Vulnerabilities > CVE-2018-10376 - Integer Overflow or Wraparound vulnerability in Smartmesh
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
NONE Integrity impact
PARTIAL Availability impact
NONE Summary
An integer overflow in the transferProxy function of a smart contract implementation for SmartMesh (aka SMT), an Ethereum ERC20 token, allows attackers to accomplish an unauthorized increase of digital assets via crafted _fee and _value parameters, as exploited in the wild in April 2018, aka the "proxyOverflow" issue.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Forced Integer Overflow This attack forces an integer variable to go out of range. The integer variable is often used as an offset such as size of memory allocation or similarly. The attacker would typically control the value of such variable and try to get it out of range. For instance the integer in question is incremented past the maximum possible value, it may wrap to become a very small, or negative number, therefore providing a very incorrect value which can lead to unexpected behavior. At worst the attacker can execute arbitrary code.
Seebug
| bulletinFamily | exploit |
| description | On 4/24/2018, 01:17:50 p.m. UTC, [PeckShield](https://peckshield.com/) again detected an unusual MESH token transaction (shown in Figure 1). In this particular transaction, someone transferred a large amount of MESH token — 0x8fff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff,ffff (63 f’s) to herself along with a huge amount fee — 0x7000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0000,0001 to the address issuing this transaction. 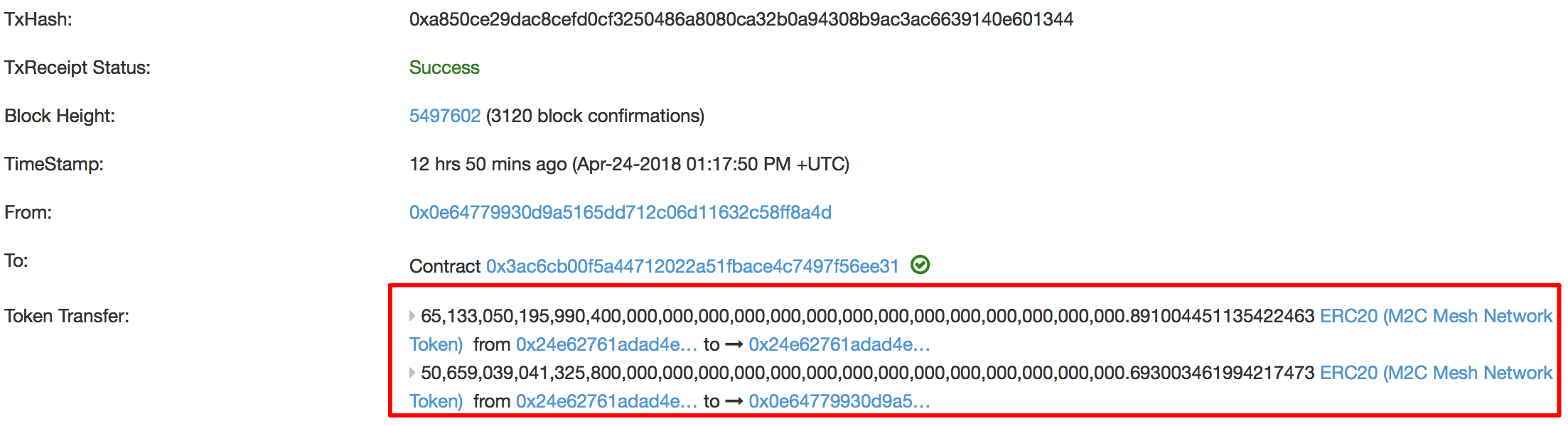 Figure 1: A Suspicious MESH Token Transfer (with huge amount) There’s another case happened to the SMT token at 07:16:19 p.m. UTC with the same attack pattern. 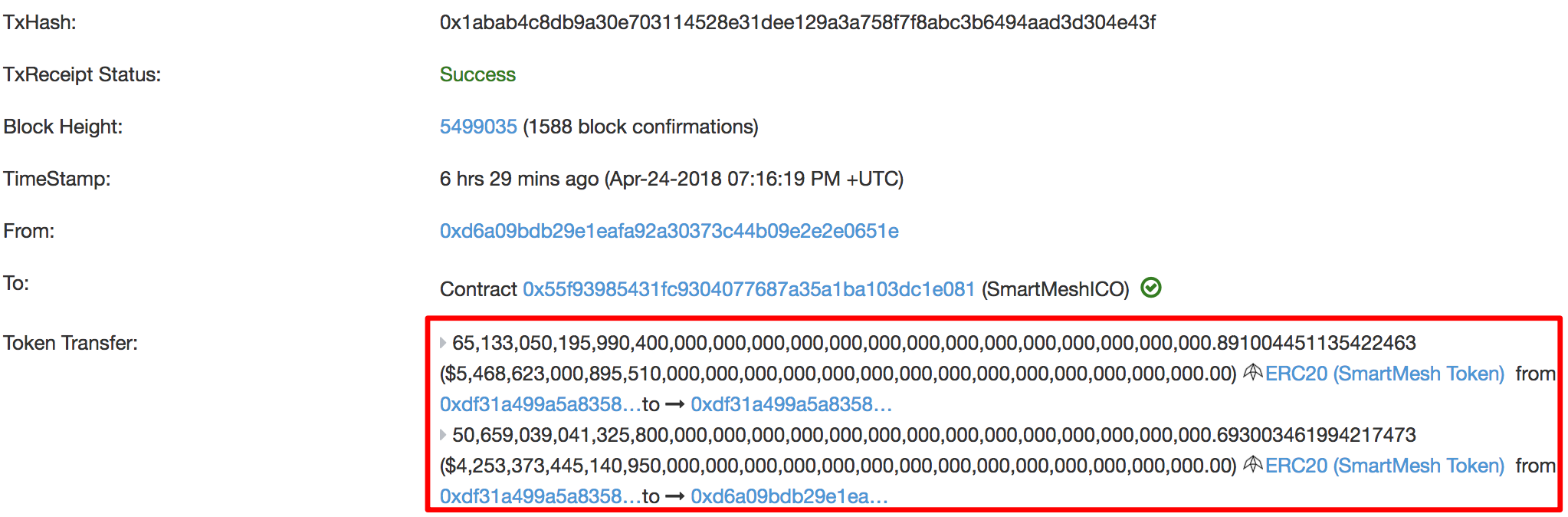 Figure 2: A Suspicious SMT Token Transfer (with huge amount) As we look into the corresponding smart contract, we find out that the proxyTransfer() function has a classic integer overflow problem. 