Security News > 2023 > March > YoroTrooper Stealing Credentials and Information from Government and Energy Organizations
A previously undocumented threat actor dubbed YoroTrooper has been targeting government, energy, and international organizations across Europe as part of a cyber espionage campaign that has been active since at least June 2022.
Prominent countries targeted include Azerbaijan, Tajikistan, Kyrgyzstan, Turkmenistan, and other Commonwealth of Independent States nations.
YoroTrooper's data gathering goals are realized through a combination of commodity and open source stealer malware such as Ave Maria, LodaRAT, Meterpreter, and Stink, with the infection chains using malicious shortcut files and decoy documents wrapped in ZIP or RAR archives that are propagated via spear-phishing.
The use of LodaRAT is notable as it indicates that the malware is being employed by multiple operators despite its attribution to another group called Kasablanka, which has also been observed distributing Ave Maria in recent campaigns targeting Russia.
Other auxiliary tools deployed by YoroTrooper consist of reverse shells and a C-based custom keylogger that's capable of recording keystrokes and saving them to a file on disk.
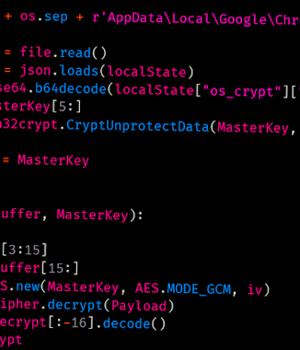
"It is worth noting that while this campaign began with the distribution of commodity malware such as Ave Maria and LodaRAT, it has evolved significantly to include Python-based malware," the researchers said.
News URL
https://thehackernews.com/2023/03/yorotrooper-stealing-credentials-and.html