Vulnerabilities > CVE-2017-12650 - SQL Injection vulnerability in Loginizer
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
PARTIAL Integrity impact
PARTIAL Availability impact
PARTIAL Summary
SQL Injection exists in the Loginizer plugin before 1.3.6 for WordPress via the X-Forwarded-For HTTP header.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
- Object Relational Mapping Injection An attacker leverages a weakness present in the database access layer code generated with an Object Relational Mapping (ORM) tool or a weakness in the way that a developer used a persistence framework to inject his or her own SQL commands to be executed against the underlying database. The attack here is similar to plain SQL injection, except that the application does not use JDBC to directly talk to the database, but instead it uses a data access layer generated by an ORM tool or framework (e.g. Hibernate). While most of the time code generated by an ORM tool contains safe access methods that are immune to SQL injection, sometimes either due to some weakness in the generated code or due to the fact that the developer failed to use the generated access methods properly, SQL injection is still possible.
- SQL Injection through SOAP Parameter Tampering An attacker modifies the parameters of the SOAP message that is sent from the service consumer to the service provider to initiate a SQL injection attack. On the service provider side, the SOAP message is parsed and parameters are not properly validated before being used to access a database in a way that does not use parameter binding, thus enabling the attacker to control the structure of the executed SQL query. This pattern describes a SQL injection attack with the delivery mechanism being a SOAP message.
- Expanding Control over the Operating System from the Database An attacker is able to leverage access gained to the database to read / write data to the file system, compromise the operating system, create a tunnel for accessing the host machine, and use this access to potentially attack other machines on the same network as the database machine. Traditionally SQL injections attacks are viewed as a way to gain unauthorized read access to the data stored in the database, modify the data in the database, delete the data, etc. However, almost every data base management system (DBMS) system includes facilities that if compromised allow an attacker complete access to the file system, operating system, and full access to the host running the database. The attacker can then use this privileged access to launch subsequent attacks. These facilities include dropping into a command shell, creating user defined functions that can call system level libraries present on the host machine, stored procedures, etc.
- SQL Injection This attack exploits target software that constructs SQL statements based on user input. An attacker crafts input strings so that when the target software constructs SQL statements based on the input, the resulting SQL statement performs actions other than those the application intended. SQL Injection results from failure of the application to appropriately validate input. When specially crafted user-controlled input consisting of SQL syntax is used without proper validation as part of SQL queries, it is possible to glean information from the database in ways not envisaged during application design. Depending upon the database and the design of the application, it may also be possible to leverage injection to have the database execute system-related commands of the attackers' choice. SQL Injection enables an attacker to talk directly to the database, thus bypassing the application completely. Successful injection can cause information disclosure as well as ability to add or modify data in the database. In order to successfully inject SQL and retrieve information from a database, an attacker:
Seebug
| bulletinFamily | exploit |
| description | As part of a vulnerability research project for our WordPress Security Scanner at WPcans.com, we have been auditing popular WordPress plugins looking for security issues. While auditing the WordPress plugin Loginizer, we discovered a SQL Injection vulnerability and a Cross-Site Request Forgery (CSRF). This plugin is currently installed on 500,000+ websites. ### About the plugin According to WordPress.org: Loginizer is a WordPress plugin which helps you fight against bruteforce attack by blocking login for the IP after it reaches maximum retries allowed. You can blacklist or whitelist IPs for login using Loginizer. You can use various other features like Two Factor Auth, reCAPTCHA, PasswordLess Login, etc. to improve security of your website. ### Are You at Risk? This vulnerability is caused by the lack of sanitization in user provided data and missing checks. As soon as possible upgrade to the latest version of the plugin: 1.3.6. You can also use our free security scanner at WPScans.com to scan for this vulnerability or the open-source tool wpscan. ### Technical Details CSRF First, the CSRF vulnerability can be triggered when a admin or a user with manage_option privileges clicks a link provided by an attacker. The link can be hidden with a URL-shortener for example, screenshots from the broken referer/nonce check: 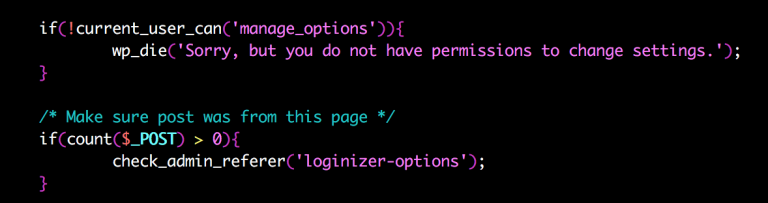 As the above screenshot shows the check_admin_referer() function is only executed if $_POST is set. But deleting a whitelist or blacklist IP does not require POST, only GET: 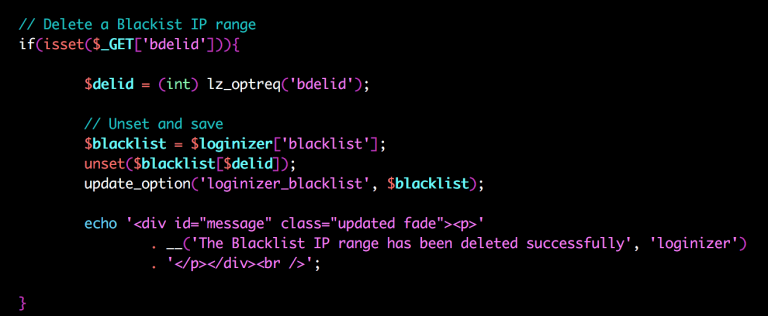 ### Technical Details SQL Injection When someone tries to login at least one SQL-query is executed by the plugin. The query looks something like this: ``` SELECT * FROM `wp_loginizer_logs` WHERE `ip` = 'myip... ``` The problem above is that an attacker can set IP using different http-headers such as X-Forwarded-For depending on the server setup. This http-header is forwarded without any sanitization to lz_selectquery() and then $wpdb->get_results(). This is a blind SQL injection vulnerability and can be exploited using sqlmap, as example: 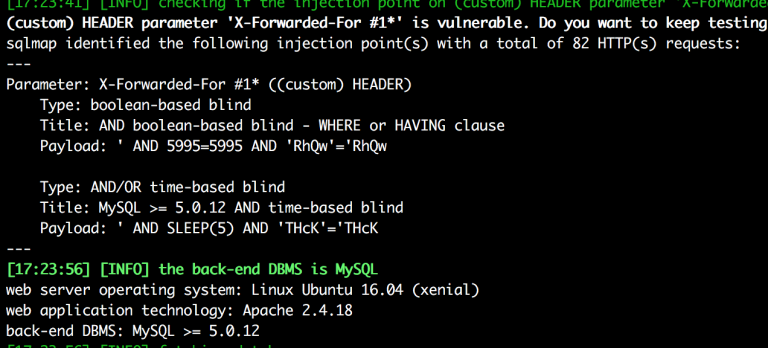 ###b Timeline * 2017-08-02 Vulnerabilities found * 2017-08-04 Plugin vendor contacted using online form * 2017-08-07 Fixed by vendor: WordPress.org changelog * 2017-08-07 CVE ID requested * 2017-08-08 Blog post published |
| id | SSV:96370 |
| last seen | 2017-11-19 |
| modified | 2017-08-22 |
| published | 2017-08-22 |
| reporter | Root |
| title | SQL Injection(CVE-2017-12650) and CSRF(CVE-2017-12651) Security Vulnerability in Loginizer |