Security News

The LockBit ransomware gang has again started using encryptors based on other operations, this time switching to one based on the leaked source code for the Conti ransomware. This week, cybersecurity collective VX-Underground first reported that the ransomware gang is now using a new encryptor named 'LockBit Green,' based on the leaked source code of the now-disbanded Conti gang.

Symantec refers to both the BlackByte group and the BlackByte ransomware by the same name. Following the departure of a number of major ransomware operations such as Conti and Sodinokibi, BlackByte has emerged as one of the ransomware actors to profit from this gap in the market.

Former members of the Conti cybercrime cartel have been implicated in five different campaigns targeting Ukraine from April to August 2022. One of the prominent campaigns undertaken by the group in June 2022 entailed the abuse of Follina vulnerability in the Windows operating system to deploy CrescentImp and Cobalt Strike Beacons on to targeted hosts in media and critical infrastructure entities.

Google says some former Conti cybercrime gang members, now part of a threat group tracked as UAC-0098, are targeting Ukrainian organizations and European non-governmental organizations. Google TAG says its attribution is based on multiple overlaps between UAC-0098, Trickbot, and the Conti cybercrime group.

Google says some former Conti ransomware gang members, now part of a threat group tracked as UAC-0098, are targeting Ukrainian organizations and European non-governmental organizations. Google TAG says its attribution is based on multiple overlaps between UAC-0098, Trickbot, and the Conti cybercrime group.
![S3 Ep96: Zoom 0-day, AEPIC leak, Conti reward, healthcare security [Audio + Text]](/static/build/img/news/s3-ep96-zoom-0-day-aepic-leak-conti-reward-healthcare-security-audio-text-small.jpg)
If you want to understand a little more about it, your Naked Security article explains it incredibly well for people that are not normally acquainted with things like APIC controllers. Do you think, Chester, that they've targeted the Conti gang because they had a little bit of dishonour among thieves, as it were?

Conti is the name of a well-known ransomware gang - more precisely, what's known as a ransomware-as-a-service gang, where the ransomware code, and the blackmail demands, and the receipt of extortion payments from desperate victims are handled by a core group. About two years ago, the REvil ransomware gang put up a cool $1,000,000 as front money in an underground hacker-recruiting forum, trying to entice new affiliates to join their cybercriminal capers.
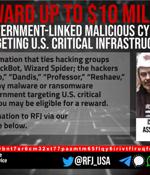
The U.S. State Department on Thursday announced a $10 million reward for information related to five individuals associated with the Conti ransomware group. The reward offer, first reported by WIRED, is also notable for the fact that it marks the first time the face of a Conti associate, known as "Target," has been unmasked.

The US government is putting a face on a claimed member of the infamous Conti ransomware group as part of a $10 million reward for information about five of the gang's crew. "The reward notice included the aliases of the alleged attackers -"Tramp," "Dandis," "Professor,"Reshaev," and "Target" - and came with a photo of a man and a message underneath it that said, "Is this the Conti associate known as 'Target'?".

Three different offshoots of the notorious Conti cybercrime cartel have resorted to the technique of call-back phishing as an initial access vector to breach targeted networks. "Three autonomous threat groups have since adopted and independently developed their own targeted phishing tactics derived from the call back phishing methodology," cybersecurity firm AdvIntel said in a Wednesday report.