Vulnerabilities > CVE-2015-7755 - Improper Authentication vulnerability in Juniper Screenos 6.3.0
Attack vector
UNKNOWN Attack complexity
UNKNOWN Privileges required
UNKNOWN Confidentiality impact
UNKNOWN Integrity impact
UNKNOWN Availability impact
UNKNOWN Summary
Juniper ScreenOS 6.2.0r15 through 6.2.0r18, 6.3.0r12 before 6.3.0r12b, 6.3.0r13 before 6.3.0r13b, 6.3.0r14 before 6.3.0r14b, 6.3.0r15 before 6.3.0r15b, 6.3.0r16 before 6.3.0r16b, 6.3.0r17 before 6.3.0r17b, 6.3.0r18 before 6.3.0r18b, 6.3.0r19 before 6.3.0r19b, and 6.3.0r20 before 6.3.0r21 allows remote attackers to obtain administrative access by entering an unspecified password during a (1) SSH or (2) TELNET session.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| OS | 4 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Authentication Abuse An attacker obtains unauthorized access to an application, service or device either through knowledge of the inherent weaknesses of an authentication mechanism, or by exploiting a flaw in the authentication scheme's implementation. In such an attack an authentication mechanism is functioning but a carefully controlled sequence of events causes the mechanism to grant access to the attacker. This attack may exploit assumptions made by the target's authentication procedures, such as assumptions regarding trust relationships or assumptions regarding the generation of secret values. This attack differs from Authentication Bypass attacks in that Authentication Abuse allows the attacker to be certified as a valid user through illegitimate means, while Authentication Bypass allows the user to access protected material without ever being certified as an authenticated user. This attack does not rely on prior sessions established by successfully authenticating users, as relied upon for the "Exploitation of Session Variables, Resource IDs and other Trusted Credentials" attack patterns.
- Exploiting Trust in Client (aka Make the Client Invisible) An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Utilizing REST's Trust in the System Resource to Register Man in the Middle This attack utilizes a REST(REpresentational State Transfer)-style applications' trust in the system resources and environment to place man in the middle once SSL is terminated. Rest applications premise is that they leverage existing infrastructure to deliver web services functionality. An example of this is a Rest application that uses HTTP Get methods and receives a HTTP response with an XML document. These Rest style web services are deployed on existing infrastructure such as Apache and IIS web servers with no SOAP stack required. Unfortunately from a security standpoint, there frequently is no interoperable identity security mechanism deployed, so Rest developers often fall back to SSL to deliver security. In large data centers, SSL is typically terminated at the edge of the network - at the firewall, load balancer, or router. Once the SSL is terminated the HTTP request is in the clear (unless developers have hashed or encrypted the values, but this is rare). The attacker can utilize a sniffer such as Wireshark to snapshot the credentials, such as username and password that are passed in the clear once SSL is terminated. Once the attacker gathers these credentials, they can submit requests to the web service provider just as authorized user do. There is not typically an authentication on the client side, beyond what is passed in the request itself so once this is compromised, then this is generally sufficient to compromise the service's authentication scheme.
- Man in the Middle Attack This type of attack targets the communication between two components (typically client and server). The attacker places himself in the communication channel between the two components. Whenever one component attempts to communicate with the other (data flow, authentication challenges, etc.), the data first goes to the attacker, who has the opportunity to observe or alter it, and it is then passed on to the other component as if it was never intercepted. This interposition is transparent leaving the two compromised components unaware of the potential corruption or leakage of their communications. The potential for Man-in-the-Middle attacks yields an implicit lack of trust in communication or identify between two components.
