Security News

Compliance requirements are meant to increase cybersecurity transparency and accountability. As cyber threats increase, so do the number of compliance frameworks and the specificity of the...

With no sign of regulations slowing down, enterprises struggle to keep pace with the rapid changes. According to a recent NTT Data survey of business executives, 3 in 4 organizations can't keep up with data regulations, holding them back from successfully using their data for innovation and digital transformation.
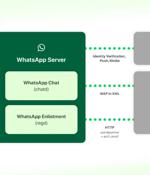
Meta has offered details on how it intends to implement interoperability in WhatsApp and Messenger with third-party messaging services as the Digital Markets Act (DMA) went into effect in the...

In this Help Net Security video, Chris Bowen, CISO at ClearDATA, emphasizes the importance of digital health companies being more transparent with their users. As more and more Americans flock to direct-to-consumer digital health apps and resources, most people don't know that the sensitive health data they share with these companies could be passed on to third parties or sold to data brokers without a single consent form.

Data protection is relevant to everyone, whether you are handling personal data or your data being processed. It delves into the main data protection applications and explores the rights afforded under these regulations.

As the frequency and sophistication of cyber threats continue to escalate, the need for robust cybersecurity regulations has never been more critical. In this Help Net Security round-up, we present segments from previously recorded videos in which cybersecurity experts underscore the importance of proactive cybersecurity measures in the face of evolving regulations.

Some of the essential questions security teams ought to be asking themselves include: How do we manage and safeguard aspects like confidentiality, integrity, and availability of data? What strategies can we employ to protect our data against cyber threats and misuse? How do we address the security challenges that emerge with expanding data repositories? How do we differentiate between valuable data and redundant information? Security teams may need to engage in discussions with business units to clarify issues such as how we are applying our data.

It may be tempting for organizations to wait and see how regulations develop or hold on for federal-level legislation; the American Data Privacy Protection Act has been introduced to Congress, although it will take a while to see if it has a chance of coming through the legislative process and being passed into law. For organizations with customers in both the US and Europe, there's recently been some good news: the EU has decided that "The United States ensures an adequate level of protection - comparable to that of the European Union - for personal data transferred from the EU to US companies." In principle, this means user data from Europe can flow freely to the US without additional data protection safeguards.

In Claroty's previous survey conducted in 2021, 32% of ransomware attacks impacted IT only, while 27% impacted both IT and OT. Today, 21% impact IT only, while 37% impact both IT and OT - a significant 10% jump for the latter in just two years. 61% of respondents are currently utilizing security tools that leverage generative AI and an alarming 47% say that it raises their security concerns.

The Australian government is moving towards regulating cryptocurrency, with a focus on those involved in developing and maintaining crypto platforms. Cryptocurrency is known for its vulnerability, with Australia experiencing several incidents, including a AUD$40 million hack on the crypto betting platform, Stake, and the theft of over one million from an Australian Bitcoin bank in 2013.