Attack vector
NETWORK Attack complexity
MEDIUM Privileges required
NONE Confidentiality impact
PARTIAL Integrity impact
NONE Availability impact
NONE Published: 2017-01-17
Updated: 2017-09-01
Summary
An issue was discovered on NETGEAR R8500, R8300, R7000, R6400, R7300, R7100LG, R6300v2, WNDR3400v3, WNR3500Lv2, R6250, R6700, R6900, and R8000 devices. They are prone to password disclosure via simple crafted requests to the web management server. The bug is exploitable remotely if the remote management option is set, and can also be exploited given access to the router over LAN or WLAN. When trying to access the web panel, a user is asked to authenticate; if the authentication is canceled and password recovery is not enabled, the user is redirected to a page that exposes a password recovery token. If a user supplies the correct token to the page /passwordrecovered.cgi?id=TOKEN (and password recovery is not enabled), they will receive the admin password for the router. If password recovery is set the exploit will fail, as it will ask the user for the recovery questions that were previously set when enabling that feature. This is persistent (even after disabling the recovery option, the exploit will fail) because the router will ask for the security questions.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Subverting Environment Variable Values
The attacker directly or indirectly modifies environment variables used by or controlling the target software. The attacker's goal is to cause the target software to deviate from its expected operation in a manner that benefits the attacker.
- Footprinting
An attacker engages in probing and exploration activity to identify constituents and properties of the target. Footprinting is a general term to describe a variety of information gathering techniques, often used by attackers in preparation for some attack. It consists of using tools to learn as much as possible about the composition, configuration, and security mechanisms of the targeted application, system or network. Information that might be collected during a footprinting effort could include open ports, applications and their versions, network topology, and similar information. While footprinting is not intended to be damaging (although certain activities, such as network scans, can sometimes cause disruptions to vulnerable applications inadvertently) it may often pave the way for more damaging attacks.
- Exploiting Trust in Client (aka Make the Client Invisible)
An attack of this type exploits a programs' vulnerabilities in client/server communication channel authentication and data integrity. It leverages the implicit trust a server places in the client, or more importantly, that which the server believes is the client. An attacker executes this type of attack by placing themselves in the communication channel between client and server such that communication directly to the server is possible where the server believes it is communicating only with a valid client. There are numerous variations of this type of attack.
- Browser Fingerprinting
An attacker carefully crafts small snippets of Java Script to efficiently detect the type of browser the potential victim is using. Many web-based attacks need prior knowledge of the web browser including the version of browser to ensure successful exploitation of a vulnerability. Having this knowledge allows an attacker to target the victim with attacks that specifically exploit known or zero day weaknesses in the type and version of the browser used by the victim. Automating this process via Java Script as a part of the same delivery system used to exploit the browser is considered more efficient as the attacker can supply a browser fingerprinting method and integrate it with exploit code, all contained in Java Script and in response to the same web page request by the browser.
- Session Credential Falsification through Prediction
This attack targets predictable session ID in order to gain privileges. The attacker can predict the session ID used during a transaction to perform spoofing and session hijacking.