Metasploit
| description | This module scans for the Juniper SSH backdoor (also valid on Telnet). Any username is required, and the password is <<< %s(un='%s') = %u. |
| id | MSF:AUXILIARY/SCANNER/SSH/JUNIPER_BACKDOOR |
| last seen | 2020-06-13 |
| modified | 2020-02-18 |
| published | 2016-03-30 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/auxiliary/scanner/ssh/juniper_backdoor.rb |
| title | Juniper SSH Backdoor Scanner |
Nessus
NASL family Firewalls NASL id SCREENOS_JSA10713.NASL description The remote host is running a version of Juniper ScreenOS that is 6.2.x prior to 6.2.0r19 or 6.3.x prior to 6.3.0r21. It is, therefore, affected by multiple vulnerabilities : - A backdoor exists that allows a remote attacker administrative access to the device over SSH or telnet. (CVE-2015-7755) - An unspecified flaw exists that allows a man-in-the-middle attacker to decrypt VPN traffic. (CVE-2015-7756) Note that Nessus has not tested for these issues but has instead relied only on the application last seen 2020-06-01 modified 2020-06-02 plugin id 87507 published 2015-12-18 reporter This script is Copyright (C) 2015-2018 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/87507 title Juniper ScreenOS 6.2.0r15 < 6.2.0r19 / 6.3.0r12 < 6.3.0r21 Multiple Vulnerabilities (JSA10713) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(87507); script_version("1.13"); script_cvs_date("Date: 2018/09/17 21:46:53"); script_cve_id("CVE-2015-7755", "CVE-2015-7756"); script_bugtraq_id(79626); script_xref(name:"JSA", value:"JSA10713"); script_xref(name:"CERT", value:"640184"); script_name(english:"Juniper ScreenOS 6.2.0r15 < 6.2.0r19 / 6.3.0r12 < 6.3.0r21 Multiple Vulnerabilities (JSA10713)"); script_summary(english:"Checks version of ScreenOS."); script_set_attribute(attribute:"synopsis", value: "The remote host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote host is running a version of Juniper ScreenOS that is 6.2.x prior to 6.2.0r19 or 6.3.x prior to 6.3.0r21. It is, therefore, affected by multiple vulnerabilities : - A backdoor exists that allows a remote attacker administrative access to the device over SSH or telnet. (CVE-2015-7755) - An unspecified flaw exists that allows a man-in-the-middle attacker to decrypt VPN traffic. (CVE-2015-7756) Note that Nessus has not tested for these issues but has instead relied only on the application's self-reported version number."); script_set_attribute(attribute:"see_also", value:"https://kb.juniper.net/InfoCenter/index?page=content&id=JSA10713"); script_set_attribute(attribute:"solution", value: "Upgrade to Juniper ScreenOS 6.2.0r19 / 6.3.0r21 or later. Alternatively, apply the appropriate patch referenced in the vendor advisory."