Vulnerabilities > CVE-2017-7269 - Improper Restriction of Operations within the Bounds of a Memory Buffer vulnerability in Microsoft Internet Information Server 6.0
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
HIGH Integrity impact
HIGH Availability impact
HIGH Summary
Buffer overflow in the ScStoragePathFromUrl function in the WebDAV service in Internet Information Services (IIS) 6.0 in Microsoft Windows Server 2003 R2 allows remote attackers to execute arbitrary code via a long header beginning with "If: <http://" in a PROPFIND request, as exploited in the wild in July or August 2016.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| Application | 1 | |
| OS | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Overflow Buffers Buffer Overflow attacks target improper or missing bounds checking on buffer operations, typically triggered by input injected by an attacker. As a consequence, an attacker is able to write past the boundaries of allocated buffer regions in memory, causing a program crash or potentially redirection of execution as per the attackers' choice.
- Client-side Injection-induced Buffer Overflow This type of attack exploits a buffer overflow vulnerability in targeted client software through injection of malicious content from a custom-built hostile service.
- Filter Failure through Buffer Overflow In this attack, the idea is to cause an active filter to fail by causing an oversized transaction. An attacker may try to feed overly long input strings to the program in an attempt to overwhelm the filter (by causing a buffer overflow) and hoping that the filter does not fail securely (i.e. the user input is let into the system unfiltered).
- MIME Conversion An attacker exploits a weakness in the MIME conversion routine to cause a buffer overflow and gain control over the mail server machine. The MIME system is designed to allow various different information formats to be interpreted and sent via e-mail. Attack points exist when data are converted to MIME compatible format and back.
Exploit-Db
description Microsoft IIS WebDav - ScStoragePathFromUrl Overflow (Metasploit). CVE-2017-7269. Remote exploit for Windows platform. Tags: Metasploit Framework file exploits/windows/remote/41992.rb id EDB-ID:41992 last seen 2017-05-11 modified 2017-05-11 platform windows port published 2017-05-11 reporter Exploit-DB source https://www.exploit-db.com/download/41992/ title Microsoft IIS WebDav - ScStoragePathFromUrl Overflow (Metasploit) type remote description Internet Information Services (IIS) 6.0 WebDAV - 'ScStoragePathFromUrl' Buffer Overflow. CVE-2017-7269. Remote exploit for Windows platform file exploits/windows/remote/41738.py id EDB-ID:41738 last seen 2017-03-27 modified 2017-03-27 platform windows port published 2017-03-27 reporter Exploit-DB source https://www.exploit-db.com/download/41738/ title Internet Information Services (IIS) 6.0 WebDAV - 'ScStoragePathFromUrl' Buffer Overflow type remote
Metasploit
| description | Buffer overflow in the ScStoragePathFromUrl function in the WebDAV service in Internet Information Services (IIS) 6.0 in Microsoft Windows Server 2003 R2 allows remote attackers to execute arbitrary code via a long header beginning with "If: Author(s) Zhiniang Peng Chen Wu Dominic Chell firefart zcgonvh Rich Whitcroft Lincoln Platform Windows |
| id | MSF:EXPLOIT/WINDOWS/IIS/IIS_WEBDAV_SCSTORAGEPATHFROMURL |
| last seen | 2020-06-08 |
| modified | 2020-03-12 |
| published | 2017-03-28 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/exploits/windows/iis/iis_webdav_scstoragepathfromurl.rb |
| title | Microsoft IIS WebDav ScStoragePathFromUrl Overflow |
