64", ourarch); flag = 0; if ( rpm_check(release:"SUSE13.2", reference:"chromedriver-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromedriver-debuginfo-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-debuginfo-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-debugsource-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-desktop-gnome-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-desktop-kde-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-ffmpegsumo-49.0.2623.75-81.2") ) flag++; if ( rpm_check(release:"SUSE13.2", reference:"chromium-ffmpegsumo-debuginfo-49.0.2623.75-81.2") ) flag++; if (flag) { if (report_verbosity > 0) security_hole(port:0, extra:rpm_report_get()); else security_hole(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "chromedriver / chromedriver-debuginfo / chromium / etc"); }NASL family Ubuntu Local Security Checks NASL id UBUNTU_USN-2920-1.NASL description It was discovered that the ContainerNode::parserRemoveChild function in Blink mishandled widget updates in some circumstances. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass same-origin restrictions. (CVE-2016-1630) It was discovered that the PPB_Flash_MessageLoop_Impl::InternalRun function in Chromium mishandled nested message loops. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass same-origin restrictions. (CVE-2016-1631) Multiple use-after-frees were discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-1633, CVE-2016-1634, CVE-2016-1644) It was discovered that the PendingScript::notifyFinished function in Blink relied on memory-cache information about integrity-check occurrences instead of integrity-check successes. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass Subresource Integrity (SRI) protections. (CVE-2016-1636) It was discovered that the SkATan2_255 function in Skia mishandled arctangent calculations. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to obtain sensitive information. (CVE-2016-1637) A use-after-free was discovered in Chromium. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via application crash, or execute arbitrary code with the privileges of the user invoking the program. (CVE-2016-1641) Multiple security issues were discovered in Chromium. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to read uninitialized memory, cause a denial of service via application crash or execute arbitrary code with the privileges of the user invoking the program. (CVE-2016-1642) A type-confusion bug was discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-1643) Multiple security issues were discovered in V8. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to read uninitialized memory, cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-2843) An invalid cast was discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-2844) It was discovered that the Content Security Policy (CSP) implementation in Blink did not ignore a URL last seen 2020-06-01 modified 2020-06-02 plugin id 89865 published 2016-03-11 reporter Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89865 title Ubuntu 14.04 LTS / 15.10 : oxide-qt vulnerabilities (USN-2920-1) code # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from Ubuntu Security Notice USN-2920-1. The text # itself is copyright (C) Canonical, Inc. See # <http://www.ubuntu.com/usn/>. Ubuntu(R) is