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:U/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:U/RL:O/RC:C"); script_set_attribute(attribute:"cvss_score_source", value:"CVE-2015-7755"); script_set_attribute(attribute:"exploitability_ease", value:"No known exploits are available"); script_set_attribute(attribute:"exploit_available", value:"false"); script_set_attribute(attribute:"vuln_publication_date",value:"2015/12/17"); script_set_attribute(attribute:"patch_publication_date",value:"2015/12/17"); script_set_attribute(attribute:"plugin_publication_date", value:"2015/12/18"); script_set_attribute(attribute:"plugin_type",value:"local"); script_set_attribute(attribute:"cpe",value:"cpe:/o:juniper:screenos"); script_set_attribute(attribute:"in_the_news", value:"true"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Firewalls"); script_copyright(english:"This script is Copyright (C) 2015-2018 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("screenos_version.nbin"); script_require_keys("Host/Juniper/ScreenOS/display_version", "Host/Juniper/ScreenOS/version"); exit(0); } include("audit.inc"); include("global_settings.inc"); include("misc_func.inc"); app_name = "Juniper ScreenOS"; display_version = get_kb_item_or_exit("Host/Juniper/ScreenOS/display_version"); version = get_kb_item_or_exit("Host/Juniper/ScreenOS/version"); respin_version = get_kb_item("Host/Juniper/ScreenOS/respin_version"); display_fix = ""; # Fixes: 6.2.0r19, 6.3.0r21 if (version =~ "^6\.2([^0-9]|$)" && ver_compare(ver:version, minver:"6.2.0.15", fix:"6.2.0.19", strict:FALSE) == -1) display_fix = "6.2.0r19"; else if (version =~ "^6\.3([^0-9]|$)" && ver_compare(ver:version, minver:"6.3.0.12", fix:"6.3.0.21", strict:FALSE) == -1) { if(version =~ "^6\.3\.0\.1[2-9](\.0)?$") { if((respin_version !~ "^[b-z]" && !isnull(respin_version)) || isnull(respin_version)) display_fix = "6.3.0r1" + version[7] + "b"; } else display_fix = "6.3.0r21"; } if(display_fix) { port = 0; if (report_verbosity > 0) { report = '\n Installed version : ' + display_version + '\n Fixed version : ' + display_fix + '\n'; security_hole(extra:report, port:port); } else security_hole(port); exit(0); } else audit(AUDIT_INST_VER_NOT_VULN, app_name, display_version);NASL family Default Unix Accounts NASL id SCREENOS_SSH_AUTH_BYPASS.NASL description The account last seen 2020-06-01 modified 2020-06-02 plugin id 87601 published 2015-12-23 reporter This script is Copyright (C) 2015-2018 Tenable Network Security, Inc. source https://www.tenable.com/plugins/nessus/87601 title Juniper ScreenOS SSH / Telnet Authentication Backdoor code # # (C) Tenable Network Security, Inc. # account = "netscreen"; password = "<<< %s(un='%s') = %u"; include("compat.inc"); if (description) { script_id(87601); script_version("1.10"); script_cvs_date("Date: 2018/07/27 18:38:14"); script_cve_id("CVE-2015-7755"); script_bugtraq_id(79626); script_xref(name:"JSA", value:"JSA10713"); script_xref(name:"CERT", value:"640184"); script_name(english:"Juniper ScreenOS SSH / Telnet Authentication Backdoor"); script_summary(english:"Attempts to log in to the remote host."); script_set_attribute(attribute:"synopsis", value: "An account on the remote host