Nessus
NASL family Web Servers NASL id IIS6_WEBDAV_CVE-2017-7269.NASL description The remote host is running Windows Server 2003 R2 and Internet Information Services (IIS) 6.0 with WebDAV enabled. It is, therefore, affected by a buffer overflow condition in the IIS WebDAV service due to improper handling of the last seen 2020-06-01 modified 2020-06-02 plugin id 99281 published 2017-04-11 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/99281 title Microsoft Windows Server 2003 R2 IIS 6.0 WebDAV PROPFIND Request Handling RCE (EXPLODINGCAN) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if(description) { script_id(99281); script_version ("1.10"); script_cvs_date("Date: 2019/04/30 14:30:16"); script_cve_id("CVE-2017-7269"); script_bugtraq_id(97127); script_xref(name:"EDB-ID", value:"41738"); script_name(english:"Microsoft Windows Server 2003 R2 IIS 6.0 WebDAV PROPFIND Request Handling RCE (EXPLODINGCAN)"); script_summary(english: "Checks for a vulnerable configuration of IIS."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host is affected by a remote code execution vulnerability."); script_set_attribute(attribute:"description", value: "The remote host is running Windows Server 2003 R2 and Internet Information Services (IIS) 6.0 with WebDAV enabled. It is, therefore, affected by a buffer overflow condition in the IIS WebDAV service due to improper handling of the 'If' header in a PROPFIND request. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition or the execution of arbitrary code. EXPLODINGCAN is one of multiple Equation Group vulnerabilities and exploits disclosed on 2017/04/14 by a group known as the Shadow Brokers."); # https://threatpost.com/publicly-attacked-microsoft-iis-zero-day-unlikely-to-be-patched/124641/ script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?c9ce665b"); # https://www.theregister.co.uk/2017/03/31/microsoft_wont_patch_server_2003/ script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?ca2c1085"); script_set_attribute(attribute:"see_also", value: "https://github.com/edwardz246003/IIS_exploit/blob/master/exploit.py"); # https://blog.0patch.com/2017/03/0patching-immortal-cve-2017-7269.html script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?91b46151"); script_set_attribute(attribute:"solution", value: "Windows Server 2003 R2 and IIS 6.0 are no longer maintained or supported by Microsoft. Upgrade to a currently supported version of Microsoft Windows and IIS. Alternatively, disable either IIS or WebDAV."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Microsoft IIS WebDav ScStoragePathFromUrl Overflow'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"vuln_publication_date", value:"2017/03/26"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/04/11"); script_set_attribute(attribute:"potential_vulnerability", value:"true"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/o:microsoft:windows"); script_set_attribute(attribute:"cpe", value:"cpe:/a:microsoft:iis"); script_set_attribute(attribute:"in_the_news", value:"true"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_family(english:"Web Servers"); script_dependencies("os_fingerprint.nasl", "webdav_enabled.nasl"); script_require_keys("www/iis", "Settings/ParanoidReport"); script_require_ports("Services/www", 80); exit(0); } include("audit.inc"); include("global_settings.inc"); include("http.inc"); include("misc_func.inc"); get_kb_item_or_exit("www/iis"); port = get_http_port(default:80); if (report_paranoia < 2) audit(AUDIT_PARANOID); app = "Microsoft IIS"; banner = get_http_banner(port:port); if (banner !