Vulnerabilities > CVE-2015-0057 - Permissions, Privileges, and Access Controls vulnerability in Microsoft products
Attack vector
UNKNOWN Attack complexity
UNKNOWN Privileges required
UNKNOWN Confidentiality impact
UNKNOWN Integrity impact
UNKNOWN Availability impact
UNKNOWN Summary
win32k.sys in the kernel-mode drivers in Microsoft Windows Server 2003 SP2, Windows Vista SP2, Windows Server 2008 SP2 and R2 SP1, Windows 7 SP1, Windows 8, Windows 8.1, Windows Server 2012 Gold and R2, and Windows RT Gold and 8.1 allows local users to gain privileges via a crafted application, aka "Win32k Elevation of Privilege Vulnerability."
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Accessing, Modifying or Executing Executable Files An attack of this type exploits a system's configuration that allows an attacker to either directly access an executable file, for example through shell access; or in a possible worst case allows an attacker to upload a file and then execute it. Web servers, ftp servers, and message oriented middleware systems which have many integration points are particularly vulnerable, because both the programmers and the administrators must be in synch regarding the interfaces and the correct privileges for each interface.
- Leverage Executable Code in Non-Executable Files An attack of this type exploits a system's trust in configuration and resource files, when the executable loads the resource (such as an image file or configuration file) the attacker has modified the file to either execute malicious code directly or manipulate the target process (e.g. application server) to execute based on the malicious configuration parameters. Since systems are increasingly interrelated mashing up resources from local and remote sources the possibility of this attack occurring is high. The attack can be directed at a client system, such as causing buffer overrun through loading seemingly benign image files, as in Microsoft Security Bulletin MS04-028 where specially crafted JPEG files could cause a buffer overrun once loaded into the browser. Another example targets clients reading pdf files. In this case the attacker simply appends javascript to the end of a legitimate url for a pdf (http://www.gnucitizen.org/blog/danger-danger-danger/) http://path/to/pdf/file.pdf#whatever_name_you_want=javascript:your_code_here The client assumes that they are reading a pdf, but the attacker has modified the resource and loaded executable javascript into the client's browser process. The attack can also target server processes. The attacker edits the resource or configuration file, for example a web.xml file used to configure security permissions for a J2EE app server, adding role name "public" grants all users with the public role the ability to use the administration functionality. The server trusts its configuration file to be correct, but when they are manipulated, the attacker gains full control.
- Blue Boxing This type of attack against older telephone switches and trunks has been around for decades. A tone is sent by an adversary to impersonate a supervisor signal which has the effect of rerouting or usurping command of the line. While the US infrastructure proper may not contain widespread vulnerabilities to this type of attack, many companies are connected globally through call centers and business process outsourcing. These international systems may be operated in countries which have not upgraded Telco infrastructure and so are vulnerable to Blue boxing. Blue boxing is a result of failure on the part of the system to enforce strong authorization for administrative functions. While the infrastructure is different than standard current applications like web applications, there are historical lessons to be learned to upgrade the access control for administrative functions.
- Restful Privilege Elevation Rest uses standard HTTP (Get, Put, Delete) style permissions methods, but these are not necessarily correlated generally with back end programs. Strict interpretation of HTTP get methods means that these HTTP Get services should not be used to delete information on the server, but there is no access control mechanism to back up this logic. This means that unless the services are properly ACL'd and the application's service implementation are following these guidelines then an HTTP request can easily execute a delete or update on the server side. The attacker identifies a HTTP Get URL such as http://victimsite/updateOrder, which calls out to a program to update orders on a database or other resource. The URL is not idempotent so the request can be submitted multiple times by the attacker, additionally, the attacker may be able to exploit the URL published as a Get method that actually performs updates (instead of merely retrieving data). This may result in malicious or inadvertent altering of data on the server.
- Target Programs with Elevated Privileges This attack targets programs running with elevated privileges. The attacker would try to leverage a bug in the running program and get arbitrary code to execute with elevated privileges. For instance an attacker would look for programs that write to the system directories or registry keys (such as HKLM, which stores a number of critical Windows environment variables). These programs are typically running with elevated privileges and have usually not been designed with security in mind. Such programs are excellent exploit targets because they yield lots of power when they break. The malicious user try to execute its code at the same level as a privileged system call.