uses a known password."); script_set_attribute(attribute:"description", value: "The account 'netscreen' on the remote host has the password '" + password +"', a known backdoor password. The affected devices are firewalls and VPN gateways. A remote attacker can exploit this vulnerability to gain administrative access and monitor network traffic, deny network access, and alter device and firewall configurations."); # https://forums.juniper.net/t5/Security-Incident-Response/Important-Announcement-about-ScreenOS/ba-p/285554 script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?f6cfb32d"); script_set_attribute(attribute:"see_also", value:"https://kb.juniper.net/InfoCenter/index?page=content&id=JSA10713"); script_set_attribute(attribute:"solution", value: "Upgrade to Juniper ScreenOS 6.2.0r19 / 6.3.0r21 or later. Alternatively, apply the appropriate patch referenced in the vendor advisory."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:U/RL:TF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:U/RL:T/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"No known exploits are available"); script_set_attribute(attribute:"exploit_available", value:"false"); script_set_attribute(attribute:"vuln_publication_date", value:"2015/12/17"); script_set_attribute(attribute:"patch_publication_date", value:"2015/12/17"); script_set_attribute(attribute:"plugin_publication_date", value:"2015/12/23"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"default_account", value:"true"); script_set_attribute(attribute:"in_the_news", value:"true"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Default Unix Accounts"); script_copyright(english:"This script is Copyright (C) 2015-2018 Tenable Network Security, Inc."); script_dependencies("ssh_detect.nasl", "account_check.nasl", "telnetserver_detect_type_nd_version.nasl"); script_require_ports("Services/telnet", 23, "Services/ssh", 22); script_exclude_keys("global_settings/supplied_logins_only"); exit(0); } include("audit.inc"); include("default_account.inc"); include("global_settings.inc"); if (supplied_logins_only) audit(AUDIT_SUPPLIED_LOGINS_ONLY); affected = FALSE; ssh_ports = get_service_port_list(svc: "ssh", default:22); foreach port (ssh_ports) { ssh_port = check_account(login:account, password:password, cmd:"get clock", cmd_regex:"The Network Time Protocol", nosh:TRUE, noexec:TRUE, check_telnet:TRUE, port:port, svc:"ssh"); if (ssh_port) { affected = TRUE; security_report_v4(port:telnet_port, severity:SECURITY_HOLE, extra:default_account_report()); } } if(affected) exit(0); telnet_ports = get_service_port_list(svc: "telnet", default:23); foreach port (telnet_ports) { telnet_port = check_account(login:account, password:password, cmd:"get clock", cmd_regex:"The Network Time Protocol", nosh:TRUE, noexec:TRUE, check_telnet:TRUE, port:port, svc:"telnet"); if (telnet_port) { affected = TRUE; security_report_v4(port:telnet_port, severity:SECURITY_HOLE, extra:default_account_report()); } } if(!affected) audit(AUDIT_HOST_NOT, "affected");