a registered # trademark of Canonical, Inc. # include("compat.inc"); if (description) { script_id(89865); script_version("2.11"); script_cvs_date("Date: 2019/09/18 12:31:45"); script_cve_id("CVE-2016-1630", "CVE-2016-1631", "CVE-2016-1633", "CVE-2016-1634", "CVE-2016-1636", "CVE-2016-1637", "CVE-2016-1641", "CVE-2016-1642", "CVE-2016-1643", "CVE-2016-1644", "CVE-2016-2843", "CVE-2016-2844", "CVE-2016-2845"); script_xref(name:"USN", value:"2920-1"); script_name(english:"Ubuntu 14.04 LTS / 15.10 : oxide-qt vulnerabilities (USN-2920-1)"); script_summary(english:"Checks dpkg output for updated package."); script_set_attribute( attribute:"synopsis", value:"The remote Ubuntu host is missing a security-related patch." ); script_set_attribute( attribute:"description", value: "It was discovered that the ContainerNode::parserRemoveChild function in Blink mishandled widget updates in some circumstances. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass same-origin restrictions. (CVE-2016-1630) It was discovered that the PPB_Flash_MessageLoop_Impl::InternalRun function in Chromium mishandled nested message loops. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass same-origin restrictions. (CVE-2016-1631) Multiple use-after-frees were discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-1633, CVE-2016-1634, CVE-2016-1644) It was discovered that the PendingScript::notifyFinished function in Blink relied on memory-cache information about integrity-check occurrences instead of integrity-check successes. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to bypass Subresource Integrity (SRI) protections. (CVE-2016-1636) It was discovered that the SkATan2_255 function in Skia mishandled arctangent calculations. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to obtain sensitive information. (CVE-2016-1637) A use-after-free was discovered in Chromium. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via application crash, or execute arbitrary code with the privileges of the user invoking the program. (CVE-2016-1641) Multiple security issues were discovered in Chromium. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to read uninitialized memory, cause a denial of service via application crash or execute arbitrary code with the privileges of the user invoking the program. (CVE-2016-1642) A type-confusion bug was discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-1643) Multiple security issues were discovered in V8. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit these to read uninitialized memory, cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-2843) An invalid cast was discovered in Blink. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to cause a denial of service via renderer crash or execute arbitrary code with the privileges of the sandboxed render process. (CVE-2016-2844) It was discovered that the Content Security Policy (CSP) implementation in Blink did not ignore a URL's path component in the case of a ServiceWorker fetch. If a user were tricked in to opening a specially crafted website, an attacker could potentially exploit this to obtain sensitive information. (CVE-2016-2845). Note that Tenable Network Security has extracted the preceding description block directly from the Ubuntu security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues." ); script_set_attribute( attribute:"see_also", value:"https://usn.ubuntu.com/2920-1/" ); script_set_attribute( attribute:"solution", value:"Update the affected liboxideqtcore0 package." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:U/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:U/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"No known exploits are available"); script_set_attribute(attribute:"exploit_available", value:"false"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:canonical:ubuntu_linux:liboxideqtcore0"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:14.04"); script_set_attribute(attribute:"cpe", value:"cpe:/o:canonical:ubuntu_linux:15.10"); script_set_attribute(attribute:"vuln_publication_date", value:"2016/03/06"); script_set_attribute(attribute:"patch_publication_date", value:"2016/03/10"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/03/11"); script_set_attribute(attribute:"generated_plugin", value:"current"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"Ubuntu Security Notice (C) 2016-2019 Canonical, Inc. / NASL script (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Ubuntu Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/cpu", "Host/Ubuntu", "Host/Ubuntu/release", "Host/Debian/dpkg-l"); exit(0); } include("audit.inc"); include("ubuntu.inc"); include("misc_func.inc"); if ( ! get_kb_item("Host/local_checks_enabled") ) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/Ubuntu/release"); if ( isnull(release) ) audit(AUDIT_OS_NOT, "Ubuntu"); release = chomp(release); if (! preg(pattern:"^(14\.04|15\.10)$", string:release)) audit(AUDIT_OS_NOT, "Ubuntu 14.04 / 15.10", "Ubuntu " + release); if ( ! get_kb_item("Host/Debian/dpkg-l") ) audit(AUDIT_PACKAGE_LIST_MISSING); cpu = get_kb_item("Host/cpu"); if (isnull(cpu)) audit(AUDIT_UNKNOWN_ARCH); if ("x86_64" >!< cpu && cpu !~ "^i[3-6]86$") audit(AUDIT_LOCAL_CHECKS_NOT_IMPLEMENTED, "Ubuntu", cpu); flag = 0; if (ubuntu_check(osver:"14.04", pkgname:"liboxideqtcore0", pkgver:"1.13.6-0ubuntu0.14.04.1")) flag++; if (ubuntu_check(osver:"15.10", pkgname:"liboxideqtcore0", pkgver:"1.13.6-0ubuntu0.15.10.1")) flag++; if (flag) { security_report_v4( port : 0, severity : SECURITY_HOLE, extra : ubuntu_report_get() ); exit(0); } else { tested = ubuntu_pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "liboxideqtcore0"); }NASL family SuSE Local Security Checks NASL id SUSE_42_1_4789-160306.NASL description Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) This plugin has been renamed to openSUSE-2016-664.nasl, plugin ID 90107. last seen 2017-10-29 modified 2016-03-24 plugin id 89721 published 2016-03-07 reporter Tenable source https://www.tenable.com/plugins/index.php?view=single&id=89721 title openSUSE Security Update : 4789 (4789-1) (deprecated) NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3507.NASL description Several vulnerabilities have been discovered in the chromium web browser. - CVE-2015-8126 Joerg Bornemann discovered multiple buffer overflow issues in the libpng library. - CVE-2016-1630 Mariusz Mlynski discovered a way to bypass the Same Origin Policy in Blink/Webkit. - CVE-2016-1631 Mariusz Mlynski discovered a way to bypass the Same Origin Policy in the Pepper Plugin API. - CVE-2016-1632 A bad cast was discovered. - CVE-2016-1633 cloudfuzzer discovered a use-after-free issue