Security News

Your profile can be used to present content that appears more relevant based on your possible interests, such as by adapting the order in which content is shown to you, so that it is even easier for you to find content that matches your interests. Content presented to you on this service can be based on your content personalisation profiles, which can reflect your activity on this or other services, possible interests and personal aspects.

Developed by OpenAI, ChatGPT has garnered attention across industries for its ability to generate relevant responses to various queries. As the adoption of ChatGPT accelerates, so do discussions surrounding its ethical and security implications.

A new information stealer named ExelaStealer has become the latest entrant to an already crowded landscape filled with various off-the-shelf malware designed to capture sensitive data from...

A Russian national helped smuggle, via shell companies in Hong Kong, more than $1.6 million in microelectronics to Moscow potentially to support its war against Ukraine, it is claimed. "Probably more than obvious at this time, but the company and board have decided it is no longer right for us to sell or ship to Russian customers and risk that our displays will be used in devices that could put US or NATO forces in harm's way, or support Russia's unlawful invasion of Ukraine and its human rights abuse," a company exec said in an email to employees, which was quoted in the prosecution's court filings.
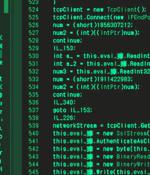
The North Korean threat actor known as Andariel has been observed employing an arsenal of malicious tools in its cyber assaults against corporations and organizations in the southern counterpart. Ariel, also known by the names Nicket Hyatt or Silent Chollima, is a sub-cluster of the Lazarus Group that's known to be active since at least 2008.

Cybersecurity expert Kayne McGladrey speaks about why AI cannot do what creative people can, and the important role of generative AI in SOCs. Kayne McGladrey, IEEE Fellow and cybersecurity veteran with more than 25 years of experience, asserts that the human element - particularly people with diverse interests, backgrounds and talents - is irreplaceable in cybersecurity.

The Iranian state-sponsored group dubbed MuddyWater has been attributed to a previously unseen command-and-control framework called PhonyC2 that's been put to use by the actor since 2021. "MuddyWater is continuously updating the PhonyC2 framework and changing TTPs to avoid detection."

A crypter malware dubbed AceCryptor has been used to pack numerous strains of malware since 2016. Some of the prominent malware families contained within AceCryptor are SmokeLoader, RedLine Stealer, RanumBot, Raccoon Stealer, Stop ransomware, and Amadey, among others.

An unidentified whistleblower has provided several media organizations with access to leaked documents from NTC Vulkan - a Moscow IT consultancy - that allegedly show how the firm supports Russia's military and intelligence agencies with cyber warfare tools. According to The Guardian, this latest whistleblower chose to distribute the secret Russian documents due to anger over Russia's bloody invasion of Ukraine and a desire to see the information reveal some of what is going on inside Russia.

A state-sponsored hacking group with links to Russia has been linked to attack infrastructure that spoofs the Microsoft login page of Global Ordnance, a legitimate U.S.-based military weapons and hardware supplier. The cybersecurity firm said it discovered 38 domains, nine of which contained references to companies like UMO Poland, Sangrail LTD, DTGruelle, Blue Sky Network, the Commission for International Justice and Accountability, and the Russian Ministry of Internal Affairs.