Seebug
bulletinFamily exploit description ``` Author: xiaohu & mt (知道创宇404安全实验室) Date: 2015-12-23 ``` ## 漏洞信息: Juniper 网络公司(瞻博网络)作为全球领先的联网和安全性解决方案供应商,Juniper 网络公司对依赖网络获得战略性收益的客户一直给予密切关注。公司的客户来自全球各行各业,包括主要的网络运营商、企业、政府机构以及研究和教育机构等。Juniper 网络公司推出的一系列联网解决方案,提供所需的安全性和性能来支持全球最大型、最复杂、要求最严格的关键网络。 Juniper 网络公司在上周发表声明,称 NetScreen 与 Juniper SSG 防火墙产品使用的操作系统 Juniper ScreenOS 中发现高危漏洞 CVE-2015-7756。涉及设备 VPN 加密伪随机密钥可被破解的漏洞。 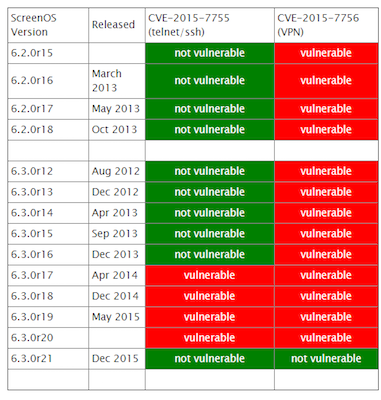 ## 漏洞分析: 首先,需要了解涉及 Juniper 的 VPN加密的几个关键函数,其次相互关系和作用。其调用关系如下表所示: 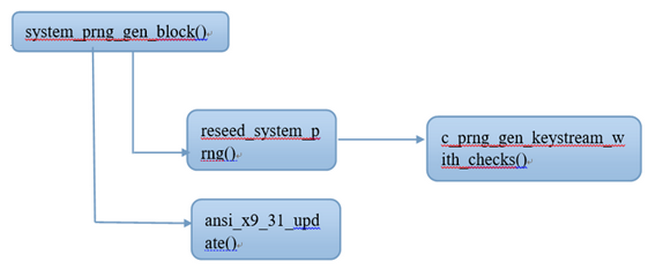 上表中 reseed_system_prng 函数的作用是生成SEED和3DES密钥, 函数 ansi_x9_31_update 作用是迭代混淆。ansi_x9_31_update函数的流程图如下:  如图所示,T 为 8字节随机数,但四个字节固定为 0,所以只有四个字节是随机数。T的生成方式为此时机器的 Timer(计时器读值)。system_prng_gen_block 和 reseed_system_prng 函数绝大部分代码已被逆向出来,其伪代码见附录。至此,基于对上述关键函数的分析,国外大牛 RPW 声称:“暂时没有发现一种切实可行的漏洞利用方法解密Juniper 的 VPN加密,但是会持续关注这个这个漏洞,而且他怀疑他错过一些东西!有时间的话他会用硬件 JTAG 调试器分析”。 在 system_prng_gen_block 伪代码中,有关键的一行并没有得到深入分析。如下:通过这句代码,我们可以根据固件推出在一个随机种子用来初始化的 prngseed。逆向ssg5ssg20.6.3.0r19.0 固件得到伪代码,从中可以找到如下代码片段: 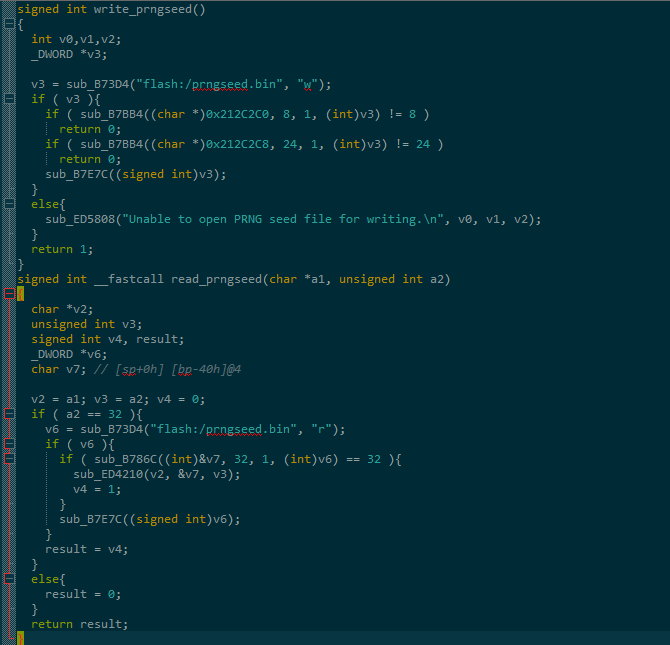 通过上述代码段,可以得到一种可能的 VPN 解密方式:在获取系统控制权或者听过其他漏洞或方法读出 prngseed 的32个字节,暴力破解 T(后4字节伪机数),最后可以实现对 VPN 的解密。另外一种可能,同时如果厂家的 prngseed 的生成机制,被泄漏出来,则 VPN 直接可以被解密。以上为我们的初步分析,我们将进一步对 Juniper 漏洞深入分析。 ## 漏洞影响: 我们从 ZoomEye 平台对全球 ScreenOS 设备分析统计发现,开放了 Telnet 服务的总数高达 34000 台。 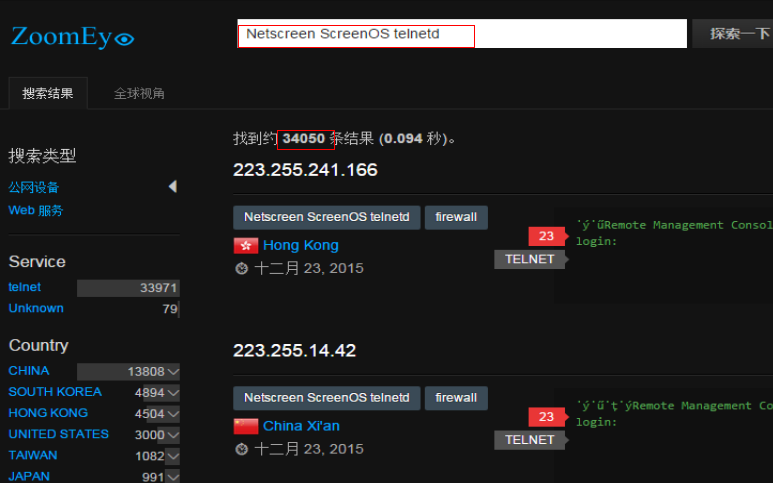 目前知道创宇 Sebug 照妖镜已提供对绕过 ScreenOS 身份认证漏洞在线检测,利用此功能可以针对 ScreenOS 设备进行测试,如果存在漏洞建议立即升级设备固件。Sebug 提供最新漏洞信息、漏洞搜索、漏洞修复、漏洞目录、安全文档、漏洞趋势分析等服务。 ## 解决方案: 目前 Juniper 网络公司已对 ScreenOS 受漏洞影响版本进行了修复。可进入官网下载设备型号相对应的固件版本进行升级。(链接:http://www.juniper.net/support/downloads/screenos.html) 另外需要说明的是,针对使用后门绕过认证,获取设备管理员权限,会被 ScreenOS 日志记录,如果一旦设备被完全控制,日志将变的不可靠,建议立即升级 ScreenOS 设备固件,如果因客观因素无法升级设备固件,应该限制对设备访问的 IP,为了进一步安全考虑,可以增加网络日志服务器,ScreenOS 所有日志发生时自动导入网络日志服务器,相对而言远程存储日志比本地存储日志被窜改的概率将会降低很多。 ## 参考资料 https://community.rapid7.com/community/infosec/blog/2015/12/20/cve-2015-7755-juniper-screenos-authentication-backdoor https://kb.juniper.net/InfoCenter/index?page=content&id=JSA10713&cat=SIRT_1&actp=LIST https://rpw.sh/blog/2015/12/21/the-backdoored-backdoor/ https://github.com/hdm/juniper-cve-2015-7755 http://www.juniper.net/support/downloads/screenos.html id SSV:90140 last seen 2017-11-19 modified 2015-12-21 published 2015-12-21 reporter Root title Juniper Networks(瞻博网络)未授权访问漏洞 bulletinFamily exploit description EC Consult has found a backdoor in Sony IPELA Engine IP Cameras, mainly used professionally by enterprises and authorities. This backdoor allows an attacker to run arbitrary code on the affected IP cameras. An attacker can use cameras to take a foothold in a network and launch further attacks, disrupt camera functionality, send manipulated images/video, add cameras into a Mirai-like botnet or to just simply spy on you. This vulnerability affects 80 different Sony camera models. Sony was informed by SEC Consult about the