Security News

A pair of flaws in ASUS routers for the home could allow an attacker to compromise the devices - and eavesdrop on all of the traffic and data that flows through them. The bugs are specifically found in the RT-AC1900P whole-home Wi-Fi model, within the router's firmware update functionality.

With the advent of the AIoT era, ASUS has embraced new technologies and methods to develop advanced manufacturing capabilities. At the end of 2019, ASUS expanded the company's AIoT business unit to be able to develop more solutions for industries and, in the process, renamed it the AIoT Business Group.
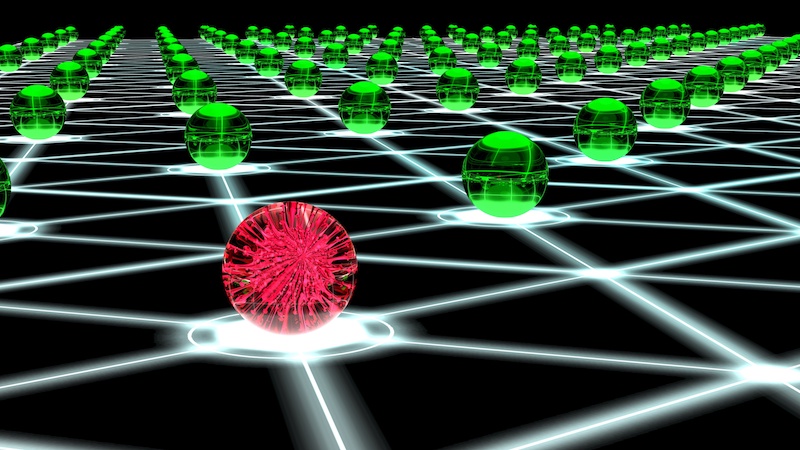
The botnet, called dark nexus, uses processes similar to previous dangerous IoT threats like the Qbot banking malware and Mirai botnet. Dark nexus also borrows code and processes previously used by Qbot and the infamous Mirai botnet that launched the 2016 Dyn DDos attack.

Vulnerabilities discovered in Acer and ASUS software preinstalled on most PCs from these companies could lead to privilege escalation and the execution of arbitrary payloads, SafeBreach warns. read more

Independent researchers found 125 different CVEs across 13 different router and NAS models.

The BlackTech cyber-espionage group has been performing man-in-the-middle (MitM) attacks on the update process of the ASUS WebStorage application to deliver the Plead backdoor to their targeted...

Here’s an overview of some of last week’s most interesting news and articles: Attackers compromised ASUS to deliver backdoored software updates Unknown attackers have compromised an update server...

EXCLUSIVE — While revealing details of a massive supply chain cyber attack against ASUS customers, Russian security firm Kaspersky last week didn't release the full list all MAC addresses that...

Kaspersky Labs is reporting on a new supply chain attack they call "Shadowhammer." In January 2019, we discovered a sophisticated supply chain attack involving the ASUS Live Update Utility. The...

ASUS says it has released a fix for the Live Update utility that threat actors abused in Operation ShadowHammer supply chain attack to deliver malware to hundreds of users. read more