Security News
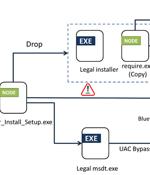
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the attack is a PDF file written in Portuguese that,...

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a high-severity flaw in Adobe Acrobat Reader to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence...

Adobe's Patch Tuesday update for September 2023 comes with a patch for a critical actively exploited security flaw in Acrobat and Reader that could permit an attacker to execute malicious code on susceptible systems. The vulnerability, tracked as CVE-2023-26369, is rated 7.8 for severity on the CVSS scoring system and impacts both Windows and macOS versions of Acrobat DC, Acrobat Reader DC, Acrobat 2020, and Acrobat Reader 2020.

Adobe has released security updates to patch a zero-day vulnerability in Acrobat and Reader tagged as exploited in attacks."Adobe is aware that CVE-2023-26369 has been exploited in the wild in limited attacks targeting Adobe Acrobat and Reader," the company said in a security advisory published today.

Cybercriminals are abusing Adobe Acrobat Sign, an online document signing service, to distribute info-stealing malware to unsuspecting users. Adobe Acrobat Sign is a free-to-try cloud-based e-signature service allowing users to send, sign, track, and manage electronic signatures.

Microsoft and Adobe have partnered to integrate the Adobe Acrobat PDF rendering engine directly into the Edge browser, replacing the existing PDF engine. Starting in March 2023, new versions of Microsoft Edge for Windows 10 and Windows 11 will roll out that includes this new PDF engine.

Security researchers found that Adobe Acrobat is trying to block security software from having visibility into the PDF files it opens, creating a security risk for the users. "Since March of 2022 we've seen a gradual uptick in Adobe Acrobat Reader processes attempting to query which security product DLLs are loaded into it by acquiring a handle of the DLL" - Minerva Labs.

Adobe is urging its throngs of Acrobat Reader users to update their software to fix critical vulnerabilities that could allow adversaries to execute arbitrary code on unpatched versions. As for the Adobe Acrobat family of software, 26 bugs were patched, 13 of which were critical and given an Adobe priority rating of "2," meaning that the affected product is at "Elevated risk" of being attacked.

Eleven critical bugs in Adobe's popular and free PDF reader, Acrobat, open both Window and macOS users to attacks ranging from an adversary arbitrarily executing commands on a targeted system to data leakage tied to system-read and memory flaws. The free Acrobat Reader 2020 and PDF-creation and editing software Acrobat 2020 were among the list of those programs with critical bugs patched.

Adobe has issued multiple security advisories with patches for critical vulnerabilities in a wide range of software products, including the ever-present Adobe Acrobat and Reader application. The Mountain View, Calif.-based Adobe urged Windows and macOS users to treat the PDF Reader patch with the utmost priority, because the flaws expose machines to remote code execution and privilege escalation attacks.