vulnerability and has since released updated firmware for the affected models. Further information about the backdoor, disclosure timeline, affected devices and updated firmware can be found in [our advisory](https://www.sec-consult.com/fxdata/seccons/prod/temedia/advisories_txt/20161206-0_Sony_IPELA_Engine_IP_Cameras_Backdoors_v10.txt). This blog post has some highlights from the vulnerability analysis.This advisory is the result of research that started by uploading a recent firmware update file from a Sony camera into our cloud based firmware analysis system IoT Inspector. After a few minutes the analysis results were available. One result immediately caught our attention: 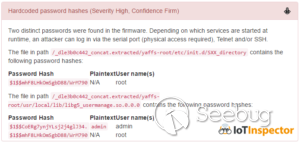 Excerpt from IoT Inspector results So here we have two password hashes, one is for the user admin and was cracked immediately. The password is admin. This is no surprise as the default login credentials are admin:admin. The second password hash is much more interesting, it’s for the user root and it was found in two different files: ``` /etc/init.d/SXX_directory and /usr/local/lib/libg5_usermanage.so.0.0.0 ``` We can use the file system browser of IoT Inspector to have a look at the SXX_directory. 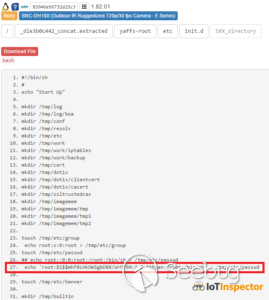 Excerpt from IoT Inspector filesystem browser It looks like this startup script (called by /sbin/init/rcS during boot) is responsible for creating and populating the file /tmp/etc/passwd (/etc/passwd is a symlink to this file). A line for the user including a password hash is added, the shell is /bin/sh. Not good! So, what can we do if we can crack the hash? At this point we can assume that it’s very likely we can login using UART pins on the PCB. This of course requires us to have physical access and to disassemble the device. The other locations where we could possibly use the password are Telnet and SSH, but both services are not available on the device … or are they? A quick string search in the firmware’s filesystem for “telnet” shows that a CGI binary called prima-factory.cgi contains this string a few times. IDA Pro to the rescue! It seems this CGI has the power to do something with Telnet: 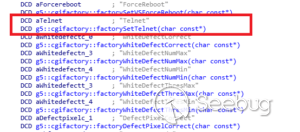 The code in g5::cgifactory::factorySetTelnet() (in decompiled form below) is pretty straight forward. Based on input, the inetd daemon is killed or started:  The inetd daemon gets its configuration from /etc/inetd.conf and inetd.conf is set up to launch Telnet 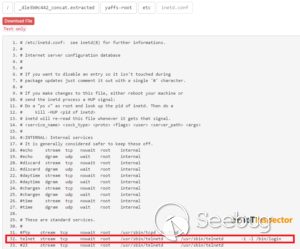 So how can we reach this CGI functionality? The answer lies in the lighttpd binary. Lighttpd is an open source web server that was modified by Sony. Some custom code for HTTP request handling and authentication was added. Below is an excerpt from a data structure that maps the URI /command/prima-factory.cgi to the CGI in the file system. The authentication function is HandleFactory.  