Exploit-Db
description Microsoft Windows win32k Local Privilege Escalation (MS15-010). CVE-2015-0057. Local exploit for win64 platform file exploits/windows_x86-64/local/39035.txt id EDB-ID:39035 last seen 2016-02-04 modified 2015-12-18 platform windows_x86-64 port published 2015-12-18 reporter Jean-Jamil Khalife source https://www.exploit-db.com/download/39035/ title Microsoft Windows win32k Local Privilege Escalation MS15-010 type local description Microsoft Windows - Local Privilege Escalation (MS15-010). CVE-2015-0003,CVE-2015-0010,CVE-2015-0057,CVE-2015-0058,CVE-2015-0059,CVE-2015-0060. Local exploit... id EDB-ID:37098 last seen 2016-02-04 modified 2015-05-25 published 2015-05-25 reporter Sky lake source https://www.exploit-db.com/download/37098/ title Microsoft Windows - Local Privilege Escalation MS15-010
Msbulletin
| bulletin_id | MS15-010 |
| bulletin_url | |
| date | 2015-02-10T00:00:00 |
| impact | Remote Code Execution |
| knowledgebase_id | 3036220 |
| knowledgebase_url | |
| severity | Critical |
| title | Vulnerabilities in Windows Kernel-Mode Driver Could Allow Remote Code Execution |
Nessus
| NASL family | Windows : Microsoft Bulletins |
| NASL id | SMB_NT_MS15-010.NASL |
| description | The remote Windows host is missing a security patch. It is, therefore, affected by the following vulnerabilities : - A privilege escalation vulnerability exists in the Windows kernel-mode driver that is caused by improperly handling objects in memory. (CVE-2015-0003, CVE-2015-0057) - A security feature bypass vulnerability exists in the Cryptography Next Generation kernel-mode driver when failing to properly validate and enforce impersonation levels. (CVE-2015-0010) - A privilege escalation vulnerability exists in the Windows kernel-mode driver due to a double-free condition. (CVE-2015-0058) - A remote code execution vulnerability exists in the Windows kernel-mode driver that is caused when improperly handling TrueType fonts. (CVE-2015-0059) - A denial of service vulnerability exists in the Windows kernel-mode driver that is caused when the Windows font mapper attempts to scale a font. (CVE-2015-0060) |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 81263 |
| published | 2015-02-10 |
| reporter | This script is Copyright (C) 2015-2018 Tenable Network Security, Inc. |
| source | https://www.tenable.com/plugins/nessus/81263 |
| title | MS15-010: Vulnerabilities in Windows Kernel-Mode Driver Could Allow Remote Code Execution (3036220) |
| code | |