~ "Server: Microsoft-IIS") audit(AUDIT_NOT_DETECT, app, port); else banner = strstr(banner, "Server:"); # slice banner # ensure WebDAV is running get_kb_item_or_exit("www/"+port+"/webdav"); # get IIS version pat = "^Server: Microsoft-IIS\/([\d]+(?:\.[\d]+)+)"; version = pregmatch(string:banner, pattern:pat); if (isnull(version)) audit(AUDIT_UNKNOWN_APP_VER, app); else version = version[1]; if (version != '6.0') audit(AUDIT_INST_VER_NOT_VULN, app, version); # ensure OS is Windows Server 2003 R2 os = get_kb_item("Host/OS"); if (isnull(os) || "Server 2003 R2" >!< os) os = get_kb_item("SMB/NativeLanManager"); if (isnull(os)) audit(AUDIT_OS_NOT, "known"); if ("Server 2003 R2" >!< os) audit(AUDIT_OS_NOT, "Windows Server 2003 R2"); report = 'IIS 6.0 is installed with WebDAV enabled on Windows Server 2003 R2.'; security_report_v4(port:port, extra:report, severity:SECURITY_HOLE);NASL family Windows : Microsoft Bulletins NASL id SMB_NT_MS17_JUNE_XP_2003.NASL description The remote Windows host is missing a security update. It is, therefore, affected by one or more of the following vulnerabilities : - A remote code execution vulnerability exists in how the Remote Desktop Protocol (RDP) handles requests if the RDP server has Smart Card authentication enabled. An authenticated, remote attacker can exploit this, via a specially crafted application, to execute arbitrary code with full user privileges. (CVE-2017-0176) - A remote code execution vulnerability exists in Microsoft Internet Explorer due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a specially crafted website, to execute arbitrary code in the context of the current user. (CVE-2017-0222) - An information disclosure vulnerability exists in the Microsoft Server Message Block 1.0 (SMBv1) server when handling certain requests. An unauthenticated, remote attacker can exploit this, via a specially crafted packet, to disclose sensitive information. (CVE-2017-0267) - A buffer overflow condition exists in the IIS WebDAV service due to improper handling of the last seen 2020-06-01 modified 2020-06-02 plugin id 100791 published 2017-06-14 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/100791 title Microsoft Security Advisory 4025685: Guidance for older platforms (XP / 2003) (EXPLODINGCAN) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if (description) { script_id(100791); script_version("1.9"); script_cvs_date("Date: 2019/04/30 14:30:16"); script_cve_id( "CVE-2017-0176", "CVE-2017-0222", "CVE-2017-0267", "CVE-2017-7269", "CVE-2017-8461", "CVE-2017-8487", "CVE-2017-8543", "CVE-2017-8552" ); script_bugtraq_id( 97127, 98127, 98259, 98752, 98824, 99012, 99013, 99035 ); script_xref(name:"MSKB", value:"3197835"); script_xref(name:"MSFT", value:"MS17-3197835"); script_xref(name:"MSKB", value:"4018271"); script_xref(name:"MSFT", value:"MS17-4018271"); script_xref(name:"MSKB", value:"4018466"); script_xref(name:"MSFT", value:"MS17-4018466"); script_xref(name:"MSKB", value:"4019204"); script_xref(name:"MSFT", value:"MS17-4019204"); script_xref(name:"MSKB", value:"4022747"); script_xref(name:"MSFT", value:"MS17-4022747"); script_xref(name:"MSKB", value:"4024323"); script_xref(name:"MSFT", value:"MS17-4024323"); script_xref(name:"MSKB", value:"4024402"); script_xref(name:"MSFT", value:"MS17-4024402"); script_xref(name:"MSKB", value:"4025218"); script_xref(name:"MSFT", value:"MS17-4025218"); script_xref(name:"EDB-ID", value:"41738"); script_xref(name:"EDB-ID", value:"41992"); script_name(english:"Microsoft Security Advisory 4025685: Guidance for older platforms (XP / 2003) (EXPLODINGCAN)"); script_summary(english:"Checks the versions of system files."