in Blink/Webkit. - CVE-2016-1634 cloudfuzzer discovered a use-after-free issue in Blink/Webkit. - CVE-2016-1635 Rob Wu discovered a use-after-free issue in Blink/Webkit. - CVE-2016-1636 A way to bypass SubResource Integrity validation was discovered. - CVE-2016-1637 Keve Nagy discovered an information leak in the skia library. - CVE-2016-1638 Rob Wu discovered a WebAPI bypass issue. - CVE-2016-1639 Khalil Zhani discovered a use-after-free issue in the WebRTC implementation. - CVE-2016-1640 Luan Herrera discovered an issue with the Extensions user interface. - CVE-2016-1641 Atte Kettunen discovered a use-after-free issue in the handling of favorite icons. - CVE-2016-1642 The chrome 49 development team found and fixed various issues during internal auditing. Also multiple issues were fixed in the v8 JavaScript library, version 4.9.385.26. last seen 2020-06-01 modified 2020-06-02 plugin id 89697 published 2016-03-07 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89697 title Debian DSA-3507-1 : chromium-browser - security update NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_F85FA236E2A6412EB5C7C42120892DE5.NASL description Google Chrome Releases reports : [560011] High CVE-2016-1630: Same-origin bypass in Blink. [569496] High CVE-2016-1631: Same-origin bypass in Pepper Plugin. [549986] High CVE-2016-1632: Bad cast in Extensions. [572537] High CVE-2016-1633: Use-after-free in Blink. [559292] High CVE-2016-1634: Use-after-free in Blink. [585268] High CVE-2016-1635: Use-after-free in Blink. [584155] High CVE-2016-1636: SRI Validation Bypass. [555544] Medium CVE-2016-1637: Information Leak in Skia. [585282] Medium CVE-2016-1638: WebAPI Bypass. [572224] Medium CVE-2016-1639: Use-after-free in WebRTC. [550047] Medium CVE-2016-1640: Origin confusion in Extensions UI. [583718] Medium CVE-2016-1641: Use-after-free in Favicon. [591402] CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives. Multiple vulnerabilities in V8 fixed. last seen 2020-06-01 modified 2020-06-02 plugin id 89711 published 2016-03-07 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89711 title FreeBSD : chromium -- multiple vulnerabilities (f85fa236-e2a6-412e-b5c7-c42120892de5) NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-664.NASL description Chromium was updated to 49.0.2623.75 to fix the following security issues: (boo#969333) - CVE-2016-1630: Same-origin bypass in Blink - CVE-2016-1631: Same-origin bypass in Pepper Plugin - CVE-2016-1632: Bad cast in Extensions - CVE-2016-1633: Use-after-free in Blink - CVE-2016-1634: Use-after-free in Blink - CVE-2016-1635: Use-after-free in Blink - CVE-2016-1636: SRI Validation Bypass - CVE-2015-8126: Out-of-bounds access in libpng - CVE-2016-1637: Information Leak in Skia - CVE-2016-1638: WebAPI Bypass - CVE-2016-1639: Use-after-free in WebRTC - CVE-2016-1640: Origin confusion in Extensions UI - CVE-2016-1641: Use-after-free in Favicon - CVE-2016-1642: Various fixes from internal audits, fuzzing and other initiatives - Multiple vulnerabilities in V8 fixed at the tip of the 4.9 branch (currently 4.9.385.26) last seen 2020-06-05 modified 2016-03-23 plugin id 90107 published 2016-03-23 reporter This script is Copyright (C) 2016-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/90107 title openSUSE Security Update : Chromium (openSUSE-2016-664) NASL family MacOS X