Security News > 2023 > March > Researchers Uncover Chinese Nation State Hackers' Deceptive Attack Strategies
Attack chains mounted by the group commence with a spear-phishing email to deploy a wide range of tools for backdoor access, command-and-control, and data exfiltration.
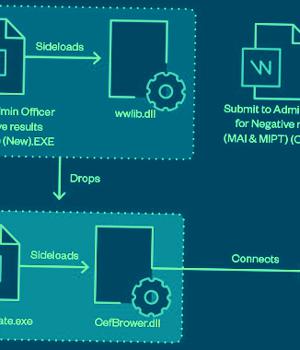
These messages come bearing with malicious lure archives distributed via Dropbox or Google Drive links that employ DLL side-loading, LNK shortcut files, and fake file extensions as arrival vectors to obtain a foothold and drop backdoors like TONEINS, TONESHELL, PUBLOAD, and MQsTTang.
"The files can then be extracted inside via the password provided in the document," the researchers said.
Other utilities deployed include CLEXEC, a backdoor capable of executing commands and clearing event logs; COOLCLIENT and TROCLIENT, implants that are designed to record keystrokes as well as read and delete files; and PlugX. "Apart from well-known legitimate tools, the threat actors also crafted highly customized tools used for exfiltration," the researchers noted.
The findings once again highlight the increased operational tempo of Chinese cyber espionage actors and their consistent investment in advancing their cyber weaponry to evade detection.
"Earth Preta is a capable and organized threat actor that is continuously honing its TTPs, strengthening its development capabilities, and building a versatile arsenal of tools and malware," the researchers concluded.
News URL
https://thehackernews.com/2023/03/researchers-uncover-chinese-nation.html
Related news
- Chinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks (source)
- Russian hackers shift to cloud attacks, US and allies warn (source)
- Russian hackers hijack Ubiquiti routers to launch stealthy attacks (source)
- Chinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware (source)
- Lazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks (source)
- Hackers target FCC, crypto firms in advanced Okta phishing attacks (source)
- Hackers steal Windows NTLM authentication hashes in phishing attacks (source)
- Hackers impersonate U.S. government agencies in BEC attacks (source)
- Chinese Earth Krahang hackers breach 70 orgs in 23 countries (source)
- Hackers Exploiting Popular Document Publishing Sites for Phishing Attacks (source)