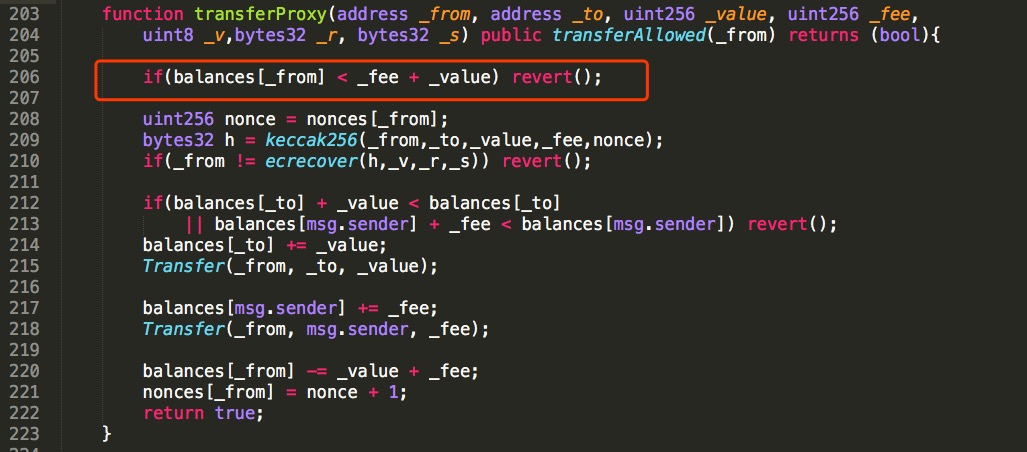 Figure 3: A proxyOverflow-affected Smart Contract As shown in Figure 3, both _fee and _value are input parameters which could be controlled by the attacher. If _fee + _value happens to be 0 (the overflow case), the sanity checks in line 206 could be passed. It means the attacker could transfer huge amount of tokens to an address (line 214) with zero balance. Also, a huge amount fee would be transferred to the msg.sender in line 217. From our system-wide scanning, we have located quite a few ERC20 tokens affected, including | Token | Related Contract | | ------------ | ------------ | | MESH | 0x3ac6cb00f5a44712022a51fbace4c7497f56ee31 | | | 0x01f2acf2914860331c1cb1a9acecda7475e06af8 | | UGToken | 0x43ee79e379e7b78d871100ed696e803e7893b644 | | SMT | 0x55F93985431Fc9304077687a35A1BA103dC1e081 | | SMART | 0x60be37dacb94748a12208a7ff298f6112365e31f | | MTC | 0x8febf7551eea6ce499f96537ae0e2075c5a7301a | | FirstCoin | 0x9e88770da20ebea0df87ad874c2f5cf8ab92f605 | | GG Token | 0xf20b76ed9d5467fdcdc1444455e303257d2827c7 | | CNY Token | 0x041b3eb05560ba2670def3cc5eec2aeef8e5d14b | | CNYTokenPlus | 0xfbb7b2295ab9f987a9f7bd5ba6c9de8ee762deb8 | With the touted “code-is-law” principle in Ethereum blockchain, there is no traditional well-known security response mechanism in place to remedy these vulnerable contracts! A proper way to recover from these vulnerabilities and devastating effects requires coordination and support from all eco-system members, especially digital asset exchanges. In the meantime, we cannot over-emphasize the importance of performing a thorough and comprehensive audit of smart contracts before deployment. Fortunately, we’re happy to know that effectively at 04/25/2018 15:30 p.m. GMT+8, OKEx has ERC-20 tokens deposit suspended. (Here is the announcement: https://support.okex.com/hc/en-us/articles/360003019292 ). Similarly, Huobi Pro also suspends deposits and withdrawals of all coins ( http://space.bitleek.com/topic/2132/huobi-pro-suspends-deposits-and-withdrawals-of-all-coins). Meanwhile, we want to point out that certain affected tokens are still tradable on some exchanges (e.g., gate.io, HitBTC, YoBit, and CoinExchange). Note that the presence of non-centralized exchanges with offline trading services could pose additional challenges as they might not be able to stop attackers from laundering their tokens. |
| id | SSV:97247 |
| last seen | 2018-06-08 |
| modified | 2018-04-26 |
| published | 2018-04-26 |
| reporter | Knownsec |
| title | New proxyOverflow Bug in Multiple ERC20 Smart Contracts (CVE-2018-10376) |