Seebug
| bulletinFamily | exploit |
| description | 来源链接:http://www.freebuf.com/vuls/90501.html FreeBuf黑客与极客(FreeBuf.COM) 原文地址:http://hdwsec.fr/blog/CVE-2015-0057.html,编译/FB小编鸢尾 **概述** 这是一个use-after-free内核漏洞,它能获取一个专属的write primitive操作,之后侵染临近的一个对象。这个yields语句可以在内核空间或者用户空间随意写入。 更准确的说,这个use-after-free触发器利用scrollbar对象,然后通过一个新的proplist对象(同样大小)替换freed对象。正是因为use-after-free,新对象的header会被一个OR primitive修改。 win32k !xxxEnableWndSBArrows+0xaa: fffff960`0036cdfe 0903 or dword ptr [rbx],eax 该漏洞导致对象属性的最大值增加,这样你就可以将数据push到堆中。通过SetProp(HWND hWnd, LPCTSTR lpString, HANDLE hData)增加一个新属性,可以覆盖下一个对象。 在下文中,我们将使用"SetProp(hWnd, V1, V2)"来代替表示"SetProp(HWND hWnd, LPCTSTR lpString, HANDLE hData)" **在Windows 8.1 (64-bit)上利用** 根据FireEye的报告,有恶意软件使用了上面我们讨论的技术侵染一个临近的菜单对象。事实上,其中有一张截图就显示了tagMENU.rgItems和tagMENU.cItems的值被覆盖。 typedef struct _MENU { … DWORD cItems // number of items contained by the items array … PITEM rgItems // pointer to the items array … } 这在Windows XP下提供了一个write primitive操作,覆盖nt!HalDispatchTable+0×4。接下来我们根据FireEye以及NCC Group所提供的技术细节,在Windows 8.1 64-bit下尝试进行漏洞复现。 我们可能会遇到以下障碍: 1.攻击者不能完全控制每个属性中的内容;虽然V2的8个字节是被完全控制的,但是V1只能使用2个字节。 2.上面提到的_MENU结构有变化,并且由于V1的内容缺乏控制,cItems和rgItems无法完全控制 3.需要绕过ASLR和SMEP 4.需要绕过heap entry编码机制 5.最后覆盖的对象还要记得恢复,以避免当内核释放时造成崩溃 **获取任意写入操作** 为了替代直接覆盖rgItems和cItems,NCC Group发现并提供的一个解决方案涉及对堆的header操作和两个覆盖,以便最终控制一个窗口结构,提供一个读写primitive操作。在此我建议大家可以看看他们提供的解决方案[3],其中的技巧已经写的非常详细了。 我选择控制一个菜单对象,因为它在各种操作系统(从Windows XP到8.1)下提供了一个常见的write primitive;在这种情况下,read primitive的不足对于我们来说也就不存在问题了。 虽然Dyre恶意软件损坏cItems和rgItems,然而我们要做的仅仅只是损坏rgItems字段: a.创建了一个item的菜单,使用CreateMenu()以及InsertMenuItem() b.使用NCC Group提供的覆盖控制方法损坏rgItems(item数组的地址) c.数组的第一个item指向rgItems包含的一个wID字段(我们使用SetMenuItemInfo()进行修改的字段),这也导致我们获得任意write primitive操作 接下来的这一步骤十分经典:nt!HalDispatchTable+8中的一个函数指针被覆盖,然后会运行的payload包括两个阶段: 1.首先恢复桌面堆(desktop heap)以及原始的函数指针 2.第二阶段是一个用于改变当前系统进程token的Shellcode **绕过heap header编码** 在该利用例子中,第一个覆盖的heap header是必须要修改的,之后我们必须在第二个覆盖内容中建立一个假的heap header。这里由于Windows 8.1的heap header是由一个cookie进行编码,为进一步的了解细节,有必要去看看Chris Valasek以及Tarjei Mandt所提供的参考[9][10] NCC Group提供的解决方案依赖于桌面堆(desktop heap)映射的只读用户区域,暴露cookie的值。 首先我们必须找到用于编码heap header的cookie,进而确认桌面堆(desktop heap)的heap base。然后我们可以获取到存储在0×80下的cookie: nt!_HEAP +0x000 Entry : _HEAP_ENTRY +0x010 SegmentSignature : Uint4B […] +0x07c EncodeFlagMask : Uint4B +0x080 Encoding : _HEAP_ENTRY […] 现在就可以通过对编码字段进行xor操作解码heap header 接着解码并修改Entry后,我们只需计算新的SmallTagIndex的校验和: Entry.SmallTagIndex = Entry.SizeLow ^ Entry.SizeHigh ^ Entry.Flags; **在中等完整性等级下绕过ASLR** 在中等完整性权限下ASLR对我们来说没有啥问题: a.