Security News

42% of businesses report employees with BYOD devices in business settings that use tools like WhatsApp have led to new security incidents, according to SafeGuard Cyber. Messaging platforms like WhatsApp, Telegram, Slack, and Teams face constant threats, emphasizing the need for robust protection.
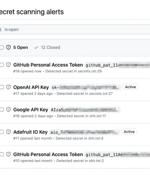
GitHub has announced an improvement to its secret scanning feature that extends validity checks to popular services such as Amazon Web Services (AWS), Microsoft, Google, and Slack. Validity...

We and our store and/or access information on a device, such as cookies and process personal data, such as unique identifiers and standard information sent by a device for personalised ads and content, ad and content measurement, and audience insights, as well as to develop and improve products. With your permission we and our partners may use precise geolocation data and identification through device scanning.

It won't be until Slack offers E2EE as well as blocking, muting and reporting features to help protect users from harassment, they claim. "Millions of people use Slack every day to do their work, volunteer, and connect with communities online - including abortion funds and reproductive rights groups that are being targeted by anti-abortion efforts," Caitlin Seeley George, Fight for the Future's campaigns and managing director, told The Register.

Slack suffered a security incident over the holidays affecting some of its private GitHub code repositories. BleepingComputer has come across a security incident notice issued by Slack on December 31st, 2022.
![S3 Ep95: Slack leak, Github onslaught, and post-quantum crypto [Audio + Text]](/static/build/img/news/s3-ep95-slack-leak-github-onslaught-and-post-quantum-crypto-audio-text-small.jpg)
If we turn back the clock to five years ago, that's when Slack started leaking hashed passwords. If you're a Slack user, I would assume that if they didn't realise they were leaking hashed passwords for five years, maybe they didn't quite enumerate the list of people affected completely either.

Popular collaboration tool Slack has just owned up to a cybersecurity SNAFU. According to a news bulletin entitled Notice about Slack password resets, the company admitted that it had inadvertently been oversharing personal data "When users created or revoked a shared invitation link for their workspace." Slack's security advisory doesn't explain the breach very clearly, saying merely that "[t]his hashed password was not visible to any Slack clients; discovering it required actively monitoring encrypted network traffic coming from Slack's servers.

Did Slack send you a password reset link last week? The company has admitted to accidentally exposing the hashed passwords of workspace users. Slack said only 0.5 percent of users were affected, which doesn't sound too terrible until you consider how many Slack users are out there.

Slack said it took the step of resetting passwords for about 0.5% of its users after a flaw exposed salted password hashes when creating or revoking shared invitation links for workspaces. "When a user performed either of these actions, Slack transmitted a hashed version of their password to other workspace members," the enterprise communication and collaboration platform said in an alert on 4th August.

Slack notified roughly 0.5% of its users that it reset their passwords after fixing a bug exposing salted password hashes when creating or revoking shared invitation links for workspaces. Luckily, the hashed passwords were not visible to Slack clients, with active monitoring of encrypted network traffic from Slack's servers required to access this exposed information, according to Slack.