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host is affected by multiple vulnerabilities."); script_set_attribute(attribute:"description", value: "The remote Windows host is missing a security update. It is, therefore, affected by one or more of the following vulnerabilities : - A remote code execution vulnerability exists in how the Remote Desktop Protocol (RDP) handles requests if the RDP server has Smart Card authentication enabled. An authenticated, remote attacker can exploit this, via a specially crafted application, to execute arbitrary code with full user privileges. (CVE-2017-0176) - A remote code execution vulnerability exists in Microsoft Internet Explorer due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a specially crafted website, to execute arbitrary code in the context of the current user. (CVE-2017-0222) - An information disclosure vulnerability exists in the Microsoft Server Message Block 1.0 (SMBv1) server when handling certain requests. An unauthenticated, remote attacker can exploit this, via a specially crafted packet, to disclose sensitive information. (CVE-2017-0267) - A buffer overflow condition exists in the IIS WebDAV service due to improper handling of the 'If' header in a PROPFIND request. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition or the execution of arbitrary code. This vulnerability, also known as EXPLODINGCAN, is one of multiple Equation Group vulnerabilities and exploits disclosed on 2017/04/14 by a group known as the Shadow Brokers. (CVE-2017-7269) - A remote code execution vulnerability exists in how the Remote Desktop Protocol (RDP) handles requests if the RDP server has Routing and Remote Access enabled. An authenticated, remote attacker can exploit this, via a specially crafted application, to execute arbitrary code with full user privileges. (CVE-2017-8461) - A remote code execution vulnerability exists in Windows OLE, specifically in olecnv32.dll, due to improper validation of user-supplied input. An unauthenticated, remote attacker can exploit this, by convincing a user to visit a specially crafted website or to open a specially crafted file or email, to execute arbitrary code in the context of the current user. (CVE-2017-8487) - A remote code execution vulnerability exists in the Windows Search functionality due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit this, via a specially crafted SMB message, to execute arbitrary code. (CVE-2017-8543) - An information disclosure vulnerability exists in the GDI component due to improper handling of objects in memory. An unauthenticated, remote attacker can exploit this, by convincing a user to open a specially crafted document or visit a specially crafted website, to disclose the contents of memory. (CVE-2017-8552)"); # https://support.microsoft.com/en-us/help/4025687/microsoft-security-advisory-4025685-guidance-for-older-platforms script_set_attribute(attribute:"see_also", value:"http://www.nessus.org/u?a0780816"); script_set_attribute(attribute:"solution", value: "Microsoft has released a set of patches for Windows XP and 2003."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Microsoft IIS WebDav ScStoragePathFromUrl Overflow'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"vuln_publication_date", value:"2017/03/26"); script_set_attribute(attribute:"patch_publication_date", value:"2017/06/13"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/06/14"); script_set_attribute(attribute:"plugin_type", value:"local"); script_set_attribute(attribute:"cpe", value:"cpe:/o:microsoft:windows"); script_set_attribute(attribute:"cpe", value:"cpe:/a:microsoft:iis"); script_set_attribute(attribute:"in_the_news", value:"true"); script_end_attributes(); script_category(ACT_GATHER_INFO); script_family(english:"Windows : Microsoft Bulletins"); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("smb_hotfixes.nasl", "ms_bulletin_checks_possible.nasl"); script_require_keys("SMB/MS_Bulletin_Checks/Possible"); script_require_ports(139, 445, "Host/patch_management_checks"); exit(0); } include("audit.inc"); include("smb_hotfixes_fcheck.inc"); include("smb_hotfixes.inc"); include("smb_func.inc"); include("smb_reg_query.inc"); include("misc_func.inc"); include("global_settings.inc"); include("install_func.inc"); include("misc_func.inc"); get_kb_item_or_exit("SMB/MS_Bulletin_Checks/Possible"); kbs = make_list( '3197835', '4018271', '4018466', '4019204', '4022747', '4024323', '4024402', '4025218' ); bulletin = 'MS17-06'; if (get_kb_item("Host/patch_management_checks")) hotfix_check_3rd_party(bulletin:bulletin, kbs:kbs, severity:SECURITY_HOLE); get_kb_item_or_exit("SMB/Registry/Enumerated"); get_kb_item_or_exit("SMB/WindowsVersion", exit_code:1); if (hotfix_check_sp_range(xp:'2,3', win2003:'2') <= 0) audit(AUDIT_OS_SP_NOT_VULN); productname = get_kb_item_or_exit("SMB/ProductName", exit_code:1); share = hotfix_get_systemdrive(as_share:TRUE, exit_on_fail:TRUE); if (!is_accessible_share(share:share)) audit(AUDIT_SHARE_FAIL, share); vuln = FALSE; if ('XP' >< productname) { if ( # Windows XP SP3 (x86) hotfix_is_vulnerable(os:"5.1", sp:3, file:"win32k.sys", version:"5.1.2600.7258", min_version:"5.1.2600.5000", dir:"\system32", bulletin:bulletin, kb:"4019204", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"query.dll", version:"5.1.2600.7273", min_version:"5.1.2600.5000", dir:"\system32", bulletin:bulletin, kb:"4024402", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"olecnv32.dll", version:"5.1.2600.7285", min_version:"5.1.2600.5000", dir:"\system32", bulletin:bulletin, kb:"4025218", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"rasmxs.dll", version:"5.1.2600.7272", min_version:"5.1.2600.5000", dir:"\system32", bulletin:bulletin, kb:"4024323", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"httpext.dll", version:"6.0.2600.7150", min_version:"6.0.0.0", dir:"\system32\inetsrv", bulletin:bulletin, kb:"3197835", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"srv.sys", version:"5.1.2600.7238", min_version:"5.1.2600.5000", dir:"\system32\drivers", bulletin:bulletin, kb:"4018466", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"mshtml.dll", version:"8.0.6001.23942", min_version:"8.0.0.0", dir:"\system32", bulletin:bulletin, kb:"4018271", arch:"x86") || hotfix_is_vulnerable(os:"5.1", sp:3, file:"gpkcsp.dll", version:"5.1.2600.7264", min_version:"5.1.2600.5000", dir:"\system32", bulletin:bulletin, kb:"4022747", arch:"x86") || # Windows XP SP2 (x64) hotfix_is_vulnerable(os:"5.2", sp:2, file:"win32k.sys", version:"5.2.3790.6080", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4019204", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"query.dll", version:"5.2.3790.6100", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4024402", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"olecnv32.dll", version:"5.2.3790.6113", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4025218", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"rasmxs.dll", version:"5.2.3790.6099", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4024323", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"httpext.dll", version:"6.0.3790.5955", min_version:"6.0.0.0", dir:"\system32\inetsrv", bulletin:bulletin, kb:"3197835", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"srv.sys", version:"5.2.3790.6051", min_version:"5.2.3790.3000", dir:"\system32\drivers", bulletin:bulletin, kb:"4018466", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"mshtml.dll", version:"8.0.6001.23942", min_version:"8.0.0.0", dir:"\system32", bulletin:bulletin, kb:"4018271", arch:"x64") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"gpkcsp.dll", version:"5.2.3790.6093", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4022747", arch:"x64") ) vuln = TRUE; } else if ('2003' >< productname) { if ( hotfix_is_vulnerable(os:"5.2", sp:2, file:"win32k.sys", version:"5.2.3790.6080", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4019204") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"query.dll", version:"5.2.3790.6100", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4024402") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"olecnv32.dll", version:"5.2.3790.6113", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4025218") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"rasmxs.dll", version:"5.2.3790.6099", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4024323") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"httpext.dll", version:"6.0.3790.5955", min_version:"6.0.0.0", dir:"\system32\inetsrv", bulletin:bulletin, kb:"3197835") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"srv.sys", version:"5.2.3790.6051", min_version:"5.2.3790.3000", dir:"\system32\drivers", bulletin:bulletin, kb:"4018466") || hotfix_is_vulnerable(os:"5.2", sp:2, file:"gpkcsp.dll", version:"5.2.3790.6093", min_version:"5.2.3790.3000", dir:"\system32", bulletin:bulletin, kb:"4022747") ) vuln = TRUE; } if (vuln) { set_kb_item(name:'SMB/Missing/'+bulletin, value:TRUE); hotfix_security_hole(); hotfix_check_fversion_end(); exit(0); } else { hotfix_check_fversion_end(); audit(AUDIT_HOST_NOT, hotfix_get_audit_report()); }NASL family Web Servers NASL id IIS6_WEBDAV_CVE-2017-7269_DIRECT.NASL description The remote host is running Windows Server 2003 and Internet Information Services (IIS) 6.0 with WebDAV enabled. It is, therefore, affected by a buffer overflow condition in the IIS WebDAV service due to improper handling of the last seen 2020-06-01 modified 2020-06-02 plugin id 99523 published 2017-04-20 reporter This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. source https://www.tenable.com/plugins/nessus/99523 title Microsoft Windows Server 2003 IIS 6.0 WebDAV PROPFIND Request Handling RCE (EXPLODINGCAN) code # # (C) Tenable Network Security, Inc. # include("compat.inc"); if(description) { script_id(99523); script_version ("1.9"); script_cvs_date("Date: 2019/04/30 14:30:16"); script_cve_id("CVE-2017-7269"); script_bugtraq_id(97127); script_xref(name:"EDB-ID", value:"41738"); script_name(english:"Microsoft Windows Server 2003 IIS 6.0 WebDAV PROPFIND Request Handling RCE (EXPLODINGCAN)"); script_summary(english: "Checks response from IIS 6.0."); script_set_attribute(attribute:"synopsis", value: "The remote Windows host is affected by a remote code execution vulnerability."); script_set_attribute(attribute:"description", value: "The remote host is running Windows Server 2003 and Internet Information Services (IIS) 6.0 with WebDAV enabled. It is, therefore, affected by a buffer overflow condition in the IIS WebDAV service due to improper handling of the 'If' header in a PROPFIND request. An unauthenticated, remote attacker can exploit this, via a specially crafted request, to cause a denial of service condition or the execution of arbitrary code. EXPLODINGCAN is one of multiple Equation Group vulnerabilities and exploits disclosed on 2017/04/14 by a group known as the Shadow