使用NtQuerySystemInformation()获取ntoskrnl以及hal.dll的基地址 b.动态获取ROP小工具偏移量,之后恢复后的hal!HaliQuerySystemInformation()会分别读取ntoskrnl.exe和hal.dll 在低等完整性等级下绕过ASLR NtQuerySystemInformation()是不能从一个低等完整性等级下进行调用的。尽管在exploit源代码中没有实现,但是Alex Ionescu [5]提出了一种使用SIDT作为内核信息泄漏的方法,该方法是不会理会完整性等级的。 **绕过SMEP** 早在2011年5月,为了使用户模式页面从内核中执行,Dan Rosenberg就提出了一种十分新颖的方式绕过Linux下的SMEP[6]。j00ru以及Gynvael Coldwind将这一技术进一步应用到到Windows[7]。对于该exploit,我使用了siberas在2014 pwn2own所展示的方法[8] **防止post-exploitation崩溃** 为了防止post-exploitation崩溃,记得一定要清理桌面堆(desktop heap)。事实上,已损坏的对象以及hal!HaliQuerySystemInformation()的原始指针都是需要进行恢复的。 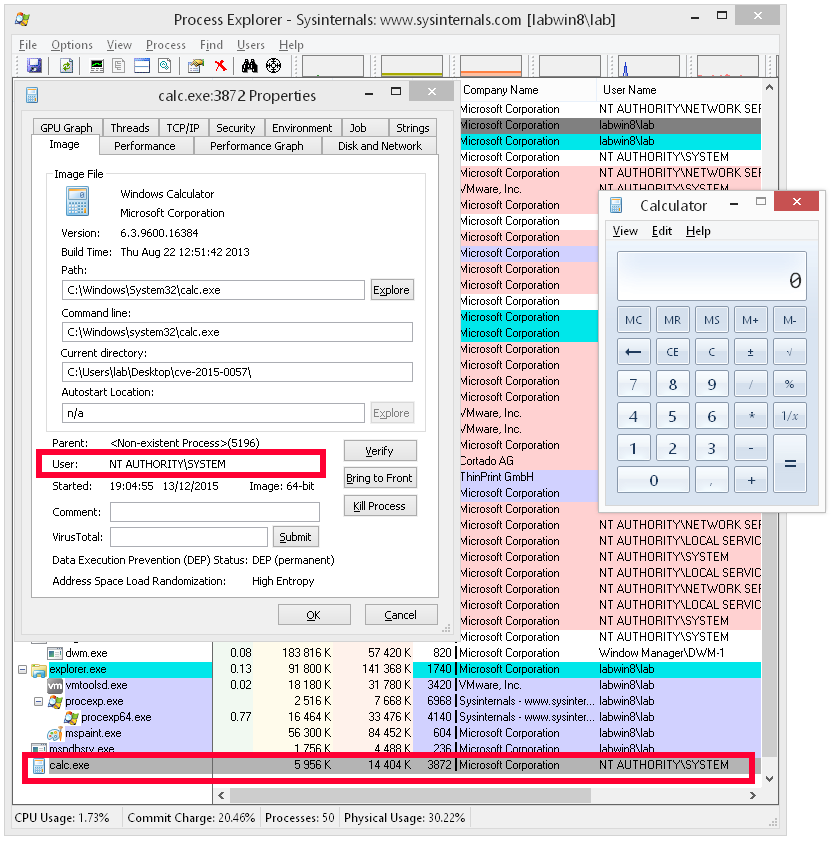 Exp放送 链接: http://pan.baidu.com/s/1kUyvFTH 密码: x5pd 参考文献 [1] http://breakingmalware.com/vulnerabilities/one-bit-rule-bypassing-windows-10-protections-using-single-bit/ [2] https://www.fireeye.com/blog/threat-research/2015/07/dyre_banking_trojan.html [3] https://www.nccgroup.trust/globalassets/newsroom/uk/blog/documents/2015/07/exploiting-cve-2015.pdf [4] https://media.blackhat.com/bh-us-11/Mandt/BH_US_11_Mandt_win32k_WP.pdf [5] http://recon.cx/2013/slides/Recon2013-Alex%20Ionescu-I%20got%2099%20problems%20but%20a%20kernel%20pointer%20ain't%20one.pdf [6] http://vulnfactory.org/blog/2011/06/05/smep-what-is-it-and-how-to-beat-it-on-linux/ [7] http://j00ru.vexillium.org/?p=783 [8] http://www.siberas.de/papers/Pwn2Own_2014_AFD.sys_privilege_escalation.pdf [9] http://illmatics.com/Understanding_the_LFH.pdf [10] http://illmatics.com/Windows%208%20Heap%20Internals.pdf |
| id | SSV:90177 |
| last seen | 2017-11-19 |
| modified | 2015-12-25 |
| published | 2015-12-25 |
| reporter | Root |
| title | Microsoft Windows Win32k 特权提升漏洞( MS15-010) |
The Hacker News
| id | THN:779F212C6D36353406ACF3EBA9C22AB9 |
| last seen | 2018-01-27 |
| modified | 2015-02-13 |
| published | 2015-02-12 |
| reporter | Swati Khandelwal |
| source | https://thehackernews.com/2015/02/bypassing-windows-security.html |
| title | Bypassing Windows Security by modifying 1 Bit Only |
References
- http://www.securityfocus.com/bid/72466
- http://www.securityfocus.com/bid/72466
- https://docs.microsoft.com/en-us/security-updates/securitybulletins/2015/ms15-010
- https://docs.microsoft.com/en-us/security-updates/securitybulletins/2015/ms15-010
- https://exchange.xforce.ibmcloud.com/vulnerabilities/100431
- https://exchange.xforce.ibmcloud.com/vulnerabilities/100431
- https://www.exploit-db.com/exploits/39035/
- https://www.exploit-db.com/exploits/39035/