Security News > 2022 > September > Researchers Disclose Critical Vulnerability in Oracle Cloud Infrastructure
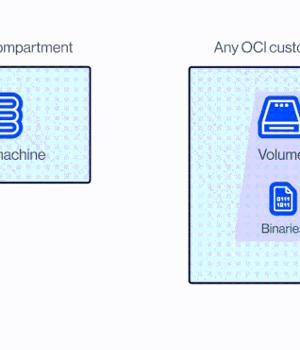
Researchers have disclosed a new severe Oracle Cloud Infrastructure vulnerability that could be exploited by users to access the virtual disks of other Oracle customers.
"Each virtual disk in Oracle's cloud has a unique identifier called OCID," Shir Tamari, head of research at Wiz, said in a series of tweets.
"Given the OCID of a victim's disk that is not currently attached to an active server or configured as shareable, an attacker could 'attach' to it and obtain read/write over it," Tamari added.
The cloud security firm, which dubbed the tenant isolation vulnerability "AttachMe," said Oracle patched the issue within 24 hours of responsible disclosure on June 9, 2022.
At its core, the vulnerability is rooted in the fact that a disk could be attached to a compute instance in another account via the Oracle Cloud Identifier without any explicit authorization.
"Insufficient validation of user permissions is a common bug class among cloud service providers," Wiz researcher Elad Gabay said.
News URL
https://thehackernews.com/2022/09/researchers-disclose-critical.html
Related news
- WordPress Plugin Alert - Critical SQLi Vulnerability Threatens 200K+ Websites (source)
- NIST CSF 2.0 released, to help all organizations, not just those in critical infrastructure (source)
- Australian spy chief fears sabotage of critical infrastructure (source)
- Phobos Ransomware Aggressively Targeting U.S. Critical Infrastructure (source)
- FBI: Critical infrastructure suffers spike in ransomware attacks (source)
- Major shifts in identity, ransomware, and critical infrastructure threat trends (source)
- Web-based PLC malware: A new potential threat to critical infrastructure (source)
- VMware patches critical flaws in ESXi, Workstation, Fusion and Cloud Foundation (source)
- Researchers Detail Kubernetes Vulnerability That Enables Windows Node Takeover (source)
- Critical FortiClient EMS vulnerability fixed, (fake?) PoC for sale (CVE-2023-48788) (source)