Local Security Checks NASL id MACOSX_GOOGLE_CHROME_49_0_2623_75.NASL description The version of Google Chrome installed on the remote Mac OS X host is prior to 49.0.2623.75. It is, therefore, affected by multiple vulnerabilities : - Multiple overflow conditions exist in the libpng library in the png_set_PLTE() and png_get_PLTE() functions due to improper handling of bit depths less than eight. A remote attacker can exploit this, via a specially crafted PNG image, to cause a denial of service condition or the execution of arbitrary code. (CVE-2015-8126) - An unspecified flaw exists in Blink that allows an attacker to bypass the same-origin policy. (CVE-2016-1630) - An unspecified flaw exists in the Pepper plugin that allows an attacker to bypass the same-origin policy. (CVE-2016-1631) - A bad cast flaw exists in the Extensions component that allows an attacker to have an unspecified impact. (CVE-2016-1632) - Multiple use-after-free errors exist in Blink. A remote attacker can exploit these issues to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1633, CVE-2016-1634, CVE-2016-1635) - An unspecified flaw exists that allows an attacker to bypass SRI validation. (CVE-2016-1636) - An unspecified flaw exists that allows an attacker to disclose sensitive information. (CVE-2016-1637) - An unspecified flaw exists that allows an attacker to bypass the webAPI. (CVE-2016-1638) - A use-after-free error exists in WebRTC. A remote attacker can exploit this issue to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1639) - An unspecified origin confusion flaw exists in the Extensions UI that allows an attacker to have an unspecified impact. (CVE-2016-1640) - A use-after-free error exists in Favicon. A remote attacker can exploit this issue to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1641) - Multiple flaws exist that allow a remote attacker to execute arbitrary code. (CVE-2016-1642) - Multiple unspecified flaws exist in Google V8 in runetime-scopes.cc that allows an attacker to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-2843) last seen 2020-06-01 modified 2020-06-02 plugin id 89686 published 2016-03-04 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89686 title Google Chrome < 49.0.2623.75 Multiple Vulnerabilities (Mac OS X) NASL family Windows NASL id GOOGLE_CHROME_49_0_2623_75.NASL description The version of Google Chrome installed on the remote Windows host is prior to 49.0.2623.75. It is, therefore, affected by multiple vulnerabilities : - Multiple overflow conditions exist in the libpng library in the png_set_PLTE() and png_get_PLTE() functions due to improper handling of bit depths less than eight. A remote attacker can exploit this, via a specially crafted PNG image, to cause a denial of service condition or the execution of arbitrary code. (CVE-2015-8126) - An unspecified flaw exists in Blink that allows an attacker to bypass the same-origin policy. (CVE-2016-1630) - An unspecified flaw exists in the Pepper plugin that allows an attacker to bypass the same-origin policy. (CVE-2016-1631) - A bad cast flaw exists in the Extensions component that allows an attacker to have an unspecified impact. (CVE-2016-1632) - Multiple use-after-free errors exist in Blink. A remote attacker can exploit these issues to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1633, CVE-2016-1634, CVE-2016-1635) - An