Exploit-Db
| description | Multiple Netgear Routers - Password Disclosure. CVE-2017-5521. Webapps exploit for Hardware platform |
| file | exploits/hardware/webapps/41205.py |
| id | EDB-ID:41205 |
| last seen | 2017-01-31 |
| modified | 2017-01-30 |
| platform | hardware |
| port | |
| published | 2017-01-30 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/41205/ |
| title | Multiple Netgear Routers - Password Disclosure |
| type | webapps |
Metasploit
| description | This module will collect the password for the `admin` user. The exploit will not complete if password recovery is set on the router. The password is received by passing the token generated from `unauth.cgi` to `passwordrecovered.cgi`. This exploit works on many different NETGEAR products. The full list of affected products is available in the 'References' section. |
| id | MSF:AUXILIARY/GATHER/NETGEAR_PASSWORD_DISCLOSURE |
| last seen | 2019-12-17 |
| modified | 2017-07-24 |
| published | 2017-02-05 |
| references | |
| reporter | Rapid7 |
| source | https://github.com/rapid7/metasploit-framework/blob/master//modules/auxiliary/gather/netgear_password_disclosure.rb |
| title | NETGEAR Administrator Password Disclosure |
Seebug
| bulletinFamily | exploit |
| description | ### 0x01 vulnerability overview NETGEAR is a United States well-known router manufacturers, its products are used worldwide extensively. Recently, foreign security researcher Simon Kenin find NETGEAR router more series there is a password leak Vulnerability, CVE-2017-5521-in. When the router Password Recovery functionality is disabled to enable remote management when the vulnerability can be triggered. ### 0x02 vulnerability Affected Router the presence of leaked password of the risk ### 0x03 impact version Currently the vulnerability of the Publisher to verify the affected version: * AC1450 V1. 