Security News

Hackers are brute-forcing exposed MS SQL database servers to deliver Mimic ransomware, Securonix researchers are warning. Mimic ransomware was first spotted in the wild in June 2022 and analyzed by Trend Micro researchers in January 2023.

A group of financially motivated Turkish hackers targets Microsoft SQL servers worldwide to encrypt the victims' files with Mimic ransomware. "The timeline for the events was about one month from initial access to the deployment of MIMIC ransomware on the victim domain."

Poorly secured Microsoft SQL (MS SQL) servers are being targeted in the U.S., European Union, and Latin American (LATAM) regions as part of an ongoing financially motivated campaign to gain...

Hackers have been observed trying to breach cloud environments through Microsoft SQL Servers vulnerable to SQL injection. The attacks Microsoft observed start with exploiting an SQL injection vulnerability in an application in the target's environment.

Microsoft has detailed a new campaign in which attackers unsuccessfully attempted to move laterally to a cloud environment through a SQL Server instance. "The attackers initially exploited a SQL...

A cyberattack campaign is targeting exposed Microsoft SQL databases, aiming to deliver ransomware and Cobalt Strike payloads. The attackers target exposed MS SQL servers by brute-forcing access credentials.
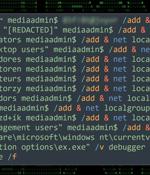
Threat actors are exploiting poorly secured Microsoft SQL servers to deliver Cobalt Strike and a ransomware strain called FreeWorld. "The ransomware payload of choice appears to be a newer variant of Mimic ransomware called FreeWorld."

Mallox ransomware activities in 2023 have witnessed a 174% increase when compared to the previous year, new findings from Palo Alto Networks Unit 42 reveal. "Mallox ransomware, like many other ransomware threat actors, follows the double extortion trend: stealing data before encrypting an organization's files, and then threatening to publish the stolen data on a leak site as leverage to convince victims to pay the ransom fee," security researchers Lior Rochberger and Shimi Cohen said in a new report shared with The Hacker News.

Poorly managed Microsoft SQL servers are the target of a new campaign that's designed to propagate a category of malware called CLR SqlShell that ultimately facilitates the deployment of cryptocurrency miners and ransomware. "Similar to web shell, which can be installed on web servers, SqlShell is a malware strain that supports various features after being installed on an MS SQL server, such as executing commands from threat actors and carrying out all sorts of malicious behavior," AhnLab Security Emergency response Center said in a report published last week.

Attackers are hacking into poorly secured and Interned-exposed Microsoft SQL servers to deploy Trigona ransomware payloads and encrypt all files. Exe service, which they use to launch the Trigona ransomware as svchost.