unspecified flaw exists that allows an attacker to bypass SRI validation. (CVE-2016-1636) - An unspecified flaw exists that allows an attacker to disclose sensitive information. (CVE-2016-1637) - An unspecified flaw exists that allows an attacker to bypass the webAPI. (CVE-2016-1638) - A use-after-free error exists in WebRTC. A remote attacker can exploit this issue to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1639) - An unspecified origin confusion flaw exists in the Extensions UI that allows an attacker to have an unspecified impact. (CVE-2016-1640) - A use-after-free error exists in Favicon. A remote attacker can exploit this issue to dereference already freed memory, resulting in the execution of arbitrary code. (CVE-2016-1641) - Multiple flaws exist that allow a remote attacker to execute arbitrary code. (CVE-2016-1642) - Multiple unspecified flaws exist in Google V8 in runetime-scopes.cc that allows an attacker to cause a denial of service condition or the execution of arbitrary code. (CVE-2016-2843 last seen 2020-06-01 modified 2020-06-02 plugin id 89685 published 2016-03-04 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89685 title Google Chrome < 49.0.2623.75 Multiple Vulnerabilities
Redhat
| rpms |
|
Seebug
bulletinFamily exploit description Author: **[Avfisher@network sharp knife](<http://avfisher.win/archives/619>)** ## 0x00 Preface This writing comes from a few days ago a buddy sent me a bug link to let the author help explain the vulnerability principle, in order to facilitate the partner understanding and left notes for future reference and then write this article. This article discusses the vulnerability has been already fixed, but as vulnerability research is still very valuable. This vulnerability by researchers Marius Mlynski discovered and, 2015 12 month 14 report of a Chrome improper use of Flash message loop to produce the UXSS Vulnerability, CVE-2016-1631 on. ## 0x01 analysis Vulnerability impact: `Chrome 47.0.2526.80 (Stable) Chrome 48.0.2564.41 (Beta) Chrome 49.0.2587.3 (Dev) Chromium 49.0.2591.0 + Pepper Flash` The original bug report is as follows: ``c From /content/renderer/pepper/ppb_flash_message_loop_impl. cc: * * * int32_t PPB_Flash_MessageLoop_Impl::InternalRun( const RunFromHostProxyCallback& callback) { (...) // It is possible that the PPB_Flash_MessageLoop_Impl object has been // destroyed when the nested message loop exits. scoped_refptrstate_protector(state_); { base::MessageLoop::ScopedNestableTaskAllower allow( base::MessageLoop::current()); base::MessageLoop::current()->Run(); } (...) } * * * `` The reporter explained: PPB_Flash_MessageLoop_Impl::InternalRun in running a nested message loop until not initialized ScopedPageLoadDeferrer, which leads to be able to in any Javascrpit to perform point load a cross-domain document cause the XSS to. Next, we look at the report provided by the [POC](<https://bugs.chromium.org/p/chromium/issues/attachment?aid=218674>), there are three main files: * p. as: an ActionScript script file * p. swf: a swf format Flash file * poc.html: specific poc code ``javascript p. as: package { import flash. display._; import flash. external._; import flash. printing.