Security News > 2023 > May > New WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East
An unknown threat actor has been observed leveraging a malicious Windows kernel driver in attacks likely targeting the Middle East since at least May 2020.
A key security measure to mitigate against malicious drivers is Driver Signature Enforcement, which ensures that only drivers signed by Microsoft can be loaded on the system.
The tech giant also maintains driver block rules to protect against known vulnerable drivers.
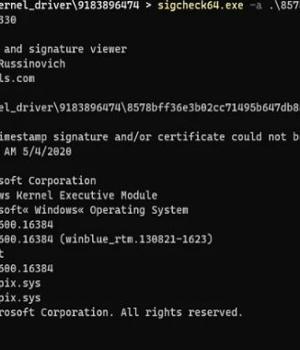
Sys, on the other hand, comes with an invalid signature, indicating that the threat actor will have to first load a legitimate but vulnerable driver in order to launch WINTAPIX. UPCOMING WEBINAR. Zero Trust + Deception: Learn How to Outsmart Attackers!
The development comes as the ALPHV ransomware group has been observed taking advantage of a malicious signed driver to impair security defenses and escape detection for extended periods of time.
POORTRY is the name assigned to a Windows kernel driver that comes with capabilities to terminate security software.
News URL
https://thehackernews.com/2023/05/new-wintapixsys-malware-engages-in.html
Related news
- CISA warns of Microsoft Streaming bug exploited in malware attacks (source)
- DarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack (source)
- From Deepfakes to Malware: AI's Expanding Role in Cyber Attacks (source)
- New BunnyLoader Malware Variant Surfaces with Modular Attack Features (source)
- Over 100 US and EU orgs targeted in StrelaStealer malware attacks (source)
- The Biggest Takeaways from Recent Malware Attacks (source)
- Critical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks (source)
- Attackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing (source)
- Microsoft fixes two Windows zero-days exploited in malware attacks (source)
- TA558 Hackers Weaponize Images for Wide-Scale Malware Attacks (source)