0. 0. 34_10. 0. 16 (Latest) * AC1450 V1. 0. 0. 22_1. 0. 10 * AC1450 V1. 0. 0. 14_1. 0. 6 * D6400 V1. 0. 0. 44_1. 0. 44 (V1. 0. 0. 52_1. 0. 52 and above not affected) * D6400 V1. 0. 0. 34_1. 3. 34 * D6400 V1. 0. 0. 38_1. 1. 38 * D6400 V1. 0. 0. 22_1. 0. 22 * DC112A V1. 0. 0. 30_1. 0. 60 (Latest) * DGN2200v4 V1. 0. 0. 24_5. 0. 8 (V1. 0. 0. 66_1. 0. 66 is latest and is not affected) * JNDR3000 V1. 0. 0. 18_1. 0. 16 (Latest) * R6200 V1. 0. 1. 48_1. 0. 37 (V1. 0. 1. 52_1. 0. 41 and above are not affected) * R6200v2 V1. 0. 1. 20_1. 0. 18 (V1. 0. 3. 10_10. 1. 10 is latest and is not affected) * R6250 V1. 0. 1. 84_1. 0. 78 (V1. 0. 4. 2_10. 1. 10 is latest and is not affected) * R6300 V1. 0. 2. 78_1. 0. 58 (Latest) * R6300v2 V1. 0. 4. 2_10. 0. 74 (V1. 0. 4. 6_10. 0. 76 is latest and is patched) * R6300v2 V1. 0. 3. 30_10. 0. 73 * R6700 V1. 0. 1. 14_10. 0. 29 (Latest beta) * R6700 V1. 0. 0. 26_10. 0. 26 (Latest stable) * R6700 V1. 0. 0. 24_10. 0. 18 * R6900 V1. 0. 0. 4_1. 0. 10 (Latest) * R7000 V1. 0. 6. 28_1. 1. 83 (V1. 0. 7. 2_1. 1. 93 is latest and is patched) * R8300 V1. 0. 2. 48_1. 0. 52 * R8500 V1. 0. 2. 30_1. 0. 43 (V1. 0. 2. 64_1. 0. 62 and above is patched) * R8500 V1. 0. 2. 26_1. 0. 41 * R8500 V1. 0. 0. 56_1. 0. 28 * R8500 V1. 0. 0. 20_1. 0. 11 * VEGN2610 V1. 0. 0. 35_1. 0. 35 (Latest) * VEGN2610 V1. 0. 0. 29_1. 0. 29 * VEGN2610 V1. 0. 0. 27_1. 0. 27 * WNDR3400v2 V1. 0. 0. 16_1. 0. 34 (V1. 0. 0. 52_1. 0. 81 is latest and is not affected) * WNDR3400v3 V1. 0. 0. 22_1. 0. 29 (V1. 0. 1. 2_1. 0. 51 is latest and is not affected) * WNDR3700v3 V1. 0. 0. 38_1. 0. 31 (Latest) * WNDR4000 V1. 0. 2. 4_9. 1. 