HandleFactory decodes the HTTP Basic Authentication header and compares it to the username/password primana:primana.  #### Now we have all ingredients to craft an attack that looks like this: * Send HTTP requests to /command/prima-factory.cgi containing the “secret” request values cPoq2fi4cFk and zKw2hEr9 and use primana:primana for HTTP authentication. This starts the Telnet service on the device. * Login using the cracked root credentials via Telnet. Note: We have not cracked the root password, but it’s only a matter of time until someone will. The user primana has access to other functionality intended for device testing or factory calibration(?). There is another user named debug with the password popeyeConnection that has access to other CGI functionality we didn’t analyze further. We believe that this backdoor was introduced by Sony developers on purpose (maybe as a way to debug the device during development or factory functional testing) and not an “unauthorized third party” like in other cases (e.g. the Juniper ScreenOS Backdoor, CVE-2015-7755). We have asked Sony some questions regarding the nature of the backdoor, intended purpose, when it was introduced and how it was fixed, but they did not answer. id SSV:97275 last seen 2018-06-26 modified 2018-05-08 published 2018-05-08 reporter My Seebug title BACKDOOR IN SONY IPELA ENGINE IP CAMERAS
References
- http://arstechnica.com/security/2015/12/unauthorized-code-in-juniper-firewalls-decrypts-encrypted-vpn-traffic/
- http://arstechnica.com/security/2015/12/unauthorized-code-in-juniper-firewalls-decrypts-encrypted-vpn-traffic/
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10713
- http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10713
- http://twitter.com/cryptoron/statuses/677900647560253442
- http://twitter.com/cryptoron/statuses/677900647560253442
- http://www.forbes.com/sites/thomasbrewster/2015/12/18/juniper-says-it-didnt-work-with-government-to-add-unauthorized-code-to-network-gear/
- http://www.forbes.com/sites/thomasbrewster/2015/12/18/juniper-says-it-didnt-work-with-government-to-add-unauthorized-code-to-network-gear/
- http://www.kb.cert.org/vuls/id/640184
- http://www.kb.cert.org/vuls/id/640184
- http://www.securityfocus.com/bid/79626
- http://www.securityfocus.com/bid/79626
- http://www.securitytracker.com/id/1034489
- http://www.securitytracker.com/id/1034489
- http://www.wired.com/2015/12/juniper-networks-hidden-backdoors-show-the-risk-of-government-backdoors/
- http://www.wired.com/2015/12/juniper-networks-hidden-backdoors-show-the-risk-of-government-backdoors/
- https://adamcaudill.com/2015/12/17/much-ado-about-juniper/
- https://adamcaudill.com/2015/12/17/much-ado-about-juniper/
- https://forums.juniper.net/t5/Security-Incident-Response/Important-Announcement-about-ScreenOS/ba-p/285554
- https://forums.juniper.net/t5/Security-Incident-Response/Important-Announcement-about-ScreenOS/ba-p/285554
- https://github.com/hdm/juniper-cve-2015-7755
- https://github.com/hdm/juniper-cve-2015-7755