Security News

As the FCC planned, the new rule also eliminates the mandatory seven-day waiting period for reporting break-ins to consumers. "Without an FCC rule requiring breach notifications for the above categories of PII, there would be no requirement in Federal law that telecommunications carriers report non-CPNI breaches to their customers," the FCC said of the new rule.

The Turkish state-backed cyber espionage group tracked as Sea Turtle has been carrying out multiple spying campaigns in the Netherlands, focusing on telcos, media, internet service providers, and Kurdish websites. Previously, Sea Turtle, also known as Teal Kurma and Cosmic Wolf, focused on the Middle Eastern region, as well as Sweden and the United States, using techniques like DNS hijacking and traffic redirection to perform man-in-the-middle attacks against government and non-government organizations, media, ISPs, and IT service providers.

The agency states that the Russian hackers "Interfered" with the communication systems of 11 telcos in the country, leading to service interruptions and potential data breaches. Sandworm is a very active espionage threat group linked to Russia's GRU. The attackers have focused on Ukraine throughout 2023, using phishing lures, Android malware, and data-wipers.

A Chinese cyber-espionage hacking group tracked as Budworm has been observed targeting a telecommunication firm in the Middle East and a government entity in Asia using a new variant of its custom 'SysUpdate' backdoor. The SysUpdate malware is a remote access trojan associated with Budworm since 2020, supporting Windows service, process, and file management, command execution, data retrieval, and screenshot capturing.

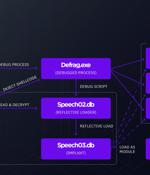
A previously unknown threat actor dubbed 'Sandman' targets telecommunication service providers in the Middle East, Western Europe, and South Asia, using a modular info-stealing malware named 'LuaDream. SandMan has been seen deploying a new modular malware named 'LuaDream' in attacks using DLL hijacking on targeted systems.

In Brief The Federal Communications Commission plans to overhaul its security reporting rules for the telecom industry to, among other things, eliminate a mandatory seven-day wait for informing customers of stolen data and expand the definition of what constitutes an incident. In a unanimous 4-0 vote, the FCC published a notice of proposed rulemaking that Chairwoman Jessica Rosenworcel said is sorely overdue, as the current rules are more than 15 years old.

To that end, telecommunications companies, mobile network operators and other communication service providers are already taking advantage of the security controls inherited from 3G/4G. And they are now supplementing them with purpose built 5G security controls to enhance their network and service security processes, while simultaneously introducing best practices and policies to deliver the necessary resilience. "Regarding security assurance, telcos have historically relied on a priori security certification of physical components and devices, such as through Common Criteria. The 'softwarization' of network components - central to the 5G service-oriented architecture - requires much more agile ways to test security."

A threat group that researchers call OPERA1ER has stolen at least $11 million from banks and telecommunication service providers in Africa using off-the-shelf hacking tools. Analysts at Group-IB, working with the CERT-CC department at Orange, have been tracking OPERA1ER since 2019 and noticed that the group changed its techniques, tactics, and procedures last year.

Telecommunications and IT service providers in the Middle East and Asia are being targeted by a previously undocumented Chinese-speaking threat group dubbed WIP19. "Almost all operations performed by the threat actor were completed in a 'hands-on keyboard' fashion, during an interactive session with compromised machines," SentinelOne researchers Joey Chen and Amitai Ben Shushan Ehrlich said in a report this week.
The cybersecurity firm codenamed the group Metador in reference to a string "I am meta" in one of their malware samples and because of Spanish-language responses from the command-and-control servers. The threat actor is said to have primarily focused on the development of cross-platform malware in its pursuit of espionage aims.