Brokers."); # https://threatpost.com/publicly-attacked-microsoft-iis-zero-day-unlikely-to-be-patched/124641/ script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?c9ce665b"); # https://www.theregister.co.uk/2017/03/31/microsoft_wont_patch_server_2003/ script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?ca2c1085"); script_set_attribute(attribute:"see_also", value: "https://github.com/edwardz246003/IIS_exploit/blob/master/exploit.py"); # https://blog.0patch.com/2017/03/0patching-immortal-cve-2017-7269.html script_set_attribute(attribute:"see_also", value: "http://www.nessus.org/u?91b46151"); script_set_attribute(attribute:"solution", value: "Windows Server 2003 and IIS 6.0 are no longer maintained or supported by Microsoft. Upgrade to a currently supported version of Microsoft Windows and IIS. Alternatively, disable either IIS or WebDAV."); script_set_cvss_base_vector("CVSS2#AV:N/AC:L/Au:N/C:C/I:C/A:C"); script_set_cvss_temporal_vector("CVSS2#E:H/RL:OF/RC:C"); script_set_cvss3_base_vector("CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H"); script_set_cvss3_temporal_vector("CVSS:3.0/E:H/RL:O/RC:C"); script_set_attribute(attribute:"exploitability_ease", value:"Exploits are available"); script_set_attribute(attribute:"exploit_available", value:"true"); script_set_attribute(attribute:"exploit_framework_core", value:"true"); script_set_attribute(attribute:"exploited_by_malware", value:"true"); script_set_attribute(attribute:"metasploit_name", value:'Microsoft IIS WebDav ScStoragePathFromUrl Overflow'); script_set_attribute(attribute:"exploit_framework_metasploit", value:"true"); script_set_attribute(attribute:"exploit_framework_canvas", value:"true"); script_set_attribute(attribute:"canvas_package", value:'CANVAS'); script_set_attribute(attribute:"vuln_publication_date", value:"2017/03/26"); script_set_attribute(attribute:"plugin_publication_date", value:"2017/04/20"); script_set_attribute(attribute:"plugin_type", value:"remote"); script_set_attribute(attribute:"cpe", value:"cpe:/o:microsoft:windows"); script_set_attribute(attribute:"cpe", value:"cpe:/a:microsoft:iis"); script_set_attribute(attribute:"in_the_news", value:"true"); script_end_attributes(); script_category(ACT_ATTACK); script_family(english:"Web Servers"); script_copyright(english:"This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof."); script_dependencies("os_fingerprint.nasl", "webdav_enabled.nasl"); script_require_keys("www/iis"); script_require_ports("Services/www", 80); exit(0); } include("audit.inc"); include("global_settings.inc"); include("http.inc"); include("misc_func.inc"); get_kb_item_or_exit("www/iis"); port = get_http_port(default:80); app = "Microsoft IIS"; banner = get_http_banner(port:port); if (banner !~ "Server: Microsoft-IIS") audit(AUDIT_NOT_DETECT, app, port); else banner = strstr(banner, "Server:"); # slice banner # ensure WebDAV is running get_kb_item_or_exit("www/"+port+"/webdav"); # get IIS version pat = "^Server: Microsoft-IIS\/([\d]+(?:\.[\d]+)+)"; version = pregmatch(string:banner, pattern:pat); if (isnull(version)) audit(AUDIT_UNKNOWN_APP_VER, app); else version = version[1]; if (version != '6.0') audit(AUDIT_INST_VER_NOT_VULN, app, version); # ensure OS is Windows Server 2003, including R2 os = get_kb_item("Host/OS"); if (isnull(os) || "Server 2003" >!< os) os = get_kb_item("SMB/NativeLanManager"); if (isnull(os)) audit(AUDIT_OS_NOT, "known"); if ("Server 2003" >!< os) audit(AUDIT_OS_NOT, "Windows Server 2003"); pay='<http://localhost/' + crap(data:'A', length:0x82) + '>'; pay+=' (Not <locktoken:write1>) '; hdrs = make_array("If", pay, "Host", "localhost", "Content-Length", 0); res = http_send_recv3( method : "PROPFIND", item : "/", port : port, add_headers : hdrs, exit_on_fail : TRUE ); if (res[0] =~ "^HTTP/[0-9]\.