*; public class p extends Sprite { public function f():void { new PrintJob(). start(); } public function p():void { ExternalInterface. addCallback('f', f); ExternalInterface. call('top. cp'); } } } `` ``javascript poc.html: `` POC works in a page to create multiple sources for the Flash file to the iframe, and then call as the script to open the print tasks, at this time Chrome will by PPB_Flash_MessageLoop_Impl::InternalRun method in the main thread to run a nested MessageLoop-message loop to send PPB_Flash_MessageLoop message to the renderer, since PPB_Flash_MessageLoop_Impl::InternalRun method is not on the stack set ScopedPageLoadDeferrer to postpone the loading of resulting in a nested MessageLoop in the loop when the callback script and load any resources as a result of the UXSS vulnerability. How, then, to understand this vulnerability? In Chrome, we know that each thread has a MessageLoop(message loop instance. Report of the PPB_Flash_MessageLoop_Impl is actually Chrome process Flash event to the message loop implementation. When the browser receives to print a Flash file to the message, it will open a MessageLoop to process the print event, but this time if you are running a nested message loop does not terminate the script callback and the resource loading method, you can pass a script callback code to bypass the SOP to load any resources, it will cause a XSS vulnerability. From the following is the source code author to do the repair can better understand the vulnerability of the generated reasons. 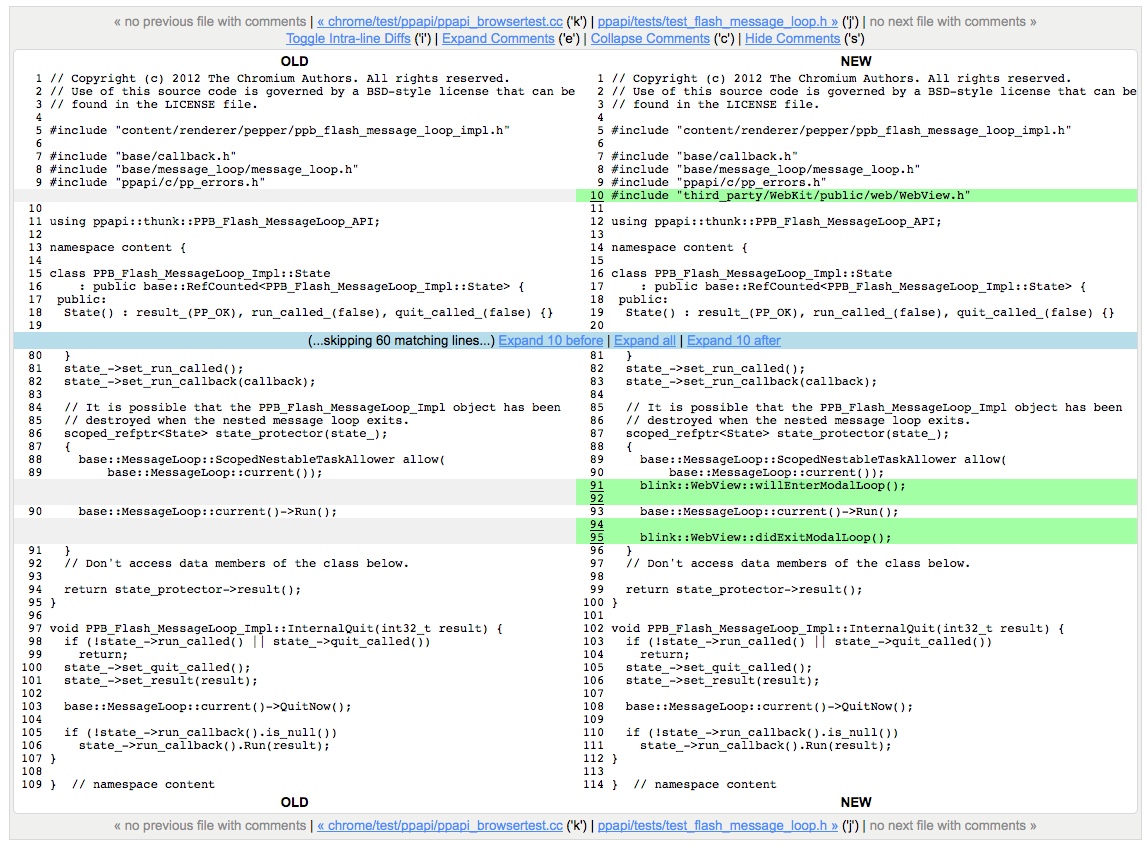 Not difficult to find, the source the author actually only made the following changes: 1\. Added#include “third_party/WebKit/public/web/WebView. h”; 2\. In the implementation of base::MessageLoop::current()->Run();before add a blink::WebView::willEnterModalLoop(); 3\. In the implementation of base::MessageLoop::current()->Run();after adding a blink::WebView::didExitModalLoop(); Find third_party/WebKit/public/web/WebView. h file, we find a step 2 and Method 3 are as follows: ``c third_party/WebKit/public/web/WebView. h: * * * // Modal dialog support------------------------------------------------ // Call these methods before and after running a nested, modal event loop // to suspend the script callbacks and resource loads. BLINK_EXPORT static void willEnterModalLoop(); BLINK_EXPORT static void didExitModalLoop(); ## (...) `` Obviously, fix the vulnerability is in the implementation of a nested modal event through the bad before and after calling these 2 methods to prevent the script callback and the resource to the load, thereby preventing the because the script callback and bypass the SOP of the XSS vulnerability. ## 0x02 use First, download the [exploit ](<https://bugs.chromium.org/p/chromium/issues/attachment?aid=190008>)and deploy to your web server. After extracting, the documents directory is as follows: `├── exploit │ ├── exploit.html │ ├── f.html │ ├── p. as │ └── p. swf` Open exploit. html modified as follows: ``javascript ``` The use of effect is as follows: 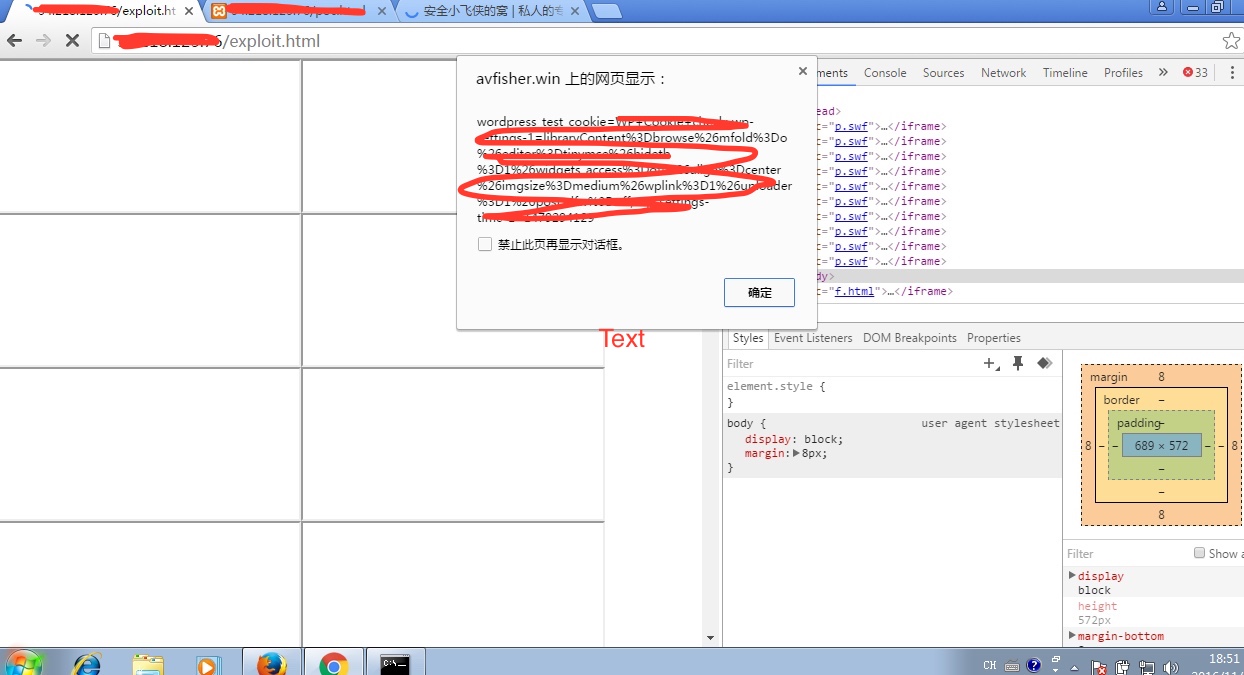 ## 0x03 reference * <https://bugs.chromium.org/p/chromium/issues/detail?id=569496> * [https://codereview.chromium.org/1559113002/diff/40001/content/renderer/pepper/ppb_flash_message_loop_impl.cc?context=10&column_width=80&tab_spaces=8](<https://codereview.chromium.org/1559113002/diff/40001/content/renderer/pepper/ppb_flash_message_loop_impl.cc?context=10&column_width=80&tab_spaces=8>) * [https://chromium.googlesource.com/chromium/src/+/dd77c2a41c72589d929db0592565125ca629fb2c/third_party/WebKit/public/web/WebView. h](<https://chromium.googlesource.com/chromium/src/+/dd77c2a41c72589d929db0592565125ca629fb2c/third_party/WebKit/public/web/WebView.h>) * [https://chromium.googlesource.com/chromium/src/+/dd77c2a41c72589d929db0592565125ca629fb2c/base/message_loop/message_loop. h#581](<https://chromium.googlesource.com/chromium/src/+/dd77c2a41c72589d929db0592565125ca629fb2c/base/message_loop/message_loop.h#581>) * <http://blog.csdn.net/zero_lee/article/details/7905121> * <http://www.360doc.com/content/13/0422/16/168576_280145531.shtml> Original link: http://avfisher.win/archives/619 id SSV:92545 last seen 2017-11-19 modified 2016-11-21 published 2016-11-21 reporter Root title Chrome the improper use of Flash message loop leads to the UXSS Vulnerability, CVE-2016-1631) bulletinFamily exploit description #### VULNERABILITY DETAILS From /content/renderer/pepper/ppb_flash_message_loop_impl. cc: `int32_t PPB_Flash_MessageLoop_Impl::InternalRun( const RunFromHostProxyCallback& callback) { (...) // It is possible that the PPB_Flash_MessageLoop_Impl object has been // destroyed when the nested message loop exits. scoped_refptr<State> state_protector(state_); { base::MessageLoop::ScopedNestableTaskAllower allow( base::MessageLoop::current()); base::MessageLoop::current()->Run(); } (...) }` |PPB_Flash_MessageLoop_Impl::InternalRun| doesn't initialize a ScopedPageLoadDeferrer before spinning an event loop. As a result, cross-origin documents can be loaded at an arbitrary javascript execution point. #### VERSION Chrome 47.0.2526.80 (Stable) Chrome 48.0.2564.41 (Beta) Chrome 49.0.2587.3 (Dev) Chromium 49.0.2591.0 + Pepper Flash (Release build compiled today) Attachment: [CVE-2016-1631.zip](<http://paper.seebug.org/papers/Archive/poc/CVE-2016-1631.zip>) id SSV:93025 last seen 2017-11-19 modified 2017-04-24 published 2017-04-24 reporter Root title Chrome Universal XSS using Flash message loop (CVE-2016-1631)
References
- http://googlechromereleases.blogspot.com/2016/03/stable-channel-update.html
- http://googlechromereleases.blogspot.com/2016/03/stable-channel-update.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00014.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00014.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00015.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00015.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00018.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00018.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00028.html
- http://lists.opensuse.org/opensuse-security-announce/2016-03/msg00028.html
- http://www.debian.org/security/2016/dsa-3507
- http://www.debian.org/security/2016/dsa-3507
- http://www.securityfocus.com/bid/84008
- http://www.securityfocus.com/bid/84008
- http://www.securitytracker.com/id/1035185
- http://www.securitytracker.com/id/1035185
- http://www.ubuntu.com/usn/USN-2920-1
- http://www.ubuntu.com/usn/USN-2920-1
- https://code.google.com/p/chromium/issues/detail?id=569496
- https://code.google.com/p/chromium/issues/detail?id=569496
- https://codereview.chromium.org/1559113002/
- https://codereview.chromium.org/1559113002/
- https://security.gentoo.org/glsa/201603-09
- https://security.gentoo.org/glsa/201603-09