86 (Latest) * WNDR4500 V1. 0. 1. 40_1. 0. 68 (Latest) * WNDR4500v2 V1. 0. 0. 60_1. 0. 38 (Latest) * WNDR4500v2 V1. 0. 0. 42_1. 0. 25 * WGR614v10 V1. 0. 2. 60_60. 0. 85 NA (Latest) * WGR614v10 V1. 0. 2. 58_60. 0. 84 NA * WGR614v10 V1. 0. 2. 54_60. 0. 82 NA * WN3100RP V1. 0. 0. 14_1. 0. 19 (Latest) * WN3100RP V1. 0. 0. 6_1. 0. 12 * Lenovo R3220 V1. 0. 0. 16_1. 0. 16 (Latest) * Lenovo R3220 V1. 0. 0. 13_1. 0. 13 ### 0x04 vulnerability verification Access vulnerability the router the following url: `ip:port/passwordrecovered. cgi?` 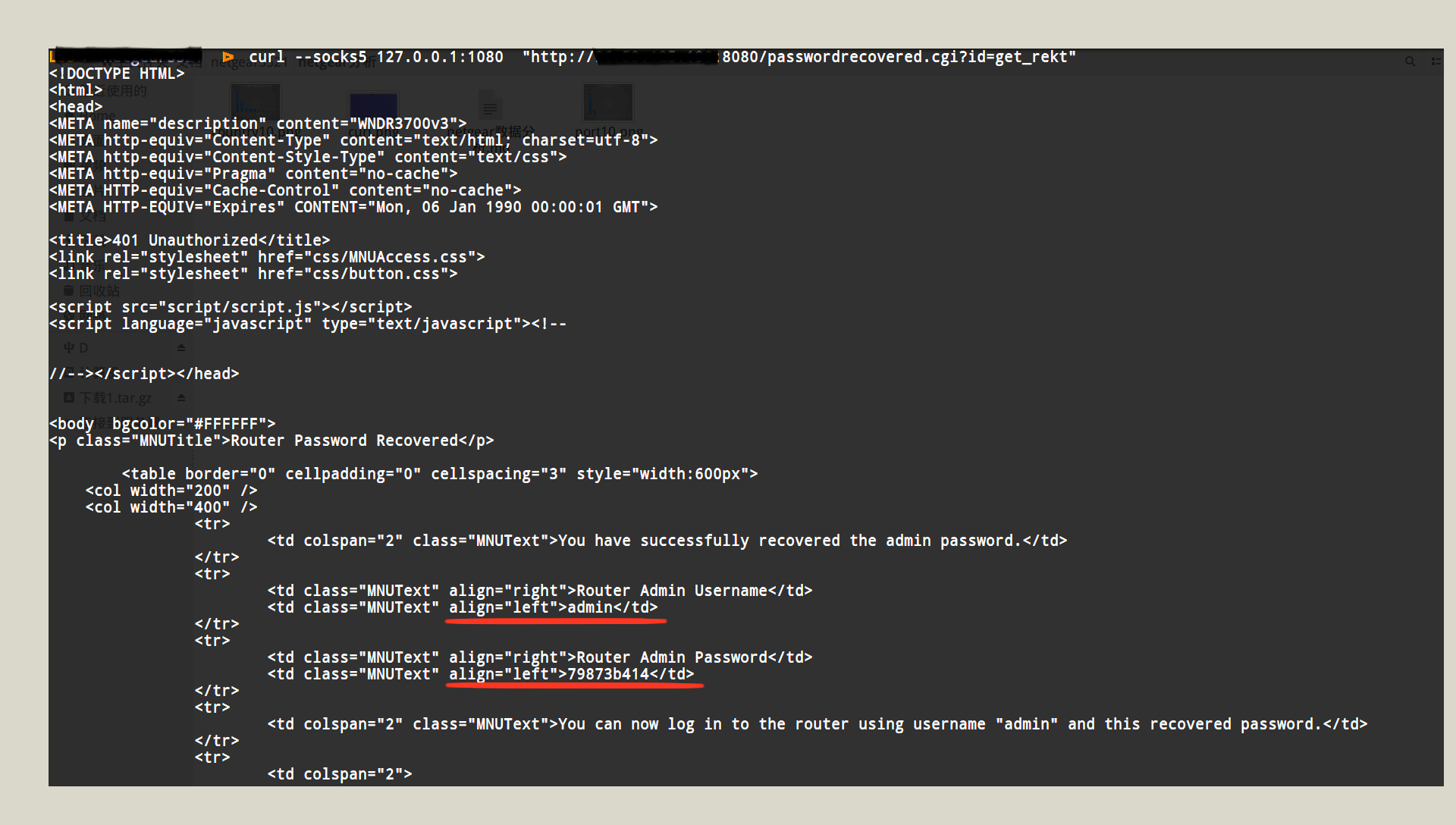 ### 0x05 vulnerability distribution We 2017-02/03 using ZoomEye cyberspace search engine to search for Netgear got 2249273 results, found still affected router has 5065, home in 81 countries. Wherein the number of the top ten country distribution as shown below: 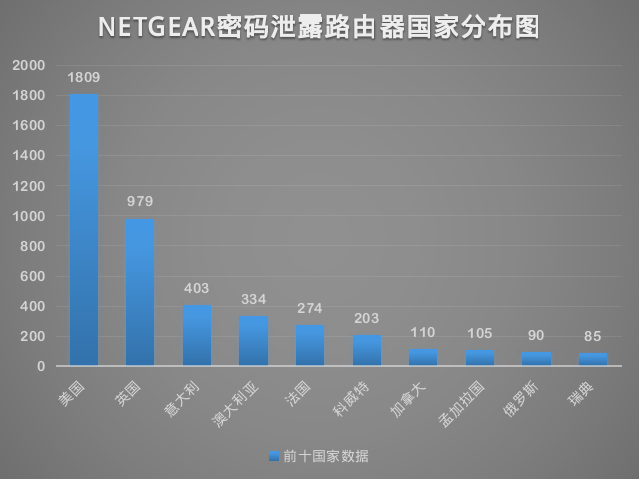 Port distribution aspect, in the router open port type a total of 32 species, of which the port number Top10 as shown below: 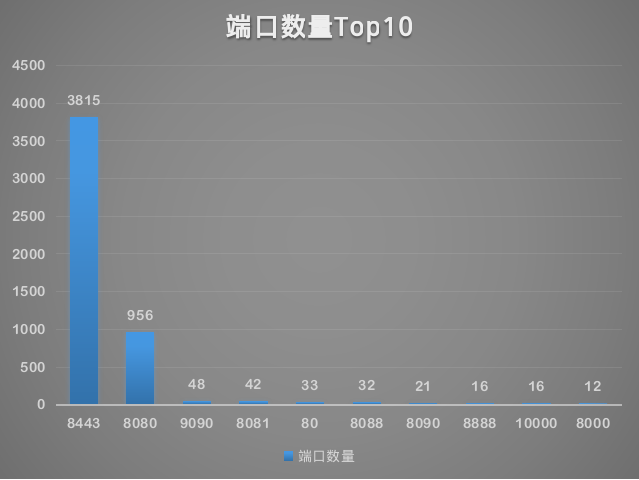 Then we on these router password classification after the statistics of the different passwords a total of 3156. The following table is the number of occurrences of the top ten passwords: 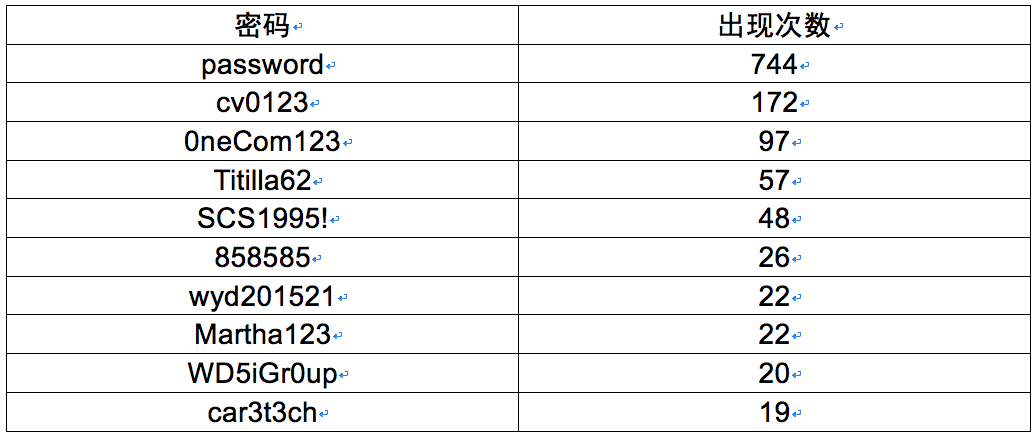 The table appears the most number of times the password is password ,this password is the NETGEAR router default password, that is those affected router has 744 using the default password,which the United States occupies 267, Kuwait occupies a 173. |
| id | SSV:92639 |
| last seen | 2017-11-19 |
| modified | 2017-02-03 |
| published | 2017-02-03 |
| source | https://www.seebug.org/vuldb/ssvid-92639 |
| title | Netgear router password disclosure Vulnerability(CVE-2017-5521) |