[0-9] 500") { if ("Internal Server Error(exception)" >< res[2]) { report = 'Nessus was to able to detect the issue with the following request: \n\n' + http_last_sent_request(); security_report_v4(port:port, extra:report, severity:SECURITY_HOLE); } else { audit(AUDIT_RESP_BAD, port, "a PROPFIND request. Unexpected HTTP 500 response body"); } } else if (res[0] =~ "^HTTP/[0-9]\.[0-9] 207") { audit(AUDIT_INST_VER_NOT_VULN, app, version); } else { audit(AUDIT_RESP_BAD, port, "a PROPFIND request. Unexpected response status: " + chomp(res[0])); }
Packetstorm
data source https://packetstormsecurity.com/files/download/142060/iis-buffer-overflow.nse id PACKETSTORM:142060 last seen 2017-04-11 published 2017-04-08 reporter Rewanth Cool source https://packetstormsecurity.com/files/142060/MS-IIS-6.0-Buffer-Overflow-NSE-Script.html title MS IIS 6.0 Buffer Overflow NSE Script data source https://packetstormsecurity.com/files/download/141997/msiis6-overflow.txt id PACKETSTORM:141997 last seen 2017-04-10 published 2017-03-27 reporter Zhiniang Peng source https://packetstormsecurity.com/files/141997/Microsoft-IIS-6.0-WebDAV-ScStoragePathFromUrl-Buffer-Overflow.html title Microsoft IIS 6.0 WebDAV ScStoragePathFromUrl Buffer Overflow data source https://packetstormsecurity.com/files/download/142471/iis_webdav_scstoragepathfromurl.rb.txt id PACKETSTORM:142471 last seen 2017-05-11 published 2017-05-11 reporter Dominic Chell source https://packetstormsecurity.com/files/142471/-Microsoft-IIS-WebDav-ScStoragePathFromUrl-Overflow.html title Microsoft IIS WebDav ScStoragePathFromUrl Overflow
Seebug
| bulletinFamily | exploit |
| description | In Windows Server 2003 IIS6. 0 the WebDAV service ScStoragePathFromUrl a function of the presence buffer overflow vulnerability, an attacker by a order“If: <http://” at the beginning of a longer `header `head `PROPFIND `request arbitrary code execution. Currently the vulnerability for install IIS6 Windows Server 2003 R2 system can be stabilized using the vulnerability as early as 2016, 7,8 month would have started on the outside is the use. Use the following PoC test in the target server back-end perform `calc.exe`, testing the PoC in the IIS default site to open the `WebDAV `extension be reproducible. As follows: 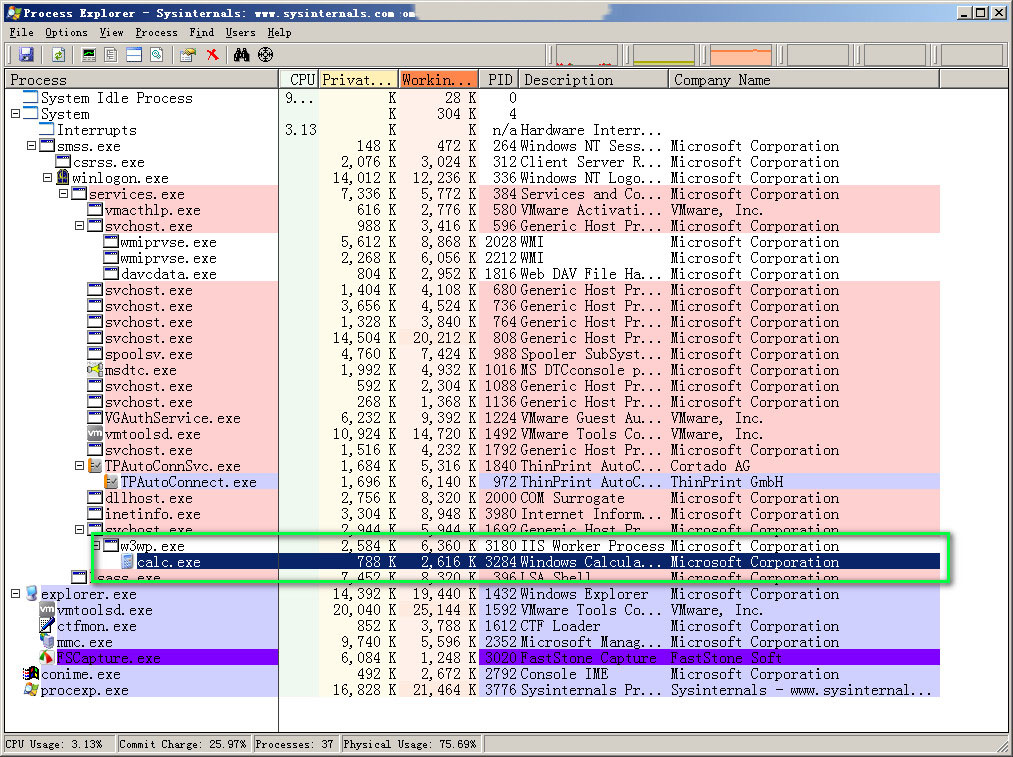 |
| id | SSV:92834 |
| last seen | 2017-11-19 |
| modified | 2017-03-28 |
| published | 2017-03-28 |
| reporter | Root |
| title | IIS 6.0 WebDAV remote code execution vulnerability (CVE-2017-7269) |
The Hacker News
| id | THN:129FB15A6EC81B3F21210807A7547381 |
| last seen | 2018-01-27 |
| modified | 2017-09-28 |
| published | 2017-09-28 |
| reporter | Swati Khandelwal |
| source | https://thehackernews.com/2017/09/windows-monero-miners.html |
| title | Hackers Exploiting Microsoft Servers to Mine Monero - Makes $63,000 In 3 Months |
Related news
References
- https://github.com/edwardz246003/IIS_exploit
- http://www.securityfocus.com/bid/97127
- https://github.com/rapid7/metasploit-framework/pull/8162
- https://0patch.blogspot.com/2017/03/0patching-immortal-cve-2017-7269.html
- https://support.microsoft.com/en-us/help/3197835/description-of-the-security-update-for-windows-xp-and-windows-server
- http://www.securitytracker.com/id/1038168
- https://www.exploit-db.com/exploits/41992/
- https://www.exploit-db.com/exploits/41738/
- https://github.com/danigargu/explodingcan
- https://medium.com/%40iraklis/number-of-internet-facing-vulnerable-iis-6-0-to-cve-2017-7269-8bd153ef5812